-$ curl foobar -.... -+``` sh +$ rake generate_json_from_responses ``` -This is not a `curl` tutorial though. Not every API call needs -to show how to access it with `curl`. - -## Development +The generated files will end up in *json-dump/*. -Nanoc compiles the site into static files living in `./output`. It's -smart enough not to try to compile unchanged files: +### Terminal blocks -```sh -$ bundle exec nanoc compile -Loading site data... -Compiling site... - identical [0.00s] output/css/960.css - identical [0.00s] output/css/pygments.css - identical [0.00s] output/css/reset.css - identical [0.00s] output/css/styles.css - identical [0.00s] output/css/uv_active4d.css - update [0.28s] output/index.html - update [1.31s] output/v3/gists/comments/index.html - update [1.92s] output/v3/gists/index.html - update [0.25s] output/v3/issues/comments/index.html - update [0.99s] output/v3/issues/labels/index.html - update [0.49s] output/v3/issues/milestones/index.html - update [0.50s] output/v3/issues/index.html - update [0.05s] output/v3/index.html +You can specify terminal blocks by using the `command-line` syntax highlighting. -Site compiled in 5.81s. -``` + ``` command-line + $ curl foobar + ``` -You can setup whatever you want to view the files. If using the adsf -gem (as listed in the Gemfile), you can start Webrick: +You can use certain characters, like `$` and `#`, to emphasize different parts +of commands. -```sh -$ bundle exec nanoc view -$ open http://localhost:3000 -``` + ``` command-line + # call foobar + $ curl foobar + .... + ``` -Compilation times got you down? Use `autocompile`! +For more information, see [the reference documentation](https://github.com/gjtorikian/extended-markdown-filter#command-line-highlighting). -```sh -$ bundle exec nanoc autocompile -``` +## Licenses -This starts a web server too, so there's no need to run `nanoc view`. -One thing: remember to add trailing slashes to all nanoc links! +The code to generate the site (everything excluding the assets, content, +and layouts directories) as well as the code samples on the site are +licensed under +[CC0-1.0](https://creativecommons.org/publicdomain/zero/1.0/legalcode). +CC0 waives all copyright restrictions but does not grant you any trademark +permissions. -## Deploy +Site content (everything in the assets, content, and layouts directories, +excluding files under open source licenses individually marked) is licensed +under [CC-BY-4.0](https://creativecommons.org/licenses/by/4.0/). CC-BY-4.0 +gives you permission to use content for almost any purpose but does not grant +you any trademark permissions, so long as you note the license and give credit, +such as follows: -```sh -$ bundle exec rake publish -``` +> Content based on +> developer.github.com +> used under the +> CC-BY-4.0 +> license. -## TODO +This means you can use the code and content in this repository except for +GitHub trademarks in your own projects. -* Integrate through a simple hurl.it app for live API calls. -*
 +```
+
+The script will check your server to see if an alternative image exists at `/images/my_image@2x.png`
+
+However, if you have:
+
+```html
+
+```
+
+The script will check your server to see if an alternative image exists at `/images/my_image@2x.png`
+
+However, if you have:
+
+```html
+ +```
+
+The script will use `http://example.com/my_image@2x.png` as the high-resolution image. No checks to the server will be performed.
+
+## How to use
+
+### JavaScript
+
+The JavaScript helper script automatically replaces images on your page with high-resolution variants (if they exist). To use it, download the script and include it at the bottom of your page.
+
+1. Place the retina.js file on your server
+2. Include the script on your page (put it at the bottom of your template, before your closing \ tag)
+
+``` html
+
+```
+
+### LESS
+
+The LESS CSS mixin is a helper for applying high-resolution background images in your stylesheet. You provide it with an image path and the dimensions of the original-resolution image. The mixin creates a media query specifically for Retina displays, changes the background image for the selector elements to use the high-resolution (@2x) variant and applies a background-size of the original image in order to maintain proper dimensions. To use it, download the mixin, import or include it in your LESS stylesheet, and apply it to elements of your choice.
+
+*Syntax:*
+
+``` less
+.at2x(@path, [optional] @width: auto, [optional] @height: auto);
+```
+
+*Steps:*
+
+1. Add the .at2x() mixin from retina.less to your LESS stylesheet (or reference it in an @import statement)
+2. In your stylesheet, call the .at2x() mixin anywhere instead of using background-image
+
+This:
+
+``` less
+.logo {
+ .at2x('/images/my_image.png', 200px, 100px);
+}
+```
+
+Will compile to:
+
+``` less
+.logo {
+ background-image: url('/images/my_image.png');
+}
+
+@media all and (-webkit-min-device-pixel-ratio: 1.5) {
+ .logo {
+ background-image: url('/images/my_image@2x.png');
+ background-size: 200px 100px;
+ }
+}
+```
+
+### Ruby on Rails 3.x
+
+...or any framework that embeds some digest/hash to the asset URLs based on the contents, e.g. `/images/image-{hash1}.jpg`.
+
+The problem with this is that the high-resolution version would have a different hash, and would not conform the usual pattern, i.e. `/images/image@2x-{hash2}.jpg`. So automatic detection would fail because retina.js would check the existence of `/images/image-{hash1}@2x.jpg`.
+
+There's no way for retina.js to know beforehand what the high-resolution image's hash would be without some sort of help from the server side. So in this case, the suggested method is to supply the high-resolution URLs using the `data-at2x` attributes as previously described in the How It Works section.
+
+In Rails, one way to automate this is using a helper, e.g.:
+
+```ruby
+# in app/helpers/some_helper.rb or app/helpers/application_helper.rb
+def image_tag_with_at2x(name_at_1x, options={})
+ name_at_2x = name_at_1x.gsub(%r{\.\w+$}, '@2x\0')
+ image_tag(name_at_1x, options.merge("data-at2x" => asset_path(name_at_2x)))
+end
+```
+
+And then in your views (templates), instead of using image_tag, you would use image_tag_with_at2x, e.g. for ERB:
+
+```erb
+<%= image_tag_with_at2x "logo.png" %>
+```
+
+It would generate something like:
+
+```html
+
+```
+
+The script will use `http://example.com/my_image@2x.png` as the high-resolution image. No checks to the server will be performed.
+
+## How to use
+
+### JavaScript
+
+The JavaScript helper script automatically replaces images on your page with high-resolution variants (if they exist). To use it, download the script and include it at the bottom of your page.
+
+1. Place the retina.js file on your server
+2. Include the script on your page (put it at the bottom of your template, before your closing \ tag)
+
+``` html
+
+```
+
+### LESS
+
+The LESS CSS mixin is a helper for applying high-resolution background images in your stylesheet. You provide it with an image path and the dimensions of the original-resolution image. The mixin creates a media query specifically for Retina displays, changes the background image for the selector elements to use the high-resolution (@2x) variant and applies a background-size of the original image in order to maintain proper dimensions. To use it, download the mixin, import or include it in your LESS stylesheet, and apply it to elements of your choice.
+
+*Syntax:*
+
+``` less
+.at2x(@path, [optional] @width: auto, [optional] @height: auto);
+```
+
+*Steps:*
+
+1. Add the .at2x() mixin from retina.less to your LESS stylesheet (or reference it in an @import statement)
+2. In your stylesheet, call the .at2x() mixin anywhere instead of using background-image
+
+This:
+
+``` less
+.logo {
+ .at2x('/images/my_image.png', 200px, 100px);
+}
+```
+
+Will compile to:
+
+``` less
+.logo {
+ background-image: url('/images/my_image.png');
+}
+
+@media all and (-webkit-min-device-pixel-ratio: 1.5) {
+ .logo {
+ background-image: url('/images/my_image@2x.png');
+ background-size: 200px 100px;
+ }
+}
+```
+
+### Ruby on Rails 3.x
+
+...or any framework that embeds some digest/hash to the asset URLs based on the contents, e.g. `/images/image-{hash1}.jpg`.
+
+The problem with this is that the high-resolution version would have a different hash, and would not conform the usual pattern, i.e. `/images/image@2x-{hash2}.jpg`. So automatic detection would fail because retina.js would check the existence of `/images/image-{hash1}@2x.jpg`.
+
+There's no way for retina.js to know beforehand what the high-resolution image's hash would be without some sort of help from the server side. So in this case, the suggested method is to supply the high-resolution URLs using the `data-at2x` attributes as previously described in the How It Works section.
+
+In Rails, one way to automate this is using a helper, e.g.:
+
+```ruby
+# in app/helpers/some_helper.rb or app/helpers/application_helper.rb
+def image_tag_with_at2x(name_at_1x, options={})
+ name_at_2x = name_at_1x.gsub(%r{\.\w+$}, '@2x\0')
+ image_tag(name_at_1x, options.merge("data-at2x" => asset_path(name_at_2x)))
+end
+```
+
+And then in your views (templates), instead of using image_tag, you would use image_tag_with_at2x, e.g. for ERB:
+
+```erb
+<%= image_tag_with_at2x "logo.png" %>
+```
+
+It would generate something like:
+
+```html
+ +```
+
+## How to test
+
+We use [mocha](http://visionmedia.github.com/mocha/) for unit testing with [should](https://github.com/visionmedia/should.js) assertions. Install mocha and should by running `npm install`.
+
+To run the test suite:
+
+``` bash
+$ npm test
+```
+
+Use [http-server](https://github.com/nodeapps/http-server) for node.js to test it. To install, run `npm install -g http-server`.
+
+If you've updated `retina.js` be sure to copy it from `src/retina.js` to `test/functional/public/retina.js`.
+
+To start the server, run:
+
+``` bash
+$ cd test/functional && http-server
+```
+
+Then navigate your browser to [http://localhost:8080](http://localhost:8080)
+
+After that, open up `test/functional/public/index.html` in your editor, and try commenting out the line that spoofs retina support, and reloading it.
diff --git a/assets/vendor/retinajs/package.json b/assets/vendor/retinajs/package.json
new file mode 100644
index 0000000000..f35dc1796f
--- /dev/null
+++ b/assets/vendor/retinajs/package.json
@@ -0,0 +1,13 @@
+{
+ "name": "retina.js",
+ "version": "1.1.0",
+ "devDependencies": {
+ "mocha": "*",
+ "should": "*",
+ "less": "*"
+ },
+ "main": "./src/retina",
+ "scripts": {
+ "test": "mocha"
+ }
+}
diff --git a/assets/vendor/retinajs/src/retina.js b/assets/vendor/retinajs/src/retina.js
new file mode 100644
index 0000000000..c948b7f4f0
--- /dev/null
+++ b/assets/vendor/retinajs/src/retina.js
@@ -0,0 +1,143 @@
+(function() {
+
+ var root = (typeof exports == 'undefined' ? window : exports);
+
+ var config = {
+ // Ensure Content-Type is an image before trying to load @2x image
+ // https://github.com/imulus/retinajs/pull/45)
+ check_mime_type: true
+ };
+
+
+
+ root.Retina = Retina;
+
+ function Retina() {}
+
+ Retina.configure = function(options) {
+ if (options == null) options = {};
+ for (var prop in options) config[prop] = options[prop];
+ };
+
+ Retina.init = function(context) {
+ if (context == null) context = root;
+
+ var existing_onload = context.onload || new Function;
+
+ context.onload = function() {
+ var images = document.getElementsByTagName("img"), retinaImages = [], i, image;
+ for (i = 0; i < images.length; i++) {
+ image = images[i];
+ retinaImages.push(new RetinaImage(image));
+ }
+ existing_onload();
+ }
+ };
+
+ Retina.isRetina = function(){
+ var mediaQuery = "(-webkit-min-device-pixel-ratio: 1.5),\
+ (min--moz-device-pixel-ratio: 1.5),\
+ (-o-min-device-pixel-ratio: 3/2),\
+ (min-resolution: 1.5dppx)";
+
+ if (root.devicePixelRatio > 1)
+ return true;
+
+ if (root.matchMedia && root.matchMedia(mediaQuery).matches)
+ return true;
+
+ return false;
+ };
+
+
+ root.RetinaImagePath = RetinaImagePath;
+
+ function RetinaImagePath(path, at_2x_path) {
+ this.path = path;
+ if (typeof at_2x_path !== "undefined" && at_2x_path !== null) {
+ this.at_2x_path = at_2x_path;
+ this.perform_check = false;
+ } else {
+ this.at_2x_path = path.replace(/\.\w+$/, function(match) { return "@2x" + match; });
+ this.perform_check = true;
+ }
+ }
+
+ RetinaImagePath.confirmed_paths = [];
+
+ RetinaImagePath.prototype.is_external = function() {
+ return !!(this.path.match(/^https?\:/i) && !this.path.match('//' + document.domain) )
+ }
+
+ RetinaImagePath.prototype.check_2x_variant = function(callback) {
+ var http, that = this;
+ if (this.is_external()) {
+ return callback(false);
+ } else if (!this.perform_check && typeof this.at_2x_path !== "undefined" && this.at_2x_path !== null) {
+ return callback(true);
+ } else if (this.at_2x_path in RetinaImagePath.confirmed_paths) {
+ return callback(true);
+ } else {
+ http = new XMLHttpRequest;
+ http.open('HEAD', this.at_2x_path);
+ http.onreadystatechange = function() {
+ if (http.readyState != 4) {
+ return callback(false);
+ }
+
+ if (http.status >= 200 && http.status <= 399) {
+ if (config.check_mime_type) {
+ var type = http.getResponseHeader('Content-Type');
+ if (type == null || !type.match(/^image/i)) {
+ return callback(false);
+ }
+ }
+
+ RetinaImagePath.confirmed_paths.push(that.at_2x_path);
+ return callback(true);
+ } else {
+ return callback(false);
+ }
+ }
+ http.send();
+ }
+ }
+
+
+
+ function RetinaImage(el) {
+ this.el = el;
+ this.path = new RetinaImagePath(this.el.getAttribute('src'), this.el.getAttribute('data-at2x'));
+ var that = this;
+ this.path.check_2x_variant(function(hasVariant) {
+ if (hasVariant) that.swap();
+ });
+ }
+
+ root.RetinaImage = RetinaImage;
+
+ RetinaImage.prototype.swap = function(path) {
+ if (typeof path == 'undefined') path = this.path.at_2x_path;
+
+ var that = this;
+ function load() {
+ if (! that.el.complete) {
+ setTimeout(load, 5);
+ } else {
+ that.el.setAttribute('width', that.el.offsetWidth);
+ that.el.setAttribute('height', that.el.offsetHeight);
+ that.el.setAttribute('src', path);
+ }
+ }
+ load();
+ }
+
+
+
+
+ if (Retina.isRetina()) {
+ Retina.init(root);
+ }
+
+})();
+
diff --git a/assets/vendor/retinajs/src/retina.less b/assets/vendor/retinajs/src/retina.less
new file mode 100644
index 0000000000..3b96a416cd
--- /dev/null
+++ b/assets/vendor/retinajs/src/retina.less
@@ -0,0 +1,14 @@
+// retina.less
+// A helper mixin for applying high-resolution background images (http://www.retinajs.com)
+
+@highdpi: ~"(-webkit-min-device-pixel-ratio: 1.5), (min--moz-device-pixel-ratio: 1.5), (-o-min-device-pixel-ratio: 3/2), (min-resolution: 1.5dppx)";
+
+.at2x(@path, @w: auto, @h: auto) {
+ background-image: url(@path);
+ @at2x_path: ~`@{path}.replace(/\.\w+$/, function(match) { return "@2x" + match; })`;
+
+ @media @highdpi {
+ background-image: url("@{at2x_path}");
+ background-size: @w @h;
+ }
+}
diff --git a/assets/vendor/retinajs/test/fixtures/desired_output.css b/assets/vendor/retinajs/test/fixtures/desired_output.css
new file mode 100644
index 0000000000..493c281363
--- /dev/null
+++ b/assets/vendor/retinajs/test/fixtures/desired_output.css
@@ -0,0 +1,18 @@
+body {
+ background-image: url('/path/to/image.png');
+}
+@media (-webkit-min-device-pixel-ratio: 1.5), (min--moz-device-pixel-ratio: 1.5), (-o-min-device-pixel-ratio: 3/2), (min-resolution: 1.5dppx) {
+ body {
+ background-image: url("/path/to/image@2x.png");
+ background-size: 200px 100px;
+ }
+}
+header {
+ background-image: url("/path/to/header.png");
+}
+@media (-webkit-min-device-pixel-ratio: 1.5), (min--moz-device-pixel-ratio: 1.5), (-o-min-device-pixel-ratio: 3/2), (min-resolution: 1.5dppx) {
+ header {
+ background-image: url("/path/to/header@2x.png");
+ background-size: 600px 50px;
+ }
+}
diff --git a/assets/vendor/retinajs/test/fixtures/image.js b/assets/vendor/retinajs/test/fixtures/image.js
new file mode 100644
index 0000000000..976b56be8f
--- /dev/null
+++ b/assets/vendor/retinajs/test/fixtures/image.js
@@ -0,0 +1,19 @@
+function Image() {
+ this.complete = true;
+ this.attributes = {
+ src : "/images/some_image.png",
+ offsetWidth : 500,
+ offsetHeight : 400
+ };
+}
+
+Image.prototype.setAttribute = function(name, value) {
+ this.attributes[name] = value;
+}
+
+Image.prototype.getAttribute = function(name) {
+ return this.attributes[name];
+}
+
+var root = (exports || window);
+root.Image = Image;
diff --git a/assets/vendor/retinajs/test/fixtures/test.less b/assets/vendor/retinajs/test/fixtures/test.less
new file mode 100644
index 0000000000..47e13f7533
--- /dev/null
+++ b/assets/vendor/retinajs/test/fixtures/test.less
@@ -0,0 +1,10 @@
+@import 'src/retina';
+
+// Single quoted
+body {
+ .at2x('/path/to/image.png', 200px, 100px);
+}
+// Double quoted
+header {
+ .at2x("/path/to/header.png", 600px, 50px);
+}
diff --git a/assets/vendor/retinajs/test/fixtures/xml_http_request.js b/assets/vendor/retinajs/test/fixtures/xml_http_request.js
new file mode 100644
index 0000000000..7c26b1cab7
--- /dev/null
+++ b/assets/vendor/retinajs/test/fixtures/xml_http_request.js
@@ -0,0 +1,24 @@
+function XMLHttpRequest() {
+ this.status = XMLHttpRequest.status;
+ this.contentType = XMLHttpRequest.contentType;
+ this.readyState = 4;
+ this.onreadystatechange = function() {}
+}
+
+XMLHttpRequest.status = 200;
+XMLHttpRequest.contentType = 'image/png';
+
+XMLHttpRequest.prototype.open = function() {
+ return true;
+}
+
+XMLHttpRequest.prototype.send = function() {
+ this.onreadystatechange();
+}
+
+XMLHttpRequest.prototype.getResponseHeader = function(contentType) {
+ return this.contentType;
+}
+
+var root = (exports || window);
+root.XMLHttpRequest = XMLHttpRequest;
diff --git a/assets/vendor/retinajs/test/functional/public/google.png b/assets/vendor/retinajs/test/functional/public/google.png
new file mode 100644
index 0000000000..533d2b2737
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/google.png differ
diff --git a/assets/vendor/retinajs/test/functional/public/google@1x.png b/assets/vendor/retinajs/test/functional/public/google@1x.png
new file mode 100644
index 0000000000..533d2b2737
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/google@1x.png differ
diff --git a/assets/vendor/retinajs/test/functional/public/google@2x.png b/assets/vendor/retinajs/test/functional/public/google@2x.png
new file mode 100644
index 0000000000..99b37d55bf
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/google@2x.png differ
diff --git a/assets/vendor/retinajs/test/functional/public/index.html b/assets/vendor/retinajs/test/functional/public/index.html
new file mode 100644
index 0000000000..8dc85f57fd
--- /dev/null
+++ b/assets/vendor/retinajs/test/functional/public/index.html
@@ -0,0 +1,39 @@
+
+
+
+
+
+
+
+
+
+```
+
+## How to test
+
+We use [mocha](http://visionmedia.github.com/mocha/) for unit testing with [should](https://github.com/visionmedia/should.js) assertions. Install mocha and should by running `npm install`.
+
+To run the test suite:
+
+``` bash
+$ npm test
+```
+
+Use [http-server](https://github.com/nodeapps/http-server) for node.js to test it. To install, run `npm install -g http-server`.
+
+If you've updated `retina.js` be sure to copy it from `src/retina.js` to `test/functional/public/retina.js`.
+
+To start the server, run:
+
+``` bash
+$ cd test/functional && http-server
+```
+
+Then navigate your browser to [http://localhost:8080](http://localhost:8080)
+
+After that, open up `test/functional/public/index.html` in your editor, and try commenting out the line that spoofs retina support, and reloading it.
diff --git a/assets/vendor/retinajs/package.json b/assets/vendor/retinajs/package.json
new file mode 100644
index 0000000000..f35dc1796f
--- /dev/null
+++ b/assets/vendor/retinajs/package.json
@@ -0,0 +1,13 @@
+{
+ "name": "retina.js",
+ "version": "1.1.0",
+ "devDependencies": {
+ "mocha": "*",
+ "should": "*",
+ "less": "*"
+ },
+ "main": "./src/retina",
+ "scripts": {
+ "test": "mocha"
+ }
+}
diff --git a/assets/vendor/retinajs/src/retina.js b/assets/vendor/retinajs/src/retina.js
new file mode 100644
index 0000000000..c948b7f4f0
--- /dev/null
+++ b/assets/vendor/retinajs/src/retina.js
@@ -0,0 +1,143 @@
+(function() {
+
+ var root = (typeof exports == 'undefined' ? window : exports);
+
+ var config = {
+ // Ensure Content-Type is an image before trying to load @2x image
+ // https://github.com/imulus/retinajs/pull/45)
+ check_mime_type: true
+ };
+
+
+
+ root.Retina = Retina;
+
+ function Retina() {}
+
+ Retina.configure = function(options) {
+ if (options == null) options = {};
+ for (var prop in options) config[prop] = options[prop];
+ };
+
+ Retina.init = function(context) {
+ if (context == null) context = root;
+
+ var existing_onload = context.onload || new Function;
+
+ context.onload = function() {
+ var images = document.getElementsByTagName("img"), retinaImages = [], i, image;
+ for (i = 0; i < images.length; i++) {
+ image = images[i];
+ retinaImages.push(new RetinaImage(image));
+ }
+ existing_onload();
+ }
+ };
+
+ Retina.isRetina = function(){
+ var mediaQuery = "(-webkit-min-device-pixel-ratio: 1.5),\
+ (min--moz-device-pixel-ratio: 1.5),\
+ (-o-min-device-pixel-ratio: 3/2),\
+ (min-resolution: 1.5dppx)";
+
+ if (root.devicePixelRatio > 1)
+ return true;
+
+ if (root.matchMedia && root.matchMedia(mediaQuery).matches)
+ return true;
+
+ return false;
+ };
+
+
+ root.RetinaImagePath = RetinaImagePath;
+
+ function RetinaImagePath(path, at_2x_path) {
+ this.path = path;
+ if (typeof at_2x_path !== "undefined" && at_2x_path !== null) {
+ this.at_2x_path = at_2x_path;
+ this.perform_check = false;
+ } else {
+ this.at_2x_path = path.replace(/\.\w+$/, function(match) { return "@2x" + match; });
+ this.perform_check = true;
+ }
+ }
+
+ RetinaImagePath.confirmed_paths = [];
+
+ RetinaImagePath.prototype.is_external = function() {
+ return !!(this.path.match(/^https?\:/i) && !this.path.match('//' + document.domain) )
+ }
+
+ RetinaImagePath.prototype.check_2x_variant = function(callback) {
+ var http, that = this;
+ if (this.is_external()) {
+ return callback(false);
+ } else if (!this.perform_check && typeof this.at_2x_path !== "undefined" && this.at_2x_path !== null) {
+ return callback(true);
+ } else if (this.at_2x_path in RetinaImagePath.confirmed_paths) {
+ return callback(true);
+ } else {
+ http = new XMLHttpRequest;
+ http.open('HEAD', this.at_2x_path);
+ http.onreadystatechange = function() {
+ if (http.readyState != 4) {
+ return callback(false);
+ }
+
+ if (http.status >= 200 && http.status <= 399) {
+ if (config.check_mime_type) {
+ var type = http.getResponseHeader('Content-Type');
+ if (type == null || !type.match(/^image/i)) {
+ return callback(false);
+ }
+ }
+
+ RetinaImagePath.confirmed_paths.push(that.at_2x_path);
+ return callback(true);
+ } else {
+ return callback(false);
+ }
+ }
+ http.send();
+ }
+ }
+
+
+
+ function RetinaImage(el) {
+ this.el = el;
+ this.path = new RetinaImagePath(this.el.getAttribute('src'), this.el.getAttribute('data-at2x'));
+ var that = this;
+ this.path.check_2x_variant(function(hasVariant) {
+ if (hasVariant) that.swap();
+ });
+ }
+
+ root.RetinaImage = RetinaImage;
+
+ RetinaImage.prototype.swap = function(path) {
+ if (typeof path == 'undefined') path = this.path.at_2x_path;
+
+ var that = this;
+ function load() {
+ if (! that.el.complete) {
+ setTimeout(load, 5);
+ } else {
+ that.el.setAttribute('width', that.el.offsetWidth);
+ that.el.setAttribute('height', that.el.offsetHeight);
+ that.el.setAttribute('src', path);
+ }
+ }
+ load();
+ }
+
+
+
+
+ if (Retina.isRetina()) {
+ Retina.init(root);
+ }
+
+})();
+
diff --git a/assets/vendor/retinajs/src/retina.less b/assets/vendor/retinajs/src/retina.less
new file mode 100644
index 0000000000..3b96a416cd
--- /dev/null
+++ b/assets/vendor/retinajs/src/retina.less
@@ -0,0 +1,14 @@
+// retina.less
+// A helper mixin for applying high-resolution background images (http://www.retinajs.com)
+
+@highdpi: ~"(-webkit-min-device-pixel-ratio: 1.5), (min--moz-device-pixel-ratio: 1.5), (-o-min-device-pixel-ratio: 3/2), (min-resolution: 1.5dppx)";
+
+.at2x(@path, @w: auto, @h: auto) {
+ background-image: url(@path);
+ @at2x_path: ~`@{path}.replace(/\.\w+$/, function(match) { return "@2x" + match; })`;
+
+ @media @highdpi {
+ background-image: url("@{at2x_path}");
+ background-size: @w @h;
+ }
+}
diff --git a/assets/vendor/retinajs/test/fixtures/desired_output.css b/assets/vendor/retinajs/test/fixtures/desired_output.css
new file mode 100644
index 0000000000..493c281363
--- /dev/null
+++ b/assets/vendor/retinajs/test/fixtures/desired_output.css
@@ -0,0 +1,18 @@
+body {
+ background-image: url('/path/to/image.png');
+}
+@media (-webkit-min-device-pixel-ratio: 1.5), (min--moz-device-pixel-ratio: 1.5), (-o-min-device-pixel-ratio: 3/2), (min-resolution: 1.5dppx) {
+ body {
+ background-image: url("/path/to/image@2x.png");
+ background-size: 200px 100px;
+ }
+}
+header {
+ background-image: url("/path/to/header.png");
+}
+@media (-webkit-min-device-pixel-ratio: 1.5), (min--moz-device-pixel-ratio: 1.5), (-o-min-device-pixel-ratio: 3/2), (min-resolution: 1.5dppx) {
+ header {
+ background-image: url("/path/to/header@2x.png");
+ background-size: 600px 50px;
+ }
+}
diff --git a/assets/vendor/retinajs/test/fixtures/image.js b/assets/vendor/retinajs/test/fixtures/image.js
new file mode 100644
index 0000000000..976b56be8f
--- /dev/null
+++ b/assets/vendor/retinajs/test/fixtures/image.js
@@ -0,0 +1,19 @@
+function Image() {
+ this.complete = true;
+ this.attributes = {
+ src : "/images/some_image.png",
+ offsetWidth : 500,
+ offsetHeight : 400
+ };
+}
+
+Image.prototype.setAttribute = function(name, value) {
+ this.attributes[name] = value;
+}
+
+Image.prototype.getAttribute = function(name) {
+ return this.attributes[name];
+}
+
+var root = (exports || window);
+root.Image = Image;
diff --git a/assets/vendor/retinajs/test/fixtures/test.less b/assets/vendor/retinajs/test/fixtures/test.less
new file mode 100644
index 0000000000..47e13f7533
--- /dev/null
+++ b/assets/vendor/retinajs/test/fixtures/test.less
@@ -0,0 +1,10 @@
+@import 'src/retina';
+
+// Single quoted
+body {
+ .at2x('/path/to/image.png', 200px, 100px);
+}
+// Double quoted
+header {
+ .at2x("/path/to/header.png", 600px, 50px);
+}
diff --git a/assets/vendor/retinajs/test/fixtures/xml_http_request.js b/assets/vendor/retinajs/test/fixtures/xml_http_request.js
new file mode 100644
index 0000000000..7c26b1cab7
--- /dev/null
+++ b/assets/vendor/retinajs/test/fixtures/xml_http_request.js
@@ -0,0 +1,24 @@
+function XMLHttpRequest() {
+ this.status = XMLHttpRequest.status;
+ this.contentType = XMLHttpRequest.contentType;
+ this.readyState = 4;
+ this.onreadystatechange = function() {}
+}
+
+XMLHttpRequest.status = 200;
+XMLHttpRequest.contentType = 'image/png';
+
+XMLHttpRequest.prototype.open = function() {
+ return true;
+}
+
+XMLHttpRequest.prototype.send = function() {
+ this.onreadystatechange();
+}
+
+XMLHttpRequest.prototype.getResponseHeader = function(contentType) {
+ return this.contentType;
+}
+
+var root = (exports || window);
+root.XMLHttpRequest = XMLHttpRequest;
diff --git a/assets/vendor/retinajs/test/functional/public/google.png b/assets/vendor/retinajs/test/functional/public/google.png
new file mode 100644
index 0000000000..533d2b2737
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/google.png differ
diff --git a/assets/vendor/retinajs/test/functional/public/google@1x.png b/assets/vendor/retinajs/test/functional/public/google@1x.png
new file mode 100644
index 0000000000..533d2b2737
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/google@1x.png differ
diff --git a/assets/vendor/retinajs/test/functional/public/google@2x.png b/assets/vendor/retinajs/test/functional/public/google@2x.png
new file mode 100644
index 0000000000..99b37d55bf
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/google@2x.png differ
diff --git a/assets/vendor/retinajs/test/functional/public/index.html b/assets/vendor/retinajs/test/functional/public/index.html
new file mode 100644
index 0000000000..8dc85f57fd
--- /dev/null
+++ b/assets/vendor/retinajs/test/functional/public/index.html
@@ -0,0 +1,39 @@
+
+
+
+
+
+
+
+
+  +
+  +
+  +
+  +
+
+
+  +
+  +
+  +
+
+
+
diff --git a/assets/vendor/retinajs/test/functional/public/ipad_hero.jpeg b/assets/vendor/retinajs/test/functional/public/ipad_hero.jpeg
new file mode 100644
index 0000000000..40943cb679
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/ipad_hero.jpeg differ
diff --git a/assets/vendor/retinajs/test/functional/public/ipad_hero@1x.jpeg b/assets/vendor/retinajs/test/functional/public/ipad_hero@1x.jpeg
new file mode 100644
index 0000000000..40943cb679
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/ipad_hero@1x.jpeg differ
diff --git a/assets/vendor/retinajs/test/functional/public/ipad_hero@2x.jpeg b/assets/vendor/retinajs/test/functional/public/ipad_hero@2x.jpeg
new file mode 100644
index 0000000000..da7a1709d4
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/ipad_hero@2x.jpeg differ
diff --git a/assets/vendor/retinajs/test/mocha.opts b/assets/vendor/retinajs/test/mocha.opts
new file mode 100644
index 0000000000..24d45f5902
--- /dev/null
+++ b/assets/vendor/retinajs/test/mocha.opts
@@ -0,0 +1,3 @@
+--require should
+--slow 20
+--growl
diff --git a/assets/vendor/retinajs/test/retina.test.js b/assets/vendor/retinajs/test/retina.test.js
new file mode 100644
index 0000000000..6dc3ad4934
--- /dev/null
+++ b/assets/vendor/retinajs/test/retina.test.js
@@ -0,0 +1,36 @@
+// Create a document object because we don't have one
+// in our Node test environment
+delete global.document;
+global.document = {};
+
+var Retina = require('../').Retina;
+
+describe('Retina', function() {
+
+ before(function(){
+ // stub out the getElementsByTagName method
+ global.document = {
+ getElementsByTagName : function(){
+ return [];
+ }
+ }
+ });
+
+ describe('init', function(){
+ it('stashes the existing onload and executes it later', function(){
+ var existingOnloadExecutions = 0;
+ var window = {
+ matchMedia : function() {
+ return { matches: false }
+ },
+ onload : function() {
+ existingOnloadExecutions++;
+ }
+ };
+ Retina.init(window);
+ window.onload();
+ existingOnloadExecutions.should.equal(1);
+ });
+ });
+
+});
diff --git a/assets/vendor/retinajs/test/retina_image_path.test.js b/assets/vendor/retinajs/test/retina_image_path.test.js
new file mode 100644
index 0000000000..439d711b4a
--- /dev/null
+++ b/assets/vendor/retinajs/test/retina_image_path.test.js
@@ -0,0 +1,195 @@
+// Create a document object because we don't have one
+// in our Node test environment
+delete global.document;
+global.document = {};
+global.Image = require('./fixtures/image').Image;
+global.XMLHttpRequest = require('./fixtures/xml_http_request').XMLHttpRequest;
+
+global.exports = {
+ devicePixelRatio : 0.9,
+ matchMedia : function() {
+ return {
+ matches : false
+ }
+ }
+}
+
+var Retina = require('../').Retina;
+var RetinaImage = require('../').RetinaImage;
+var RetinaImagePath = require('../').RetinaImagePath;
+
+describe('RetinaImagePath', function() {
+ var path = null;
+
+ before(function(){
+ global.document = {domain: null};
+ });
+
+ describe('@at_2x_path', function(){
+ it('adds "@2x" before the extension', function(){
+ path = new RetinaImagePath("/path/to/image.png");
+ path.at_2x_path.should.equal("/path/to/image@2x.png");
+ });
+
+ it('uses data-@2x when supplied', function(){
+ path = new RetinaImagePath("/path/to/image-hash1.png", "/path/to/image@2x-hash2.png");
+ path.at_2x_path.should.equal("/path/to/image@2x-hash2.png");
+ });
+ });
+
+ describe('#is_external()', function() {
+ it('should return true when image path references a remote domain with www', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://www.google.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path references a remote domain without www', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://google.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path references a remote domain with https', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("https://google.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path is a remote domain with www and domain is localhost', function() {
+ document.domain = "localhost";
+ path = new RetinaImagePath("http://www.google.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path is a remote domain without www and domain is localhost', function() {
+ document.domain = "localhost"
+ path = new RetinaImagePath("http://google.com/images/some_image.png")
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path has www and domain does not', function() {
+ document.domain = "apple.com";
+ path = new RetinaImagePath("http://www.apple.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path does not have www and domain does', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://apple.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return false when image path is relative with www', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("/images/some_image.png");
+ path.is_external().should.equal(false);
+ });
+
+ it('should return false when image path is relative without www', function() {
+ document.domain = "apple.com";
+ path = new RetinaImagePath("/images/some_image.png");
+ path.is_external().should.equal(false);
+ });
+
+ it('should return false when image path is relative to localhost', function() {
+ document.domain = "localhost";
+ path = new RetinaImagePath("/images/some_image.png");
+ path.is_external().should.equal(false);
+ });
+
+ it('should return false when image path has same domain as current site with www', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://www.apple.com/images/some_image.png");
+ path.is_external().should.equal(false);
+ });
+ });
+
+ describe('#check_2x_variant()', function() {
+ it('should callback with false when #is_external() is true', function(done) {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://google.com/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(false);
+ done();
+ });
+ });
+
+ it('should callback with true when at2x is supplied', function(done) {
+ path = new RetinaImagePath("/images/some_image.png", "/images/some_image@100x.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(true);
+ done();
+ });
+ });
+
+ it('should callback with false when remote at2x image does not exist', function(done) {
+ XMLHttpRequest.status = 404; // simulate a failing request
+ XMLHttpRequest.contentType = 'image/png'; // simulate a proper content type
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(false);
+ done();
+ });
+ });
+
+ it('should callback with false when content-type is not an image type', function(done) {
+ XMLHttpRequest.status = 200; // simulate a an image request that comes back OK
+ XMLHttpRequest.contentType = 'text/html'; // but is actually an improperly coded 404 page
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(false);
+ done();
+ });
+ });
+
+ it('should callback with true when content-type is wrong, but check_mime_type is false', function(done) {
+ XMLHttpRequest.status = 200; // simulate a proper request
+ XMLHttpRequest.contentType = 'text/html'; // but with an incorrect content type
+
+ Retina.configure({
+ check_mime_type: false // but ignore it
+ });
+
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(true);
+
+ Retina.configure({
+ check_mime_type: true
+ });
+
+ done();
+ });
+ });
+
+ it('should callback with true when remote at2x image exists', function(done) {
+ XMLHttpRequest.status = 200; // simulate a proper request
+ XMLHttpRequest.contentType = 'image/png'; // simulate a proper content type
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(true);
+ done();
+ });
+ });
+
+ it('should add path to cache when at2x image exists', function(done) {
+ XMLHttpRequest.status = 200; // simulate a proper request
+ XMLHttpRequest.contentType = 'image/png'; // simulate a proper content type
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ RetinaImagePath.confirmed_paths.should.include(path.at_2x_path);
+ done();
+ });
+ });
+
+ it('should return true when the at2x image path has already been checked and confirmed', function(done) {
+ RetinaImagePath.confirmed_paths = ['/images/some_image@2x.png']
+ path = new RetinaImagePath("/images/some_image.png")
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(true);
+ done();
+ });
+ });
+ });
+});
diff --git a/assets/vendor/retinajs/test/retina_less.test.js b/assets/vendor/retinajs/test/retina_less.test.js
new file mode 100644
index 0000000000..7268ab14e4
--- /dev/null
+++ b/assets/vendor/retinajs/test/retina_less.test.js
@@ -0,0 +1,17 @@
+var fs = require('fs');
+var less = require('less');
+
+describe('retina.less', function() {
+
+ describe('.at2x()', function(){
+ it('compiles correctly', function(done){
+ var desired_output = fs.readFileSync('test/fixtures/desired_output.css', 'utf8');
+ var input = fs.readFileSync('test/fixtures/test.less', 'utf8');
+ less.render(input, function (e, actual_output) {
+ actual_output.should.equal(desired_output);
+ done();
+ });
+ });
+ });
+
+});
diff --git a/bower.json b/bower.json
new file mode 100644
index 0000000000..d2ddf6b081
--- /dev/null
+++ b/bower.json
@@ -0,0 +1,8 @@
+{
+ "name": "developer.github.com",
+ "dependencies": {
+ "lunr.js": "0.6.0",
+ "octicons": "3.0.1",
+ "retinajs": "1.1.0"
+ }
+}
diff --git a/changes.atom b/changes.atom
deleted file mode 100644
index 502617e422..0000000000
--- a/changes.atom
+++ /dev/null
@@ -1,1201 +0,0 @@
-
-
+
+
+
+
diff --git a/assets/vendor/retinajs/test/functional/public/ipad_hero.jpeg b/assets/vendor/retinajs/test/functional/public/ipad_hero.jpeg
new file mode 100644
index 0000000000..40943cb679
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/ipad_hero.jpeg differ
diff --git a/assets/vendor/retinajs/test/functional/public/ipad_hero@1x.jpeg b/assets/vendor/retinajs/test/functional/public/ipad_hero@1x.jpeg
new file mode 100644
index 0000000000..40943cb679
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/ipad_hero@1x.jpeg differ
diff --git a/assets/vendor/retinajs/test/functional/public/ipad_hero@2x.jpeg b/assets/vendor/retinajs/test/functional/public/ipad_hero@2x.jpeg
new file mode 100644
index 0000000000..da7a1709d4
Binary files /dev/null and b/assets/vendor/retinajs/test/functional/public/ipad_hero@2x.jpeg differ
diff --git a/assets/vendor/retinajs/test/mocha.opts b/assets/vendor/retinajs/test/mocha.opts
new file mode 100644
index 0000000000..24d45f5902
--- /dev/null
+++ b/assets/vendor/retinajs/test/mocha.opts
@@ -0,0 +1,3 @@
+--require should
+--slow 20
+--growl
diff --git a/assets/vendor/retinajs/test/retina.test.js b/assets/vendor/retinajs/test/retina.test.js
new file mode 100644
index 0000000000..6dc3ad4934
--- /dev/null
+++ b/assets/vendor/retinajs/test/retina.test.js
@@ -0,0 +1,36 @@
+// Create a document object because we don't have one
+// in our Node test environment
+delete global.document;
+global.document = {};
+
+var Retina = require('../').Retina;
+
+describe('Retina', function() {
+
+ before(function(){
+ // stub out the getElementsByTagName method
+ global.document = {
+ getElementsByTagName : function(){
+ return [];
+ }
+ }
+ });
+
+ describe('init', function(){
+ it('stashes the existing onload and executes it later', function(){
+ var existingOnloadExecutions = 0;
+ var window = {
+ matchMedia : function() {
+ return { matches: false }
+ },
+ onload : function() {
+ existingOnloadExecutions++;
+ }
+ };
+ Retina.init(window);
+ window.onload();
+ existingOnloadExecutions.should.equal(1);
+ });
+ });
+
+});
diff --git a/assets/vendor/retinajs/test/retina_image_path.test.js b/assets/vendor/retinajs/test/retina_image_path.test.js
new file mode 100644
index 0000000000..439d711b4a
--- /dev/null
+++ b/assets/vendor/retinajs/test/retina_image_path.test.js
@@ -0,0 +1,195 @@
+// Create a document object because we don't have one
+// in our Node test environment
+delete global.document;
+global.document = {};
+global.Image = require('./fixtures/image').Image;
+global.XMLHttpRequest = require('./fixtures/xml_http_request').XMLHttpRequest;
+
+global.exports = {
+ devicePixelRatio : 0.9,
+ matchMedia : function() {
+ return {
+ matches : false
+ }
+ }
+}
+
+var Retina = require('../').Retina;
+var RetinaImage = require('../').RetinaImage;
+var RetinaImagePath = require('../').RetinaImagePath;
+
+describe('RetinaImagePath', function() {
+ var path = null;
+
+ before(function(){
+ global.document = {domain: null};
+ });
+
+ describe('@at_2x_path', function(){
+ it('adds "@2x" before the extension', function(){
+ path = new RetinaImagePath("/path/to/image.png");
+ path.at_2x_path.should.equal("/path/to/image@2x.png");
+ });
+
+ it('uses data-@2x when supplied', function(){
+ path = new RetinaImagePath("/path/to/image-hash1.png", "/path/to/image@2x-hash2.png");
+ path.at_2x_path.should.equal("/path/to/image@2x-hash2.png");
+ });
+ });
+
+ describe('#is_external()', function() {
+ it('should return true when image path references a remote domain with www', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://www.google.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path references a remote domain without www', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://google.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path references a remote domain with https', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("https://google.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path is a remote domain with www and domain is localhost', function() {
+ document.domain = "localhost";
+ path = new RetinaImagePath("http://www.google.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path is a remote domain without www and domain is localhost', function() {
+ document.domain = "localhost"
+ path = new RetinaImagePath("http://google.com/images/some_image.png")
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path has www and domain does not', function() {
+ document.domain = "apple.com";
+ path = new RetinaImagePath("http://www.apple.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return true when image path does not have www and domain does', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://apple.com/images/some_image.png");
+ path.is_external().should.equal(true);
+ });
+
+ it('should return false when image path is relative with www', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("/images/some_image.png");
+ path.is_external().should.equal(false);
+ });
+
+ it('should return false when image path is relative without www', function() {
+ document.domain = "apple.com";
+ path = new RetinaImagePath("/images/some_image.png");
+ path.is_external().should.equal(false);
+ });
+
+ it('should return false when image path is relative to localhost', function() {
+ document.domain = "localhost";
+ path = new RetinaImagePath("/images/some_image.png");
+ path.is_external().should.equal(false);
+ });
+
+ it('should return false when image path has same domain as current site with www', function() {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://www.apple.com/images/some_image.png");
+ path.is_external().should.equal(false);
+ });
+ });
+
+ describe('#check_2x_variant()', function() {
+ it('should callback with false when #is_external() is true', function(done) {
+ document.domain = "www.apple.com";
+ path = new RetinaImagePath("http://google.com/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(false);
+ done();
+ });
+ });
+
+ it('should callback with true when at2x is supplied', function(done) {
+ path = new RetinaImagePath("/images/some_image.png", "/images/some_image@100x.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(true);
+ done();
+ });
+ });
+
+ it('should callback with false when remote at2x image does not exist', function(done) {
+ XMLHttpRequest.status = 404; // simulate a failing request
+ XMLHttpRequest.contentType = 'image/png'; // simulate a proper content type
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(false);
+ done();
+ });
+ });
+
+ it('should callback with false when content-type is not an image type', function(done) {
+ XMLHttpRequest.status = 200; // simulate a an image request that comes back OK
+ XMLHttpRequest.contentType = 'text/html'; // but is actually an improperly coded 404 page
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(false);
+ done();
+ });
+ });
+
+ it('should callback with true when content-type is wrong, but check_mime_type is false', function(done) {
+ XMLHttpRequest.status = 200; // simulate a proper request
+ XMLHttpRequest.contentType = 'text/html'; // but with an incorrect content type
+
+ Retina.configure({
+ check_mime_type: false // but ignore it
+ });
+
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(true);
+
+ Retina.configure({
+ check_mime_type: true
+ });
+
+ done();
+ });
+ });
+
+ it('should callback with true when remote at2x image exists', function(done) {
+ XMLHttpRequest.status = 200; // simulate a proper request
+ XMLHttpRequest.contentType = 'image/png'; // simulate a proper content type
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(true);
+ done();
+ });
+ });
+
+ it('should add path to cache when at2x image exists', function(done) {
+ XMLHttpRequest.status = 200; // simulate a proper request
+ XMLHttpRequest.contentType = 'image/png'; // simulate a proper content type
+ path = new RetinaImagePath("/images/some_image.png");
+ path.check_2x_variant(function(hasVariant) {
+ RetinaImagePath.confirmed_paths.should.include(path.at_2x_path);
+ done();
+ });
+ });
+
+ it('should return true when the at2x image path has already been checked and confirmed', function(done) {
+ RetinaImagePath.confirmed_paths = ['/images/some_image@2x.png']
+ path = new RetinaImagePath("/images/some_image.png")
+ path.check_2x_variant(function(hasVariant) {
+ hasVariant.should.equal(true);
+ done();
+ });
+ });
+ });
+});
diff --git a/assets/vendor/retinajs/test/retina_less.test.js b/assets/vendor/retinajs/test/retina_less.test.js
new file mode 100644
index 0000000000..7268ab14e4
--- /dev/null
+++ b/assets/vendor/retinajs/test/retina_less.test.js
@@ -0,0 +1,17 @@
+var fs = require('fs');
+var less = require('less');
+
+describe('retina.less', function() {
+
+ describe('.at2x()', function(){
+ it('compiles correctly', function(done){
+ var desired_output = fs.readFileSync('test/fixtures/desired_output.css', 'utf8');
+ var input = fs.readFileSync('test/fixtures/test.less', 'utf8');
+ less.render(input, function (e, actual_output) {
+ actual_output.should.equal(desired_output);
+ done();
+ });
+ });
+ });
+
+});
diff --git a/bower.json b/bower.json
new file mode 100644
index 0000000000..d2ddf6b081
--- /dev/null
+++ b/bower.json
@@ -0,0 +1,8 @@
+{
+ "name": "developer.github.com",
+ "dependencies": {
+ "lunr.js": "0.6.0",
+ "octicons": "3.0.1",
+ "retinajs": "1.1.0"
+ }
+}
diff --git a/changes.atom b/changes.atom
deleted file mode 100644
index 502617e422..0000000000
--- a/changes.atom
+++ /dev/null
@@ -1,1201 +0,0 @@
-
-Whoops, looks like that page doesn't exist.
+
-curl -i -u pengwynn \
- -d '{"name": "create-repo-test", "auto_init": true}' \
- https://api.github.com/user/repos
-
+``` command-line
+$ curl -i -u pengwynn \
+$ -d '{"name": "create-repo-test", "auto_init": true}' \
+$ https://api.github.com/user/repos
+```
The resulting repository will have a README stub and an initial commit.
-
+
### .gitignore templates
@@ -29,13 +27,12 @@
the basename of any template in the [GitHub gitignore templates
project](https://github.com/github/gitignore).
-
-curl -i -u pengwynn \
- -d '{"name": "create-repo-test", "auto_init": true, \
- "gitignore_template": "Haskell"}' \
- https://api.github.com/user/repos
-
-
+``` command-line
+$ curl -i -u pengwynn \
+$ -d '{"name": "create-repo-test", "auto_init": true, \
+$ "gitignore_template": "Haskell"}' \
+$ https://api.github.com/user/repos
+```
As the [docs point out](/v3/repos/#create), the `gitignore_template` parameter
is ignored if `auto_init` is not present and `true`.
@@ -47,4 +44,3 @@
[twitter]: https://twitter.com/githubapi
[email]: mailto:support@github.com
[c]: https://github.com/c
-
diff --git a/content/changes/2012-10-14-rate-limit-changes.html b/content/changes/2012-10-14-rate-limit-changes.html
index b33e2cf9bc..60aa94f4fa 100644
--- a/content/changes/2012-10-14-rate-limit-changes.html
+++ b/content/changes/2012-10-14-rate-limit-changes.html
@@ -1,7 +1,5 @@
---
-kind: change
title: Rate limit changes for unauthenticated requests
-created_at: 2012-10-14
author_name: pengwynn
---
@@ -11,7 +9,7 @@
[authenticate](http://developer.github.com/v3/#authentication) via Basic Auth
or OAuth. Unauthenticated requests will be limited to 60 per hour unless you
[include your OAuth client and
-secret](http://developer.github.com/v3/#unauthenticated-rate-limited-requests).
+secret](http://developer.github.com/v3/#increasing-the-unauthenticated-rate-limit-for-oauth-applications).
We'll soon require all requests to include a valid [User Agent
header](http://en.wikipedia.org/wiki/User_agent). Setting a
diff --git a/content/changes/2012-10-17-org-members-redirection.md b/content/changes/2012-10-17-org-members-redirection.md
index 6b8a3f54da..ace24c0173 100644
--- a/content/changes/2012-10-17-org-members-redirection.md
+++ b/content/changes/2012-10-17-org-members-redirection.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Organization Members Resource Changes
-created_at: 2012-10-17
author_name: pezra
---
diff --git a/content/changes/2012-10-24-set-default-branch.html b/content/changes/2012-10-24-set-default-branch.html
index 05bb456161..ac9800b41b 100644
--- a/content/changes/2012-10-24-set-default-branch.html
+++ b/content/changes/2012-10-24-set-default-branch.html
@@ -1,21 +1,19 @@
---
-kind: change
title: Set the default branch for a repository
-created_at: 2012-10-24
author_name: pengwynn
---
You can set the default branch for a repository to something other than 'master' from the GitHub repository admin screen:
-
+
Now, you can update this setting via the API. We've added a `default_branch` parameter to the [Edit Repository method][edit-repo]:
-
-curl -u pengwynn \
- -d '{"name": "octokit", "default_branch":"development"}' \
- https://api.github.com/repos/pengwynn/octokit
-
+``` command-line
+$ curl -u pengwynn \
+$ -d '{"name": "octokit", "default_branch":"development"}' \
+$ https://api.github.com/repos/octokit/octokit.rb
+```
If you provide a branch name that hasn't been pushed to GitHub, we'll gracefully fall back to `'master'` or the first branch.
diff --git a/content/changes/2012-10-26-notifications-api.md b/content/changes/2012-10-26-notifications-api.md
index 6d1e6bd3e4..db08698377 100644
--- a/content/changes/2012-10-26-notifications-api.md
+++ b/content/changes/2012-10-26-notifications-api.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Notifications API
-created_at: 2012-10-26
author_name: technoweenie
---
@@ -17,56 +15,54 @@ view and mark notifications as read.
The core notifications functionality is under the `/notifications` endpoint.
You can look for unread notifications:
-+``` command-line $ curl https://api.github.com/notifications -+``` You can filter these notifications to a single Repository: -
+``` command-line $ curl https://api.github.com/repos/technoweenie/faraday/notifications -+``` You can mark them as read: -
+``` command-line
# all notifications
$ curl https://api.github.com/notifications \
- -X PUT -d '{"read": true}'
+$ -X PUT -d '{"read": true}'
# notifications for a single repository
$ curl https://api.github.com/repos/technoweenie/faraday/notifications \
- -X PUT -d '{"read": true}'
-
+$ -X PUT -d '{"read": true}'
+```
You can also modify subscriptions for a Repository or a single thread.
-+``` command-line # subscription details for the thread (either an Issue or Commit) $ curl https://api.github.com/notifications/threads/1/subscription # subscription details for a whole Repository. $ curl https://api.github.com/repos/technoweenie/faraday/subscription -+``` ## Polling The Notifications API is optimized for polling by the last modified time: -
+``` command-line # Add authentication to your requests $ curl -I https://api.github.com/notifications -HTTP/1.1 200 OK -Last-Modified: Thu, 25 Oct 2012 15:16:27 GMT -X-Poll-Interval: 60 +> HTTP/1.1 200 OK +> Last-Modified: Thu, 25 Oct 2012 15:16:27 GMT +> X-Poll-Interval: 60 # Pass the Last-Modified header exactly $ curl -I https://api.github.com/notifications - -H "If-Modified-Since: Thu, 25 Oct 2012 15:16:27 GMT" -HTTP/1.1 304 Not Modified -X-Poll-Interval: 60 -+$ -H "If-Modified-Since: Thu, 25 Oct 2012 15:16:27 GMT" +> HTTP/1.1 304 Not Modified +> X-Poll-Interval: 60 +``` You can read about the API details in depth in the [Notifications documentation][api]. - - diff --git a/content/changes/2012-10-31-gist-comment-uris.md b/content/changes/2012-10-31-gist-comment-uris.md index 09c112586c..a6f3d9e4f4 100644 --- a/content/changes/2012-10-31-gist-comment-uris.md +++ b/content/changes/2012-10-31-gist-comment-uris.md @@ -1,7 +1,5 @@ --- -kind: change title: Gist comment URIs -created_at: 2012-10-31 author_name: pezra --- diff --git a/content/changes/2012-11-27-forking-to-organizations.html b/content/changes/2012-11-27-forking-to-organizations.html index 7e4530985a..90282f045a 100644 --- a/content/changes/2012-11-27-forking-to-organizations.html +++ b/content/changes/2012-11-27-forking-to-organizations.html @@ -1,29 +1,32 @@ --- -kind: change title: Forking to Organizations -created_at: 2012-11-27 author_name: technoweenie --- We made a slight change to the way you fork a repository. By default, you can fork my repository through an HTTP POST to the repository's fork resource. - $ curl -X POST https://api.github.com/repos/technoweenie/faraday/forks +``` command-line +$ curl -X POST https://api.github.com/repos/technoweenie/faraday/forks +``` This repository forks to your personal account. However, there are cases when you want to fork to one of your organizations instead. The previous method required a `?org` query parameter: - $ curl -X POST /repos/technoweenie/faraday/forks?org=mycompany +``` command-line +$ curl -X POST /repos/technoweenie/faraday/forks?org=mycompany +``` Query parameters on POST requests are unusual in APIs, and definitely inconsistent with the rest of the GitHub API. You should be able to post a JSON body like every other POST endpoint. Now, you can! Only, now we're calling the field `organization`. - $ curl /repos/technoweenie/faraday/forks?org=mycompany \ - -d '{"organization": "mycompany"}' +``` command-line +$ curl /repos/technoweenie/faraday/forks?org=mycompany \ +$ -d '{"organization": "mycompany"}' +``` Don't worry, we are committed to maintaining the legacy behavior until the next major change of the GitHub API. - diff --git a/content/changes/2012-11-29-gitignore-templates.html b/content/changes/2012-11-29-gitignore-templates.html index 931e12b060..d88d39b88f 100644 --- a/content/changes/2012-11-29-gitignore-templates.html +++ b/content/changes/2012-11-29-gitignore-templates.html @@ -1,58 +1,60 @@ --- -kind: change title: Gitignore Templates API -created_at: 2012-11-29 author_name: pengwynn --- We recently [made it easy][init-post] to initialize a repository when you create it [via the API][repo-create]. One of the options you can pass when creating a repository is `gitignore_template`. This value is the name of one of the -templates from the the public [GitHub .gitignore repository][templates-repo]. +templates from the public [GitHub .gitignore repository][templates-repo]. The [Gitignore Templates API][new-api] makes it easy to list those templates: - curl https://api.github.com/gitignore/templates +``` command-line +$ curl https://api.github.com/gitignore/templates - HTTP/1.1 200 OK +> HTTP/1.1 200 OK - [ - "Actionscript", - "Android", - "AppceleratorTitanium", - "Autotools", - "Bancha", - "C", - "C++", - ... +> [ +> "Actionscript", +> "Android", +> "AppceleratorTitanium", +> "Autotools", +> "Bancha", +> "C", +> "C++", +> ... +``` If you'd like to view the source, you can also fetch a single template. - curl -H 'Accept: application/vnd.github.raw' \ - https://api.github.com/gitignore/templates/Objective-C - - HTTP/1.1 200 OK - - # Xcode - .DS_Store - build/ - *.pbxuser - !default.pbxuser - *.mode1v3 - !default.mode1v3 - *.mode2v3 - !default.mode2v3 - *.perspectivev3 - !default.perspectivev3 - *.xcworkspace - !default.xcworkspace - xcuserdata - profile - *.moved-aside - DerivedData - .idea/ - -[init-post]: /changes/2012-9-28-auto-init-for-repositories/ +``` command-line +$ curl -H 'Accept: application/vnd.github.raw' \ +$ https://api.github.com/gitignore/templates/Objective-C + +> HTTP/1.1 200 OK + +# Xcode +> .DS_Store +> build/ +> *.pbxuser +> !default.pbxuser +> *.mode1v3 +> !default.mode1v3 +> *.mode2v3 +> !default.mode2v3 +> *.perspectivev3 +> !default.perspectivev3 +> *.xcworkspace +> !default.xcworkspace +> xcuserdata +> profile +> *.moved-aside +> DerivedData +> .idea/ +``` + +[init-post]: /changes/2012-09-28-auto-init-for-repositories/ [repo-create]: /v3/repos/#create [templates-repo]: https://github.com/github/gitignore [new-api]: /v3/gitignore/ diff --git a/content/changes/2012-12-04-List-comments-for-repo.html b/content/changes/2012-12-04-List-comments-for-repo.html index 228bdc849b..7511737cdc 100644 --- a/content/changes/2012-12-04-List-comments-for-repo.html +++ b/content/changes/2012-12-04-List-comments-for-repo.html @@ -1,7 +1,5 @@ --- -kind: change title: Per-repository Review and Issue Comment listing -created_at: 2012-12-04 author_name: pengwynn --- @@ -12,15 +10,15 @@ Today, we're introducing two new methods to grab all Issue Comments and Review Comments for a repository. - # Grab all Issue Comments - curl https://api.github.com/repos/mathiasbynens/dotfiles/issues/comments +``` command-line +# Grab all Issue Comments +> curl https://api.github.com/repos/mathiasbynens/dotfiles/issues/comments - # Grab all Review Comments - curl https://api.github.com/repos/mathiasbynens/dotfiles/pulls/comments +# Grab all Review Comments +> curl https://api.github.com/repos/mathiasbynens/dotfiles/pulls/comments +``` Check out the docs for sorting and filtering options: * [Issue comments](/v3/issues/comments/#list-comments-in-a-repository) * [Review comments](/v3/pulls/comments/#list-comments-in-a-repository) - - diff --git a/content/changes/2012-12-06-create-authorization-for-app.html b/content/changes/2012-12-06-create-authorization-for-app.html index d03a97a817..a1de9eb1b0 100644 --- a/content/changes/2012-12-06-create-authorization-for-app.html +++ b/content/changes/2012-12-06-create-authorization-for-app.html @@ -1,7 +1,5 @@ --- -kind: change title: Create an OAuth authorization for an app -created_at: 2012-12-06 author_name: pengwynn --- @@ -9,12 +7,12 @@ authorization using Basic Auth. Just POST your desired scopes and optional note and you get a token back: -
- curl -u pengwynn -d '{"scopes": ["user", "gist"]}' \
- https://api.github.com/authorizations
-
+``` command-line
+$ curl -u pengwynn -d '{"scopes": ["user", "gist"]}' \
+$ https://api.github.com/authorizations
+```
-This call creates a token for the authenticating user tied to a special "API"
+This call creates a token for the authenticated user tied to a special "API"
OAuth application.
We now support creating tokens for _your own OAuth application_ by passing your
@@ -22,14 +20,14 @@
the settings page for your OAuth application.
-
- curl -u pengwynn -d '{ \
- "scopes": ["user", "gist"], \
- "client_id": "abcdeabcdeabcdeabcdeabcde" \
- "client_secret": "abcdeabcdeabcdeabcdeabcdeabcdeabcdeabcdeabcde" \
- }' \ '
- https://api.github.com/authorizations
-
+``` command-line
+$ curl -u pengwynn -d '{ \
+$ "scopes": ["user", "gist"], \
+$ "client_id": "abcdeabcdeabcdeabcdeabcde" \
+$ "client_secret": "abcdeabcdeabcdeabcdeabcdeabcdeabcdeabcdeabcde" \
+$ }' \ '
+$ https://api.github.com/authorizations
+```
No more implementing the [web flow][web-flow] just to get a token tied to your
app's rate limit.
diff --git a/content/changes/2012-12-08-finding-source-and-fork-repos-for-organizations.html b/content/changes/2012-12-08-finding-source-and-fork-repos-for-organizations.html
index d7bf6aec6c..bd9f91bedf 100644
--- a/content/changes/2012-12-08-finding-source-and-fork-repos-for-organizations.html
+++ b/content/changes/2012-12-08-finding-source-and-fork-repos-for-organizations.html
@@ -1,7 +1,5 @@
---
-kind: change
title: Finding sources and fork repositories for organizations
-created_at: 2012-12-08
author_name: rick
---
@@ -11,13 +9,14 @@
which are forks of another repository, as well as those repositories which
are sources (not forks).
- # Grab all fork Repositories for an Organization
- curl "https://api.github.com/orgs/:org/repos?type=forks"
+``` command-line
+# Grab all fork Repositories for an Organization
+$ curl "https://api.github.com/orgs/:org/repos?type=forks"
- # Grab all source Repositories for an Organization
- curl "https://api.github.com/orgs/:org/repos?type=sources"
+# Grab all source Repositories for an Organization
+$ curl "https://api.github.com/orgs/:org/repos?type=sources"
+```
Check out the docs for sorting and filtering options:
* [Organization Repositories](/v3/repos/#list-organization-repositories)
-
diff --git a/content/changes/2012-12-09-organization-repositories-results-now-paginate.html b/content/changes/2012-12-09-organization-repositories-results-now-paginate.html
index d58a557520..530d13e2ef 100644
--- a/content/changes/2012-12-09-organization-repositories-results-now-paginate.html
+++ b/content/changes/2012-12-09-organization-repositories-results-now-paginate.html
@@ -1,7 +1,5 @@
---
-kind: change
title: Pagination for Organization Repository lists now paginates properly
-created_at: 2012-12-09
author_name: rick
---
diff --git a/content/changes/2012-12-10-Diff-and-patch-media-types.html b/content/changes/2012-12-10-Diff-and-patch-media-types.html
index 5345c9466f..96eb82a02a 100644
--- a/content/changes/2012-12-10-Diff-and-patch-media-types.html
+++ b/content/changes/2012-12-10-Diff-and-patch-media-types.html
@@ -1,7 +1,5 @@
---
-kind: change
title: Diff and patch media types
-created_at: 2012-12-10
author_name: pengwynn
---
@@ -13,22 +11,23 @@
Simply use the same resource URL and send either `application/vnd.github.diff` or `application/vnd.github.patch` in the `Accept` header:
- curl -H "Accept: application/vnd.github.diff" https://api.github.com/repos/pengwynn/dotfiles/commits/aee60a4cd56fb4c6a50e60f17096fc40c0d4d72c
+``` command-line
+$ curl -H "Accept: application/vnd.github.diff" $ https://api.github.com/repos/pengwynn/dotfiles/commits/aee60a4cd56fb4c6a50e60f17096fc40c0d4d72c
- diff --git a/tmux/tmux.conf.symlink b/tmux/tmux.conf.symlink
- index 1f599cb..abaf625 100755
- --- a/tmux/tmux.conf.symlink
- +++ b/tmux/tmux.conf.symlink
- @@ -111,6 +111,7 @@ set-option -g base-index 1
- ## enable mouse
- set-option -g mouse-select-pane on
- set-option -g mouse-select-window on
- +set-option -g mouse-resize-pane on
- set-window-option -g mode-keys vi
- set-window-option -g mode-mouse on
- # set-window-option -g monitor-activity off
+> diff --git a/tmux/tmux.conf.symlink b/tmux/tmux.conf.symlink
+> index 1f599cb..abaf625 100755
+> --- a/tmux/tmux.conf.symlink
+> +++ b/tmux/tmux.conf.symlink
+> @@ -111,6 +111,7 @@ set-option -g base-index 1
+> ## enable mouse
+> set-option -g mouse-select-pane on
+> set-option -g mouse-select-window on
+> +set-option -g mouse-resize-pane on
+> set-window-option -g mode-keys vi
+> set-window-option -g mode-mouse on
+> # set-window-option -g monitor-activity off
+```
[commits-get]: /v3/repos/commits/#get-a-single-commit
[commits-compare]: /v3/repos/commits/#compare-two-commits
[pulls]: /v3/pulls/#get-a-single-pull-request
-
diff --git a/content/changes/2013-01-08-new-user-scopes.html b/content/changes/2013-01-08-new-user-scopes.html
index c0e3aeae7f..ecd48a14db 100644
--- a/content/changes/2013-01-08-new-user-scopes.html
+++ b/content/changes/2013-01-08-new-user-scopes.html
@@ -1,7 +1,5 @@
---
-kind: change
title: New User scopes
-created_at: 2013-01-08
author_name: technoweenie
---
diff --git a/content/changes/2013-01-31-user-agent-will-soon-be-mandatory.html b/content/changes/2013-01-31-user-agent-will-soon-be-mandatory.html
index 2407d3a97d..3c06f81381 100644
--- a/content/changes/2013-01-31-user-agent-will-soon-be-mandatory.html
+++ b/content/changes/2013-01-31-user-agent-will-soon-be-mandatory.html
@@ -1,13 +1,11 @@
---
-kind: change
title: User Agent mandatory from March 4th 2013
-created_at: 2013-01-31
author_name: agh
---
Following on from our [previous post](http://developer.github.com/changes/2012-10-14-rate-limit-changes/)
about requiring requests to include a valid [User Agent header](http://en.wikipedia.org/wiki/User_agent)
-we will soon be changing our API servers to return HTTP 403
+we will soon be changing our API servers to return HTTP 403
to any clients not providing a valid User Agent header.
We will be making this change on Monday, March 4th 2013.
diff --git a/content/changes/2013-2-5-changes-to-services.html b/content/changes/2013-02-05-changes-to-services.html
similarity index 85%
rename from content/changes/2013-2-5-changes-to-services.html
rename to content/changes/2013-02-05-changes-to-services.html
index ba86cb0243..4ff6d6e8cd 100644
--- a/content/changes/2013-2-5-changes-to-services.html
+++ b/content/changes/2013-02-05-changes-to-services.html
@@ -1,7 +1,5 @@
---
-kind: change
title: Upcoming Changes to GitHub Services
-created_at: 2013-2-5
author_name: technoweenie
---
@@ -30,5 +28,5 @@
core Services backend for everyone. Maintaining custom logic and libraries for
over 100 services is taking too much of this focus away.
-[codeclimate]: https://github.com/github/github-services/blob/master/lib/services/codeclimate.rb
-[cf]: https://github.com/github/github-services/blob/master/lib/services/campfire.rb
+[codeclimate]: https://github.com/github/github-services/blob/fbc0db24b8b7685b2058462181d928a5f2a0a448/lib/services/codeclimate.rb
+[cf]: https://github.com/github/github-services/blob/fbc0db24b8b7685b2058462181d928a5f2a0a448/lib/services/campfire.rb
diff --git a/content/changes/2013-2-13-hookshot-issues.html b/content/changes/2013-02-13-hookshot-issues.html
similarity index 93%
rename from content/changes/2013-2-13-hookshot-issues.html
rename to content/changes/2013-02-13-hookshot-issues.html
index 6141df4757..7e69bc2ada 100644
--- a/content/changes/2013-2-13-hookshot-issues.html
+++ b/content/changes/2013-02-13-hookshot-issues.html
@@ -1,7 +1,5 @@
---
-kind: change
title: Some Hookshot Issues
-created_at: 2013-2-13T11:00:00
author_name: technoweenie
---
@@ -17,4 +15,3 @@
We're currently working on solving this problem. Hit up [support@github.com](mailto:support@github.com)
if you have any questions.
-
diff --git a/content/changes/2013-2-13-hookshot-load-balancer.html b/content/changes/2013-02-13-hookshot-load-balancer.html
similarity index 91%
rename from content/changes/2013-2-13-hookshot-load-balancer.html
rename to content/changes/2013-02-13-hookshot-load-balancer.html
index 6e605af7e4..fd6b3114cd 100644
--- a/content/changes/2013-2-13-hookshot-load-balancer.html
+++ b/content/changes/2013-02-13-hookshot-load-balancer.html
@@ -1,7 +1,5 @@
---
-kind: change
title: Hookshot Load balancer
-created_at: 2013-2-13T12:00:00
author_name: technoweenie
---
diff --git a/content/changes/2013-2-13-sortable-stars.html b/content/changes/2013-02-14-sortable-stars.html
similarity index 73%
rename from content/changes/2013-2-13-sortable-stars.html
rename to content/changes/2013-02-14-sortable-stars.html
index fbaf50dab0..d7b253b919 100644
--- a/content/changes/2013-2-13-sortable-stars.html
+++ b/content/changes/2013-02-14-sortable-stars.html
@@ -1,7 +1,5 @@
---
-kind: change
title: Sortable Stars in Repository Starring API
-created_at: 2013-2-14
author_name: pengwynn
---
@@ -9,9 +7,9 @@
Repository Starring API now supports [two new parameters][params] when listing
Stars: `sort` and `direction`.
--curl https://api.github.com/users/defunkt/starred?sort=created&direction=asc -+``` command-line +$ curl https://api.github.com/users/defunkt/starred?sort=created&direction=asc +``` Enjoy. diff --git a/content/changes/2013-3-1-new-hookshot-coming.html b/content/changes/2013-03-01-new-hookshot-coming.html similarity index 96% rename from content/changes/2013-3-1-new-hookshot-coming.html rename to content/changes/2013-03-01-new-hookshot-coming.html index b0ede13721..c109a40653 100644 --- a/content/changes/2013-3-1-new-hookshot-coming.html +++ b/content/changes/2013-03-01-new-hookshot-coming.html @@ -1,7 +1,5 @@ --- -kind: change title: New Hookshot Changes -created_at: 2013-3-1 author_name: technoweenie --- @@ -22,4 +20,3 @@ This also means we should be able to start accepting [GitHub Services pull requests](https://github.com/github/github-services/pulls) very soon :) - diff --git a/content/changes/2013-04-24-user-agent-required.html b/content/changes/2013-04-24-user-agent-required.html index 292d14c5a1..b1fae21ff0 100644 --- a/content/changes/2013-04-24-user-agent-required.html +++ b/content/changes/2013-04-24-user-agent-required.html @@ -1,7 +1,5 @@ --- -kind: change title: User Agent now mandatory -created_at: 2013-04-24 author_name: pengwynn --- diff --git a/content/changes/2013-04-25-deprecating-merge-commit-sha.html b/content/changes/2013-04-25-deprecating-merge-commit-sha.html index 54a024593b..8bff84e414 100644 --- a/content/changes/2013-04-25-deprecating-merge-commit-sha.html +++ b/content/changes/2013-04-25-deprecating-merge-commit-sha.html @@ -1,7 +1,5 @@ --- -kind: change title: Deprecating a Confusing Attribute in the Pull Request API -created_at: 2013-04-25 author_name: jasonrudolph --- @@ -13,7 +11,7 @@ confusion. To help current API consumers, we've [documented the -attribute](/v3/pulls/#mergability) for improved understanding. +attribute](/v3/pulls/#get-a-single-pull-request) for improved understanding. To protect future API consumers from this confusion, we have [deprecated](/v3/versions/#v3-deprecations) the `merge_commit_sha` attribute, and we will diff --git a/content/changes/2013-04-30-improved-submodule-support-in-repository-contents-api.md b/content/changes/2013-04-30-improved-submodule-support-in-repository-contents-api.md index fcd99765f1..8b7598e783 100644 --- a/content/changes/2013-04-30-improved-submodule-support-in-repository-contents-api.md +++ b/content/changes/2013-04-30-improved-submodule-support-in-repository-contents-api.md @@ -1,39 +1,37 @@ --- -kind: change title: Improved Support for Submodules in the Repository Contents API -created_at: 2013-04-30 author_name: jasonrudolph --- When you view a repository with a submodule on github.com, you get useful links and information for the submodule. -[][screenshot] +[][screenshot] Today we're making that data available in the [Repository Contents API][docs]. -
-curl https://api.github.com/repos/jquery/jquery/contents/test/qunit
+``` command-line
+$ curl https://api.github.com/repos/jquery/jquery/contents/test/qunit
-{
- "name": "qunit",
- "path": "test/qunit",
- "type": "submodule",
- "submodule_git_url": "git://github.com/jquery/qunit.git",
- "sha": "6ca3721222109997540bd6d9ccd396902e0ad2f9",
- "size": 0,
- "url": "https://api.github.com/repos/jquery/jquery/contents/test/qunit?ref=master",
- "git_url": "https://api.github.com/repos/jquery/qunit/git/trees/6ca3721222109997540bd6d9ccd396902e0ad2f9",
- "html_url": "https://github.com/jquery/qunit/tree/6ca3721222109997540bd6d9ccd396902e0ad2f9",
- "_links": {
- "self": "https://api.github.com/repos/jquery/jquery/contents/test/qunit?ref=master",
- "git": "https://api.github.com/repos/jquery/qunit/git/trees/6ca3721222109997540bd6d9ccd396902e0ad2f9",
- "html": "https://github.com/jquery/qunit/tree/6ca3721222109997540bd6d9ccd396902e0ad2f9"
- }
-}
-
+> {
+> "name": "qunit",
+> "path": "test/qunit",
+> "type": "submodule",
+> "submodule_git_url": "git://github.com/jquery/qunit.git",
+> "sha": "6ca3721222109997540bd6d9ccd396902e0ad2f9",
+> "size": 0,
+> "url": "https://api.github.com/repos/jquery/jquery/contents/test/qunit?ref=master",
+> "git_url": "https://api.github.com/repos/jquery/qunit/git/trees/6ca3721222109997540bd6d9ccd396902e0ad2f9",
+> "html_url": "https://github.com/jquery/qunit/tree/6ca3721222109997540bd6d9ccd396902e0ad2f9",
+> "_links": {
+> "self": "https://api.github.com/repos/jquery/jquery/contents/test/qunit?ref=master",
+> "git": "https://api.github.com/repos/jquery/qunit/git/trees/6ca3721222109997540bd6d9ccd396902e0ad2f9",
+> "html": "https://github.com/jquery/qunit/tree/6ca3721222109997540bd6d9ccd396902e0ad2f9"
+> }
+> }
+```
If you have any questions or feedback, please drop us a line at
[support@github.com](mailto:support@github.com?subject=Submodules in Repository Contents API).
[docs]: /v3/repos/contents/#get-contents
-[screenshot]: /images/posts/submodule-links.png
+[screenshot]: /assets/images/posts/submodule-links.png
diff --git a/content/changes/2013-04-30-statuses-for-branches-and-tags.md b/content/changes/2013-04-30-statuses-for-branches-and-tags.md
index d35724dcd6..b42aafdb81 100644
--- a/content/changes/2013-04-30-statuses-for-branches-and-tags.md
+++ b/content/changes/2013-04-30-statuses-for-branches-and-tags.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Commit Statuses Now Available for Branches and Tags
-created_at: 2013-04-30
author_name: foca
---
@@ -9,9 +7,9 @@ Last week we announced [support for build statuses in the branches page][blog].
Now we are extending this to the API. The [API endpoint for commit statuses][doc]
has been extended to allow branch and tag names, as well as commit SHAs.
-+``` command-line curl https://api.github.com/repos/rails/rails/statuses/3-2-stable -+``` Enjoy. diff --git a/content/changes/2013-05-06-create-update-delete-individual-files.md b/content/changes/2013-05-06-create-update-delete-individual-files.md index bd30049ca0..f9baff52ca 100644 --- a/content/changes/2013-05-06-create-update-delete-individual-files.md +++ b/content/changes/2013-05-06-create-update-delete-individual-files.md @@ -1,7 +1,5 @@ --- -kind: change title: Create, update, and delete individual files -created_at: 2013-05-06 author_name: ymendel --- diff --git a/content/changes/2013-05-06-repository-stats.md b/content/changes/2013-05-06-repository-stats.md index 08569d9347..3ff4b37d97 100644 --- a/content/changes/2013-05-06-repository-stats.md +++ b/content/changes/2013-05-06-repository-stats.md @@ -1,7 +1,5 @@ --- -kind: change title: Repository Statistics -created_at: 2013-05-06 author_name: Caged --- diff --git a/content/changes/2013-07-01-feeds-api.md b/content/changes/2013-07-01-feeds-api.md index 8111964252..e15115c5bf 100644 --- a/content/changes/2013-07-01-feeds-api.md +++ b/content/changes/2013-07-01-feeds-api.md @@ -1,53 +1,49 @@ --- -kind: change title: Feeds API -created_at: 2013-7-01 author_name: pengwynn --- Today we're releasing a new [Feeds API][], an easy way to list all the Atom resources available to the authenticated user. -
-
-curl -u defunkt https://api.github.com/feeds
-
-{
- "timeline_url": "https://github.com/timeline",
- "user_url": "https://github.com/{user}",
- "current_user_public_url": "https://github.com/defunkt",
- "current_user_url": "https://github.com/defunkt.private?token=abc123",
- "current_user_actor_url": "https://github.com/defunkt.private.actor?token=abc123",
- "current_user_organization_url": "https://github.com/organizations/{org}/defunkt.private.atom?token=abc123",
- "_links": {
- "timeline": {
- "href": "https://github.com/timeline",
- "type": "application/atom+xml"
- },
- "user": {
- "href": "https://github.com/{user}",
- "type": "application/atom+xml"
- },
- "current_user_public": {
- "href": "https://github.com/defunkt",
- "type": "application/atom+xml"
- },
- "current_user": {
- "href": "https://github.com/defunkt.private?token=abc123",
- "type": "application/atom+xml"
- },
- "current_user_actor": {
- "href": "https://github.com/defunkt.private.actor?token=abc123",
- "type": "application/atom+xml"
- },
- "current_user_organization": {
- "href": "https://github.com/organizations/{org}/defunkt.private.atom?token=abc123",
- "type": "application/atom+xml"
- }
- }
-}
-
-
+``` command-line
+$ curl -u defunkt https://api.github.com/feeds
+
+> {
+> "timeline_url": "https://github.com/timeline",
+> "user_url": "https://github.com/{user}",
+> "current_user_public_url": "https://github.com/defunkt",
+> "current_user_url": "https://github.com/defunkt.private?token=abc123",
+> "current_user_actor_url": "https://github.com/defunkt.private.actor?token=abc123",
+> "current_user_organization_url": "https://github.com/organizations/{org}/defunkt.private.atom?token=abc123",
+> "_links": {
+> "timeline": {
+> "href": "https://github.com/timeline",
+> "type": "application/atom+xml"
+> },
+> "user": {
+> "href": "https://github.com/{user}",
+> "type": "application/atom+xml"
+> },
+> "current_user_public": {
+> "href": "https://github.com/defunkt",
+> "type": "application/atom+xml"
+> },
+> "current_user": {
+> "href": "https://github.com/defunkt.private?token=abc123",
+> "type": "application/atom+xml"
+> },
+> "current_user_actor": {
+> "href": "https://github.com/defunkt.private.actor?token=abc123",
+> "type": "application/atom+xml"
+> },
+> "current_user_organization": {
+> "href": "https://github.com/organizations/{org}/defunkt.private.atom?token=abc123",
+> "type": "application/atom+xml"
+> }
+> }
+> }
+```
If you have any questions or feedback, [please drop us a line][contact].
diff --git a/content/changes/2013-07-02-rate-limit-reset.md b/content/changes/2013-07-02-rate-limit-reset.md
index ab19eed93e..5106f7412b 100644
--- a/content/changes/2013-07-02-rate-limit-reset.md
+++ b/content/changes/2013-07-02-rate-limit-reset.md
@@ -1,39 +1,37 @@
---
-kind: change
title: When Does My Rate Limit Reset?
-created_at: 2013-07-02
author_name: jasonrudolph
---
Have you ever wondered when your [rate limit][rate-limit-docs] will reset back to its maximum value?
That information is now available in the new `X-RateLimit-Reset` response header.
-+``` command-line $ curl -I https://api.github.com/orgs/octokit -HTTP/1.1 200 OK -Status: 200 OK -X-RateLimit-Limit: 60 -X-RateLimit-Remaining: 42 -X-RateLimit-Reset: 1372700873 -... -+> HTTP/1.1 200 OK +> Status: 200 OK +> X-RateLimit-Limit: 60 +> X-RateLimit-Remaining: 42 +> X-RateLimit-Reset: 1372700873 +> ... +``` The `X-RateLimit-Reset` header provides a [Unix UTC timestamp][unix-time], letting you know the exact time that your fresh new rate limit kicks in. The reset timestamp is also available as part of the `/rate_limit` resource. -
+``` command-line
$ curl https://api.github.com/rate_limit
-{
- "rate": {
- "limit": 60,
- "remaining": 42,
- "reset": 1372700873
- }
-}
-
+> {
+> "rate": {
+> "limit": 60,
+> "remaining": 42,
+> "reset": 1372700873
+> }
+> }
+```
For more information on rate limits, be sure to check out the [docs][rate-limit-docs].
diff --git a/content/changes/2013-07-19-preview-the-new-search-api.md b/content/changes/2013-07-19-preview-the-new-search-api.md
index 736b4a28b6..370a1440c2 100644
--- a/content/changes/2013-07-19-preview-the-new-search-api.md
+++ b/content/changes/2013-07-19-preview-the-new-search-api.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Preview the New Search API
-created_at: 2013-07-19
author_name: jasonrudolph
---
diff --git a/content/changes/2013-08-20-search-api-improvements.md b/content/changes/2013-08-20-search-api-improvements.md
index 230de12678..1ab04d2b9e 100644
--- a/content/changes/2013-08-20-search-api-improvements.md
+++ b/content/changes/2013-08-20-search-api-improvements.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Improvements to the Search API
-created_at: 2013-08-20
author_name: jasonrudolph
---
@@ -14,54 +12,51 @@ Now, you can also [get this metadata][code-text-matches] for matches that occur
For example, when [searching for files that have "client" in their path][example-path-search], the results include this match for `lib/octokit/client/commits.rb`:
-
-{
- "name": "commits.rb",
- "path": "lib/octokit/client/commits.rb",
- "text_matches": [
+{:.json}
{
- "object_url": "https://api.github.com/repositories/417862/contents/lib/octokit/client/commits.rb?ref=8d487ab06ccef463aa9f5412a56f1a2f1fa4dc88",
- "object_type": "FileContent",
- "property": "path",
- "fragment": "lib/octokit/client/commits.rb",
- "matches": [
+ "name": "commits.rb",
+ "path": "lib/octokit/client/commits.rb",
+ "text_matches": [
{
- "text": "client",
- "indices": [ 12, 18 ]
+ "object_url": "https://api.github.com/repositories/417862/contents/lib/octokit/client/commits.rb?ref=8d487ab06ccef463aa9f5412a56f1a2f1fa4dc88",
+ "object_type": "FileContent",
+ "property": "path",
+ "fragment": "lib/octokit/client/commits.rb",
+ "matches": [
+ {
+ "text": "client",
+ "indices": [ 12, 18 ]
+ }
+ ]
}
]
+ // ...
}
- ]
- // ...
-}
-
## Better Text Match Metadata
Before today, the API applied HTML entity encoding to all `fragment` data.
-For example, imagine your search returns an issue like [rails/rails#11889][example-issue]:
+For example, imagine your search returns an issue like rails/rails#11889:

The response would include a `text_matches` array with the following object:
-
-{
- "fragment": "undefined method `except' for #<Array:XXX>",
- // ...
-}
-
+{:.json}
+ {
+ "fragment": "undefined method 'except' for #<Array:XXX>",
+ // ...
+ }
Inside the `fragment` value, we see HTML-encoded entities (e.g., `<`).
Since we're returning JSON (not HTML), API clients might not expect any HTML-encoded text.
As of today, the API returns these fragments _without_ this extraneous encoding.
-
-{
- "fragment": "undefined method `except' for #<Array:XXX>",
- // ...
-}
-
+{:.json}
+ {
+ "fragment": "undefined method 'except' for #
+``` command-line
$ curl -i -H "Authorization: token TOKEN" \
- -H "Accept: application/vnd.github.manifold-preview" \
- "https://uploads.github.com/repos/hubot/singularity/releases/assets/123"
+$ -H "Accept: application/vnd.github.manifold-preview" \
+$ "https://uploads.github.com/repos/hubot/singularity/releases/assets/123"
-HTTP/1.1 200 OK
+> HTTP/1.1 200 OK
-{
- "id": 123,
- ...
-}
-
+> {
+> "id": 123,
+> ...
+> }
+```
Pass "application/octet-stream" to download the binary content.
-+``` command-line $ curl -i -H "Authorization: token TOKEN" \ - -H "Accept: application/octet-stream" \ - "https://uploads.github.com/repos/hubot/singularity/releases/assets/123" +$ -H "Accept: application/octet-stream" \ +$ "https://uploads.github.com/repos/hubot/singularity/releases/assets/123" -HTTP/1.1 302 Found -+> HTTP/1.1 302 Found +``` Uploads are handled by a single request to a companion "uploads.github.com" service. -
+``` command-line
$ curl -H "Authorization: token TOKEN" \
-H "Accept: application/vnd.github.manifold-preview" \
-H "Content-Type: application/zip" \
--data-binary @build/mac/package.zip \
"https://uploads.github.com/repos/hubot/singularity/releases/123/assets?name=1.0.0-mac.zip"
-
+```
## Preview mode
diff --git a/content/changes/2013-09-28-an-update-on-the-new-search-api.md b/content/changes/2013-09-28-an-update-on-the-new-search-api.md
index 2212fdff16..fbdf1623d8 100644
--- a/content/changes/2013-09-28-an-update-on-the-new-search-api.md
+++ b/content/changes/2013-09-28-an-update-on-the-new-search-api.md
@@ -1,7 +1,5 @@
---
-kind: change
title: An Update on the New Search API
-created_at: 2013-09-28
author_name: jasonrudolph
---
diff --git a/content/changes/2013-10-04-oauth-changes-coming.html b/content/changes/2013-10-04-oauth-changes-coming.html
index 842175a2d7..a81fbc7c99 100644
--- a/content/changes/2013-10-04-oauth-changes-coming.html
+++ b/content/changes/2013-10-04-oauth-changes-coming.html
@@ -1,22 +1,20 @@
---
-kind: change
title: OAuth changes coming
-created_at: 2013-10-04
author_name: tclem
---
Starting today, we are returning granted scopes as part of the
-[access_token response](/v3/oauth/#github-redirects-back-to-your-site).
+[access_token response](/v3/oauth/#2-github-redirects-back-to-your-site).
For example, if you are making a POST with the `application/json`
mime-type you'll see an additional field for the granted scopes.
-
+``` json
{
"access_token":"e72e16c7e42f292c6912e7710c838347ae178b4a",
"scope":"repo,gist",
"token_type":"bearer"
}
-
+``` command-line
$ curl -H "Authorization: token [yours]" https://api.github.com/user/teams
-[
- {
- "name": "Testing",
- "id": 396018,
- "slug": "testing",
- "permission": "pull",
- "url": "https://api.github.com/teams/396018",
- "members_url": "https://api.github.com/teams/396018/members{/member}",
- "repositories_url": "https://api.github.com/teams/396018/repos",
- "members_count": 1,
- "repos_count": 0,
- "organization": {
- "login": "dotfiles",
- "id": 1593590,
- "url": "https://api.github.com/orgs/dotfiles",
- "repos_url": "https://api.github.com/orgs/dotfiles/repos",
- "events_url": "https://api.github.com/orgs/dotfiles/events",
- "members_url": "https://api.github.com/orgs/dotfiles/members{/member}",
- "public_members_url": "https://api.github.com/orgs/dotfiles/public_members{/member}",
- "avatar_url": "https://0.gravatar.com/avatar/67d30facf213f62853c119fc2a05e246?d=https%3A%2F%2Fidenticons.github.com%2Fc90a68e6ab739e81c642f0e93f88c722.png"
- }
- },
- ...
-]
-
+> [
+> {
+> "name": "Testing",
+> "id": 396018,
+> "slug": "testing",
+> "permission": "pull",
+> "url": "https://api.github.com/teams/396018",
+> "members_url": "https://api.github.com/teams/396018/members{/member}",
+> "repositories_url": "https://api.github.com/teams/396018/repos",
+> "members_count": 1,
+> "repos_count": 0,
+> "organization": {
+> "login": "dotfiles",
+> "id": 1593590,
+> "url": "https://api.github.com/orgs/dotfiles",
+> "repos_url": "https://api.github.com/orgs/dotfiles/repos",
+> "events_url": "https://api.github.com/orgs/dotfiles/events",
+> "members_url": "https://api.github.com/orgs/dotfiles/members{/member}",
+> "public_members_url": "https://api.github.com/orgs/dotfiles/public_members{/member}",
+> "avatar_url": "https://0.gravatar.com/avatar/67d30facf213f62853c119fc2a05e246?d=https%3A%2F%2Fidenticons.github.com%2Fc90a68e6ab739e81c642f0e93f88c722.png"
+> }
+> },
+> ...
+> ]
+```
As always, if you have any questions or feedback, please [drop us a line][contact].
diff --git a/content/changes/2013-10-18-new-code-search-requirements.md b/content/changes/2013-10-18-new-code-search-requirements.md
index bef8684509..746f3f61df 100644
--- a/content/changes/2013-10-18-new-code-search-requirements.md
+++ b/content/changes/2013-10-18-new-code-search-requirements.md
@@ -1,7 +1,5 @@
---
-kind: change
title: New Validation Rule for Beta Code Search API
-created_at: 2013-10-18
author_name: jasonrudolph
---
diff --git a/content/changes/2013-10-29-search-api-becomes-an-official-part-of-github-api-v3.md b/content/changes/2013-10-29-search-api-becomes-an-official-part-of-github-api-v3.md
index e9fb466d7f..5ca31f1042 100644
--- a/content/changes/2013-10-29-search-api-becomes-an-official-part-of-github-api-v3.md
+++ b/content/changes/2013-10-29-search-api-becomes-an-official-part-of-github-api-v3.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Search API Becomes an Official Part of API v3
-created_at: 2013-10-29
author_name: jasonrudolph
---
diff --git a/content/changes/2013-11-04-releases-api-is-official.md b/content/changes/2013-11-04-releases-api-is-official.md
index 9691006777..4bb7dd971a 100644
--- a/content/changes/2013-11-04-releases-api-is-official.md
+++ b/content/changes/2013-11-04-releases-api-is-official.md
@@ -1,13 +1,11 @@
---
-kind: change
title: Releases API is Official
-created_at: 2013-11-04
author_name: technoweenie
---
Hot on the heels of the [Search API][search-api], the [Releases API][releases-api]
is now officially part of GitHub API v3. We now consider it stable for
-production use.
+production use.
### Preview Media Type No Longer Needed
diff --git a/content/changes/2013-12-13-paginating-org-members.md b/content/changes/2013-12-13-paginating-org-members.md
index a6f89987ad..80c3432fdf 100644
--- a/content/changes/2013-12-13-paginating-org-members.md
+++ b/content/changes/2013-12-13-paginating-org-members.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Paginated results for organization members
-created_at: 2013-12-13
author_name: pengwynn
---
diff --git a/content/changes/2014-01-07-upcoming-change-to-default-media-type.md b/content/changes/2014-01-07-upcoming-change-to-default-media-type.md
index 730089e6f4..fad283d768 100644
--- a/content/changes/2014-01-07-upcoming-change-to-default-media-type.md
+++ b/content/changes/2014-01-07-upcoming-change-to-default-media-type.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Upcoming Change to Default Media Type
-created_at: 2014-01-07
author_name: jasonrudolph
---
@@ -40,7 +38,9 @@ If you are affected by this change, we recommend that you:
If you cannot update your application to depend on the v3 functionality by April 15[*](#cutover-test), you can just request the beta media type via the `Accept` header. Doing so will insulate you from this change.
-## Cutover test on March 12, 2014 {#cutover-test}
+
+
+## Cutover test on March 12, 2014
To help you understand the impact of this change before it becomes permanent, we will temporarily implement this change for a single day on March 12. From approximately 12:01am UTC to 11:59pm UTC on March 12, the API will respond with the v3 media type by default.
diff --git a/content/changes/2014-01-09-preview-the-new-deployments-api.md b/content/changes/2014-01-09-preview-the-new-deployments-api.md
index 003a99be33..fd2a28d148 100644
--- a/content/changes/2014-01-09-preview-the-new-deployments-api.md
+++ b/content/changes/2014-01-09-preview-the-new-deployments-api.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Preview the New Deployments API
-created_at: 2014-01-09
author_name: atmos
---
diff --git a/content/changes/2014-01-29-audit-org-members-for-2fa.md b/content/changes/2014-01-29-audit-org-members-for-2fa.md
index ddfe46dd3a..5e7239801a 100644
--- a/content/changes/2014-01-29-audit-org-members-for-2fa.md
+++ b/content/changes/2014-01-29-audit-org-members-for-2fa.md
@@ -1,7 +1,5 @@
---
-kind: change
title: Audit organization members for two-factor authentication
-created_at: 2014-01-29
author_name: pengwynn
---
@@ -9,10 +7,10 @@ We've added a [new filter][filter] for listing members of an organization withou
[two-factor authentication][2fa-blog] enabled:
-+``` command-line $ curl -H "Authorization: token [yours]" \ - https://api.github.com/orgs/[orgname]/members\?filter\=2fa_disabled -+ "https://api.github.com/orgs/[orgname]/members?filter=2fa_disabled" +``` The new filter is available for owners of organizations with private repositories. Happy auditing and [send us your feedback or questions][contact]. diff --git a/content/changes/2014-2-10-ping-event-for-webhooks.html b/content/changes/2014-02-10-ping-event-for-webhooks.html similarity index 95% rename from content/changes/2014-2-10-ping-event-for-webhooks.html rename to content/changes/2014-02-10-ping-event-for-webhooks.html index cfd9c38eec..386ba8cf75 100644 --- a/content/changes/2014-2-10-ping-event-for-webhooks.html +++ b/content/changes/2014-02-10-ping-event-for-webhooks.html @@ -1,7 +1,5 @@ --- -kind: change title: Ping Event for Webhooks -created_at: 2014-2-10 author_name: kdaigle --- diff --git a/content/changes/2014-02-10-repo-hook-scopes.md b/content/changes/2014-02-10-repo-hook-scopes.md index 71c91bc8f7..56f8372627 100644 --- a/content/changes/2014-02-10-repo-hook-scopes.md +++ b/content/changes/2014-02-10-repo-hook-scopes.md @@ -1,7 +1,5 @@ --- -kind: change title: New scopes for managing repository hooks -created_at: 2014-02-10 author_name: pengwynn --- diff --git a/content/changes/2014-02-13-exposing-the-page-api.html b/content/changes/2014-02-13-exposing-the-page-api.html index 314aed7336..72167855c0 100644 --- a/content/changes/2014-02-13-exposing-the-page-api.html +++ b/content/changes/2014-02-13-exposing-the-page-api.html @@ -1,7 +1,5 @@ --- -kind: change title: Introducing the Pages API -created_at: 2014-02-13 author_name: gjtorikian --- diff --git a/content/changes/2014-02-19-repo-contributors-for-empty-repos.md b/content/changes/2014-02-19-repo-contributors-for-empty-repos.md index 67f10dde2f..9fe6911aa1 100644 --- a/content/changes/2014-02-19-repo-contributors-for-empty-repos.md +++ b/content/changes/2014-02-19-repo-contributors-for-empty-repos.md @@ -1,7 +1,5 @@ --- -kind: change title: Repository Contributors and Empty Repositories -created_at: 2014-02-20 author_name: izuzak --- diff --git a/content/changes/2014-02-21-gist-raw-file-url-change.md b/content/changes/2014-02-21-gist-raw-file-url-change.md index 8d98f7097f..7117f55411 100644 --- a/content/changes/2014-02-21-gist-raw-file-url-change.md +++ b/content/changes/2014-02-21-gist-raw-file-url-change.md @@ -1,7 +1,5 @@ --- -kind: change title: Gist raw file URI change -created_at: 2014-02-21 author_name: spicycode --- diff --git a/content/changes/2014-02-24-finer-grained-scopes-for-ssh-keys.md b/content/changes/2014-02-24-finer-grained-scopes-for-ssh-keys.md index c84ec89abb..833b4f4e6c 100644 --- a/content/changes/2014-02-24-finer-grained-scopes-for-ssh-keys.md +++ b/content/changes/2014-02-24-finer-grained-scopes-for-ssh-keys.md @@ -1,7 +1,5 @@ --- -kind: change title: Finer-grained OAuth scopes for SSH keys -created_at: 2014-02-24 author_name: pengwynn --- As [we announced][blog], we've made some important changes to the way that API consumers manage SSH keys. diff --git a/content/changes/2014-02-24-wildcard-event-for-webhooks.md b/content/changes/2014-02-24-wildcard-event-for-webhooks.md index 5e9a29a7b7..ecad8cead1 100644 --- a/content/changes/2014-02-24-wildcard-event-for-webhooks.md +++ b/content/changes/2014-02-24-wildcard-event-for-webhooks.md @@ -1,7 +1,5 @@ --- -kind: change title: Wildcard Event for Webhooks -created_at: 2014-2-24 author_name: kdaigle --- diff --git a/content/changes/2014-02-25-organization-oauth-scopes.md b/content/changes/2014-02-25-organization-oauth-scopes.md index 40911b2b3e..e28320c694 100644 --- a/content/changes/2014-02-25-organization-oauth-scopes.md +++ b/content/changes/2014-02-25-organization-oauth-scopes.md @@ -1,7 +1,5 @@ --- -kind: change title: OAuth scopes for organization and team resources -created_at: 2014-02-25 author_name: pengwynn --- As a follow up to [the new scopes][yesterday] we announced yesterday, we've diff --git a/content/changes/2014-02-28-issue-and-pull-query-enhancements.md b/content/changes/2014-02-28-issue-and-pull-query-enhancements.md index c5a052bd31..5b113f0480 100644 --- a/content/changes/2014-02-28-issue-and-pull-query-enhancements.md +++ b/content/changes/2014-02-28-issue-and-pull-query-enhancements.md @@ -1,24 +1,22 @@ --- -kind: change title: Query enhancements for listing issues and pull requests -created_at: 2014-02-28 author_name: pengwynn --- We've made it even easier to list all [issues][] and [pull requests][] via the API. The `state` parameter now supports a value of `all` that will return issues and pull requests regardless of state. -
+``` command-line $ curl https://api.github.com/repos/atom/vim-mode/issues\?state\=all -+``` We've also introduced new sorting options for [listing pull requests][pull requests]. You can now sort pull requests by `created`, `updated`, `popularity`, and `long-running`. -
+``` command-line $ curl https://api.github.com/repos/rails/rails/pulls\?sort\=long-running\&direction\=desc -+``` Happy querying. If you have any questions or feedback [get in touch][contact]. diff --git a/content/changes/2014-03-03-deployments-api-updates.md b/content/changes/2014-03-03-deployments-api-updates.md index b4354c8dee..bf6198beb4 100644 --- a/content/changes/2014-03-03-deployments-api-updates.md +++ b/content/changes/2014-03-03-deployments-api-updates.md @@ -1,7 +1,5 @@ --- -kind: change title: New Payload Format for Deployments -created_at: 2014-03-03 author_name: atmos --- diff --git a/content/changes/2014-03-04-timezone-handling-changes.html b/content/changes/2014-03-04-timezone-handling-changes.html index 8642f0c46c..2f8e862653 100644 --- a/content/changes/2014-03-04-timezone-handling-changes.html +++ b/content/changes/2014-03-04-timezone-handling-changes.html @@ -1,7 +1,5 @@ --- -kind: change title: Improved timezone handling in the API -created_at: 2014-03-04 author_name: dbussink --- @@ -30,7 +28,9 @@ It is possible to supply a `Time-Zone` header which defines a timezone according to the [list of names from the Olson database](https://en.wikipedia.org/wiki/List_of_tz_database_time_zones). - $ curl -H "Time-Zone: Europe/Amsterdam" -X POST https://api.github.com/repos/github/linguist/contents/new_file.md +``` command-line +$ curl -H "Time-Zone: Europe/Amsterdam" -X POST https://api.github.com/repos/github/linguist/contents/new_file.md +``` This means that we generate a timestamp for the moment your API call is made in the timezone this header defines. For example, the [Contents API](/v3/repos/contents/) diff --git a/content/changes/2014-03-05-reminder-about-upcoming-cutover-test.md b/content/changes/2014-03-05-reminder-about-upcoming-cutover-test.md index e19dd70b96..3a6aabfff0 100644 --- a/content/changes/2014-03-05-reminder-about-upcoming-cutover-test.md +++ b/content/changes/2014-03-05-reminder-about-upcoming-cutover-test.md @@ -1,7 +1,5 @@ --- -kind: change title: "Reminder: March 12 Cutover Test for Default Media Type" -created_at: 2014-03-05 author_name: jasonrudolph --- diff --git a/content/changes/2014-03-12-page-build-event-for-webhooks.md b/content/changes/2014-03-12-page-build-event-for-webhooks.md index bdc50b2a1c..64e19a83c8 100644 --- a/content/changes/2014-03-12-page-build-event-for-webhooks.md +++ b/content/changes/2014-03-12-page-build-event-for-webhooks.md @@ -1,7 +1,5 @@ --- -kind: change title: Page Build Event for Webhooks -created_at: 2014-3-12 author_name: benbalter --- diff --git a/content/changes/2014-03-18-paginating-method-changes.md b/content/changes/2014-03-18-paginating-method-changes.md index 7366e928ae..9cba74b8db 100644 --- a/content/changes/2014-03-18-paginating-method-changes.md +++ b/content/changes/2014-03-18-paginating-method-changes.md @@ -1,7 +1,5 @@ --- -kind: change title: Pagination changes for some resource lists -created_at: 2014-03-18 author_name: pengwynn --- @@ -107,9 +105,9 @@ Here's the complete list of updated methods: [Gist commits]: /v3/gists/#list-gist-commits [Gist forks]: /v3/gists/#list-gist-forks [Git refs]: /v3/git/refs/#get-all-references -[Repository collaborators]: /v3/repos/collaborators/#list +[Repository collaborators]: /v3/repos/collaborators/#list-collaborators [Repository downloads]: /v3/repos/downloads/#list-downloads-for-a-repository -[Repository keys]: /v3/repos/keys/#list +[Repository keys]: /v3/repos/keys/#list-deploy-keys [Repository labels]: /v3/issues/labels/#list-all-labels-for-this-repository [Team repositories]: /v3/orgs/teams/#list-team-repos [User emails]: /v3/users/emails/#list-email-addresses-for-a-user @@ -121,7 +119,7 @@ Here's the complete list of updated methods: [Pull Request files]: /v3/pulls/#list-pull-requests-files [Release assets]: /v3/repos/releases/#list-assets-for-a-release [Repository contributors]: /v3/repos/#list-contributors -[Repository branches]: /v3/repos/#list-branches +[Repository branches]: /v3/repos/branches/#list-branches [Repository tags]: /v3/repos/#list-tags [Repository teams]: /v3/repos/#list-teams [Team members]: /v3/orgs/teams/#list-team-members diff --git a/content/changes/2014-03-27-combined-status-api.md b/content/changes/2014-03-27-combined-status-api.md index bb1c5dd742..2edc34295a 100644 --- a/content/changes/2014-03-27-combined-status-api.md +++ b/content/changes/2014-03-27-combined-status-api.md @@ -1,7 +1,5 @@ --- -kind: change title: Preview the New Combined Status API -created_at: 2014-03-27 author_name: bhuga --- diff --git a/content/changes/2014-04-04-create-public-repo-without-repo-scope.md b/content/changes/2014-04-04-create-public-repo-without-repo-scope.md index b1627b6f2b..1231f241a4 100644 --- a/content/changes/2014-04-04-create-public-repo-without-repo-scope.md +++ b/content/changes/2014-04-04-create-public-repo-without-repo-scope.md @@ -1,7 +1,5 @@ --- -kind: change title: Grant access to create public repositories without granting access to private repositories -created_at: 2014-04-04 author_name: pengwynn --- diff --git a/content/changes/2014-04-07-understanding-search-results-and-potential-timeouts.md b/content/changes/2014-04-07-understanding-search-results-and-potential-timeouts.md index baf4f56c8a..07090d55c5 100644 --- a/content/changes/2014-04-07-understanding-search-results-and-potential-timeouts.md +++ b/content/changes/2014-04-07-understanding-search-results-and-potential-timeouts.md @@ -1,7 +1,5 @@ --- -kind: change title: Understanding search results and potential timeouts -created_at: 2014-04-07 author_name: izuzak --- diff --git a/content/changes/2014-04-08-reset-api-tokens.md b/content/changes/2014-04-08-reset-api-tokens.md index ebaf80f642..ed07db685f 100644 --- a/content/changes/2014-04-08-reset-api-tokens.md +++ b/content/changes/2014-04-08-reset-api-tokens.md @@ -1,7 +1,5 @@ --- -kind: change title: "Recommendation: Reset OAuth authorizations" -created_at: 2014-04-08 author_name: pengwynn --- @@ -18,13 +16,18 @@ and use in its place. This new method provides a safe way to reset user authorizations without requiring users to re-authorize the application on the web. -Integrators can also use the existing revocation methods to [revoke all -tokens][] or [revoke a single token][] for their applications. +Integrators can also use the existing revocation methods to ~~revoke all +tokens~~ or [revoke a single token][] for their applications. + +{{#tip}} + +**UPDATE (2016-01-25):** API v3 no longer provides a method to revoke all of an application's tokens as previously referenced above. If you need to revoke all tokens for your application, you can do so via the settings page for your application. + +{{/tip}} If you have any questions or feedback, please [get in touch][contact]. [contact]: https://github.com/contact?form[subject]=API+resetting+tokens [api]: /v3/oauth_authorizations/#reset-an-authorization -[revoke all tokens]: /v3/oauth_authorizations/#revoke-all-authorizations-for-an-application [revoke a single token]: /v3/oauth_authorizations/#revoke-an-authorization-for-an-application [heartbleed-blog-post]: https://github.com/blog/1818-security-heartbleed-vulnerability diff --git a/content/changes/2014-04-09-reminder-about-default-media-type-change.md b/content/changes/2014-04-09-reminder-about-default-media-type-change.md index 295c34071a..ba70ed5456 100644 --- a/content/changes/2014-04-09-reminder-about-default-media-type-change.md +++ b/content/changes/2014-04-09-reminder-about-default-media-type-change.md @@ -1,7 +1,5 @@ --- -kind: change title: "Reminder: Default media type will change on April 15" -created_at: 2014-04-09 author_name: jasonrudolph --- diff --git a/content/changes/2014-04-10-deployment-api-preview-extension.md b/content/changes/2014-04-10-deployment-api-preview-extension.md index 968304164c..2087c59656 100644 --- a/content/changes/2014-04-10-deployment-api-preview-extension.md +++ b/content/changes/2014-04-10-deployment-api-preview-extension.md @@ -1,7 +1,5 @@ --- -kind: change title: Extending the preview period for the Deployments API -created_at: 2014-04-10 author_name: atmos --- diff --git a/content/changes/2014-04-22-deprecating-beta-media-type.md b/content/changes/2014-04-22-deprecating-beta-media-type.md index 3c726555d8..e212e5ae0e 100644 --- a/content/changes/2014-04-22-deprecating-beta-media-type.md +++ b/content/changes/2014-04-22-deprecating-beta-media-type.md @@ -1,13 +1,11 @@ --- -kind: change title: Deprecating the beta media type -created_at: 2014-04-22 author_name: jasonrudolph --- Now that the GitHub API is [serving the v3 media type by default][v3-default], we are deprecating the legacy [beta media type][beta]. -We will eventually remove support for the beta media type, but we have no official retirement date to annouce at the moment. When the time comes, rest assured that we'll announce the retirement with plenty of notice. In the meantime, existing API clients that rely on the beta media type should start making plans to migrate to v3. The beta media type differs from v3 in [just a few places][differences]. In most cases, migrating an application from the beta media type to the v3 media type is smooth and painless. +We will eventually remove support for the beta media type, but we have no official retirement date to announce at the moment. When the time comes, rest assured that we'll announce the retirement with plenty of notice. In the meantime, existing API clients that rely on the beta media type should start making plans to migrate to v3. The beta media type differs from v3 in [just a few places][differences]. In most cases, migrating an application from the beta media type to the v3 media type is smooth and painless. As always, if you have any questions, please [get in touch][contact]. diff --git a/content/changes/2014-04-25-user-content-security.md b/content/changes/2014-04-25-user-content-security.md new file mode 100644 index 0000000000..f1faba04eb --- /dev/null +++ b/content/changes/2014-04-25-user-content-security.md @@ -0,0 +1,35 @@ +--- +title: New user content domains +author_name: azizshamim +--- + +## Securing your content + +The [GitHub Bug Bounty program](https://bounty.github.com) recently identified a few cross-domain vulnerabilities related to user-generated content, and we've shipped improvements today to address those issues. + +In order to better isolate your content from potentially malicious content uploaded by other users (e.g., content that might contain Cross-Site Scripting or other embedded attacks), we now serve user-generated content from subdomains of **githubusercontent.com**. This content is no longer served from subdomains of **github.com**. + +## What's affected? + +This change affects the following subdomains: + +* **raw.github.com** : Serves raw file content from your repository. +* **embed.github.com** : Allows users to embed rich GitHub content on other sites. +* **render.github.com** : Displays rich content on GitHub.com. +* **f.cloud.github.com** : Hosts all those amazing gifs you use in Pull Requests and Issues. + +Content formerly served by these subdomains is now served from subdomains of **githubusercontent.com**. + +## Older links + +If you have old links to this content, don't worry: as of today, we're forcing the old domains to redirect to the new domains. Your existing links should continue to work automatically in your browser. If you're using a URL from Gist or GitHub to directly access user-generated content via `curl`, `wget`, or a library (like [HTTParty](https://github.com/jnunemaker/httparty)), be sure to configure that tool to follow the redirect. + +## Your proxies or filters + +Some security systems (web proxies, for example) may not recognize the **githubusercontent.com** domain. In those cases, you may need update your proxies and security software accordingly. + +As always, if you have any questions, please [get in touch][contact]. + +*Happy and safe GitHubbing!* + +[contact]: https://github.com/contact?form[subject]=Changes+to+user+content+domains diff --git a/content/changes/2014-05-06-gist-api-now-truncating-large-files.md b/content/changes/2014-05-06-gist-api-now-truncating-large-files.md new file mode 100644 index 0000000000..9b1fa4c26c --- /dev/null +++ b/content/changes/2014-05-06-gist-api-now-truncating-large-files.md @@ -0,0 +1,38 @@ +--- +title: "Changes to Gist API response for large files" +author_name: leongersing +--- + +In order to provide a faster, more robust API for Gist, we are making two changes to better handle large files in [Gist API responses][gist-json-representation]. + +### Truncating file contents larger than one megabyte + +The [Gist API response][gist-json-representation] includes data for every file in the Gist. That works well for Gists with reasonably-sized files. When a Gist contains large files, however, it can lead to timeouts when preparing or sending the API response. + +To eliminate those timeouts, the API now limits the amount of content returned for each file. If a file is larger than one megabyte in size, the API response will include the first megabyte of content for that file. (Few Gists have files this large. As a result, most API clients won't notice any impact from this change.) + +### New "truncated" attribute + +The JSON snippet below illustrates the attributes provided for each file in the Gist API response. In it, you'll notice a new `truncated` attribute included as part of the file metadata. This Boolean attribute indicates whether the `content` value is truncated for this request. + + { + files: { + "my_large_file.md": { + "size": 2097152, + "content": "Large content. Truncated at end of first megabyte. [...]", + "truncated": true, + "raw_url": "https://raw.githubusercontent.com/[...]/my_large_file.md", + "type": "text/plain", + "language": "Markdown" + } + } + } + +### Getting the full content for truncated files + +We recognize that sometimes you'll still want the full content for a file, even if it's too large to get returned in the standard Gist API response. For files under 10 megabytes, simply make a request to the URL specified in the `raw_url` attribute, and you'll receive the complete content for that file. For larger files, you'll need to clone the gist locally via the ```git_pull_url``` to access the full file contents. + +If you have any questions, don’t hesitate to [get in touch][contact]. + +[contact]: https://github.com/contact?form[subject]=Gist+API+now+truncates+large+files +[gist-json-representation]: /v3/gists/#detailed-gist-representation diff --git a/content/changes/2014-05-09-improved-pagination-for-the-repository-commits-api.md b/content/changes/2014-05-09-improved-pagination-for-the-repository-commits-api.md new file mode 100644 index 0000000000..b6d535ad9b --- /dev/null +++ b/content/changes/2014-05-09-improved-pagination-for-the-repository-commits-api.md @@ -0,0 +1,16 @@ +--- +title: Improved pagination for the Repository Commits API +author_name: izuzak +--- + +The [Repository Commits API](/v3/repos/commits/) now supports an additional approach for paginating [commit lists](/v3/repos/commits/#list-commits-on-a-repository). As of today, this endpoint supports the "standard" [`page` and `per_page` parameters](/v3/#pagination) for controlling pagination. This API now uses these parameters by default when constructing [page links](/v3/#pagination). + +## Improved results and increased consistency + +This new approach improves the reliability of this endpoint, which on rare occasions skipped some commits during pagination. This enhancement also increases the overall consistency of the API, as all endpoints now paginate resource lists the same way. + +## Old parameters still supported + +The old way of paginating, using `top`, `last_sha`, and `per_page` parameters, is still supported in API v3, but it will be removed in the [next major version of the API](https://developer.github.com/v3/versions/#v3-deprecations). API clients that are manually constructing URLs for pages should be modified to use the new parameters. Even better, API clients shouldn't construct URLs for pages manually, but should use [page links provided by the `Link` header](/guides/traversing-with-pagination/) in API responses. + +Since both the new and the old pagination parameters are still supported in API v3, API clients shouldn't notice any changes today. Still, if you notice any problems with this endpoint, please [let us know](https://github.com/contact?form%5Bsubject%5D=API:+Commits+pagination+improvements). diff --git a/content/changes/2014-05-19-deployments-api-updates.md b/content/changes/2014-05-19-deployments-api-updates.md new file mode 100644 index 0000000000..8343de77c2 --- /dev/null +++ b/content/changes/2014-05-19-deployments-api-updates.md @@ -0,0 +1,94 @@ +--- +title: New attributes for the Deployments API +author_name: atmos +--- + +We're continuing to iterate on the [Deployments API preview][deployments-preview], and we're starting to see it satisfy more and more use cases. Today we're introducing new attributes for Deployments and Deployment Statuses as well as a few payload changes. + +**This is a breaking change for Deployment Status payloads**. If you're trying out this new API during its preview period, you'll need to update your code to continue working with it. + +## API Changes + +For Deployments we're introducing the concept of an `environment`. An environment is basically a unique identifier for a deployment target. Lots of people tend toward the concept of environments for staging, QA, user acceptance testing, etc. We hope this enhancement will enable more use cases for our users that deploy to multiple environments. + +Deployments are also persisting the requested deployment `ref`. Previously we resolved a ref to the current SHA for that ref. Now we'll be keeping the ref around for historical purposes. This is especially helpful if you're deploying branches to verify them before you merge them into your default branch (e.g., "master"). + +## JSON Payload Changes + +We're also adding a few attributes to the outbound Deployment payloads. We're now including the `ref` attribute so you know the branch or tag name that resolved to a specific SHA. The `environment` is also present. + +## Webhook Changes + +The Deployment Status payloads now embed the associated Deployment object. With this enhancement, Deployment Status events received via webhooks will have enough information to notify other systems, without having to call back to the GitHub API for the `environment`, `ref`, or payload that was deployed. + +### Example Deployment JSON + +``` json +{ + "url": "https://api.github.com/repos/my-org/my-repo/deployments/392", + "id": 392, + "sha": "837db83be4137ca555d9a5598d0a1ea2987ecfee", + "ref": "master", + "environment": "staging", + "payload": { + "fe": [ + "fe1", + "fe2", + "fe3" + ] + }, + "description": "ship it!", + "creator": { + "login": "my-org", + "id": 521, + "avatar_url": "https://avatars.githubusercontent.com/u/2988?", + "type": "User" + }, + "created_at": "2014-05-09T19:56:47Z", + "updated_at": "2014-05-09T19:56:47Z", + "statuses_url": "https://api.github.com/repos/my-org/my-repo/deployments/392/statuses" +} +``` + +### Example Deployment Status JSON + +``` json +{ + "url": "https://api.github.com/repos/my-org/my-repo/deployments/396/statuses/1", + "id": 1, + "state": "success", + "deployment": { + "url": "https://api.github.com/repos/my-org/my-repo/deployments/396", + "id": 392, + "sha": "837db83be4137ca555d9a5598d0a1ea2987ecfee", + "ref": "master", + "payload": { + "fe": [ + "fe1", + "fe2", + "fe3" + ] + }, + "environment": "production", + "description": "Deploying to production", + "creator": { + "login": "alysson-goldner", + "id": 540, + "type": "User" + }, + "created_at": "2014-05-09T19:59:36Z", + "updated_at": "2014-05-09T19:59:36Z", + "statuses_url": "https://api.github.com/repos/my-org/my-repo/deployments/396/statuses" + }, + "description": "Deployment succeeded", + "target_url": "https://deploy.myorg.com/apps/my-repo/logs/420", + "created_at": "2014-05-09T19:59:39Z", + "updated_at": "2014-05-09T19:59:39Z", + "deployment_url": "https://api.github.com/repos/my-org/my-repo/deployments/396" +} +``` + +If you have any questions or feedback, please [get in touch][contact]. + +[contact]: https://github.com/contact?form[subject]=Deployments+API +[deployments-preview]: https://developer.github.com/changes/2014-01-09-preview-the-new-deployments-api/ diff --git a/content/changes/2014-06-09-new-attributes-for-pull-request-review-comment-events.md b/content/changes/2014-06-09-new-attributes-for-pull-request-review-comment-events.md new file mode 100644 index 0000000000..e8420a7c35 --- /dev/null +++ b/content/changes/2014-06-09-new-attributes-for-pull-request-review-comment-events.md @@ -0,0 +1,11 @@ +--- +title: New attributes for PullRequestReviewComment events +author_name: jdpace +--- + +We've enhanced the [PullRequestReviewComment events payloads][pr-review-comment-events] to include `action` and `pull_request` attributes. With the addition of the `pull_request` attribute, you now have immediate access to detailed information about the pull request without needing an additional API request. + +If you have any questions or feedback, please [get in touch][contact]. + +[contact]: https://github.com/contact?form[subject]=PullRequestReviewComment+Event+Payloads +[pr-review-comment-events]: https://developer.github.com/v3/activity/events/types/#pullrequestreviewcommentevent diff --git a/content/changes/2014-06-11-improved-ci-support-for-deployments-api.md b/content/changes/2014-06-11-improved-ci-support-for-deployments-api.md new file mode 100644 index 0000000000..8f5a6e1ab3 --- /dev/null +++ b/content/changes/2014-06-11-improved-ci-support-for-deployments-api.md @@ -0,0 +1,20 @@ +--- +title: Improved CI support for the Deployments API +author_name: atmos +--- + +Today we're making a few minor changes to the [Deployments API preview][2]. With the introduction of [combined statuses][4] in a [recent update][3], we noticed a few inconsistencies with the API that we'd like to remedy. + +We're introducing a new parameter called `required_contexts`. This parameter accepts an array of named [commit status][5] contexts that are ensured to be in a "success" state before the deployment is created. This allows you to verify that more than one system verified your code before you deploy it. + +We've removed support for the `force` parameter. The force parameter existed to bypass both the auto-merge and commit status checks. The same behavior can now be accomplished by setting `auto_merge` and `required_contexts` appropriately. + +We're also setting a context for all [commit statuses][5]. If a commit status is created without a context, we'll now set it to the string "default". + +If you have any questions or concerns, [drop us a line][1]. + +[1]: https://github.com/contact?form[subject]=Deployments+API +[2]: https://developer.github.com/changes/2014-01-09-preview-the-new-deployments-api/ +[3]: https://developer.github.com/changes/2014-04-10-deployment-api-preview-extension/ +[4]: https://developer.github.com/changes/2014-03-27-combined-status-api/ +[5]: https://developer.github.com/v3/repos/statuses/ diff --git a/content/changes/2014-06-19-combined-status-api-pagination.md b/content/changes/2014-06-19-combined-status-api-pagination.md new file mode 100644 index 0000000000..7cb5fc9c98 --- /dev/null +++ b/content/changes/2014-06-19-combined-status-api-pagination.md @@ -0,0 +1,20 @@ +--- +title: Pagination in the Combined Status API +author_name: bhuga +--- + +We're getting close to bringing the [Combined Status API][1] out of preview +mode, and have just a couple of small changes to make before it's :sparkles:. + +First, we're now [paginating][2] combined status API calls. The combined status +`state` field will always take all statuses into account, but we'll now only +return 100 embedded statuses at a time. + +Second, we're adding a `total_count` field, mirroring the Search API. This +count represents the number of contexts submitted for the given commit. + +As always, we're interested in [hearing your feedback][3]. + +[1]: /v3/repos/statuses/#get-the-combined-status-for-a-specific-ref +[2]: /v3/#pagination +[3]: https://github.com/contact?form[subject]=Combined+Status+API diff --git a/content/changes/2014-06-23-the-github-enterprise-api-documentation-has-a-new-home.md b/content/changes/2014-06-23-the-github-enterprise-api-documentation-has-a-new-home.md new file mode 100644 index 0000000000..4ec77ea539 --- /dev/null +++ b/content/changes/2014-06-23-the-github-enterprise-api-documentation-has-a-new-home.md @@ -0,0 +1,10 @@ +--- +title: The GitHub Enterprise API documentation has a new home! +author_name: gjtorikian +--- + +[GitHub Enterprise](https://enterprise.github.com) offers the same set of APIs as GitHub.com, as well as its own set of Enterprise-specific functionality. + +The GitHub Enterprise API has been documented on the Enterprise Help for some time. We've now [moved the resources to this site](https://developer.github.com/v3/enterprise/) to be hosted alongside the rest of the GitHub API documentation. + +Is there an API workflow you're particularly interested in? [Let us know](https://github.com/contact?form%5Bsubject%5D=Suggestion+for+an+Enterprise+Guide) and we'll do our best to [write a guide](https://developer.github.com/guides/)! diff --git a/content/changes/2014-07-07-example-webhook-payloads.md b/content/changes/2014-07-07-example-webhook-payloads.md new file mode 100644 index 0000000000..b7403f75f8 --- /dev/null +++ b/content/changes/2014-07-07-example-webhook-payloads.md @@ -0,0 +1,17 @@ +--- +title: New example webhook payloads +author_name: kdaigle +--- + +Today, we’ve added example [webhook][webhooks] payloads to the [event types][event-types] page. +Alongside existing descriptions for each event, we now include an [example payload][full-payload] +so that you can quickly see the data provided by the event. You can learn more about how webhooks +work with our [Webhooks Guide][webhooks-guide]. + +If you have any questions or feedback, please [get in touch][get-in-touch]. + +[webhooks]: https://github.com/blog/1778-webhooks-level-up +[event-types]: /v3/activity/events/types/ +[full-payload]: /v3/activity/events/types/#issuesevent +[webhooks-guide]: /webhooks/ +[get-in-touch]: https://github.com/contact?form[subject]=Example+webhook+payloads diff --git a/content/changes/2014-07-09-status-contexts-are-official.md b/content/changes/2014-07-09-status-contexts-are-official.md new file mode 100644 index 0000000000..614febd9d4 --- /dev/null +++ b/content/changes/2014-07-09-status-contexts-are-official.md @@ -0,0 +1,35 @@ +--- +title: The Combined Status API is official +author_name: bhuga +--- + +We're happy to announce that the [Combined Status API][docs] is officially part +of the GitHub API v3. We now consider it stable for production use. + +Thanks to everyone who provided feedback during the comment period. We got +some great feedback, and hope this feature helps you build the tools you +need to make GitHub the best place to ship exactly the way you want. + +### Preview media type no longer needed + +If you used the Combined Status API during the preview period, you needed to +provide a custom media type in the `Accept` header: + + application/vnd.github.she-hulk-preview+json + +Now that the preview period has ended, you no longer need to pass this custom +media type. + +Instead, we [recommend][media-types] that you specify `v3` as the version in the +`Accept` header: + + application/vnd.github.v3+json + +### Feedback + +We'll never be done listening to you! As always, please don't hesitate to +[share your feedback][feedback]. + +[docs]: /v3/repos/statuses/#get-the-combined-status-for-a-specific-ref +[media-types]: /v3/media +[feedback]: https://github.com/contact?form[subject]=Combined+Status+API diff --git a/content/changes/2014-07-28-assignee-and-label-actions-for-issue-events.md b/content/changes/2014-07-28-assignee-and-label-actions-for-issue-events.md new file mode 100644 index 0000000000..80e7045040 --- /dev/null +++ b/content/changes/2014-07-28-assignee-and-label-actions-for-issue-events.md @@ -0,0 +1,13 @@ +--- +title: New assigned/labeled actions for issue and pull request events +author_name: jdpace +--- + +As part of the [new GitHub Issues][issues-three], we've added new actions to the issues and pull requests webhook events: "labeled", "unlabeled", "assigned", and "unassigned". The payload will also include the respective assignee or label for these new actions. + +If you already have a [webhook](/webhooks/) subscribed to the `issues` or `pull_request` events, you'll start seeing these new actions immediately. The new events can also be fetched from the [issue events API](/v3/issues/events/). + +For more information, be sure to check out our documentation for the [IssuesEvent](/v3/activity/events/types/#issuesevent) or [PullRequestEvent](/v3/activity/events/types/#pullrequestevent). If you have any questions or feedback, please [drop us a line][contact]. + +[issues-three]: https://github.com/blog/1866-the-new-github-issues +[contact]: https://github.com/contact?form%5Bsubject%5D=New+Assigned+and+Labeled+Actions+for+Issues+and+Pull+Request+Events diff --git a/content/changes/2014-08-05-team-memberships-api.md b/content/changes/2014-08-05-team-memberships-api.md new file mode 100644 index 0000000000..fb85053ecb --- /dev/null +++ b/content/changes/2014-08-05-team-memberships-api.md @@ -0,0 +1,38 @@ +--- +title: We're changing the way you add new members to your organization +author_name: jakeboxer +--- + +Today, we're announcing a change to the way organization owners add new members to their organization. + +Previously, if you were an organization owner, you could use the [add team member][add-team-member] endpoint to add any GitHub user to any team on your organization without any sort of approval from them. Now, we're increasing user security by sending [invitations][org-invitations] to users when they're added to teams on organizations that they aren't yet a part of. + +With this change, if you use the [add team member][add-team-member] endpoint to add a user to a team and that user isn't already on another team in your organization, the request will fail. + +### The new Team Memberships API + +You should change all your [add team member][add-team-member] requests to use the new [add team membership][add-team-membership] endpoint. This new endpoint works exactly the same as the old one, with one important change: if the membership being added is for a user who is unaffiliated with the team's organization, that user will be sent an invitation via email. + +Unlike the [add team member][add-team-member] endpoint, a successful request to the [add team membership][add-team-membership] endpoint does *not* guarantee that the user is now a member of the team. If you're trying to migrate to the new endpoint and need to know when a user has been successfully added (not just invited) to a team, please check out [TeamAddEvent][team-add-event]. + +### Preview period + +We're making the new Team Memberships API (and the breaking changes to the [add team member][add-team-member] API) available today for developers to preview. During this period, we may change aspects of these endpoints. If we do, we will announce the changes on the developer blog, but we will not provide any advance notice. + +While these new APIs are in their preview period, you'll need to provide the following custom media type in the `Accept` header: + + application/vnd.github.the-wasp-preview+json + +We expect the preview period to last 30-60 days. At the end of the preview period, the Team Memberships API will become an official component of GitHub API v3, as will the [add team member][add-team-member] API's breaking changes. + +If you have any questions or feedback, please [get in touch with us][contact]! + +[contact]: https://github.com/contact?form[subject]=Team+Memberships+API +[org-invitations]: https://help.github.com/articles/adding-organization-members-to-a-team +[add-team-member]: /v3/orgs/teams/#add-team-member +[add-team-membership]: /v3/orgs/teams/#add-team-membership +[get-team-member]: /v3/orgs/teams/#get-team-member +[get-team-membership]: /v3/orgs/teams/#get-team-membership +[remove-team-member]: /v3/orgs/teams/#remove-team-member +[remove-team-membership]: /v3/orgs/teams/#remove-team-membership +[team-add-event]: /v3/activity/events/types/#teamaddevent diff --git a/content/changes/2014-08-15-deployments-api-changes.md b/content/changes/2014-08-15-deployments-api-changes.md new file mode 100644 index 0000000000..ac6455dc22 --- /dev/null +++ b/content/changes/2014-08-15-deployments-api-changes.md @@ -0,0 +1,27 @@ +--- +title: New features for the Deployments API preview +author_name: atmos +--- + +We've added two new features to the [Deployments API preview][deployments-preview]: the ability to query deployments and a new `task` attribute for different types of deployment tasks. + +## API changes + +You can now search for deployments via query parameters to the [listing endpoint][listing-endpoint]. You can filter on `sha`, `ref`, `task`, and `environment`. This makes it easier to answer questions like "when was the last time someone deployed to staging?" + +``` command-line +$ curl -H "Authorization: token [yours]" \ + https://api.github.com/repos/octocat/my-repo/deployments?environment=staging +``` + +## New attribute + +We've also added a `task` attribute to the deployment resource. The `task` attribute allows you to specify tasks other than just pushing code. Popular deployment tools like [capistrano][capistrano] and [fabric][fabric] support named tasks to do things like running schema migrations. We hope this attribute will give integrators the flexibility they need to provide custom functionality. + +If you have any questions or feedback, please [get in touch][contact]. + +[contact]: https://github.com/contact?form[subject]=Deployments+API +[deployments-preview]: https://developer.github.com/changes/2014-01-09-preview-the-new-deployments-api/ +[listing-endpoint]: https://developer.github.com/v3/repos/deployments/#list-deployments +[fabric]: http://www.fabfile.org/ +[capistrano]: http://capistranorb.com/ diff --git a/content/changes/2014-08-28-accepting-organization-invitations-from-the-api.md b/content/changes/2014-08-28-accepting-organization-invitations-from-the-api.md new file mode 100644 index 0000000000..e62023979b --- /dev/null +++ b/content/changes/2014-08-28-accepting-organization-invitations-from-the-api.md @@ -0,0 +1,36 @@ +--- +title: Accepting organization invitations from the API +author_name: jakeboxer +--- + +The upcoming [Team Memberships API][team-memberships-api] gives you the power to [invite][org-invitations] new GitHub users to your organization via the API. We're expanding the API to also allow users to view their organization membership statuses and accept any invitations they've received. + +### The new Organization Memberships API + +When someone [invites][org-invitations] you to an organization, your membership with that organization begins in the "pending" state. The new [list organization memberships][list-org-memberships] endpoint allows you to find your pending memberships. You can then change them to "active" (accepting the invitation in the process) by using the [edit organization membership][edit-org-membership] endpoint. + +### New Team Membership API response attribute + +Previously, responses from the [add team membership][add-team-membership] and [get team membership][get-team-membership] endpoints included a "status" attribute, which could either be "active" or "pending". We've renamed this attribute from "status" to "state" for better consistency with our other API calls. + +To give you time to update your apps, we'll keep the legacy "status" attribute around alongside the new "state" attribute until **September 4th, 2014**. + +### Preview period + +The new Organization Memberships API is available for developers to preview alongside the [Team Memberships API][team-memberships-api]. During this period, we may change aspects of these endpoints. If we do, we will announce the changes on the developer blog, but we will not provide any advance notice. + +While these new APIs are in their preview period, you'll need to provide the following custom media type in the `Accept` header: + + application/vnd.github.the-wasp-preview+json + +We expect the preview period to last 30-60 days. At the end of the preview period, the Team and Organization Memberships APIs will become official components of GitHub API v3. + +If you have any questions or feedback, please [get in touch with us][contact]! + +[contact]: https://github.com/contact?form[subject]=Team+Memberships+API +[team-memberships-api]: /changes/2014-08-05-team-memberships-api/ +[org-invitations]: https://help.github.com/articles/adding-organization-members-to-a-team +[list-org-memberships]: /v3/orgs/members/#list-your-organization-memberships +[edit-org-membership]: /v3/orgs/members/#edit-your-organization-membership +[add-team-membership]: /v3/orgs/teams/#add-team-membership +[get-team-membership]: /v3/orgs/teams/#get-team-membership diff --git a/content/changes/2014-09-05-removing-gravatar-id.md b/content/changes/2014-09-05-removing-gravatar-id.md new file mode 100644 index 0000000000..3d9f4442a1 --- /dev/null +++ b/content/changes/2014-09-05-removing-gravatar-id.md @@ -0,0 +1,21 @@ +--- +title: Removing Gravatar ID from user payloads +author_name: mastahyeti +--- + +We have deprecated the `gravatar_id` attribute in the [user +representation](https://developer.github.com/v3/users/). Starting September 19, +the API will always provide an empty string as the value for this attribute. + +Users have been able to upload avatars directly to GitHub for [a while +now](https://github.com/blog/1803-switch-your-picture-with-ease). If users +haven't uploaded an avatar, we still try to fetch one from Gravatar, but that +happens behind the scenes on GitHub's servers. As a result, the `gravatar_id` +attribute no longer identifies a GitHub user's canonical avatar. Instead, API +consumers should use the `avatar_url` to fetch a user's avatar. The `avatar_url` +attribute has always been present in the [v3 user representation](/v3/users/) +and is the only reliable way to find a GitHub user's avatar. + +If you have any questions or feedback, please [get drop us a line][contact]. + +[contact]: https://github.com/contact?form[subject]=Removing+Gravatar+ID diff --git a/content/changes/2014-09-12-changing-organization-feeds.md b/content/changes/2014-09-12-changing-organization-feeds.md new file mode 100644 index 0000000000..c885113e98 --- /dev/null +++ b/content/changes/2014-09-12-changing-organization-feeds.md @@ -0,0 +1,44 @@ +--- +title: Changing organization feeds in the Feeds API +author_name: mastahyeti +--- + +We have deprecated the `current_user_organization_url` attribute and the +`current_user_organization.href` attribute in the [Feeds API][docs]. If you make +use of these attributes, you'll want to update your code to use the new +`current_user_organization_urls` attribute instead. + +### Changes to the deprecated attributes + +Previously, the deprecated attributes returned URI template. For example: + +``` json +"current_user_organization_url": + "https://github.com/organizations/{org}/mastahyeti.private.atom?token=abc123" +``` + +The template included a deprecated authentication token. Our new tokens are +valid only for a concrete feed URL (not for a URI template). Because the +deprecated attributes were templates and did not specify a concrete URL, the API +could not provide a token that could be used for organization feeds. + +Starting today, the API returns empty values for the deprecated attributes. + +### New attribute for organization feeds + +In order to preserve the functionality of this API, we have added a new +attribute that lists specific Atom feed urls for each of the user's +organizations. + +``` json +"current_user_organization_urls": [ + "https://github.com/organizations/github/mastahyeti.private.atom?token=abc123" + "https://github.com/organizations/requests/mastahyeti.private.atom?token=token=def456" +] +``` + +Check out the updated [Feeds API documentation][docs] for the new fields. If you +have any questions or feedback, please [get drop us a line][contact]. + +[docs]: /v3/activity/feeds/ +[contact]: https://github.com/contact?form[subject]=Changing+organization+feeds+in+the+Feeds+API diff --git a/content/changes/2014-09-16-finalizing-the-organization-and-team-membership-apis.md b/content/changes/2014-09-16-finalizing-the-organization-and-team-membership-apis.md new file mode 100644 index 0000000000..5b6f7b340b --- /dev/null +++ b/content/changes/2014-09-16-finalizing-the-organization-and-team-membership-apis.md @@ -0,0 +1,28 @@ +--- +title: Finalizing the Organization and Team Membership APIs +author_name: jakeboxer +--- + +For the past few weeks, the new [Organization Membership][org-membership-api] and [Team Membership][team-membership-api] APIs have been available for early access via a preview media type. As of today, these APIs are stable and suitable for production use. + +### Preview period ends on September 23 + +On September 23, 2014, these APIs will become official parts of the GitHub API v3. At that time, the preview media type will no longer be required to access these APIs. + +### Reminder: Breaking change to legacy endpoint + +The [breaking change to the "Add team member" endpoint][add-team-member] will also go into effect for all requests on **September 23, 2014**. At that time, if you use the [add team member][add-team-member] endpoint to add a user to a team and that user isn't already on another team in your organization, the request will fail. To avoid this, be sure to use the [add team membership][add-team-membership] endpoint. + +### Addition to the Organization Membership API + +Thanks to your feedback, we've updated the Organization Membership API to provide direct access to basic information about the organization whenever you fetch a [list of memberships][list-org-memberships] or a [single membership][get-org-membership]. + +If you have any questions or feedback, please [get in touch with us][contact]! + +[contact]: https://github.com/contact?form[subject]=Organization+and+Team+Membership+APIs +[org-membership-api]: /changes/2014-08-28-accepting-organization-invitations-from-the-api/ +[team-membership-api]: /changes/2014-08-05-team-memberships-api/ +[add-team-member]: /v3/orgs/teams/#add-team-member +[add-team-membership]: /v3/orgs/teams/#add-team-membership +[list-org-memberships]: /v3/orgs/members/#list-your-organization-memberships +[get-org-membership]: /v3/orgs/members/#get-your-organization-membership diff --git a/content/changes/2014-09-23-one-more-week-before-the-add-team-member-api-breaking-change.md b/content/changes/2014-09-23-one-more-week-before-the-add-team-member-api-breaking-change.md new file mode 100644 index 0000000000..8ef7561d6d --- /dev/null +++ b/content/changes/2014-09-23-one-more-week-before-the-add-team-member-api-breaking-change.md @@ -0,0 +1,21 @@ +--- +title: One more week before the "Add team member" API breaking change +author_name: jakeboxer +--- + +**UPDATE (2014-09-30):** In response to feedback from developers, we're delaying the breaking change to the ["Add team member" API][add-team-member] until Monday, **October 6, 2014**. The change will go into effect for all requests on that date. + +Starting October 6, if you use [the "Add team member" API][add-team-member] to add a user to a team and that user isn't already on another team in your organization, the request will fail. To avoid this, be sure to use the ["Add team membership" API][add-team-membership]. + +### The Organization and Team Membership APIs are now official + +As promised in [our blog post earlier this month][finalizing], the [Organization Membership][org-membership-api] and [Team Membership][team-membership-api] APIs are now an official part of the GitHub API! The preview media type is no longer required to access them. + +If you have any questions or feedback, please [get in touch with us][contact]! + +[add-team-member]: /v3/orgs/teams/#add-team-member +[add-team-membership]: /v3/orgs/teams/#add-team-membership +[finalizing]: /changes/2014-09-16-finalizing-the-organization-and-team-membership-apis/ +[org-membership-api]: /changes/2014-08-28-accepting-organization-invitations-from-the-api/ +[team-membership-api]: /changes/2014-08-05-team-memberships-api/ +[contact]: https://github.com/contact?form[subject]=Organization+and+Team+Membership+APIs diff --git a/content/changes/2014-10-06-new-attributes-for-issue-events-api.md b/content/changes/2014-10-06-new-attributes-for-issue-events-api.md new file mode 100644 index 0000000000..009d26b12c --- /dev/null +++ b/content/changes/2014-10-06-new-attributes-for-issue-events-api.md @@ -0,0 +1,17 @@ +--- +title: New Attributes for Issue Events API +author_name: jdpace +--- + +We've made it easier to track changes to issues. The Issue Events API now provides more context for several event types: + +- `assigned` and `unassigned` events now include an `assignee` object so you can see just who was assigned or unassigned. +- `labeled` and `unlabeled` events include a `label` object. +- `milestoned` and `demilesoned` events include a `milestone` object. +- `renamed` events include a `rename` object with the title before and after the rename. + +Check out the [Issue Events API documentation][issue-events] for a full list of supported events. If you have +any questions or feedback, please [drop us a line][contact]. + +[issue-events]: /v3/issues/events/ +[contact]: https://github.com/contact?form[subject]=New+Attrs+for+Issue+Events+API diff --git a/content/changes/2014-10-16-removed-ssl-version-3-support-from-webhooks-and-services.md b/content/changes/2014-10-16-removed-ssl-version-3-support-from-webhooks-and-services.md new file mode 100644 index 0000000000..9414413fd5 --- /dev/null +++ b/content/changes/2014-10-16-removed-ssl-version-3-support-from-webhooks-and-services.md @@ -0,0 +1,14 @@ +--- +title: Removed SSLv3 support from webhooks and services +author_name: kdaigle +--- + +This morning, we [removed support][github-services-pr] for the `ssl_version` webhook configuration +option and made `TLS 1.X` the default cryptographic protocol to address the [POODLE exploit][poodle]. +You should no longer set or rely on the `ssl_version` configuration option. + +If you have any questions or feedback, please [drop us a line][contact]. + +[github-services-pr]: https://github.com/github/github-services/pull/949 +[poodle]: https://www.openssl.org/~bodo/ssl-poodle.pdf +[contact]: https://github.com/contact?form[subject]=Removed+SSLv3+support+from+webhooks+and+services diff --git a/content/changes/2014-10-21-deployment-webhook-payload-changes.md b/content/changes/2014-10-21-deployment-webhook-payload-changes.md new file mode 100644 index 0000000000..e74d85137c --- /dev/null +++ b/content/changes/2014-10-21-deployment-webhook-payload-changes.md @@ -0,0 +1,152 @@ +--- +title: Deployment webhook payload changes +author_name: atmos +--- + +On November 4th, 2014, we will begin sending a new format for [deployment][1] and [deployment status][2] payloads for webhooks. In the meantime we'll be running in a compatibility mode that will give integrators the time needed to start taking advantage of the new format. Integrators who are working with webhooks and deployments are advised to upgrade to the new payload format to avoid service interruption. + +This change brings the payloads for these events more inline with the responses you'd receive from the API. Instead of having deployment and deployment status attributes as top-level keys, we will now nest them under `deployment` and `deployment_status` keys. Since we're still in the [preview period][3] for the deployments API we felt it was best to correct this inconsistency now. + +## DeploymentEvent Changes + +#### Old Format + +``` json +{ + "id": 42, + "sha": "deadbeef", + "ref": "master", + "task": "deploy", + "name": "my-org/our-app", + "environment": "production", + "payload": {…}, + "description": "Deploying master", + "repository": {…}, + "sender": {…} +} +``` + +#### Current Format - 2014/10/22 + +``` json +{ + "id": 42, + "sha": "deadbeef", + "ref": "master", + "task": "deploy", + "name": "my-org/our-app", + "environment": "production", + "payload": {…}, + "description": "Deploying master", + "repository": {…}, + "deployment": { + "url": "https://api.github.com/repos/my-org/our-app/deployments/42", + "id": 42, + "sha": "deadbeef", + "ref": "master", + "task": "deploy", + "environment": "production", + "payload": {…}, + "description": "Deploying master", + "creator": {…}, + "created_at": "2014-09-23T16:37:49Z", + "updated_at": "2014-09-23T16:37:49Z", + "statuses_url": "https://api.github.com/repos/my-org/our-app/deployments/42/statuses" + }, + "sender": {…} +} +``` + +#### New Format - 2014/11/05 + +``` json +{ + "deployment": { + "url": "https://api.github.com/repos/my-org/our-app/deployments/42", + "id": 42, + "sha": "deadbeef", + "ref": "master", + "task": "deploy", + "environment": "production", + "payload": {…}, + "description": "Deploying master", + "creator": {…}, + "created_at": "2014-09-23T16:37:49Z", + "updated_at": "2014-09-23T16:37:49Z", + "statuses_url": "https://api.github.com/repos/my-org/our-app/deployments/42/statuses" + }, + "repository": {…}, + "sender": {…} +} +``` + +## DeploymentStatusEvent Changes + +#### Old Format + +``` json +{ + "id": 2600, + "state": "success", + "deployment": {…}, + "target_url": "https://gist.github.com/deadbeef", + "description": "Deployment was successful", + "repository": {…}, + "sender": {…} +} +``` + +#### Current Format - 2014/10/22 + +``` json +{ + "id": 2600, + "state": "success", + "target_url": "https://gist.github.com/deadbeef", + "description": "Deployment was successful", + "repository": {…}, + "deployment_status": { + "url": "https://api.github.com/repos/my-org/our-app/deployments/42/statuses2600", + "id": 2600, + "state": "success", + "creator": {…}, + "target_url": "https://gist.github.com/deadbeef", + "description": "Deployment was successful", + "created_at": "2014-09-23T16:45:49Z", + "updated_at": "2014-09-23T16:45:49Z", + "deployment_url": "https://api.github.com/repos/my-org/our-app/deployments/42", + "repository_url": "https://api.github.com/repos/my-org/our-app" + }, + "deployment": {…}, + "sender": {…} +} +``` + +#### New Format - 2014/11/05 + +``` json +{ + "deployment_status": { + "url": "https://api.github.com/repos/my-org/our-app/deployments/42/statuses2600", + "id": 2600, + "state": "success", + "creator": {…}, + "target_url": "https://gist.github.com/deadbeef", + "description": "Deployment was successful", + "created_at": "2014-09-23T16:45:49Z", + "updated_at": "2014-09-23T16:45:49Z", + "deployment_url": "https://api.github.com/repos/my-org/our-app/deployments/42", + "repository_url": "https://api.github.com/repos/my-org/our-app" + }, + "deployment": {…}, + "repository": {…}, + "sender": {…} +} +``` + +If you have any questions or feedback, please [get in touch][get-in-touch]. + +[1]: https://developer.github.com/v3/activity/events/types/#deploymentevent +[2]: https://developer.github.com/v3/activity/events/types/#deploymentstatusevent +[3]: https://developer.github.com/changes/2014-01-09-preview-the-new-deployments-api/ +[get-in-touch]: https://github.com/contact?form[subject]=Deployments+API diff --git a/content/changes/2014-10-24-status-api-limits.md b/content/changes/2014-10-24-status-api-limits.md new file mode 100644 index 0000000000..c58ae0ebe4 --- /dev/null +++ b/content/changes/2014-10-24-status-api-limits.md @@ -0,0 +1,16 @@ +--- +title: Status API Limits +author_name: rsanheim +--- + +To ensure a high level of service for all API consumers, we will soon limit the number of [statuses] +to 1000 per commit SHA, repository, and context. + +Beginning Monday, November 3rd, we will trim existing data sets that exceed this limit, deleting the oldest +records first. Attempts to create statuses beyond that limit will result in a [validation error]. + +If you have any feedback or questions, please don't hesitate to [contact] us. + +[statuses]: /v3/repos/statuses/ +[validation error]: https://developer.github.com/v3/#client-errors +[contact]: https://github.com/contact?form[subject]=Combined+Status+API diff --git a/content/changes/2014-11-25-the-deployments-api-is-official.md b/content/changes/2014-11-25-the-deployments-api-is-official.md new file mode 100644 index 0000000000..90bcc90c4d --- /dev/null +++ b/content/changes/2014-11-25-the-deployments-api-is-official.md @@ -0,0 +1,35 @@ +--- +title: The Deployments API is official +author_name: atmos +--- + +We're happy to announce that the [Deployments API][docs] is officially part +of GitHub API v3. We now consider it stable for production use. + +Thanks to everyone who provided feedback during the preview period. We got +some great feedback, and hope this feature helps you build the tools you +need to make GitHub the best place to ship exactly the way you want. + +### Preview media type no longer needed + +If you used the Deployments API during the preview period, you needed to +provide a custom media type in the `Accept` header: + + application/vnd.github.cannonball-preview+json + +Now that the preview period has ended, you no longer need to pass this custom +media type. + +Instead, we [recommend][media-types] that you specify `v3` as the version in the +`Accept` header: + + application/vnd.github.v3+json + +### Feedback + +We'll never be done listening to you! As always, please don't hesitate to +[share your feedback][feedback]. + +[docs]: /v3/repos/deployments +[media-types]: /v3/media +[feedback]: https://github.com/contact?form[subject]=Deployments+API diff --git a/content/changes/2014-12-03-preview-the-new-organization-webhooks-api.md b/content/changes/2014-12-03-preview-the-new-organization-webhooks-api.md new file mode 100644 index 0000000000..f64f7a2f3a --- /dev/null +++ b/content/changes/2014-12-03-preview-the-new-organization-webhooks-api.md @@ -0,0 +1,40 @@ +--- +title: Preview the New Organization Webhooks API +author_name: jdpace +--- + +Today we're very excited [to announce Organization Webhooks][dotcom-blog-post]. +Organization Webhooks allow you to subscribe to events that happen across an +entire organization. + +In addition to being able to subscribe to the existing repository oriented +events across an organization, we're also adding some new events which are +exclusive to organization webhooks. The new [`repository` +event][repository-event] allows you to receive webhook payloads when a new +repository is created. By subscribing to the [`membership` +event][membership-event], you'll be notified whenever a user is added or +removed from a team. + +We’re making this new API for Organization Webhooks available today [for +developers to preview][docs-preview]. The preview period will allow us to [get +your feedback][contact] before declaring the Organization Webhooks API final. +We expect the preview +period to last for roughly 30-60 days. + +As we discover opportunities to improve the API during the preview period, we +may ship changes that break clients using the preview version of the API. We +want to iterate quickly. To do so, we will announce any changes here (on the +developer blog), but we will not provide any advance notice. + +At the end of preview period, the Organization Webhooks API will become an +official component of GitHub API v3. At that point, the new Organization +Webhooks API will be stable and suitable for production use. + +We hope you’ll take it for a spin and [send us your feedback][contact]. + +[dotcom-blog-post]: https://github.com/blog/1933-introducing-organization-webhooks +[repository-event]: /v3/activity/events/types/#repositoryevent +[membership-event]: /v3/activity/events/types/#membershipevent +[docs]: /v3/orgs/hooks/ +[docs-preview]: /v3/orgs/hooks/ +[contact]: https://github.com/contact?form[subject]=Organization+Webhooks diff --git a/content/changes/2014-12-08-organization-permissions-api-preview.md b/content/changes/2014-12-08-organization-permissions-api-preview.md new file mode 100644 index 0000000000..cc32c582c4 --- /dev/null +++ b/content/changes/2014-12-08-organization-permissions-api-preview.md @@ -0,0 +1,105 @@ +--- +title: Preview the upcoming organization permission changes +author_name: jakeboxer +--- +**UPDATE (2014-12-12):** The [List your organizations][list-your-organizations] API is now included in this preview as well. + +We have some upcoming changes that will affect the way organization members and repositories are managed. The most important changes are: + +- The Owners team will no longer be special. +- The [List your repositories][list-your-repos] API will include organization-owned repositories. +- The [List user organizations][list-user-organizations] API will only include public organization memberships. +- The [List your organizations][list-your-organizations] API will require `user` scope or `read:org` scope. + +## What's happening to the Owners team? + +Currently, members of your Owners team are administrators of your organization. Soon, your Owners team will become a totally normal team. Adding and removing Owners team members won't change their administrator status anymore. Instead, you'll be able to directly grant admin permissions to your organization's members without adding them to any special teams. + +We won't delete your Owners team, but you'll be able to delete or rename it yourself if you want. Organizations created after the change won't have an Owners team. + +### What should you do? + +In preparation for this change to the Owners team, we're releasing a few new APIs. You'll be able to use these APIs to manage organization admins without relying on the Owners team. + +#### Adding an organization admin + +To add a new organization admin, use the new [Add or update organization membership][add-org-membership] endpoint, specifying a role of `"admin"` in the request body. This replaces adding or inviting people to the Owners team. + +#### Removing an organization admin + +To remove someone from the organization role but keep them as a member of their teams, use the new [Add or update organization membership][add-org-membership] endpoint, specifying a role of `"member"` in the request body. This replaces removing people from the Owners team. + +#### Listing organization admins + +To get a list of all your organization's admins, use the [Organization members list][list-org-members] endpoint, specifying a role of `"admin"` in the query string. This replaces listing the members of the Owners team. + +#### Checking if someone is an organization admin + +To check if a given user is an organization admin, use the new [Get organization membership][get-org-membership] endpoint. If the returned `"role"` attribute is set to `"admin"` and the returned `"state"` attribute is set to `"active"`, the user is an organization admin. This replaces checking if a user is on the Owners team. + +## What's happening to the "List your repositories" API? + +Currently, the [List your repositories][list-your-repos] API only returns repositories that are owned by users, not by organizations. If you want a list of *all* the repositories that the authenticated user has access to, you need to use multiple API methods. + +Soon, this API will include all repositories that the authenticated user has access to (whether they're owned by a user or by an organization). + +### What should you do? + +Many apps use the [List your repositories][list-your-repos] API in conjunction with the [List your organizations][list-your-orgs] and [List organization repositories][list-org-repos] APIs to build up a list of all the repositories the authenticated user has access to. If your app is doing this, you'll be able to get rid of all the organization-related API calls and just use the [List your repositories][list-your-repos] API. + +If your app uses the [List your repositories][list-your-repos] API for another purpose, you'll need to update your app to handle the new organization-owned repositories we'll be returning. + +## What's happening to the "List user organizations" API? + +The [List user organizations][list-user-organizations] API is intended provide [public organization memberships][public-org-membership] for any user. When you use this API to fetch *your own* organizations, this API currently returns your public and private organization memberships. + +Soon, this API will only return public organization memberships. + +### What should you do? + +If your app uses the [List user organizations][list-user-organizations] API to fetch all of the organization memberships (public and private) for the authenticated user, you'll need to update your app to use the [List your organizations][list-your-organizations] API instead. The [List your organizations][list-your-organizations] API returns all organizations (public and private) that your app is authorized to access. + +## What's happening to the "List your organizations" API? + +OAuth requests will soon require minimum [scopes][] in order to access the [List your organizations][list-your-organizations] API. + +Currently, the API response always includes your [public organization memberships][public-org-membership], regardless of the OAuth scopes associated with your request. If you have `user`, `read:org`, `write:org`, or `admin:org` scope, the response also includes your private organization memberships. + +Soon, this API will only return organizations that your authorization allows you to operate on in some way (e.g., you can list teams with `read:org` scope, you can publicize your organization membership with `user` scope, etc.). Therefore, this API will require at least `user` or `read:org` scope. (`write:org` and `admin:org` scope implicitly include `read:org` scope.) OAuth requests with insufficient scope will receive a `403 Forbidden` response. + +### What should you do? + +If you [authenticate via username and password][username-password-authn], you are not affected by this change. + +If your app only needs to fetch the user's public organization memberships, you should use the [List user organizations][list-user-organizations] API instead. Since that API only returns public information, it does not require any scopes. + +## Preview period + +Starting **today**, these new APIs are available for developers to preview. We expect the preview period to last for four weeks. (Stay tuned to the developer blog for updates.) At the end of the preview period, these additions will become official components of the GitHub API. + +While these additions are in their preview period, you'll need to provide the following custom media type in the `Accept` header: + + application/vnd.github.moondragon-preview+json + +During the preview period, we may change aspects of these endpoints. If we do, we will announce the changes on the developer blog, but we will not provide any advance notice. + +## Migration period + +At the end of the preview period, we will announce the start of a migration period. At that time, developers should update their applications to use the new APIs for managing organization admins. During this period, you will still be able to use the Owners team to manage your organization's admins, so that you have time to update your applications to use the new APIs without breakage. We expect the migration period to last for four weeks. + +At the end of the migration period, the Owners team will no longer be special, and you'll no longer be able to rely on it for managing organization admins. + +If you have any questions or feedback, please [get in touch with us][contact]! + +[contact]: https://github.com/contact?form[subject]=Organization+Admin+Pre-release+Preview +[list-your-repos]: /v3/repos/#list-your-repositories +[list-your-orgs]: /v3/orgs/#list-your-organizations +[list-org-repos]: /v3/repos/#list-organization-repositories +[add-org-membership]: /v3/orgs/members/#add-or-update-organization-membership +[list-org-members]: /v3/orgs/members/#members-list +[get-org-membership]: /v3/orgs/members/#get-organization-membership +[list-user-organizations]: /v3/orgs/#list-user-organizations +[list-your-organizations]: /v3/orgs/#list-your-organizations +[public-org-membership]: https://help.github.com/articles/publicizing-or-concealing-organization-membership +[username-password-authn]: /v3/auth/#via-username-and-password +[scopes]: /v3/oauth/#scopes diff --git a/content/changes/2014-12-08-removing-authorizations-token.md b/content/changes/2014-12-08-removing-authorizations-token.md new file mode 100644 index 0000000000..994fe04884 --- /dev/null +++ b/content/changes/2014-12-08-removing-authorizations-token.md @@ -0,0 +1,103 @@ +--- +title: Removing token attribute from Authorizations API responses +author_name: ptoomey3 +--- + +Since OAuth access tokens function like passwords, they should be treated with +care. Today we are making it easier to more securely work with authorizations +via the Authorizations API. We are deprecating the use of the `token` +attribute in the majority of the [Authorizations API](/v3/oauth_authorizations/) +responses. For the [affected APIs][authorizations-token-deprecation-notice], the +`token` attribute will soon return an empty string. To get ready for that +change, we are giving developers a chance to +[preview the updated API](#preview-period) starting today. + +## What's changing? + +The current [OAuth Authorizations API](/v3/oauth_authorizations/) requires GitHub to store the full value for +each OAuth token on our servers. In order to increase the security for our +users, we are changing our architecture to store the SHA-256 digest of OAuth +tokens instead. GitHub securely hashes user passwords using bcrypt and we want +to provide comparable security for OAuth tokens as well. + +Rest assured that this change is an entirely proactive measure from GitHub and is not associated with any security incident. + +## Who is affected? + +This change affects any code that relies on accessing the `token` attribute from +[these OAuth Authorizations API responses][authorizations-token-deprecation-notice]. +For example, our own [GitHub for Mac][github-for-mac] and +[GitHub for Windows][github-for-windows] applications relied on reading the `token` +from the [Get-or-create an authorization for a specific app][get-or-create-for-app] API, in order to support multiple installations of our desktop application for a single user. + +## What should you do? + +In order to reduce the impact of removing the `token` attribute, the OAuth +Authorizations API has added a new request attribute (`fingerprint`), added +three new response attributes (`token_last_eight`, `hashed_token`, and +`fingerprint`), and added [one new API][get-or-create-for-app-fingerprint]. +While these new APIs and attributes do not replace the full functionality that +previously existed, they can be used in place of `token` for most common use cases. + +* `token_last_eight` returns the last eight characters of the associated OAuth +token. As an example, `token_last_eight` could be used to display a list of +partial token values to help a user manage their OAuth tokens. + +* `hashed_token` is the base64 of the SHA-256 digest of the token. +`hashed_token` could be used to programmatically validate that a given token +matches an authorization returned by the API. + +* `fingerprint` is a new optional request parameter that allows an OAuth +application to create multiple authorizations for a single user. `fingerprint` +should be a string that distinguishes the new authorization from others +for the same client ID and user. + + For example, to differentiate installations of a desktop application across + multiple devices you might set `fingerprint` to + `SHA256_HEXDIGEST("GitHub for Mac - MAC_ADDRESS_OF_MACHINE")`. Since + `fingerprint` is not meant to be a user-facing value, you should still set + the `note` attribute to help a user differentiate between authorizations on their + [OAuth applications listing on GitHub][app-listing]. + +* [Get-or-create an authorization for a specific app and fingerprint][get-or-create-for-app-fingerprint] +is a new API that is analogous to the +[Get-or-create an authorization for a specific app][get-or-create-for-app] +API, but adds support for the new `fingerprint` request parameter. + +## Preview period + +We are making the new Authorizations API available today for developers to +preview. During this period, we may change aspects of these endpoints. If we do, +we will announce the changes on the developer blog, but we will not provide any +advance notice. + +While these new APIs are in their preview period, you’ll need to provide the +following custom media type in the Accept header: + + application/vnd.github.mirage-preview+json + +We expect the preview period to last 4-6 weeks. (Stay tuned to the developer blog for updates.) At the end of the preview period, these changes will become an official and stable part of GitHub API. + +## Migration period + +At the end of the preview period, we will announce the start of a migration period. Developers will have 8 weeks to update existing code to use the new APIs. + +## Why SHA-256 over bcrypt? + +Some users may be curious why we are not using bcrypt to hash our OAuth tokens +like we do for user passwords. Bcrypt is purposefully computationally expensive +in order to mitigate brute force attacks against low entropy passwords. However, +OAuth tokens are highly random and are not susceptible to brute force attacks. +Given that OAuth token validation occurs for each request to the API we chose +SHA-256 for performance reasons. + +If you have any questions or feedback, please [drop us a line][contact]. + +[contact]: https://github.com/contact?form[subject]=Removing+authorizations+token +[app-listing]: https://github.com/settings/applications +[create-a-new-authorization]: /v3/oauth_authorizations/#create-a-new-authorization +[get-or-create-for-app]: /v3/oauth_authorizations/#get-or-create-an-authorization-for-a-specific-app +[get-or-create-for-app-fingerprint]: /v3/oauth_authorizations/#get-or-create-an-authorization-for-a-specific-app-and-fingerprint +[github-for-mac]: https://mac.github.com/ +[github-for-windows]: https://windows.github.com/ +[authorizations-token-deprecation-notice]: /v3/oauth_authorizations/#deprecation-notice diff --git a/content/changes/2014-12-09-new-attributes-for-stars-api.md b/content/changes/2014-12-09-new-attributes-for-stars-api.md new file mode 100644 index 0000000000..8f0f6673d4 --- /dev/null +++ b/content/changes/2014-12-09-new-attributes-for-stars-api.md @@ -0,0 +1,19 @@ +--- +title: New Attributes for Starring API +author_name: arfon +--- + +You can now see when a user starred a repository. To receive the new response format containing the `starred_at` field, request the new media type: + +``` command-line +curl -H "Accept: application/vnd.github.v3.star+json" https://api.github.com/users/andrew/starred +``` + +Note the starred repository is now available in the repo field. + +### Feedback + +If you have any questions or feedback about these changes, please [drop us a line][contact]. + +[starring]: /v3/activity/starring/#list-repositories-being-starred-with-star-creation-timestamps +[contact]: https://github.com/contact?form[subject]=New+Attributes+for+Starring+API diff --git a/content/changes/2014-12-12-replace-older-ssh-keys-created-by-your-application.md b/content/changes/2014-12-12-replace-older-ssh-keys-created-by-your-application.md new file mode 100644 index 0000000000..41c509f4cc --- /dev/null +++ b/content/changes/2014-12-12-replace-older-ssh-keys-created-by-your-application.md @@ -0,0 +1,35 @@ +--- +title: Replace older SSH keys created by your application +author_name: jasonrudolph +--- +Back in February, we [improved the security audit trail for SSH keys](/changes/2014-02-24-finer-grained-scopes-for-ssh-keys/#keys-are-now-immutable). Soon, organizations will be able to block access for SSH keys that were created prior to those improvements. If your application relies on [deploy keys](/guides/managing-deploy-keys/#deploy-keys) or [user keys](/v3/users/keys/) for repository access, we recommend replacing any keys created before February 24, 2014. + +To ensure that your application is not affected by organizations blocking access to these keys, **you should replace the affected keys by January 15, 2015**. + +## How should you replace these keys? + +We recommend the following steps for identifying and replacing the affected keys. + +### 1. Identify the affected keys + +You only need to replace keys that your application created prior to February 24, 2014. If you don't know when your app created a given key, you can get the creation timestamp from the API. The `created_at` property is available for [deploy keys](/v3/repos/keys/) and for [user keys](/v3/users/keys/#list-your-public-keys). + +### 2. Inform the affected users + +Once you know which keys you need to replace, we recommend that you inform the affected users. + +For security, GitHub automatically sends an email to a user whenever a new SSH key is added to their account. Similarly, when a new deploy key is added to a repository, GitHub sends an email to the repository's administrators. When you replace your application's old keys with new ones, GitHub will email the affected users. To avoid surprising those users, you should alert them that you'll be replacing your keys. You may want to include a link to this post in your message. + +### 3. Add a new key + +Use the API to add the new [deploy key](/v3/repos/keys/#add-a-new-deploy-key) or [user key](/v3/users/keys/#create-a-public-key). + +### 4. Delete the old key + +Once your application is using the new key, use the API to delete the old one. There's an [API for deleting deploy keys](/v3/repos/keys/#remove-a-deploy-key) and an [API for deleting user keys](/v3/users/keys/#delete-a-public-key). + +## We're here to help + +As always, if you have any questions or concerns, please [get in touch][contact]. + +[contact]: https://github.com/contact?form[subject]=Replace+SSH+keys+created+by+application diff --git a/content/changes/2015-01-07-prepare-for-organization-permissions-changes.md b/content/changes/2015-01-07-prepare-for-organization-permissions-changes.md new file mode 100644 index 0000000000..9df288c09f --- /dev/null +++ b/content/changes/2015-01-07-prepare-for-organization-permissions-changes.md @@ -0,0 +1,36 @@ +--- +title: Prepare for upcoming organization permissions changes +author_name: jakeboxer +--- + +**UPDATE (2015-06-10):** As [announced on June 10][2015-06-10-update], these changes will become an official part of GitHub API v3 on June 24. (This post originally announced that these changes would come to GitHub API v3 on February 24.) + +Last month, we [released a preview][org-permissions-preview] of several API changes related to managing organization members and repositories. Today, we're finalizing these changes. This new functionality is now stable and suitable for production use. If your application relies on any of the affected functionality (described below), be sure to **update your code before June 24** to account for these changes. + +## Breaking changes coming on June 24 + +If your application uses any of the following APIs, then you are affected by this change: + +- APIs for managing your organization's admins through the Owners team +- The [List your repositories][list-your-repos] API +- The [List your organizations][list-your-organizations] API +- The [List user organizations][list-user-organizations] API + +If your application uses these APIs, we urge you to update your application as soon as possible. (Read [last month's announcement][org-permissions-preview] for more details on the changes.) + +Starting today, we're offering a migration period allowing applications to opt in to these changes (as described below). On June 24, these changes will become official parts of the GitHub API v3. At that time, these changes will apply to all API consumers. + +## Migration period + +During the migration period, you can opt-in to these changes using the following custom media type in the `Accept` header: + + application/vnd.github.moondragon+json + +We want to make these updates as smooth as possible for everyone, and we hope that the migration period gives you flexibility to adopt these changes on your own schedule. If you have any questions or feedback, please [get in touch with us][contact]! + +[org-permissions-preview]: /changes/2014-12-08-organization-permissions-api-preview/ +[list-your-repos]: /v3/repos/#list-your-repositories +[list-user-organizations]: /v3/orgs/#list-user-organizations +[list-your-organizations]: /v3/orgs/#list-your-organizations +[contact]: https://github.com/contact?form[subject]=Organization+Permissions+API +[2015-06-10-update]: /changes/2015-06-10-breaking-changes-to-organization-permissions-coming-on-june-24/ diff --git a/content/changes/2015-01-08-discovering-resources-for-a-user.md b/content/changes/2015-01-08-discovering-resources-for-a-user.md new file mode 100644 index 0000000000..7687d01fcd --- /dev/null +++ b/content/changes/2015-01-08-discovering-resources-for-a-user.md @@ -0,0 +1,10 @@ +--- +title: "New guide: Discovering resources for a user" +author_name: jasonrudolph +--- + +Is your application taking advantage of the recommended workflow for discovering a user's repositories and organizations? With the [recent improvements to the API](/changes/2014-12-08-organization-permissions-api-preview/), the process is simpler than ever. In our newest guide, we show you how to [reliably identify the resources that your app can access for a given user](/guides/discovering-resources-for-a-user/). + +If you have any questions or feedback, we'd love to [hear from you][contact]. + +[contact]: https://github.com/contact?form%5Bsubject%5D=API+v3:+Discovering+resources+for+a+user diff --git a/content/changes/2015-01-19-an-integrators-guide-to-organization-application-policies.md b/content/changes/2015-01-19-an-integrators-guide-to-organization-application-policies.md new file mode 100644 index 0000000000..0630465be3 --- /dev/null +++ b/content/changes/2015-01-19-an-integrators-guide-to-organization-application-policies.md @@ -0,0 +1,97 @@ +--- +title: "An integrator's guide to organization application policies" +author_name: pengwynn +--- + +As we [announced over on the GitHub blog][ann], organization admins can now +control how third-party applications access their organization data. Allowing +admins to approve or deny applications will ultimately result in deeper trust +and increase overall adoption of integrations within organizations on GitHub. + +As an integrator, here's what you need to know about organization application +policies and how this feature could impact your application. + +### Guiding principles + +We've tried to strike the right balance between organization privacy and the +user experience for integrators and end users. Organizations should be able to +prevent applications they do not trust from accessing their organization data +without creating a multitude of new edge cases for integrators. + +With that goal in mind, the feature works like this: **if an organization's +application policy prevents an application from accessing its resources, the +API behaves as if the authenticating user is not a member of the +organization**. Specifically, this means an application authenticating on +behalf of a user using OAuth will have: + +- **Read-only access to public resources.** Organization-owned public + repositories, issues, and other resources will be visible via the API and + show up in resource listings, but mutating methods (`POST`, `PATCH`, `PUT`, + and `DELETE`) will return status `403`. +- **No access to private resources.** Organization-owned private repositories, + issues, and other resources will not be visible via the API and will not + show up in resource [listings][] that co-mingle public and private + resources. Hooks for these private repositories are muted and will not be + delivered as long as the application is restricted by the organization. + +Since applications should already handle the scenario where a user loses access +to organization resources, this reduces the work integrators need to do. + +### Checking organization access + +As organization admins adopt application whitelists and restrict third-party +application access to organization resources, your application may lose access +to those resources. If an organization member is not aware of the new access +policy, they may wonder why their private repositories or other resources no +longer work or show up in your application. + +There are a couple ways to help troubleshoot access for your end users. + +- **Via the GitHub UI.** The simplest way to help end users understand how + organization access policies affect their access to your application is to + provide a link to [their authorization details][help-request-approval] + under their GitHub account settings as [described in the OAuth + documentation][auth-link]. + +- **Via the API.** For an even better user experience, [use the + API][discovering-guide] to list which user organizations your application + can access, and provide users with the link mentioned above to request + access from their organization admins. + +### Listing accessible organization resources + +In addition to checking access to a user's organizations, you'll want to ensure +you're discovering their accessible resources in the most efficient way. Recent +changes to the [Repositories API][listing-repos] might reduce the API calls +your application needs to make to find a user's repositories across all of +their organization memberships. + +### Ensuring uninterrupted SSH access + +Since applications should already handle the scenario where a user loses access +to organization resources (e.g., when a user leaves an organization), this +reduces the work integrators need to do. Keys created by OAuth applications (or +those created before GitHub started tracking that information) will not have +access to repositories owned by organizations that restrict third-party +applications. If your application uses keys **created before February 24, +2014**, you [should replace those older keys][keys] to ensure things keep +running smoothly for your application. + +### We're here to help + +This is a big feature, and we're sure it will impact many of our integrators as +organizations adopt third-party application restrictions. We also think it +provides a huge net benefit for integrators as organizations choose to use +OAuth integrations with more confidence. + +If you have any questions or feedback, please [get in touch][contact]. + +[ann]: https://github.com/blog/1941-organization-approved-applications +[auth-link]: /v3/oauth/#directing-users-to-review-their-access-for-an-application +[help-request-approval]: https://help.github.com/articles/requesting-organization-approval-for-your-authorized-applications/ +[list-orgs]: /v3/orgs/#list-your-organizations +[contact]: https://github.com/contact?form[subject]=Organization+Access+Policies+help+for+integrators +[listing-repos]: /v3/repos/#list-your-repositories +[discovering-guide]: /guides/discovering-resources-for-a-user/ +[keys]: /changes/2014-12-12-replace-older-ssh-keys-created-by-your-application/ +[listings]: /v3/issues/#list-issues diff --git a/content/changes/2015-02-03-removing-authorizations-token-update.md b/content/changes/2015-02-03-removing-authorizations-token-update.md new file mode 100644 index 0000000000..a7d53f037b --- /dev/null +++ b/content/changes/2015-02-03-removing-authorizations-token-update.md @@ -0,0 +1,15 @@ +--- +title: Removing token attribute from Authorizations API responses (Update) +author_name: ptoomey3 +--- + +In December, we [released a preview][removing-authorizations-token] of several API changes related to managing OAuth application authorizations. As part of those changes we introduced several new response attributes (`token_last_eight`, `hashed_token`, and `fingerprint`) to the Authorizations API. We have decided to modify `hashed_token` to return the SHA-256 hex digest of the associated token instead of Base64. Given that Base64 has several common variants (original, URL safe, etc) we decided that returning the value as hex is less ambiguous and will be more useful for developers. + +### Extended preview period + +Because of the change to `hashed_token`, we are extending the preview period by two weeks. If no additional changes are made during this extended preview period we will announce the end of the preview and beginning of the eight week migration period on February 17. The migration period will allow applications to opt in to these changes before they become an official part of the GitHub API v3. + +If you have any questions or feedback, please [drop us a line][contact]! + +[removing-authorizations-token]: /changes/2014-12-08-removing-authorizations-token/ +[contact]: https://github.com/contact?form[subject]=Removing+authorizations+token diff --git a/content/changes/2015-02-18-new-releases-api-methods.md b/content/changes/2015-02-18-new-releases-api-methods.md new file mode 100644 index 0000000000..639bcb10b4 --- /dev/null +++ b/content/changes/2015-02-18-new-releases-api-methods.md @@ -0,0 +1,19 @@ +--- +title: New Releases API methods +author_name: pengwynn +--- + +We've added two new methods to the [Releases API][]. You can now get the [latest published release][latest] for a repository. + + GET /repos/:owner/:repo/releases/latest + +You can also get a [release by tag name][by-tag]. + + GET /repos/:owner/:repo/releases/tags/:tag + +If you have any questions or feedback, please [get in touch][contact]. + +[Releases API]: /v3/repos/releases/ +[latest]: /v3/repos/releases/#get-the-latest-release +[by-tag]: /v3/repos/releases/#get-a-release-by-tag-name +[contact]: https://github.com/contact?form[subject]=New+Releases+API+methods diff --git a/content/changes/2015-02-20-migration-period-removing-authorizations-token.md b/content/changes/2015-02-20-migration-period-removing-authorizations-token.md new file mode 100644 index 0000000000..9b154e13f2 --- /dev/null +++ b/content/changes/2015-02-20-migration-period-removing-authorizations-token.md @@ -0,0 +1,38 @@ +--- +title: Breaking changes to Authorizations API responses on April 20 +author_name: ptoomey3 +--- + +A couple weeks ago we [extended the preview period][removing-authorizations-token-extended-preview] of several API changes related to managing OAuth application authorizations. Today, we're finalizing these changes. This new functionality is now stable and suitable for production use. If your application relies on any of the affected functionality (described below), be sure to **update your code before April 20** to account for these changes. + +### Breaking changes coming on April 20 + +If your application uses any of the following APIs, then you may be affected by this change: + +- The [List your authorizations][list-your-authorizations] API +- The [Get a single authorization][get-a-single-authorization] API +- The [Get-or-create an authorization for a specific app][get-or-create-an-authorization-for-a-specific-app] API (`token` is still returned for "create") +- The [Get-or-create an authorization for a specific app and fingerprint][get-or-create-an-authorization-for-a-specific-app-and-fingerprint] API (`token` is still returned for "create") +- The [Update an existing authorization][update-an-existing-authorization] API + + +If your application uses these APIs, we urge you to update your application as soon as possible. (Read [the December announcement][removing-authorizations-token] for more details on the changes.) + +Starting today, we're offering a migration period allowing applications to opt in to these changes (as described below). On April 20, these changes will become official parts of the GitHub API v3. At that time, these changes will apply to all API consumers. + +### Migration period + +During the migration period, you can opt-in to these changes using the following custom media type in the `Accept` header: + + application/vnd.github.mirage-preview+json + +We want to make these updates as smooth as possible for everyone, and we hope that the migration period gives you flexibility to adopt these changes on your own schedule. If you have any questions or feedback, please [get in touch with us][contact]! + +[removing-authorizations-token-extended-preview]: /changes/2015-02-03-removing-authorizations-token-update/ +[removing-authorizations-token]: /changes/2014-12-08-removing-authorizations-token/ +[list-your-authorizations]: /v3/oauth_authorizations/#list-your-authorizations +[get-a-single-authorization]: /v3/oauth_authorizations/#get-a-single-authorization +[get-or-create-an-authorization-for-a-specific-app]: /v3/oauth_authorizations/#get-or-create-an-authorization-for-a-specific-app +[get-or-create-an-authorization-for-a-specific-app-and-fingerprint]: /v3/oauth_authorizations/#get-or-create-an-authorization-for-a-specific-app-and-fingerprint +[update-an-existing-authorization]: /v3/oauth_authorizations/#update-an-existing-authorization +[contact]: https://github.com/contact?form[subject]=Removing+authorizations+token diff --git a/content/changes/2015-02-24-more-time-to-prepare-for-the-breaking-changes-to-organization-permissions.md b/content/changes/2015-02-24-more-time-to-prepare-for-the-breaking-changes-to-organization-permissions.md new file mode 100644 index 0000000000..0b9370abd7 --- /dev/null +++ b/content/changes/2015-02-24-more-time-to-prepare-for-the-breaking-changes-to-organization-permissions.md @@ -0,0 +1,11 @@ +--- +title: More time to prepare for the breaking changes to organization permissions +author_name: jakeboxer +--- + +After listening to your feedback on the upcoming [breaking changes to organization permissions][org-permissions-preview], we're giving developers more time to update their applications. We'll announce an updated timeline for these changes in the coming weeks. + +In the meantime, if your application relies on any of the affected functionality described in our [previous blog post][org-permissions-preview], please **update your code** to account for these changes. If you have any questions or feedback, please [get in touch with us][contact]! + +[org-permissions-preview]: /changes/2014-12-08-organization-permissions-api-preview/ +[contact]: https://github.com/contact?form[subject]=Organization+Permissions+API diff --git a/content/changes/2015-03-09-licenses-api.md b/content/changes/2015-03-09-licenses-api.md new file mode 100644 index 0000000000..c38277b3b5 --- /dev/null +++ b/content/changes/2015-03-09-licenses-api.md @@ -0,0 +1,24 @@ +--- +title: Licenses API +author_name: benbalter +--- + +We're introducing a new [license API](/v3/licenses) preview to support [open source license usage on GitHub.com](https://github.com/blog/1964-license-usage-on-github-com). + +To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.drax-preview+json + +This will then expose two new API endpoints. You can get a list of all known licenses: + + GET /licenses + +Or get information about a particular license: + + GET /licenses/mit + +When the preview media type is passed, the repository api will also return information about a repository's license file when you get an individual repository: + + GET /repos/github/hubot + +For more information, see the [licenses API documentation](/v3/licenses/), and if you have any questions or feedback, please [let us know](https://github.com/contact?form%5Bsubject%5D=Licenses+API). diff --git a/content/changes/2015-04-17-preview-repository-redirects.md b/content/changes/2015-04-17-preview-repository-redirects.md new file mode 100644 index 0000000000..9f185466b8 --- /dev/null +++ b/content/changes/2015-04-17-preview-repository-redirects.md @@ -0,0 +1,38 @@ +--- +title: Preview repository redirects +author_name: jasonrudolph +--- + +From time to time, repository names change. If you make a GitHub API request using a repository's old name in the URL, the API has historically responded with `404 Not Found`. To help API clients gracefully handle renamed repositories, the API will soon begin [redirecting][redirects] to the repository's new location. + +You can preview these redirects now. In the coming weeks, we'll announce the timeline for enabling these redirects for everyone. + +## How can I try out the redirects? + +Starting today, developers can preview the redirect functionality for relocated repositories. To access this redirect functionality during the preview period, you’ll need to provide the following custom [media type][] in the `Accept` header: + + application/vnd.github.quicksilver-preview+json + +During the preview period, we may change aspects of the redirect behavior based on developer feedback. If we do, we will announce the changes here on the developer blog, but we will not provide any advance notice. + +## When will the redirects occur? + +To understand when these redirects would take place, you'll want to understand how to identify a repository's location. Repositories are located using the combination of the owner's name and the repository's name. For example, the [@twbs][] organization owns the popular [bootstrap repository](https://github.com/twbs/bootstrap). We identify this repository as [twbs/bootstrap](https://github.com/twbs/bootstrap). + +The repository's location changes in the following scenarios: + +- When the owner changes the repository name. +- When the owner renames their user account or organization account. +- When the owner transfers the repository to a new owner. + +Continuing our [twbs/bootstrap](https://github.com/twbs/bootstrap) example, this repository used to be owned by the [@twitter][] organization, and it was therefore located at [twitter/bootstrap](https://github.com/twitter/bootstrap). With repository redirects, you'll be able to make an API request using the repository's old location and receive [either a `301` or `307` HTTP redirect][redirects], depending on the type of request being made. You can then follow the redirect to the new location. + +## Send us your feedback + +We hope you'll take these redirects for a spin and [let us know what you think][contact]. Happy redirecting! + +[@twbs]: https://github.com/twbs +[@twitter]: https://github.com/twitter +[contact]: https://github.com/contact?form%5Bsubject%5D=API+Repository+Redirects +[media type]: /v3/media/ +[redirects]: /v3/#http-redirects diff --git a/content/changes/2015-04-20-authorizations-api-response-changes-are-now-in-effect.md b/content/changes/2015-04-20-authorizations-api-response-changes-are-now-in-effect.md new file mode 100644 index 0000000000..46a41d715e --- /dev/null +++ b/content/changes/2015-04-20-authorizations-api-response-changes-are-now-in-effect.md @@ -0,0 +1,36 @@ +--- +title: Authorizations API response changes are now in effect +author_name: ptoomey3 +--- + +Two months ago, we +[announced the migration period][migration-period-announcement] +for several [API changes related to managing OAuth authorizations][original-announcement]. +As promised, the migration period concluded today, and these changes are +now in effect for all requests. + +### Preview media type no longer needed + +If you used the updated Authorizations API during the migration period, you needed +to provide a custom media type in the `Accept` header: + + application/vnd.github.mirage-preview+json + +Now that the migration period has ended, you no longer need to pass this custom +media type. + +Instead, we [recommend][media-types] that you specify `v3` as the version in the +`Accept` header: + + application/vnd.github.v3+json + +### Feedback + +As always, if you have any feedback, please don't hesitate to +[get in touch with us][contact]. + +[migration-period-announcement]: /changes/2015-02-20-migration-period-removing-authorizations-token +[original-announcement]: /changes/2014-12-08-removing-authorizations-token/ +[docs]: /v3/oauth_authorizations +[media-types]: /v3/media +[contact]: https://github.com/contact?form[subject]=Removing+token+from+Authorizations+API diff --git a/content/changes/2015-04-21-organization-hooks-api-finalized.md b/content/changes/2015-04-21-organization-hooks-api-finalized.md new file mode 100644 index 0000000000..9d0e70aea1 --- /dev/null +++ b/content/changes/2015-04-21-organization-hooks-api-finalized.md @@ -0,0 +1,28 @@ +--- +title: Organization Webhooks API finalized +author_name: pengwynn +--- + +After [four months in preview release][ann], the [Organization Webhooks API][docs] is now considered stable and ready for production use. + +### Preview media type no longer needed + +During the preview period, you needed to provide a custom media type in the `Accept` header when using the Organization Webhooks API: + + application/vnd.github.sersi-preview+json + +Now that the preview has ended, you no longer need to pass this custom +media type, though providing an explicit [media type][media-types] is recommended: + + application/vnd.github.v3+json + +### Feedback + +If you have any questions or feedback on this API, please [get in touch][contact]. + +[ann]: /changes/2014-12-03-preview-the-new-organization-webhooks-api/ +[docs]: /v3/orgs/hooks +[media-types]: /v3/media +[contact]: https://github.com/contact?form%5Bsubject%5D=Organization+Webhooks + + diff --git a/content/changes/2015-05-26-repository-redirects-are-coming.md b/content/changes/2015-05-26-repository-redirects-are-coming.md new file mode 100644 index 0000000000..ff577c0648 --- /dev/null +++ b/content/changes/2015-05-26-repository-redirects-are-coming.md @@ -0,0 +1,20 @@ +--- +title: Repository redirects are coming to API v3 in July +author_name: jasonrudolph +--- + +Last month, we announced the [upcoming repository redirect behavior for the API][original announcement], and we made it available for developers to preview. Starting **July 21, 2015**, the API will automatically provide these redirects for all API consumers. + +To learn more about repository redirects and how they will benefit your applications, be sure to check out the [original announcement][]. + +To start enjoying repository redirects right away, just provide the following custom [media type][] in the `Accept` header: + + application/vnd.github.quicksilver-preview+json + +Thanks to everyone that tried out this enhancement during the preview period. + +As always, if you have any questions, please [get in touch][contact]. We love hearing from you. + +[media type]: /v3/media/ +[original announcement]: /changes/2015-04-17-preview-repository-redirects/ +[contact]: https://github.com/contact?form%5Bsubject%5D=API+Repository+Redirects diff --git a/content/changes/2015-06-10-breaking-changes-to-organization-permissions-coming-on-june-24.md b/content/changes/2015-06-10-breaking-changes-to-organization-permissions-coming-on-june-24.md new file mode 100644 index 0000000000..d56295e02b --- /dev/null +++ b/content/changes/2015-06-10-breaking-changes-to-organization-permissions-coming-on-june-24.md @@ -0,0 +1,37 @@ +--- +title: Breaking changes to organization permissions coming on June 24 +author_name: jakeboxer +--- + +Back in January, we [encouraged developers to update their applications][org-permissions-finalization] to prepare for [upcoming API changes][org-permissions-preview] related to managing organization members and repositories. In order to support the upcoming [improvements to organization permissions][direct-org-membership-blog-post], these changes will become official parts of GitHub API v3 on **June 24**. + +If your application relies on any of the affected functionality (described below), be sure to **update your code before June 24** to account for these changes. + +## Breaking changes coming on June 24 + +If your application uses any of the following APIs, then you are affected by this change: + +- APIs for managing your organization's admins through the Owners team +- The [List your repositories][list-your-repos] API +- The [List your organizations][list-your-organizations] API +- The [List user organizations][list-user-organizations] API + +If your application uses these APIs, we urge you to update your application as soon as possible. (Read [December's announcement][org-permissions-preview] for full details on the changes.) + +In January, we [announced a migration period][org-permissions-finalization] allowing API consumers to opt in to these changes. If you haven't already opted in to these changes, you still do so as described below. On June 24, these changes will become official parts of GitHub API v3. At that time, these changes will apply to all API consumers. + +## Migration period + +During these final days of the migration period, you can opt in to these changes using the following custom media type in the `Accept` header: + + application/vnd.github.moondragon+json + +We want to make these updates as smooth as possible for everyone, and we hope that the migration period gives you flexibility to adopt these changes on your own schedule. If you have any questions or feedback, please [get in touch with us][contact]! + +[org-permissions-finalization]: /changes/2015-01-07-prepare-for-organization-permissions-changes/ +[org-permissions-preview]: /changes/2014-12-08-organization-permissions-api-preview/ +[direct-org-membership-blog-post]: https://github.com/blog/2020-improved-organization-permissions/ +[list-your-repos]: /v3/repos/#list-your-repositories +[list-user-organizations]: /v3/orgs/#list-user-organizations +[list-your-organizations]: /v3/orgs/#list-your-organizations +[contact]: https://github.com/contact?form[subject]=Organization+Permissions+API diff --git a/content/changes/2015-06-11-pages-a-records.md b/content/changes/2015-06-11-pages-a-records.md new file mode 100644 index 0000000000..a18197d3b8 --- /dev/null +++ b/content/changes/2015-06-11-pages-a-records.md @@ -0,0 +1,31 @@ +--- +title: GitHub Pages' A Records Added to Meta API +author_name: leereilly +--- + +The [Meta API](/v3/meta/) now includes the A record IP addresses for [GitHub Pages](https://pages.github.com/). + +``` command-line +$ curl https://api.github.com/meta +``` + +``` json +{ + "verifiable_password_authentication": true, + "github_services_sha": "23c6105183b626cf74c045f6d53af7a178bfdb4c", + "hooks": [ + "192.30.252.0/22" + ], + "git": [ + "192.30.252.0/22" + ], + "pages": [ + "192.30.252.153/32", + "192.30.252.154/32" + ] +} +``` + +These IP addresses are used to [configure A records with your DNS provider for GitHub Pages](https://help.github.com/articles/tips-for-configuring-an-a-record-with-your-dns-provider/). These addresses have changed a few times in the past. This API always provides the current addresses so that you can automate the process of keeping your DNS records up to date. + +If you have any questions, please [get in touch](https://github.com/contact?form%5Bsubject%5D=GitHub+Pages+A+Records+Added+to+API). We’ll be happy to help. diff --git a/content/changes/2015-06-17-organizations-endpoint.md b/content/changes/2015-06-17-organizations-endpoint.md new file mode 100644 index 0000000000..39326640a0 --- /dev/null +++ b/content/changes/2015-06-17-organizations-endpoint.md @@ -0,0 +1,29 @@ +--- +title: List all organizations +author_name: keavy +--- + +We've added a [new API method](/v3/orgs#list-all-organizations) to list all organizations: + +``` command-line +$ curl https://api.github.com/organizations + +> [ +> { +> "login": "github", +> "id": 9919, +> "url": "https://api.github.com/orgs/github", +> "repos_url": "https://api.github.com/orgs/github/repos", +> "events_url": "https://api.github.com/orgs/github/events", +> "members_url": "https://api.github.com/orgs/github/members{/member}", +> "public_members_url": "https://api.github.com/orgs/github/public_members{/member}", +> "avatar_url": "https://avatars.githubusercontent.com/u/9919?v=3", +> "description": "GitHub, the company." +> }, +> ... +> ] +``` + +As always, if you have any questions or feedback, please [drop us a line][contact]. + +[contact]: https://github.com/contact?form[subject]=API+-+Listing+Organizations diff --git a/content/changes/2015-06-24-api-enhancements-for-working-with-organization-permissions.md b/content/changes/2015-06-24-api-enhancements-for-working-with-organization-permissions.md new file mode 100644 index 0000000000..1bd6623359 --- /dev/null +++ b/content/changes/2015-06-24-api-enhancements-for-working-with-organization-permissions.md @@ -0,0 +1,86 @@ +--- +title: API enhancements for working with organization permissions +author_name: jakeboxer +--- + +We're introducing several enhancements to allow API developers to take advantage of the [improved organization permissions][dotcom-blog-post] that we are rolling out. Learn about these enhancements and how you can try them out below. + +Since we're rolling out the [improved organization permissions][dotcom-blog-post] improvements slowly, these enhancements will only apply to certain organizations at first. Most of these enhancements will degrade gracefully (returning an empty array or something similar) if used on an organization that doesn't support improved organization permissions yet. Check the documentation for your specific API to see if errors are possible. + +## API enhancements + +### Team permissions + +In our improved permissions system, a team no longer has a single permission that applies to all of its repositories. Instead, each repository is added to a team with its own permission. For example, an organization could use a single team to grant pull access to one repository, push access to a second, and admin access to a third. + +The team APIs now support this more granular notion of permissions: + +- The [Add team repository][add-team-repo] API accepts a `permission` parameter, so that you can specify whether a team should grant `pull`, `push`, or `admin` access on a given repository. +- In the [List team repositories][list-team-repos] and [Check if a team manages a repository][get-team-repo] API, the response includes a `permissions` attribute, indicating whether the team grants `pull`, `push`, or `admin` access on each repository. +- The `permission` parameter in the [Create team][create-team] and [Edit team][edit-team] APIs is deprecated. Since teams can grant a different permission on each repository, this parameter no longer dictates what permission a team grants on all of its repositories. Instead, it dictates the default permission that the [Add team repository][add-team-repo] API will use for requests where no `permission` parameter is specified. + +### Team privacy + +We now allow you to modify the privacy level of your teams. A "secret" team can only be seen by organization owners and people who are members of that team (which is how all teams have worked historically), while a "closed" team is visible to every member of the organization (which makes it easier to use [@mentions][team-mentions] throughout your organization). + +The team APIs now support this new team privacy concept: + +- The [Create team][create-team] and [Edit team][edit-team] APIs accept a `privacy` parameter, so that you can specify whether a team should be `secret` or `closed`. +- All team resources in the API now include a `privacy` attribute, indicating whether the team is `secret` or `closed`. + +### Team maintainers + +We've added the ability for you to delegate team maintenance to non-owners, reducing the workload for your organization's owners. You can now promote a non-owner member of a team to be a "maintainer" of that team. A maintainer can add and remove team members and change the team's title and description. + +The team membership APIs now support this new team maintainer concept: + +- The [Add team membership][add-team-membership] API accepts a `role` parameter, so that you can specify whether a given team member should be a `maintainer` or a regular `member`. +- The [List team members][list-team-members] API accepts an optional `role` parameter, allowing you to fetch only `maintainer`s or only regular `member`s. +- In the [Get team membership][get-team-membership] and [Add team membership][add-team-membership] APIs, the response includes a `role` attribute, indicating whether a user is a `maintainer` or a regular `member` of the team. + +For more information on our improved team permissions, check out our [documentation][understanding-team-permissions]. + +### Filtering organization members by role + +The organization [Members list][org-members-list] API now accepts a `role` parameter, so that you can request to see only the owners (or non-owners) of your organization. + +### Repository collaborators + +We now allow you to add collaborators directly to organization-owned repositories, just like we always have for user-owned repositories. + +The collaborator APIs now support organization-owned repositories: + +- The [Add user as a collaborator][add-collab] API works for organization-owned repositories. We've also added a `permission` parameter to it (currently valid for organization-owned repositories only), so that you can specify what level of access the collaborator should have on the repository. +- In the [List collaborators][list-collabs] API, the response includes a `permissions` attribute describing the permissions that each collaborator has on your organization's repositories. + +## Preview period + +Starting today, these API enhancements are available for developers to preview. At the end of the preview period, these enhancements will become official components of the GitHub API. + +While these enhancements are in their preview period, you'll need to provide the following [custom media type][custom-media-types] in the `Accept` header: + + application/vnd.github.ironman-preview+json + +During the preview period, we may change aspects of these enhancements. If we do, we will announce the changes on the developer blog, but we will not provide any advance notice. + +## Send us your feedback + +We would love to hear your thoughts on these enhancements. If you have any questions or feedback, please [get in touch with us][contact]! + +[dotcom-blog-post]: https://github.com/blog/2020-improved-organization-permissions +[understanding-team-permissions]: https://help.github.com/articles/improved-organization-permissions/#understanding-team-permissions +[create-team]: /v3/orgs/teams/#create-team +[edit-team]: /v3/orgs/teams/#edit-team +[list-team-members]: /v3/orgs/teams/#list-team-members +[get-team-membership]: /v3/orgs/teams/#get-team-membership +[add-team-membership]: /v3/orgs/teams/#add-team-membership +[list-team-repos]: /v3/orgs/teams/#list-team-repos +[get-team-repo]: /v3/orgs/teams/#check-if-a-team-manages-a-repository +[add-team-repo]: /v3/orgs/teams/#add-or-update-team-repository +[org-members-list]: /v3/orgs/members/#members-list +[org-public-members-list]: /v3/orgs/members/#public-members-list +[list-collabs]: /v3/repos/collaborators/#list-collaborators +[add-collab]: /v3/repos/collaborators/#add-user-as-a-collaborator +[contact]: https://github.com/contact?form[subject]=Organization+Permissions+API +[team-mentions]: https://github.com/blog/1121-introducing-team-mentions +[custom-media-types]: /v3/media/ diff --git a/content/changes/2015-06-24-breaking-changes-to-organization-permissions-are-now-official.md b/content/changes/2015-06-24-breaking-changes-to-organization-permissions-are-now-official.md new file mode 100644 index 0000000000..fdecc9b91d --- /dev/null +++ b/content/changes/2015-06-24-breaking-changes-to-organization-permissions-are-now-official.md @@ -0,0 +1,16 @@ +--- +title: Breaking changes to organization permissions are now official +author_name: jakeboxer +--- + +As [promised earlier this month][notice], the [API changes][api-changes] related to managing organization members and repositories are now official parts of the GitHub API. + +During the migration period, you needed to [provide a custom media type in the `Accept` header][migration-period] to opt-in to the changes. Now that the migration period has ended, you no longer need to specify this custom [media type][media-types]. + +If you have any questions or feedback, please [get in touch with us][contact]! + +[notice]: /changes/2015-06-10-breaking-changes-to-organization-permissions-coming-on-june-24 +[api-changes]: /changes/2014-12-08-organization-permissions-api-preview/ +[contact]: https://github.com/contact?form[subject]=Organization+Permissions+API +[media-types]: /v3/media +[migration-period]: /changes/2015-06-10-breaking-changes-to-organization-permissions-coming-on-june-24/#migration-period diff --git a/content/changes/2015-06-24-licenses-api-update.md b/content/changes/2015-06-24-licenses-api-update.md new file mode 100644 index 0000000000..26f5b340d3 --- /dev/null +++ b/content/changes/2015-06-24-licenses-api-update.md @@ -0,0 +1,20 @@ +--- +title: Licenses API update +author_name: mislav +--- + +We are expanding the [Licenses API](/v3/licenses) to make it more useful for auditing license usage across all repositories owned by a user or organization. + +Before, license information was only returned for an individual repository: + + GET /repos/github/hubot + +Now, license information will also be included in responses from endpoints that list multiple repositories, such as [List organization repositories](/v3/repos/#list-organization-repositories): + + GET /orgs/github/repos + +As before, to access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.drax-preview+json + +For more information, see the [Licenses API documentation](/v3/licenses/), and if you have any questions or feedback, please [let us know](https://github.com/contact?form%5Bsubject%5D=Licenses+API). diff --git a/content/changes/2015-07-21-automatic-redirects-for-renamed-repositories.md b/content/changes/2015-07-21-automatic-redirects-for-renamed-repositories.md new file mode 100644 index 0000000000..4477688d15 --- /dev/null +++ b/content/changes/2015-07-21-automatic-redirects-for-renamed-repositories.md @@ -0,0 +1,15 @@ +--- +title: Automatic redirects for renamed repositories +author_name: jasonrudolph +--- + +To help API clients gracefully handle renamed repositories, the API now [automatically redirects to the repository’s new location][original-announcement]. + +Our thanks goes out to everyone that tried out this enhancement [during the preview period][original-announcement]. During the preview period, you needed to [provide a custom media type in the `Accept` header][preview-media-type] to opt-in to the redirects. Now that the preview period has ended, you no longer need to specify this custom [media type][]. + +To learn more about these redirects and how they benefit your applications, be sure to check out the [preview period announcement][original-announcement]. As always, if you have any questions, we're [here to help][contact]. + +[contact]: https://github.com/contact?form%5Bsubject%5D=API+Repository+Redirects +[media type]: /v3/media/ +[original-announcement]: /changes/2015-04-17-preview-repository-redirects/ +[preview-media-type]: /changes/2015-04-17-preview-repository-redirects/#how-can-i-try-out-the-redirects diff --git a/content/changes/2015-07-22-more-flexible-options-for-listing-repositories.md b/content/changes/2015-07-22-more-flexible-options-for-listing-repositories.md new file mode 100644 index 0000000000..26a762e414 --- /dev/null +++ b/content/changes/2015-07-22-more-flexible-options-for-listing-repositories.md @@ -0,0 +1,16 @@ +--- +title: More flexible options for listing repositories +author_name: jakeboxer +--- + +The [List your repositories][list-your-repos] API now offers additional parameters to help you fetch the exact set of repositories you're looking for: + +- The `visibility` parameter lets you request only your public repositories, only your private repositories, or both. +- With the `affiliation` parameter, you can ask for repositories you own, repositories where you are a collaborator, repositories you have access to as an organization member, or any combination that suits your needs. + +Use these new parameters separately, together, or in combination with other parameters to craft flexible queries that fetch the specific repositories you're seeking. + +For full details, check out the [documentation][list-your-repos]. If you have any questions, please [get in touch][contact]! + +[list-your-repos]: /v3/repos/#list-your-repositories +[contact]: https://github.com/contact?form[subject]=List+your+repositories+API diff --git a/content/changes/2015-08-04-get-license-contents.md b/content/changes/2015-08-04-get-license-contents.md new file mode 100644 index 0000000000..676bfbc447 --- /dev/null +++ b/content/changes/2015-08-04-get-license-contents.md @@ -0,0 +1,24 @@ +--- +title: Get the contents of a repository’s license +author_name: benbalter +--- + +The [License API Preview](/v3/licenses/) now allows you to retrieve the contents of a repository's open source license. As before, when the appropriate preview media type is passed, the repository endpoint will return information about the detected license, if any: + +``` command-line +curl -H "Accept: application/vnd.github.drax-preview+json" https://api.github.com/repos/benbalter/gman +``` + +You can now also get the contents of the repository's license file, whether or not the license was successfully identified via the license contents endpoint: + +``` command-line +curl -H "Accept: application/vnd.github.drax-preview+json" https://api.github.com/repos/benbalter/gman/license +``` + +Similar to [the repository contents API](/v3/repos/contents/#get-contents), the license contents method also supports [custom media types](/v3/repos/contents/#custom-media-types) for retrieving the raw license content or rendered license HTML. + +``` command-line +curl -H "Accept: application/vnd.github.drax-preview.raw" https://api.github.com/repos/benbalter/gman/license +``` + +For more information, see [the license API documentation](/v3/licenses/#get-the-contents-of-a-repositorys-license), and as always, if you have any questions or feedback, please [get in touch with us](https://github.com/contact?form%5Bsubject%5D=License+API). diff --git a/content/changes/2015-09-03-ensure-your-app-is-ready-for-protected-branches.md b/content/changes/2015-09-03-ensure-your-app-is-ready-for-protected-branches.md new file mode 100644 index 0000000000..e32d9ef35f --- /dev/null +++ b/content/changes/2015-09-03-ensure-your-app-is-ready-for-protected-branches.md @@ -0,0 +1,55 @@ +--- +title: Ensure your app is ready for Protected Branches +author_name: aroben +--- + +We’ve begun to [roll out Protected Branches][blog] across GitHub. When you +protect a branch in one of your repositories, you will be prevented from +force pushing to that branch or deleting it. You can also configure required +status checks for your protected branch. When configured, changing a branch to +point at a new commit will fail unless that commit (or another commit with +the same [Git tree][tree]) has a [Status][statuses] in the `success` state for +each required status check. + +These restrictions apply to branch manipulations performed via the GitHub API +as well. So when you protect a branch, you will no longer be able to [delete +the branch][delete] via the API or [update it][update] to point at a +non-ancestor commit, even with `"force": true`. And if your branch has required +status checks, you won’t be able to [update it][update] or [merge pull +requests][merge] into that branch until `success` Statuses have been posted to +the target commit for all required status checks. + +These restrictions are all represented by 422 errors: + +``` command-line +$ curl -i -H 'Authorization: token TOKEN' \ +$ -X DELETE https://api.github.com/repos/octocat/hubot/git/refs/heads/master + +> HTTP/1.1 422 Unprocessable Entity +> { +> "message": "Cannot delete a protected branch", +> "documentation_url": "https://help.github.com/articles/about-protected-branches" +> } +``` + +Protected branches and required status checks are a great way to ensure your +project’s conventions are followed. For example, you could write a Status +integration that only posts a `success` Status when the pull request’s author +has signed your project’s Contributor License Agreement. Or you could write one +that only posts a `success` Status when three or more members of your +`@initech/senior-engineers` team have left a comment saying they’ve reviewed +the changes. If you configure these integrations as required status checks, you +can be sure that these conditions have been satisfied before a pull request is +merged. See our [Status API guide][guide] to learn how to create integrations +like these. + +If you have any questions, please [let us know][contact]. + +[blog]: https://github.com/blog/2051-protected-branches-and-required-status-checks +[statuses]: /v3/repos/statuses/ +[tree]: http://git-scm.com/book/en/v2/Git-Internals-Git-Objects#Tree-Objects +[delete]: /v3/git/refs/#delete-a-reference +[update]: /v3/git/refs/#update-a-reference +[merge]: /v3/pulls/#merge-a-pull-request-merge-button +[contact]: https://github.com/contact?form[subject]=Protected+Branches+in+API+responses +[guide]: /guides/building-a-ci-server/ diff --git a/content/changes/2015-11-11-protected-branches-api.md b/content/changes/2015-11-11-protected-branches-api.md new file mode 100644 index 0000000000..6b09f0ac9b --- /dev/null +++ b/content/changes/2015-11-11-protected-branches-api.md @@ -0,0 +1,40 @@ +--- +title: Protected Branches API Preview Period +author_name: nakajima +--- + +**UPDATE (2016-06-27):** As [announced](/changes/2016-06-27-protected-branches-api-update/), there is an extended version of the protected branches API available. This older version will be removed once the new one becomes official. + +We're starting a preview period for the [protected branches](https://github.com/blog/2051-protected-branches-and-required-status-checks) API. Protecting a branch prevents force-pushes to it as well as deleting it. You can also specify required status checks that are required to merge code into the branch. + +To protect a branch, make a `PATCH` request to the URL of the branch: + +``` command-line +curl "https://api.github.com/repos/github/hubot/branches/master" \ + -XPATCH \ + -H 'Authorization: token TOKEN' \ + -H "Accept: application/vnd.github.loki-preview" \ + -d '{ + "protection": { + "enabled": true, + "required_status_checks": { + "enforcement_level": "everyone", + "contexts": [ + "required-status" + ] + } + } + }' +``` + +#### How can I try it? + +To access this functionality during the preview period, you’ll need to provide the following custom media type in the Accept header: + +``` +application/vnd.github.loki-preview+json +``` + +Take a look at [the docs here](/v3/repos/branches/). + +If you have any questions, please [get in touch](https://github.com/contact?form%5Bsubject%5D=Protected+Branches+API+Preview). diff --git a/content/changes/2016-01-05-api-enhancements-for-working-with-organization-permissions-are-now-official.md b/content/changes/2016-01-05-api-enhancements-for-working-with-organization-permissions-are-now-official.md new file mode 100644 index 0000000000..84fb64bbb2 --- /dev/null +++ b/content/changes/2016-01-05-api-enhancements-for-working-with-organization-permissions-are-now-official.md @@ -0,0 +1,16 @@ +--- +title: API enhancements for working with organization permissions are now official +author_name: jakeboxer +--- + +To allow API developers to take advantage of the [improved organization permissions][dotcom-blog-post] that launched in September 2015, we're making the [API enhancements][api-enhancements-blog-post] for working with organization permissions a part of the official GitHub API. + +During the preview period, you needed to [provide a custom media type in the `Accept` header][preview-period] to opt-in to the changes. Now that the preview period has ended, you no longer need to specify this custom [media type][custom-media-types]. + +If you have any questions or feedback, please [get in touch with us][contact]! + +[dotcom-blog-post]: https://github.com/blog/2064-new-organization-permissions-now-available +[api-enhancements-blog-post]: /changes/2015-06-24-api-enhancements-for-working-with-organization-permissions/ +[preview-period]: /changes/2015-06-24-api-enhancements-for-working-with-organization-permissions/#preview-period +[custom-media-types]: /v3/media/ +[contact]: https://github.com/contact?form[subject]=Organization+Permissions+API diff --git a/content/changes/2016-02-11-issue-locking-api.md b/content/changes/2016-02-11-issue-locking-api.md new file mode 100644 index 0000000000..07177d4910 --- /dev/null +++ b/content/changes/2016-02-11-issue-locking-api.md @@ -0,0 +1,43 @@ +--- +title: Issue Locking and Unlocking API Preview Period +author_name: davidcelis +--- + +We're introducing new API methods to allow repository collaborators to [lock and unlock conversations][lock-an-issue]. Developers with [collaborator permissions][permissions] on a repository can start experimenting with these new endpoints today during the preview period. + +To lock a conversation, make a `PUT` request to the conversation's issue: + +``` command-line +$ curl "https://api.github.com/repos/github/hubot/issues/1/lock" \ + -X PUT \ + -H "Authorization: token $TOKEN" \ + -H "Content-Length: 0" \ + -H "Accept: application/vnd.github.the-key-preview" +``` + +To unlock a conversation, make a similarly constructed `DELETE` request: + +``` command-line +$ curl "https://api.github.com/repos/github/hubot/issues/1/lock" \ + -X DELETE \ + -H "Authorization: token $TOKEN" \ + -H "Accept: application/vnd.github.the-key-preview" +``` + +#### How can I try it? + +Starting today, developers can preview these new API methods. To use them during the preview period, you’ll need to provide the following custom [media type][media-types] in the `Accept` header: + +``` +application/vnd.github.the-key-preview+json +``` + +During the preview period, we may change aspects of these API methods based on developer feedback. If we do, we will announce the changes here on the developer blog, but we will not provide any advance notice. + +Take a look at [the documentation][docs] and, if you have any questions, please [get in touch][contact]. + +[contact]: https://github.com/contact?form%5Bsubject%5D=Issue+Locking+and+Unlocking+API+Preview +[docs]: /v3/issues/#lock-an-issue +[lock-an-issue]: https://help.github.com/articles/locking-conversations/ +[media-types]: /v3/media/ +[permissions]: https://help.github.com/articles/what-are-the-different-access-permissions/ diff --git a/content/changes/2016-02-19-source-import-preview-api.md b/content/changes/2016-02-19-source-import-preview-api.md new file mode 100644 index 0000000000..1caf3c446e --- /dev/null +++ b/content/changes/2016-02-19-source-import-preview-api.md @@ -0,0 +1,18 @@ +--- +title: Preview the Source Import API +author_name: spraints +--- + +We've added an API for source imports, which will let you start an import from a Git, Subversion, Mercurial, or Team Foundation Server source repository. This is the same functionality as [the GitHub Importer](https://help.github.com/articles/importing-from-other-version-control-systems-to-github/). + +To access [the Source Import API][docs] during the preview period, you must provide a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.barred-rock-preview + +During the preview period, we may change aspects of these API methods based on developer feedback. If we do, we will announce the changes here on the developer blog, but we will not provide any advance notice. + +If you have any questions or feedback, please [let us know][contact]! + +[media-type]: /v3/media +[docs]: /v3/migration/source_imports/ +[contact]: https://github.com/contact?form%5Bsubject%5D=Source+Import+API diff --git a/content/changes/2016-02-24-commit-reference-sha-api.md b/content/changes/2016-02-24-commit-reference-sha-api.md new file mode 100644 index 0000000000..e78af07bab --- /dev/null +++ b/content/changes/2016-02-24-commit-reference-sha-api.md @@ -0,0 +1,41 @@ +--- +title: Commit Reference SHA-1 Preview Period +author_name: mikemcquaid +--- + +We're introducing a new API media type to allow users to get the SHA-1 of a commit reference. This can be useful in working out if you have the latest version of a remote branch based on your local branch's SHA-1. Developers with read access to a repository can start experimenting with this new media type today during the preview period. + +To get the commit reference's SHA-1, make a `GET` request to the repository's reference: + +``` command-line +$ curl "https://api.github.com/repos/Homebrew/homebrew/commits/master" \ + -H "Accept: application/vnd.github.chitauri-preview+sha" +``` + +To check if a remote branch's SHA-1 is the same as your local branch's SHA-1, make a `GET` request to the repository's branch and provide the current SHA-1 for the local branch as the ETag: + +``` command-line +$ curl "https://api.github.com/repos/Homebrew/homebrew/commits/master" \ + -H "Accept: application/vnd.github.chitauri-preview+sha" \ + -H "If-None-Match: \"814412cfbd631109df337e16c807207e78c0d24e\"" +``` + +If the remote and your local branch point to the same SHA-1 then this call will return a `304 Unmodified` status code (and not use your rate limit). + +You can see an example of this API in a pull request to Homebrew/homebrew's updater: https://github.com/Homebrew/homebrew/pull/49219. + +#### How can I try it? + +To use this new API media type during the preview period, you’ll need to provide the following custom [media type][media-types] in the `Accept` header: + +``` +application/vnd.github.chitauri-preview+sha +``` + +During the preview period, we may change aspects of this API media type based on developer feedback. If we do, we will announce the changes here on the developer blog, but we will not provide any advance notice. + +Take a look at [the documentation][docs] and, if you have any questions, please [get in touch][contact]. + +[contact]: https://github.com/contact?form%5Bsubject%5D=Commit+Reference+SHA-1+Preview +[docs]: /v3/repos/commits/#get-the-sha-1-of-a-commit-reference +[media-types]: /v3/media/ diff --git a/content/changes/2016-03-15-new-webhook-actions.md b/content/changes/2016-03-15-new-webhook-actions.md new file mode 100644 index 0000000000..82e916d655 --- /dev/null +++ b/content/changes/2016-03-15-new-webhook-actions.md @@ -0,0 +1,53 @@ +--- +title: New webhook event actions are coming +author_name: davidcelis +--- + +We will soon begin introducing new `action` values for several existing webhook events. If you currently subscribe to webhooks but do not check the payload's `action` value, you may end up incorrectly processing events after this change is released. To ensure that your webhook processing is not affected by these new `action` values, **you should audit your webhook processing logic by April 15th, 2016**. + +We are providing an advance notice to warn of these changes. In the future, we may continue adding new actions without providing further warning. + +### A brief overview of GitHub webhook actions + +Webhook events can have multiple actions. For example, the [`IssuesEvent`](https://developer.github.com/v3/activity/events/types/#issuesevent) has several possible actions. These include `opened` when the issue is created, `closed` when the issue is closed, and `assigned` when the issue is assigned to someone. Historically, we haven't added new actions to webhook events that have only one action. However, as GitHub's feature set grows, we may occasionally add new actions to existing event types. We encourage you to take some time and ensure that your application explicitly checks the action before doing any processing. + +### What to avoid when working with event actions + +Here's an example of functionality that **will not work** when attempting to process an `IssuesEvent`. In this example, the `process_closed` method will be called for any event action which is not `opened` or `assigned`. This means that the `process_closed` method will be called for events with the `closed` action, but also other events with actions other than `opened` or `assigned` that are delivered to the webhook. + +```ruby +# The following is not future-proof! +case action +when "opened" + process_opened +when "assigned" + process_assigned +else + process_closed +end +``` + +### How to work with new event actions + +We suggest that you explicitly check event actions and act accordingly. In this example, the `closed` action is checked first before calling the `process_closed` method. Additionally, for unknown actions, we log that something new was encountered: + +```ruby +# The following is recommended +case action +when "opened" + process_opened +when "assigned" + process_assigned +when "closed" + process_closed +else + puts "Ooohh, something new from GitHub!" +end +``` + +We may also add new webhook event types from time to time. If your webhook is configured to "Send me **everything**", your code should also explicitly check for the event type in a similar way as we have done with checking for the action type above. Take a look at our [integrators best practices guide][best-practices] for more tips. + +If you have any questions or feedback, please [get in touch][get-in-touch]. + +[best-practices]: https://developer.github.com/guides/best-practices-for-integrators/ +[get-in-touch]: https://github.com/contact?form[subject]=New+Webhook+Actions diff --git a/content/changes/2016-03-17-the-451-status-code-is-now-supported.md b/content/changes/2016-03-17-the-451-status-code-is-now-supported.md new file mode 100644 index 0000000000..d9c1d1a451 --- /dev/null +++ b/content/changes/2016-03-17-the-451-status-code-is-now-supported.md @@ -0,0 +1,26 @@ +--- +title: The 451 status code is now supported +author_name: gjtorikian +--- + +In December 2015, [the IETF ratified status code `451`](https://datatracker.ietf.org/doc/rfc7725/). A `451` response indicates that a resource is unavailable due to an external legal request. + +The GitHub API will now respond with a `451` status code for resources it has been asked to take down due to a DMCA notice. For example: + +``` command-line +$ curl https://api.github.com/repos/github/a-repository-that-s-been-taken-down +> HTTP/1.1 451 +> Server: GitHub.com + +> { +> "message": "Repository access blocked", +> "block": { +> "reason": "dmca", +> "created_at": "2016-03-17T15:39:46-07:00" +> } +> } +``` + +This `451` code will be returned for repositories and gists. Previously, the API responded with a `403 - Forbidden`. Aside from the semantic difference, we feel that it's important for users to know precisely why their data cannot be served. + +If you're receiving a `451` due to a DMCA takedown, please read our article on [submitting a DMCA counter notice](https://help.github.com/articles/guide-to-submitting-a-dmca-counter-notice/) and know your rights. For more information, see [GitHub's DMCA Takedown Policy](https://help.github.com/articles/dmca-takedown-policy/). diff --git a/content/changes/2016-04-01-squash-api-preview.md b/content/changes/2016-04-01-squash-api-preview.md new file mode 100644 index 0000000000..9d43ccac5e --- /dev/null +++ b/content/changes/2016-04-01-squash-api-preview.md @@ -0,0 +1,29 @@ +--- +title: Preview Squash Support for the Pull Request Merge API +author_name: scottjg +--- + +With the [recent addition](https://github.com/blog/2141-squash-your-commits) of squashing Pull Requests via the merge button, we're adding support to squash Pull Requests in the API as well. You can squash a pull request in the [Pull Request Merge API][docs] during the preview period by providing a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.polaris-preview + +For example: + +``` command-line +curl "https://api.github.com/repos/github/hubot/pulls/123/merge" \ + -XPUT \ + -H 'Authorization: token TOKEN' \ + -H "Accept: application/vnd.github.polaris-preview" \ + -d '{ + "squash": true, + "commit_title": "Never tell me the odds" + }' +``` + +During the preview period, we may change aspects of these API methods based on developer feedback. We will announce the changes here on the developer blog, but we will not provide advance notice. + +If you have any questions or feedback, please [let us know][contact]. + +[media-type]: /v3/media +[docs]: /v3/pulls/#merge-a-pull-request-merge-button +[contact]: https://github.com/contact?form%5Bsubject%5D=Squash+API+Preview diff --git a/content/changes/2016-04-04-git-signing-api-preview.md b/content/changes/2016-04-04-git-signing-api-preview.md new file mode 100644 index 0000000000..cd8a9364ea --- /dev/null +++ b/content/changes/2016-04-04-git-signing-api-preview.md @@ -0,0 +1,29 @@ +--- +title: Preview support for Git signing +author_name: mastahyeti +--- + +GitHub [recently started verifying GPG signed commits and tags](https://github.com/blog/2144-gpg-signature-verification). We are adding API support for signature verification and user GPG key management as well. You can enable these changes during the preview period by providing a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.cryptographer-preview + +For example: + +``` command-line +curl "https://api.github.com/user/gpg_keys" \ + -H 'Authorization: token TOKEN' \ + -H "Accept: application/vnd.github.cryptographer-preview" \ +``` + +You can learn more about the new signature verification response objects in the updated [repository commit][repo-commit-doc], [Git commit][git-commit-doc], and [Git tag][git-tag-doc] documentation. There is also new [GPG key management][gpg-keys-doc] documentation. + +During the preview period, we may change aspects of these APIs based on developer feedback. We will announce the changes here on the developer blog, but we will not provide advance notice. + +If you have any questions or feedback, please [let us know][contact]. + +[media-type]: /v3/media +[repo-commit-doc]: /v3/repos/commits +[git-commit-doc]: /v3/git/commits +[git-tag-doc]: /v3/git/tags +[gpg-keys-doc]: /v3/users/gpg_keys +[contact]: https://github.com/contact?form%5Bsubject%5D=Squash+API+Preview diff --git a/content/changes/2016-04-06-deployment-and-deployment-status-enhancements.md b/content/changes/2016-04-06-deployment-and-deployment-status-enhancements.md new file mode 100644 index 0000000000..c13aa14ccb --- /dev/null +++ b/content/changes/2016-04-06-deployment-and-deployment-status-enhancements.md @@ -0,0 +1,49 @@ +--- +title: Deployment and DeploymentStatus API enhancements preview period +author_name: tarebyte +--- + +We've expanded our Deployments APIs to accommodate more powerful deployment practices and to lay the foundation for a more seamless integration of deployments within GitHub. + +## Link to a live deployment + +To enable easy access to a live version of a deployment, we've added an `environment_url` field to the Deployments API. This environment will be exposed as a link in the Pull Request timeline to enable users to directly access a running version of their code without leaving the context of their work. + +*Note: To add some clarity, we've renamed the `target_url` field to `log_url`. We will continue accept `target_url` to support legacy uses, but we recommend modifying this to the new name to avoid confusion. Future API versions might not support `target_url`*. + +## Inactive deployment status + +We recognize that deployments in many common practices don't last forever. So, we've added a new `inactive` state to Deployment Statuses. You can use this state to communicate that a deployment is no longer active (e.g. something different has been deployed to the environment or the environment has been destroyed). + +## More information about environments + +We've expanded our Deployments API to provide additional information about the environments associated with deployments. + +We've added a new `transient_environment` field to allow you to communicate that an environment is specific to a deployment and will no longer exist at some point in the future (e.g. a temporary testing environment like a [Heroku Review App][heroku-review-app]). By pairing this with other additions, we can determine that an `inactive` deployment associated with a `transient_environment` has an `environment_url` that is no longer accessible. + +Similarly, we've added a new `production_environment` field to allow you to communicate that an environment is one with which end users directly interact. We automatically set `production_environment` to `true` if the value for `environment` is ``"production"``. + +## Automatic creation of inactive statuses + +Each time we receive a new successful deployment status, we automatically add a new `inactive` status to all previous deployments made within the relevant repository to the same environment (based on the value of `environment`) given the environment is both non-transient and non-production. You can opt out of this behavior by passing `false` with the new `auto_inactive` parameter. + +For example, if `feature-branch` within `https://github.com/user/repository` is deployed to an environment named `staging` (which is a non-transient, non-production environment) and `bugfix-branch` within `https://github.com/user/repository` is later deployed to an environment named `staging`, we would automatically create a new `inactive` status for the deployment associated with `feature-branch`. + +#### How can I try it? + +Starting today, these API enhancements are available for developers to preview. At the end of the preview period, these enhancements will become official components of the GitHub API. + +To access the API during the preview period, you must provide a custom [media type][media-types] in the Accept header: + +``` +application/vnd.github.ant-man-preview+json +``` + +During the preview period, we may change aspects of these enhancements. If we do, we will announce the changes on the developer blog, but we will not provide any advance notice. + +Take a look at [the documentation][docs] for full details. We would love to hear your thoughts on these enhancements. If you have any questions or feedback, please [get in touch with us][contact]! + +[contact]: https://github.com/contact?form%5Bsubject%5D=Deployment+and+DeploymentStatus+API+enhancements+preview+period +[media-types]: /v3/media/ +[heroku-review-app]: https://devcenter.heroku.com/articles/github-integration-review-apps +[docs]:https://developer.github.com/v3/repos/deployments/ diff --git a/content/changes/2016-04-12-commit-reference-sha-api-is-now-official.md b/content/changes/2016-04-12-commit-reference-sha-api-is-now-official.md new file mode 100644 index 0000000000..adbec89580 --- /dev/null +++ b/content/changes/2016-04-12-commit-reference-sha-api-is-now-official.md @@ -0,0 +1,14 @@ +--- +title: Commit Reference SHA-1 API is now official +author_name: mikemcquaid +--- + +We're making the [Commit Reference SHA-1 API][api-enhancements-blog-post] part of the official GitHub API. + +During the preview period you needed to provide the `application/vnd.github.chitauri-preview+sha` preview media type in the `Accept` header to opt-in to the changes. Now that the preview period has ended the custom [media type][custom-media-types] has changed to `application/vnd.github.v3.sha` (but the preview type will continue to work). + +If you have any questions or feedback, please [get in touch with us][contact]! + +[api-enhancements-blog-post]: /changes/2016-02-24-commit-reference-sha-api/ +[custom-media-types]: /v3/media/ +[contact]: https://github.com/contact?form[subject]=Commit+Reference+SHA-1+API diff --git a/content/changes/2016-04-18-new-webhook-actions-are-live.md b/content/changes/2016-04-18-new-webhook-actions-are-live.md new file mode 100644 index 0000000000..40c28b16ce --- /dev/null +++ b/content/changes/2016-04-18-new-webhook-actions-are-live.md @@ -0,0 +1,65 @@ +--- +title: New webhook event actions are now live +author_name: davidcelis +--- + +As [promised last month][notice], we've expanded several webhook events with new functionality. Webhook events involving repositories, issues, and comments have all been updated to include new actions. + +Repository events will now fire when a repository is deleted, made public, or made private. In addition, while repository creation events will still only fire for organizations, the new repository event actions can be delivered for user-owned repositories. + +Events for issues, pull requests, and comments have also been updated and will now fire when these objects are edited or deleted. When an issue, pull request, or a comment has been edited, the event's payload will include a "changes" object. For example, if you've updated the title and body of an issue, the webhook payload informs you of what the issue used to look like: + +```json +{ + "action": "edited", + "changes": { + "title": { "from": "This is the old title." }, + "body": { "from": "This is the old body." } + }, + "issue": { + "title": "This is the new title.", + "body": "This is the new body." + } +} +``` + +The new values will be present in the `issue` object itself, as detailed above. Unchanged values will not be present within the `changes` object. Comment edits follow a similar pattern, though because they have no titles, the only change included in the payload would be the comment's body. + +## List of comprehensive changes + +New actions were added to five events, all of which are detailed below. + +### [RepositoryEvent][repository-event] + +* `deleted`: sent when a user-owned or organization-owned repository is deleted. +* `publicized`: sent when a user-owned or organization-owned repository is switched from private to public. +* `privatized`: sent when a user-owned or organization-owned repository is switched from public to private. + +### [IssuesEvent][issues-event] + +* `edited`: sent when the title and/or body of an issue is edited. + +### [IssueCommentEvent][issue-comment-event] + +* `edited`: sent when a comment on an issue or pull request is edited +* `deleted`: sent when a comment on an issue or pull request is deleted + +### [PullRequestEvent][pull-request-event] + +* `edited`: sent when the title and/or body of a pull request is edited. + +### [PullRequestReviewCommentEvent][pull-request-review-comment-event] + +* `edited`: sent when a comment on a pull request's unified diff (in the Files Changed tab) is edited +* `deleted`: sent when a comment on a pull request's unified diff (in the Files Changed tab) is deleted + +Take a look at [the documentation][docs] for full details. If you have any questions or feedback, please [get in touch][get-in-touch]. + +[docs]: https://developer.github.com/webhooks/ +[get-in-touch]: https://github.com/contact?form[subject]=New+Webhook+Actions +[issue-comment-event]: https://developer.github.com/v3/activity/events/types/#issuecommentevent +[issues-event]: https://developer.github.com/v3/activity/events/types/#issuesevent +[notice]: https://developer.github.com/changes/2016-03-15-new-webhook-actions/ +[pull-request-event]: https://developer.github.com/v3/activity/events/types/#pullrequestevent +[pull-request-review-comment-event]: https://developer.github.com/v3/activity/events/types/#pullrequestreviewcommentevent +[repository-event]: https://developer.github.com/v3/activity/events/types/#repositoryevent diff --git a/content/changes/2016-04-21-oauth-authorizations-grants-api-preview.md b/content/changes/2016-04-21-oauth-authorizations-grants-api-preview.md new file mode 100644 index 0000000000..7e60f4baec --- /dev/null +++ b/content/changes/2016-04-21-oauth-authorizations-grants-api-preview.md @@ -0,0 +1,29 @@ +--- +title: Preview support for OAuth authorizations grants API +author_name: ptoomey3 +--- + +GitHub recently made changes to [the application authorizations settings screen within GitHub][authorized-application-listing] to display one entry for each OAuth application a user has authorized. Previously this screen showed one entry for each OAuth token that was generated by an OAuth application. For example, if you installed two instances of GitHub Desktop, you would see one entry for each installation. To simplify OAuth application management, we now show a single entry for each OAuth application. For OAuth applications that use the [web flow][web-flow] this was not a problem, since the web flow never generates more than one token for a given OAuth application and user. However, going forward, GitHub would like to allow all OAuth applications, including those that use the web flow, to generate more than one token. + +In preparation for that change, we are adding API support to simplify management of OAuth applications that matches what is available on GitHub.com. You can enable these changes during the preview period by providing a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.damage-preview + +For example: + +``` command-line +curl -u username "https://api.github.com/applications/grants" \ + -H "Accept: application/vnd.github.damage-preview" +``` + +You can learn more about the new APIs in the [OAuth authorizations][oauth-authorizations-api] documentation. + +During the preview period, we may change aspects of these APIs based on developer feedback. We will announce the changes here on the developer blog, but we will not provide advance notice. + +If you have any questions or feedback, please [let us know][contact]. + +[media-type]: /v3/media +[oauth-authorizations-api]: /v3/oauth_authorizations +[authorized-application-listing]: https://github.com/settings/applications#authorized +[contact]: https://github.com/contact?form%5Bsubject%5D=OAuth+Authorizations+Grants+API+Preview +[web-flow]: /v3/oauth/#web-application-flow diff --git a/content/changes/2016-05-03-source-import-api-enhancements-for-working-with-git-lfs.md b/content/changes/2016-05-03-source-import-api-enhancements-for-working-with-git-lfs.md new file mode 100644 index 0000000000..4f7f8bb308 --- /dev/null +++ b/content/changes/2016-05-03-source-import-api-enhancements-for-working-with-git-lfs.md @@ -0,0 +1,40 @@ +--- +title: Source Import API enhancements for working with Git LFS +author_name: lizzhale +--- + +Today we're introducing enhancements to the [Source Import API][docs] to support importing repositories with files larger than 100MB. + +**Changes to parameters for starting an import** + +[Starting an import][start-an-import] no longer requires a `vcs` parameter. Please be aware that without this parameter, the import job will take additional time to detect the vcs type before beginning the import. This detection step will be reflected in the response. + +**New methods** + +We've added 3 new methods that will enable API consumers to: + + * [update][update-existing-import] the authentication or project choice for an import. If no parameters are provided during the request, the import will be restarted. Please note that this is a **breaking change**. Updating authentication for the originating URL is no longer supported through the [start an import][start-an-import] method. Please update your applications to use the new method. + + * [set their preference][set-git-lfs-preference] for using Git LFS to import files larger than 100MB. + + * [list all the files larger than 100MB][get-large-files] that were found during the import. + +**New attributes for Git LFS** + +Several new response attributes (`use_lfs`, `has_large_files`, `large_files_size`, `large_files`) were added to provide details regarding the large files found during the import. You can read more about the attributes [here][git-lfs-related-fields]. + +As before, to access the API during the preview period, you must provide a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.barred-rock-preview + +For more information, see the [Source Import API documentation][docs], and if you have any questions or feedback, please [let us know][contact]. + + +[docs]: /v3/migration/source_imports/ +[start-an-import]: /v3/migration/source_imports/#start-an-import +[update-existing-import]: /v3/migration/source_imports/#update-existing-import +[set-git-lfs-preference]: /v3/migration/source_imports/#set-git-lfs-preference +[get-large-files]: /v3/migration/source_imports/#get-large-files +[git-lfs-related-fields]: /v3/migration/source_imports/#git-lfs-related-fields +[media-type]: /v3/media +[contact]: https://github.com/contact?form%5Bsubject%5D=Source+Import+API diff --git a/content/changes/2016-05-12-reactions-api-preview.md b/content/changes/2016-05-12-reactions-api-preview.md new file mode 100644 index 0000000000..fbf93d1aa7 --- /dev/null +++ b/content/changes/2016-05-12-reactions-api-preview.md @@ -0,0 +1,33 @@ +--- +title: Preview support for Reactions API +author_name: kneemer +--- + +GitHub recently added [Reactions to Pull Requests, Issues, and Comments][reactions-blog-post] to help people express their feelings more simply and effectively in conversations. We are adding endpoints for Reactions so that you can now react and unreact via the API. You can enable these changes during the preview period by providing a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.squirrel-girl-preview + +For example: + +To view reactions on an issue: + +``` command-line +$ curl "https://api.github.com/repos/github/hubot/issues/1/reactions" \ + -H "Accept: application/vnd.github.squirrel-girl-preview" +``` + + +You can learn more about the new reaction response objects in the updated [Commit comment][commit-comment-doc], [Issue][issue-doc], [Issue comment][issue-comment-doc], and [Review Comment][review-comment-doc] documentation. There is also new [Reaction][reaction-doc] documentation. + +During the preview period, we may change aspects of these APIs based on developer feedback. We will announce the changes here on the developer blog, but we will not provide advance notice. + +If you have any questions or feedback, please [let us know][contact]. + +[media-type]: /v3/media +[reaction-doc]: /v3/reactions +[issue-doc]: /v3/issues#preview-period-org-issues +[issue-comment-doc]: /v3/issues/comments#preview-period-issue-comments +[review-comment-doc]: /v3/pulls/comments#preview-period-pull-comments +[commit-comment-doc]: /v3/repos/comments#preview-period-commits-comments +[contact]: https://github.com/contact?form%5Bsubject%5D=Reactions+API+Preview +[reactions-blog-post]: https://github.com/blog/2119-add-reactions-to-pull-requests-issues-and-comments diff --git a/content/changes/2016-05-23-timeline-preview-api.md b/content/changes/2016-05-23-timeline-preview-api.md new file mode 100644 index 0000000000..2400991a20 --- /dev/null +++ b/content/changes/2016-05-23-timeline-preview-api.md @@ -0,0 +1,19 @@ +--- +title: Preview the Timeline API +author_name: nickh +--- + +We've added an API for issue timelines, which will let you fetch a list +of events from an issue or pull request timeline. + +To access [the Timeline API][docs] during the preview period, you must provide a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.mockingbird-preview + +During the preview period, we may change aspects of these API methods based on developer feedback. If we do, we will announce the changes here on the developer blog, but we will not provide any advance notice. + +If you have any questions or feedback, please [let us know][contact]! + +[media-type]: /v3/media +[docs]: /v3/issues/timeline/ +[contact]: https://github.com/contact?form%5Bsubject%5D=Timeline+API diff --git a/content/changes/2016-06-07-reactions-api-update.md b/content/changes/2016-06-07-reactions-api-update.md new file mode 100644 index 0000000000..017d189394 --- /dev/null +++ b/content/changes/2016-06-07-reactions-api-update.md @@ -0,0 +1,46 @@ +--- +title: Reactions API Preview now includes user information +author_name: kneemer +--- + +To avoid making extra API calls, we've updated the [Reactions API preview][initial-reaction-api-post] to include additional user information when listing Reactions. + +**This is a breaking change for Reaction payloads**. If you're trying out this new API during its preview period, you'll need to update your code to continue working with it. + +## JSON Payload Changes + +We're replacing the `user_id` attribute with `user` and changing the schema type from a number to a JSON object. + +## Example Reaction JSON +```json +[ + { + "id": 1, + "user": { + "login": "octocat", + "id": 1, + "avatar_url": "https://github.com/images/error/octocat_happy.gif", + "gravatar_id": "", + "url": "https://api.github.com/users/octocat", + "html_url": "https://github.com/octocat", + "followers_url": "https://api.github.com/users/octocat/followers", + "following_url": "https://api.github.com/users/octocat/following{/other_user}", + "gists_url": "https://api.github.com/users/octocat/gists{/gist_id}", + "starred_url": "https://api.github.com/users/octocat/starred{/owner}{/repo}", + "subscriptions_url": "https://api.github.com/users/octocat/subscriptions", + "organizations_url": "https://api.github.com/users/octocat/orgs", + "repos_url": "https://api.github.com/users/octocat/repos", + "events_url": "https://api.github.com/users/octocat/events{/privacy}", + "received_events_url": "https://api.github.com/users/octocat/received_events", + "type": "User", + "site_admin": false + }, + "content": "heart" + } +] +``` + +As always, if you have any questions or feedback, please [get in touch][contact]. + +[initial-reaction-api-post]: /changes/2016-05-12-reactions-api-preview +[contact]: https://github.com/contact?form%5Bsubject%5D=Reactions+API+Preview diff --git a/content/changes/2016-06-14-repository-invitations.md b/content/changes/2016-06-14-repository-invitations.md new file mode 100644 index 0000000000..00cddde89d --- /dev/null +++ b/content/changes/2016-06-14-repository-invitations.md @@ -0,0 +1,28 @@ +--- +title: API changes for Repository Invitations +author_name: CoralineAda +--- + +We announced [repository invitation functionality][repo-invitations-announcement] on May 23. Using the site, you can invite collaborators to work on your repository. Invitees will receive an email with the invitation and have the option to accept or decline. + +We have now have endpoints for managing repository invitations for both repository administrators and invitation recipients through the GitHub API. You can enable these changes during the preview period by providing a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.swamp-thing-preview + +For example: + +``` command-line +curl "https://api.github.com/repos/github/hubot/invitations" \ + -H 'Authorization: token TOKEN' \ + -H "Accept: application/vnd.github.swamp-thing-preview" +``` + +You can learn more about the new endpoints in the updated [Collaborators][collaborators] and new [Repository Invitations][repo-invitations] documentation. + +If you have any questions or feedback, please [let us know][contact]. + +[media-type]: /v3/media +[collaborators]: /v3/repos/collaborators +[repo-invitations]: /v3/repos/invitations +[repo-invitations-announcement]: https://github.com/blog/2170-repository-invitations +[contact]: https://github.com/contact?form%5Bsubject%5D=Repository+Invitations+API+Preview diff --git a/content/changes/2016-06-22-issue-locking-api-is-now-official.md b/content/changes/2016-06-22-issue-locking-api-is-now-official.md new file mode 100644 index 0000000000..81fb174003 --- /dev/null +++ b/content/changes/2016-06-22-issue-locking-api-is-now-official.md @@ -0,0 +1,14 @@ +--- +title: Issue locking and unlocking APIs are now official +author_name: davidcelis +--- + +We're making the [Issue locking and unlocking APIs][issue-locking-blog-post] part of the official GitHub API. + +During the preview period you needed to provide the `application/vnd.github.the-key-preview+json` preview media type in the `Accept` header to opt-in to the new endpoints. Now that the preview period has ended, you no longer need to specify this custom [media type][custom-media-types]. + +If you have any questions or feedback, please [get in touch with us][contact]! + +[issue-locking-blog-post]: /changes/2016-02-11-issue-locking-api/ +[custom-media-types]: /v3/media/ +[contact]: https://github.com/contact?form[subject]=Issue+Locking+and+Unlocking+API diff --git a/content/changes/2016-06-27-protected-branches-api-update.md b/content/changes/2016-06-27-protected-branches-api-update.md new file mode 100644 index 0000000000..6ce7053298 --- /dev/null +++ b/content/changes/2016-06-27-protected-branches-api-update.md @@ -0,0 +1,22 @@ +--- +title: Update to Protected Branches API Preview +author_name: tma +--- + +Over the past few months, we've made a few [improvements](https://github.com/blog/2137-protected-branches-improvements) to the way [protected branches](https://github.com/blog/2051-protected-branches-and-required-status-checks) work in our web interface. Today, we're modifying the protected branches API [preview period](https://developer.github.com/changes/2015-11-11-protected-branches-api/) to include these improvements. + +Included in these API changes is the ability to allow organizations to specify which members and teams should be able to push to a protected branch, as well as providing a new setting for required status checks which will remove the requirement of a pull request to be up to date before merging. + +You'll notice a new endpoint structure. One set of endpoints for modifying the branch settings as a whole (`PATCH /repos/:owner/:repo/branches/:branch` has been updated to be `PUT /repos/:owner/:repo/branches/:branch/protection`), and a series of more granular endpoints to modify a subset of the branch protection settings. + +**This will be a breaking change for the protected branch API.** The deprecated API endpoint will be removed when the protected branches API will leave the preview period. If you're trying out the old protected branches API, you'll need to update your code. + +#### How can I try it? + +To access this functionality during the preview period, you’ll need to provide the following custom media type in the Accept header: + +``` +application/vnd.github.loki-preview+json +``` + +Take a look at [the docs here](/v3/repos/branches/). If you have any questions, please [get in touch](https://github.com/contact?form%5Bsubject%5D=Protected+Branches+API+Preview). diff --git a/content/changes/2016-07-06-github-pages-preview-api.md b/content/changes/2016-07-06-github-pages-preview-api.md new file mode 100644 index 0000000000..ab14cbee46 --- /dev/null +++ b/content/changes/2016-07-06-github-pages-preview-api.md @@ -0,0 +1,43 @@ +--- +title: Introducing the GitHub Pages preview API +author_name: benbalter +--- + +We're introducing additional preview functionality to the [GitHub Pages API](/v3/repos/pages/) to give developers better control over their GitHub Pages site. + +#### Requesting a page build + +You can now manually request a build of your GitHub Pages site without needing to push a new commit by making a `POST` request to the endpoint already available to see past builds. For example: + +``` command-line +curl "https://api.github.com/repos/github/developer.github.com/pages/builds" \ + -X POST + -H 'Authorization: token TOKEN' \ + -H "Accept: application/vnd.github.mister-fantastic-preview" \ +``` + +#### Retrieving a site's URL + +With the introduction of [HTTPS support for GitHub Pages sites](https://github.com/blog/2186-https-for-github-pages), it's important to know not just a site's custom domain, if it has one, but also if it has HTTPS enforcement enabled. The GitHub Pages API will now return an additional `html_url` field, which will include the computed absolute URL to the site. + +The resulting URL can be `https://username.github.io` (or `http://username.github.io`) for user sites without a custom domain, `https://username.gituhb.io/project` for project sites, or `http://example.com` for sites with custom domains, saving third-party applications the trouble of having to construct complicated URL logic based on the username, owner, and CNAME, as was previously necessary. + +For example, to request the HTML URL: + +``` command-line +curl "https://api.github.com/repos/github/developer.github.com/pages" \ + -H 'Authorization: token TOKEN' \ + -H "Accept: application/vnd.github.mister-fantastic-preview" \ +``` + +#### How can I try it? + +To access this functionality during the preview period, you’ll need to provide the following custom media type in the Accept header: + +``` +application/vnd.github.mister-fantastic-preview+json +``` + +During the preview period, we may change aspects of these API methods based on developer feedback. If we do, we will announce the changes here on the developer blog, but we will not provide any advance notice. + +For more information, take a look at [the docs here](/v3/repos/pages/), and if you have any questions, please [get in touch](https://github.com/contact?form%5Bsubject%5D=GitHub+Pages+API+Preview). diff --git a/content/changes/2016-07-12-ending-multiple-assignees-preview-period.md b/content/changes/2016-07-12-ending-multiple-assignees-preview-period.md new file mode 100644 index 0000000000..13f6fc318b --- /dev/null +++ b/content/changes/2016-07-12-ending-multiple-assignees-preview-period.md @@ -0,0 +1,13 @@ +--- +title: Multiple Assignees API is now official +author_name: nakajima +--- + +We're making [Multiple Assignees][blog-post] part of the official GitHub API. + +During the preview period you needed to provide the `application/vnd.github.cerberus-preview` preview media type in the `Accept` header to opt-in to the changes. Now that the preview period has ended, you no longer need to specify this custom media type. + +If you have any questions or feedback, please [get in touch with us][contact]! + +[blog-post]: /changes/2016-5-27-multiple-assignees/ +[contact]: https://github.com/contact?form[subject]=Multiple+Assignees+API diff --git a/content/changes/2016-08-09-breaking-change-removed-sensitive-fields-from-organization-api-responses-for-owner.md b/content/changes/2016-08-09-breaking-change-removed-sensitive-fields-from-organization-api-responses-for-owner.md new file mode 100644 index 0000000000..22f0e9cd3c --- /dev/null +++ b/content/changes/2016-08-09-breaking-change-removed-sensitive-fields-from-organization-api-responses-for-owner.md @@ -0,0 +1,22 @@ +--- +title: "Breaking change: Removed sensitive fields from Organization API responses for non-owners" +author_name: kdaigle +--- + +We're removing some values from [Organization API](https://developer.github.com/v3/orgs/) responses to help protect our +users' privacy. Previously, these fields were returned to all members of the organization. +As of today, you must be an Organization owner to +receive values for the following fields in Organization responses: + +* `private_gists` +* `disk_usage` +* `collaborators` +* `billing_email` + +If you're not an organization owner, the above keys will now return `null`. +We will continue to send these fields without their values to minimize the impact +of this change. + +If you have any questions or feedback, please [drop us a line][contact]. + +[contact]: https://github.com/contact?form[subject]=Removed+sensitive+fields+from+org+api diff --git a/content/changes/2016-08-15-traffic-api-preview.md b/content/changes/2016-08-15-traffic-api-preview.md new file mode 100644 index 0000000000..60b089e380 --- /dev/null +++ b/content/changes/2016-08-15-traffic-api-preview.md @@ -0,0 +1,18 @@ +--- +title: Preview the Repository Traffic API +author_name: shreyasjoshis +--- + + We've added an API for repository traffic, which will let you fetch details about traffic for repositories you have push access to. This data is already available in graphical form in the [Graphs section](https://help.github.com/articles/about-repository-graphs/#traffic) on GitHub.com. + +To access [the Traffic API][docs] during the preview period, you must provide a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.spiderman-preview + +During the preview period, we may change aspects of these API methods based on developer feedback. If we do, we will announce the changes here on the developer blog, but we will not provide any advance notice. + +If you have any questions or feedback, please [let us know][contact]! + +[media-type]: /v3/media +[docs]: /v3/repos/traffic/ +[contact]: https://github.com/contact?form%5Bsubject%5D=Traffic+API diff --git a/content/changes/2016-08-23-change-base.md b/content/changes/2016-08-23-change-base.md new file mode 100644 index 0000000000..a83f67b8e3 --- /dev/null +++ b/content/changes/2016-08-23-change-base.md @@ -0,0 +1,25 @@ +--- +title: API changes for changing the base branch on Pull Requests +author_name: scottjg +--- +GitHub recently added the ability to [change the base branch][blog post] on a Pull Request after it's created. Now we're updating the Pull Request API to enable the new functionality. + +For example: + +``` command-line +curl "https://api.github.com/repos/github/hubot/pulls/123" \ + -H 'Authorization: token TOKEN' \ + -d '{ "base": "master" }' +``` + +The Pull Request base will be updated to point to the master branch. + +You can learn more about the new responses and endpoints in the updated [Pull Request][pulls] documentation. + +If you have any questions or feedback, please [let us know][contact]! + + +[pulls]: /v3/pulls +[blog post]: https://github.com/blog/2224-change-the-base-branch-of-a-pull-request +[contact]: https://github.com/contact?form%5Bsubject%5D=Change+base+on+Pull+Requests + diff --git a/content/changes/2016-5-27-multiple-assignees.md b/content/changes/2016-5-27-multiple-assignees.md new file mode 100644 index 0000000000..1a9c70fbb0 --- /dev/null +++ b/content/changes/2016-5-27-multiple-assignees.md @@ -0,0 +1,28 @@ +--- +title: API changes for Multiple Issue Assignees +author_name: nakajima +--- +GitHub recently added the ability to assign up to ten people to issues. We're updating Issue payloads and adding a couple new endpoints to help you build apps. You can enable these changes during the preview period by providing a custom [media type][media-type] in the `Accept` header: + + application/vnd.github.cerberus-preview + +For example: + +``` command-line +curl "https://api.github.com/repos/github/hubot/issues" \ + -H 'Authorization: token TOKEN' \ + -H "Accept: application/vnd.github.cerberus-preview" \ +``` + +The issues returned in this list will include the new `assignees` key. + +You can learn more about the new responses and endpoints in the updated [Issues][issues] and [Issue Assignees][issue-assignees] documentation. + +If you have any questions or feedback, please [let us know][contact]! + + +[media-type]: /v3/media +[issues]: /v3/issues +[issue-assignees]: /v3/issues/assignees +[contact]: https://github.com/contact?form%5Bsubject%5D=Multiple+Assignees+API + diff --git a/content/changes/index.html b/content/changes/index.html index f11cff1475..e51085796f 100644 --- a/content/changes/index.html +++ b/content/changes/index.html @@ -3,5 +3,8 @@ layout: blog --- -<%= render '_changes', :changes => api_changes %> +<%= renderp '/_changes.*', :changes => paginated_api_changes(0, 9) %> +
- Well, hello there! -
-- We're going to now talk to the GitHub API. Ready? - Click here to begin! -
-- If that link doesn't work, remember to provide your own Client ID! -
- - +``` erb + + + + ++ Well, hello there! +
++ We're going to now talk to the GitHub API. Ready? + Click here to begin! +
++ If that link doesn't work, remember to provide your own Client ID! +
+ + +``` (If you're unfamiliar with how Sinatra works, we recommend [reading the Sinatra guide][Sinatra guide].) @@ -77,38 +81,39 @@ Also, notice that the URL uses the `scope` query parameter to define the requesting `user:email` scope for reading private email addresses. Navigate your browser to `http://localhost:4567`. After clicking on the link, you -should be taken to GitHub, and presented with a dialog that looks something like this: - +should be taken to {{ site.data.variables.product.product_name }}, and presented with a dialog that looks something like this: + If you trust yourself, click **Authorize App**. Wuh-oh! Sinatra spits out a `404` error. What gives?! Well, remember when we specified a Callback URL to be `callback`? We didn't provide -a route for it, so GitHub doesn't know where to drop the user after they authorize +a route for it, so {{ site.data.variables.product.product_name }} doesn't know where to drop the user after they authorize the app. Let's fix that now! ### Providing a callback In _server.rb_, add a route to specify what the callback should do: - #!ruby - get '/callback' do - # get temporary GitHub code... - session_code = request.env['rack.request.query_hash']['code'] - - # ... and POST it back to GitHub - result = RestClient.post('https://github.com/login/oauth/access_token', - {:client_id => CLIENT_ID, - :client_secret => CLIENT_SECRET, - :code => session_code}, - :accept => :json) - - # extract the token and granted scopes - access_token = JSON.parse(result)['access_token'] - end - -After a successful app authentication, GitHub provides a temporary `code` value. -You'll need to `POST` this code back to GitHub in exchange for an `access_token`. +``` ruby +get '/callback' do + # get temporary GitHub code... + session_code = request.env['rack.request.query_hash']['code'] + + # ... and POST it back to GitHub + result = RestClient.post('https://github.com/login/oauth/access_token', + {:client_id => CLIENT_ID, + :client_secret => CLIENT_SECRET, + :code => session_code}, + :accept => :json) + + # extract the token and granted scopes + access_token = JSON.parse(result)['access_token'] +end +``` + +After a successful app authentication, {{ site.data.variables.product.product_name }} provides a temporary `code` value. +You'll need to `POST` this code back to {{ site.data.variables.product.product_name }} in exchange for an `access_token`. To simplify our GET and POST HTTP requests, we're using the [rest-client][REST Client]. Note that you'll probably never access the API through REST. For a more serious application, you should probably use [a library written in the language of your choice][libraries]. @@ -123,10 +128,17 @@ were granted for the token by the user. The scopes that were granted are returned as a part of the response from exchanging a token. - #!ruby - # check if we were granted user:email scope - scopes = JSON.parse(result)['scope'].split(',') - has_user_email_scope = scopes.include? 'user:email' +``` ruby +get '/callback' do + # ... + # Get the access_token using the code sample above + # ... + + # check if we were granted user:email scope + scopes = JSON.parse(result)['scope'].split(',') + has_user_email_scope = scopes.include? 'user:email' +end +``` In our application, we're using `scopes.include?` to check if we were granted the `user:email` scope needed for fetching the authenticated user's private @@ -139,7 +151,7 @@ if the application had asked for `user` scope, it might have been granted only `user:email` scope. In that case, the application wouldn't have been granted what it asked for, but the granted scopes would have still been sufficient. -Checking for scopes only before making requests is not enough since it's posible +Checking for scopes only before making requests is not enough since it's possible that users will change the scopes in between your check and the actual request. In case that happens, API calls you expected to succeed might fail with a `404` or `401` status, or return a different subset of information. @@ -157,36 +169,39 @@ changes in available application functionality. At last, with this access token, you'll be able to make authenticated requests as the logged in user: - #!ruby - # fetch user information - auth_result = JSON.parse(RestClient.get('https://api.github.com/user', - {:params => {:access_token => access_token}})) +``` ruby +# fetch user information +auth_result = JSON.parse(RestClient.get('https://api.github.com/user', + {:params => {:access_token => access_token}})) - # if the user authorized it, fetch private emails - if has_user_email_scope - auth_result['private_emails'] = - JSON.parse(RestClient.get('https://api.github.com/user/emails', - {:params => {:access_token => access_token}})) +# if the user authorized it, fetch private emails +if has_user_email_scope + auth_result['private_emails'] = + JSON.parse(RestClient.get('https://api.github.com/user/emails', + {:params => {:access_token => access_token}})) +end - erb :basic, :locals => auth_result +erb :basic, :locals => auth_result +``` We can do whatever we want with our results. In this case, we'll just dump them straight into _basic.erb_: - #!html+erb -Hello, <%= login %>!
-- <% if !email.nil? && !email.empty? %> It looks like your public email address is <%= email %>. - <% else %> It looks like you don't have a public email. That's cool. - <% end %> -
-- <% if defined? private_emails %> - With your permission, we were also able to dig up your private email addresses: - <%= private_emails.join(', ') %> - <% else %> - Also, you're a bit secretive about your private email addresses. - <% end %> -
+``` erb +Hello, <%= login %>!
++ <% if !email.nil? && !email.empty? %> It looks like your public email address is <%= email %>. + <% else %> It looks like you don't have a public email. That's cool. + <% end %> +
++ <% if defined? private_emails %> + With your permission, we were also able to dig up your private email addresses: + <%= private_emails.map{ |private_email_address| private_email_address["email"] }.join(', ') %> + <% else %> + Also, you're a bit secretive about your private email addresses. + <% end %> +
+``` ## Implementing "persistent" authentication @@ -196,7 +211,7 @@ time they needed to access the web page. For example, try navigating directly to What if we could circumvent the entire "click here" process, and just _remember_ that, as long as the user's logged into -GitHub, they should be able to access this application? Hold on to your hat, +{{ site.data.variables.product.product_name }}, they should be able to access this application? Hold on to your hat, because _that's exactly what we're going to do_. Our little server above is rather simple. In order to wedge in some intelligent @@ -212,86 +227,86 @@ the `user:email` scope. Create a file called _advanced_server.rb_, and paste these lines into it: - #!ruby - require 'sinatra' - require 'rest_client' - require 'json' - - # !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! - # Instead, set and test environment variables, like below - # if ENV['GITHUB_CLIENT_ID'] && ENV['GITHUB_CLIENT_SECRET'] - # CLIENT_ID = ENV['GITHUB_CLIENT_ID'] - # CLIENT_SECRET = ENV['GITHUB_CLIENT_SECRET'] - # end - - CLIENT_ID = ENV['GH_BASIC_CLIENT_ID'] - CLIENT_SECRET = ENV['GH_BASIC_SECRET_ID'] - - use Rack::Session::Cookie, :secret => rand.to_s() - - def authenticated? - session[:access_token] +``` ruby +require 'sinatra' +require 'rest_client' +require 'json' + +# !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! +# Instead, set and test environment variables, like below +# if ENV['GITHUB_CLIENT_ID'] && ENV['GITHUB_CLIENT_SECRET'] +# CLIENT_ID = ENV['GITHUB_CLIENT_ID'] +# CLIENT_SECRET = ENV['GITHUB_CLIENT_SECRET'] +# end + +CLIENT_ID = ENV['GH_BASIC_CLIENT_ID'] +CLIENT_SECRET = ENV['GH_BASIC_SECRET_ID'] + +use Rack::Session::Pool, :cookie_only => false + +def authenticated? + session[:access_token] +end + +def authenticate! + erb :index, :locals => {:client_id => CLIENT_ID} +end + +get '/' do + if !authenticated? + authenticate! + else + access_token = session[:access_token] + scopes = [] + + begin + auth_result = RestClient.get('https://api.github.com/user', + {:params => {:access_token => access_token}, + :accept => :json}) + rescue => e + # request didn't succeed because the token was revoked so we + # invalidate the token stored in the session and render the + # index page so that the user can start the OAuth flow again + + session[:access_token] = nil + return authenticate! end - def authenticate! - erb :index, :locals => {:client_id => CLIENT_ID} + # the request succeeded, so we check the list of current scopes + if auth_result.headers.include? :x_oauth_scopes + scopes = auth_result.headers[:x_oauth_scopes].split(', ') end - get '/' do - if !authenticated? - authenticate! - else - access_token = session[:access_token] - scopes = [] - - begin - auth_result = RestClient.get('https://api.github.com/user', - {:params => {:access_token => access_token}, - :accept => :json}) - rescue => e - # request didn't succeed because the token was revoked so we - # invalidate the token stored in the session and render the - # index page so that the user can start the OAuth flow again - - session[:access_token] = nil - return authenticate! - end - - # the request succeeded, so we check the list of current scopes - if auth_result.headers.include? :x_oauth_scopes - scopes = auth_result.headers[:x_oauth_scopes].split(', ') - end - - auth_result = JSON.parse(auth_result) - - if scopes.include? 'user:email' - auth_result['private_emails'] = - JSON.parse(RestClient.get('https://api.github.com/user/emails', - {:params => {:access_token => access_token}, - :accept => :json})) - end - - erb :advanced, :locals => auth_result - end + auth_result = JSON.parse(auth_result) + + if scopes.include? 'user:email' + auth_result['private_emails'] = + JSON.parse(RestClient.get('https://api.github.com/user/emails', + {:params => {:access_token => access_token}, + :accept => :json})) end - get '/callback' do - session_code = request.env['rack.request.query_hash']['code'] + erb :advanced, :locals => auth_result + end +end - result = RestClient.post('https://github.com/login/oauth/access_token', - {:client_id => CLIENT_ID, - :client_secret => CLIENT_SECRET, - :code => session_code}, - :accept => :json) +get '/callback' do + session_code = request.env['rack.request.query_hash']['code'] - session[:access_token] = JSON.parse(result)['access_token'] + result = RestClient.post('https://github.com/login/oauth/access_token', + {:client_id => CLIENT_ID, + :client_secret => CLIENT_SECRET, + :code => session_code}, + :accept => :json) - redirect '/' - end + session[:access_token] = JSON.parse(result)['access_token'] + redirect '/' +end +``` Much of the code should look familiar. For example, we're still using `RestClient.get` -to call out to the GitHub API, and we're still passing our results to be rendered +to call out to the {{ site.data.variables.product.product_name }} API, and we're still passing our results to be rendered in an ERB template (this time, it's called `advanced.erb`). Also, we now have the `authenticated?` method which checks if the user is already @@ -300,27 +315,28 @@ OAuth flow and updates the session with the granted token and scopes. Next, create a file in _views_ called _advanced.erb_, and paste this markup into it: - #!html+erb - - - - -Well, well, well, <%= login %>!
-- <% if !email.empty? %> It looks like your public email address is <%= email %>. - <% else %> It looks like you don't have a public email. That's cool. - <% end %> -
-- <% if defined? private_emails %> - With your permission, we were also able to dig up your private email addresses: - <%= private_emails.join(', ') %> - <% else %> - Also, you're a bit secretive about your private email addresses. - <% end %> -
- - +``` erb + + + + +Well, well, well, <%= login %>!
++ <% if !email.empty? %> It looks like your public email address is <%= email %>. + <% else %> It looks like you don't have a public email. That's cool. + <% end %> +
++ <% if defined? private_emails %> + With your permission, we were also able to dig up your private email addresses: + <%= private_emails.map{ |private_email_address| private_email_address["email"] }.join(', ') %> + <% else %> + Also, you're a bit secretive about your private email addresses. + <% end %> +
+ + +``` From the command line, call `ruby advanced_server.rb`, which starts up your server on port `4567` -- the same port we used when we had a simple Sinatra app. @@ -329,10 +345,10 @@ which redirects you to `/callback`. `/callback` then sends us back to `/`, and since we've been authenticated, renders _advanced.erb_. We could completely simplify this roundtrip routing by simply changing our callback -URL in GitHub to `/`. But, since both _server.rb_ and _advanced.rb_ are relying on +URL in {{ site.data.variables.product.product_name }} to `/`. But, since both _server.rb_ and _advanced.rb_ are relying on the same callback URL, we've got to do a little bit of wonkiness to make it work. -Also, if we had never authorized this application to access our GitHub data, +Also, if we had never authorized this application to access our {{ site.data.variables.product.product_name }} data, we would've seen the same confirmation dialog from earlier pop-up and warn us. If you'd like, you can play around with [yet another Sinatra-GitHub auth example][sinatra auth github test] @@ -341,7 +357,7 @@ available as a separate project. [webflow]: /v3/oauth/#web-application-flow [Sinatra]: http://www.sinatrarb.com/ [about env vars]: http://en.wikipedia.org/wiki/Environment_variable#Getting_and_setting_environment_variables -[Sinatra guide]: http://sinatra-book.gittr.com/#hello_world_application +[Sinatra guide]: https://github.com/sinatra/sinatra-book/blob/master/book/Introduction.markdown#hello-world-application [REST Client]: https://github.com/archiloque/rest-client [libraries]: /libraries/ [sinatra auth github test]: https://github.com/atmos/sinatra-auth-github-test @@ -350,4 +366,4 @@ available as a separate project. [check token valid]: /v3/oauth_authorizations/#check-an-authorization [platform samples]: https://github.com/github/platform-samples/tree/master/api/ruby/basics-of-authentication [new oauth app]: https://github.com/settings/applications/new -[app settings]: https://github.com/settings/applications +[app settings]: https://github.com/settings/developers diff --git a/content/guides/best-practices-for-integrators.md b/content/guides/best-practices-for-integrators.md new file mode 100644 index 0000000000..f0cd17c9b4 --- /dev/null +++ b/content/guides/best-practices-for-integrators.md @@ -0,0 +1,162 @@ +--- +title: Best practices for integrators +--- + +# Best practices for integrators + +Interested in integrating with the GitHub platform? [You're in good company](https://github.com/integrations). This guide will help you build an app that provides the best experience for your users *and* ensure that it's reliably interacting with the API. + +{:toc} + +## Secure payloads delivered from GitHub + +It's very important that you secure [the payloads sent from GitHub][event-types]. Although no personal information (like passwords) is ever transmitted in a payload, leaking *any* information is not good. Some information that might be sensitive include committer email address or the names of private repositories. + +There are three steps you can take to secure receipt of payloads delivered by GitHub: + +1. Ensure that your receiving server is on an HTTPS connection. By default, GitHub will verify SSL certificates when delivering payloads. +2. You can whitelist [the IP address we use when delivering hooks](https://help.github.com/articles/what-ip-addresses-does-github-use-that-i-should-whitelist) to your server. To ensure that you're always checking the right IP address, you can [use the `/meta` endpoint](/v3/meta/#meta) to find the address we use. +3. Provide [a secret token](/webhooks/securing/) to ensure payloads are definitely coming from GitHub. By enforcing a secret token, you're ensuring that any data received by your server is absolutely coming from GitHub. Ideally, you should provide a different secret token *per user* of your service. That way, if one token is compromised, no other user would be affected. + +## Favor asynchronous work over synchronous + +GitHub expects that integrations respond within thirty seconds of receiving the webhook payload. If your service takes longer than that to complete, then GitHub terminates the connection and the payload is lost. + +Since it's impossible to predict how fast your service will complete, you should do all of "the real work" in a background job. [Resque](https://github.com/resque/resque/) (for Ruby), [RQ](http://python-rq.org/) (for Python), or [RabbitMQ](http://www.rabbitmq.com/) (for Java) are examples of libraries that can handle queuing and processing of background jobs. + +Note that even with a background job running, GitHub still expects your server to respond within thirty seconds. Your server simply needs to acknowledge that it received the payload by sending some sort of response. It's critical that your service to performs any validations on a payload as soon as possible, so that you can accurately report whether your server will continue with the request or not. + +## Use appropriate HTTP status codes when responding to GitHub + +Every webhook has its own "Recent Deliveries" section, which lists whether a deployment was successful or not. + + + +You should make use of proper HTTP status codes in order to inform users. You can use codes like `201` or `202` to acknowledge receipt of payload that won't be processed (for example, a payload delivered by a branch that's not the default). Reserve the `500` error code for catastrophic failures. + +## Provide as much information as possible to the user + +Users can dig into the server responses you send back to GitHub. Ensure that your messages are clear and informative. + + + +## Follow any redirects that the API sends you + +GitHub is explicit in telling you when a resource has moved by providing a redirect status code. You should follow these redirections. Every redirect response sets the `Location` header with the new URI to go to. If you receive a redirect, it's best to update your code to follow the new URI, in case you're requesting a deprecated path that we might remove. + +We've provided [a list of HTTP status codes](/v3/#http-redirects) to watch out for when designing your app to follow redirects. + +## Don't manually parse URLs + +Often, API responses contain data in the form of URLs. For example, when requesting a repository, we'll send a key called `clone_url` with a URL you can use to clone the repository. + +For the stability of your app, you shouldn't try to parse this data or try to guess and construct the format of future URLs. Your app is liable to break if we decide to change the URL. + +For example, when working with paginated results, it's often tempting to construct URLs that append `?page=
-$ curl https://api.github.com/zen
+``` command-line
+$ curl {{ site.data.variables.product.api_url_pre }}/zen
-Keep it logically awesome.
-
+> Keep it logically awesome.
+```
The response will be a random selection from our design philosophies.
Next, let's `GET` [Chris Wanstrath's][defunkt github] [GitHub profile][users api]:
-
+``` command-line
# GET /users/defunkt
-$ curl https://api.github.com/users/defunkt
+$ curl {{ site.data.variables.product.api_url_pre }}/users/defunkt
-{
- "login": "defunkt",
- "id": 2,
- "url": "https://api.github.com/users/defunkt",
- "html_url": "https://github.com/defunkt",
- ...
-}
-
+> {
+> "login": "defunkt",
+> "id": 2,
+> "url": "{{ site.data.variables.product.api_url_pre }}/users/defunkt",
+> "html_url": "https://github.com/defunkt",
+> ...
+> }
+```
Mmmmm, tastes like [JSON][json]. Let's add the `-i` flag to include headers:
-
-$ curl -i https://api.github.com/users/defunkt
-
-HTTP/1.1 200 OK
-Server: GitHub.com
-Date: Sun, 11 Nov 2012 18:43:28 GMT
-Content-Type: application/json; charset=utf-8
-Connection: keep-alive
-Status: 200 OK
-ETag: "bfd85cbf23ac0b0c8a29bee02e7117c6"
-X-RateLimit-Limit: 60
-X-RateLimit-Remaining: 57
-X-RateLimit-Reset: 1352660008
-X-GitHub-Media-Type: github.v3
-Vary: Accept
-Cache-Control: public, max-age=60, s-maxage=60
-X-Content-Type-Options: nosniff
-Content-Length: 692
-Last-Modified: Tue, 30 Oct 2012 18:58:42 GMT
-
-{
- "login": "defunkt",
- "id": 2,
- "url": "https://api.github.com/users/defunkt",
- "html_url": "https://github.com/defunkt",
- ...
-}
-
+``` command-line
+$ curl -i {{ site.data.variables.product.api_url_pre }}/users/defunkt
+
+> HTTP/1.1 200 OK
+> Server: GitHub.com
+> Date: Sun, 11 Nov 2012 18:43:28 GMT
+> Content-Type: application/json; charset=utf-8
+> Connection: keep-alive
+> Status: 200 OK
+> ETag: "bfd85cbf23ac0b0c8a29bee02e7117c6"
+> X-RateLimit-Limit: 60
+> X-RateLimit-Remaining: 57
+> X-RateLimit-Reset: 1352660008
+> X-GitHub-Media-Type: github.v3
+> Vary: Accept
+> Cache-Control: public, max-age=60, s-maxage=60
+> X-Content-Type-Options: nosniff
+> Content-Length: 692
+> Last-Modified: Tue, 30 Oct 2012 18:58:42 GMT
+
+> {
+> "login": "defunkt",
+> "id": 2,
+> "url": "{{ site.data.variables.product.api_url_pre }}/users/defunkt",
+> "html_url": "https://github.com/defunkt",
+> ...
+> }
+```
There are a few interesting bits in the response headers. As expected, the
`Content-Type` is `application/json`.
@@ -93,19 +92,19 @@ client has already spent.
## Authentication
Unauthenticated clients can make 60 requests per hour. To get more, we'll need to
-_authenticate_. In fact, doing anything interesting with the GitHub API requires
+_authenticate_. In fact, doing anything interesting with the {{ site.data.variables.product.product_name }} API requires
[authentication][authentication].
### Basic
-The easiest way to authenticate with the GitHub API is by simply using your GitHub
+The easiest way to authenticate with the {{ site.data.variables.product.product_name }} API is by simply using your {{ site.data.variables.product.product_name }}
username and password via Basic Authentication.
-
-$ curl -i -u <your_username> https://api.github.com/users/defunkt
+``` command-line
+$ curl -i -u your_username {{ site.data.variables.product.api_url_pre }}/users/defunkt
-Enter host password for user '<your_username>':
-
+> Enter host password for user your_username:
+```
The `-u` flag sets the username, and cURL will prompt you for the password. You
can use `-u "username:password"` to avoid the prompt, but this leaves your
@@ -121,19 +120,19 @@ reading and writing private information via the API.
If you have [two-factor authentication][2fa] enabled, the API will return a
`401 Unauthorized` error code for the above request (and every other API request):
-
-$ curl -i -u <your_username> https://api.github.com/users/defunkt
+``` command-line
+$ curl -i -u your_username {{ site.data.variables.product.api_url_pre }}/users/defunkt
-Enter host password for user '<your_username>':
+> Enter host password for user your_username:
-HTTP/1.1 401 Unauthorized
-X-GitHub-OTP: required; :2fa-type
+> HTTP/1.1 401 Unauthorized
+> X-GitHub-OTP: required; :2fa-type
-{
- "message": "Must specify two-factor authentication OTP code.",
- "documentation_url": "https://developer.github.com/v3/auth#working-with-two-factor-authentication"
-}
-
+> {
+> "message": "Must specify two-factor authentication OTP code.",
+> "documentation_url": "https://developer.github.com/v3/auth#working-with-two-factor-authentication"
+> }
+```
The easiest way to get around that error is to create an OAuth token and use
OAuth authentication instead of Basic Authentication. See the
@@ -142,32 +141,32 @@ OAuth authentication instead of Basic Authentication. See the
### Get your own user profile
When properly authenticated, you can take advantage of the permissions
-associated with your GitHub account. For example, try getting
+associated with your {{ site.data.variables.product.product_name }} account. For example, try getting
[your own user profile][auth user api]:
-
-$ curl -i -u <your_username> https://api.github.com/user
-
-{
- ...
- "plan": {
- "space": 2516582,
- "collaborators": 10,
- "private_repos": 20,
- "name": "medium"
- }
- ...
-}
-
+``` command-line
+$ curl -i -u your_username {{ site.data.variables.product.api_url_pre }}/user
+
+> {
+> ...
+> "plan": {
+> "space": 2516582,
+> "collaborators": 10,
+> "private_repos": 20,
+> "name": "medium"
+> }
+> ...
+> }
+```
This time, in addition to the same set of public information we
retrieved for [@defunkt][defunkt github] earlier, you should also see the non-public
information for your user profile. For example, you'll see a `plan` object
-in the response which gives details about the GitHub plan for the account.
+in the response which gives details about the {{ site.data.variables.product.product_name }} plan for the account.
### OAuth
-While convenient, Basic Authentication isn't ideal because you shouldn't give your GitHub
+While convenient, Basic Authentication isn't ideal because you shouldn't give your {{ site.data.variables.product.product_name }}
username and password to anyone. Applications that need to read or write
private information using the API on behalf of another user should use [OAuth][oauth].
@@ -179,58 +178,61 @@ features:
will provide before authorizing a third party app
Normally, tokens are created via a [web flow][webflow]. An application
-sends users to GitHub to log in. GitHub then presents a dialog
+sends users to {{ site.data.variables.product.product_name }} to log in. {{ site.data.variables.product.product_name }} then presents a dialog
indicating the name of the app, as well as the level of access the app
-has once it's authorized by the user. After a user authorizes access, GitHub
+has once it's authorized by the user. After a user authorizes access, {{ site.data.variables.product.product_name }}
redirects the user back to the application:
-
+
However, you don't need to set up the entire web flow to begin working with OAuth tokens.
-An easier way to get a token is to [create a **Personal token**][personal token] via your
-[Application settings page][application settings]:
+An easier way to get a token is to [create a **personal access token**][personal token] via your
+[Personal access tokens settings page][tokens settings]:
-
+
Also, the [**Authorizations API**][authorizations api] makes it simple to use Basic Authentication
to create an OAuth token. Try pasting and running the following command:
-
-$ curl -i -u <your_username> -d '{"scopes": ["repo"], "note": "getting-started"}' \
- https://api.github.com/authorizations
-
-HTTP/1.1 201 Created
-Location: https://api.github.com/authorizations/2
-Content-Length: 384
-
-{
- "scopes": [
- "repo"
- ],
- "token": "5199831f4dd3b79e7c5b7e0ebe75d67aa66e79d4",
- "updated_at": "2012-11-14T14:04:24Z",
- "url": "https://api.github.com/authorizations/2",
- "app": {
- "url": "https://developer.github.com/v3/oauth/#oauth-authorizations-api",
- "name": "GitHub API"
- },
- "created_at": "2012-11-14T14:04:24Z",
- "note_url": null,
- "id": 2,
- "note": "getting-started"
-}
-
+``` command-line
+$ curl -i -u your_username -d '{"scopes": ["repo", "user"], "note": "getting-started"}' \
+$ {{ site.data.variables.product.api_url_pre }}/authorizations
+
+> HTTP/1.1 201 Created
+> Location: {{ site.data.variables.product.api_url_pre }}/authorizations/2
+> Content-Length: 384
+
+> {
+> "scopes": [
+> "repo",
+> "user"
+> ],
+> "token": "5199831f4dd3b79e7c5b7e0ebe75d67aa66e79d4",
+> "updated_at": "2012-11-14T14:04:24Z",
+> "url": "{{ site.data.variables.product.api_url_pre }}/authorizations/2",
+> "app": {
+> "url": "https://developer.github.com/v3/oauth/#oauth-authorizations-api",
+> "name": "GitHub API"
+> },
+> "created_at": "2012-11-14T14:04:24Z",
+> "note_url": null,
+> "id": 2,
+> "note": "getting-started"
+> }
+```
There's a lot going on in this one little call, so let's break it down. First,
the `-d` flag indicates we're doing a `POST`, using the
`application/x-www-form-urlencoded` content type (as opposed to `GET`). All `POST`
-requests to the GitHub API should be in JSON.
+requests to the {{ site.data.variables.product.product_name }} API should be in JSON.
Next, let's look at the `scopes` we're sending over in this call. When creating
a new token, we include an optional array of [_scopes_][scopes], or access
levels, that indicate what information this token can access. In this case,
we're setting up the token with _repo_ access, which grants access to read and
-write to private repositories. See [the scopes docs][scopes] for a full list of
+write to public and private repositories, and _user_ scope, which grants read
+and write access to public and private user profile data. See
+[the scopes docs][scopes] for a full list of
scopes. You should **only** request scopes that your application actually needs,
in order to not frighten users with potentially invasive actions. The `201`
status code tells us that the call was successful, and the JSON returned
@@ -241,11 +243,11 @@ return the [previously described `401 Unauthorized` error code][2fa section]
for the above request. You can get around that error by providing a 2FA OTP code
in the [X-GitHub-OTP request header][2fa header]:
-
-$ curl -i -u <your_username> -H "X-GitHub-OTP: <your_2fa_OTP_code>" \
- -d '{"scopes": ["repo"], "note": "getting-started"}' \
- https://api.github.com/authorizations
-
+``` command-line
+$ curl -i -u your_username -H "X-GitHub-OTP: your_2fa_OTP_code" \
+ -d '{"scopes": ["repo", "user"], "note": "getting-started"}' \
+ {{ site.data.variables.product.api_url_pre }}/authorizations
+```
If you enabled 2FA with a mobile application, go ahead and get an OTP code from
your one-time password application on your phone. If you enabled 2FA with text
@@ -255,10 +257,10 @@ this endpoint.
Now, we can use the forty character `token` instead of a username and password
in the rest of our examples. Let's grab our own user info again, using OAuth this time:
-+``` command-line $ curl -i -H 'Authorization: token 5199831f4dd3b79e7c5b7e0ebe75d67aa66e79d4' \ - https://api.github.com/user -+ {{ site.data.variables.product.api_url_pre }}/user +``` **Treat OAuth tokens like passwords!** Don't share them with other users or store them in insecure places. The tokens in these examples are fake and the names have @@ -269,32 +271,32 @@ the [Repositories API][repos-api]. ## Repositories -Almost any meaningful use of the GitHub API will involve some level of Repository +Almost any meaningful use of the {{ site.data.variables.product.product_name }} API will involve some level of Repository information. We can [`GET` repository details][get repo] in the same way we fetched user details earlier: -
-$ curl -i https://api.github.com/repos/twbs/bootstrap -+``` command-line +$ curl -i {{ site.data.variables.product.api_url_pre }}/repos/twbs/bootstrap +``` In the same way, we can [view repositories for the authenticated user][user repos api]: -
+``` command-line $ curl -i -H 'Authorization: token 5199831f4dd3b79e7c5b7e0ebe75d67aa66e79d4' \ - https://api.github.com/user/repos -+ {{ site.data.variables.product.api_url_pre }}/user/repos +``` Or, we can [list repositories for another user][other user repos api]: -
-$ curl -i https://api.github.com/users/technoweenie/repos -+``` command-line +$ curl -i {{ site.data.variables.product.api_url_pre }}/users/technoweenie/repos +``` Or, we can [list repositories for an organization][org repos api]: -
-$ curl -i https://api.github.com/orgs/mozilla/repos -+``` command-line +$ curl -i {{ site.data.variables.product.api_url_pre }}/orgs/mozilla/repos +``` The information returned from these calls will depend on how we authenticate: @@ -308,9 +310,9 @@ can filter the repositories returned based on what type of access the user has for the repository. In this way, we can fetch only directly-owned repositories, organization repositories, or repositories the user collaborates on via a team. -
-$ curl -i "https://api.github.com/users/technoweenie/repos?type=owner" -+``` command-line +$ curl -i "{{ site.data.variables.product.api_url_pre }}/users/technoweenie/repos?type=owner" +``` In this example, we grab only those repositories that technoweenie owns, not the ones on which he collaborates. Note the quoted URL above. Depending on your @@ -320,10 +322,10 @@ query string. ### Create a repository Fetching information for existing repositories is a common use case, but the -GitHub API supports creating new repositories as well. To [create a repository][create repo], +{{ site.data.variables.product.product_name }} API supports creating new repositories as well. To [create a repository][create repo], we need to `POST` some JSON containing the details and configuration options. -
+``` command-line
$ curl -i -H 'Authorization: token 5199831f4dd3b79e7c5b7e0ebe75d67aa66e79d4' \
-d '{ \
"name": "blog", \
@@ -331,14 +333,13 @@ $ curl -i -H 'Authorization: token 5199831f4dd3b79e7c5b7e0ebe75d67aa66e79d4' \
"private": true, \
"gitignore_template": "nanoc" \
}' \
- https://api.github.com/user/repos
-
+ {{ site.data.variables.product.api_url_pre }}/user/repos
+```
In this minimal example, we create a new repository for our blog (to be served
on [GitHub Pages][pages], perhaps). Though the blog will be public, we've made
the repository private. In this single step, we'll also initialize it with
-a README and a [nanoc][nanoc]-flavored [.gitignore template][gitignore
-templates].
+a README and a [nanoc][nanoc]-flavored [.gitignore template][gitignore templates].
The resulting repository will be found at `https://github.com/
-$ curl -i https://api.github.com/repos/pengwynn/blog
+``` command-line
+$ curl -i {{ site.data.variables.product.api_url_pre }}/repos/pengwynn/blog
-HTTP/1.1 404 Not Found
+> HTTP/1.1 404 Not Found
-{
- "message": "Not Found"
-}
-
+> {
+> "message": "Not Found"
+> }
+```
Oh noes! Where did it go? Since we created the repository as _private_, we need
to authenticate in order to see it. If you're a grizzled HTTP user, you might
expect a `403` instead. Since we don't want to leak information about private
-repositories, the GitHub API returns a `404` in this case, as if to say "we can
+repositories, the {{ site.data.variables.product.product_name }} API returns a `404` in this case, as if to say "we can
neither confirm nor deny the existence of this repository."
## Issues
-The UI for Issues on GitHub aims to provide 'just enough' workflow while
-staying out of your way. With the GitHub [Issues API][issues-api], you can pull
+The UI for Issues on {{ site.data.variables.product.product_name }} aims to provide 'just enough' workflow while
+staying out of your way. With the {{ site.data.variables.product.product_name }} [Issues API][issues-api], you can pull
data out or create issues from other tools to create a workflow that works for
your team.
Just like github.com, the API provides a few methods to view issues for the
authenticated user. To [see all your issues][get issues api], call `GET /issues`:
-+``` command-line $ curl -i -H 'Authorization: token 5199831f4dd3b79e7c5b7e0ebe75d67aa66e79d4' \ - https://api.github.com/issues -+ {{ site.data.variables.product.api_url_pre }}/issues +``` -To get only the [issues under one of your GitHub organizations][get issues api], call `GET +To get only the [issues under one of your {{ site.data.variables.product.product_name }} organizations][get issues api], call `GET /orgs/
+``` command-line $ curl -i -H 'Authorization: token 5199831f4dd3b79e7c5b7e0ebe75d67aa66e79d4' \ - https://api.github.com/orgs/rails/issues -+ {{ site.data.variables.product.api_url_pre }}/orgs/rails/issues +``` We can also get [all the issues under a single repository][repo issues api]: -
-$ curl -i https://api.github.com/repos/rails/rails/issues -+``` command-line +$ curl -i {{ site.data.variables.product.api_url_pre }}/repos/rails/rails/issues +``` ### Pagination @@ -397,14 +398,15 @@ A project the size of Rails has thousands of issues. We'll need to [paginate][pa making multiple API calls to get the data. Let's repeat that last call, this time taking note of the response headers: -
-$ curl -i https://api.github.com/repos/rails/rails/issues
+``` command-line
+$ curl -i {{ site.data.variables.product.api_url_pre }}/repos/rails/rails/issues
-HTTP/1.1 200 OK
+> HTTP/1.1 200 OK
-Link: <https://api.github.com/repos/rails/rails/issues?page=2>; rel="next",
-<https://api.github.com/repos/rails/rails/issues?page=14>; rel="last"
-
+> ...
+> Link: <{{ site.data.variables.product.api_url_pre }}/repositories/8514/issues?page=2>; rel="next", <{{ site.data.variables.product.api_url_pre }}/repositories/8514/issues?page=30>; rel="last"
+> ...
+```
The [`Link` header][link-header] provides a way for a response to link to
external resources, in this case additional pages of data. Since our call found
@@ -421,55 +423,55 @@ OAuth token in the header. Also, we'll pass the title, body, and labels in the J
body to the `/issues` path underneath the repository in which we want to create
the issue:
-
+``` command-line
$ curl -i -H 'Authorization: token 5199831f4dd3b79e7c5b7e0ebe75d67aa66e79d4' \
- -d '{ \
- "title": "New logo", \
- "body": "We should have one", \
- "labels": ["design"] \
- }' \
- https://api.github.com/repos/pengwynn/api-sandbox/issues
-
-HTTP/1.1 201 Created
-Location: https://api.github.com/repos/pengwynn/api-sandbox/issues/17
-X-RateLimit-Limit: 5000
-
-{
- "pull_request": {
- "patch_url": null,
- "html_url": null,
- "diff_url": null
- },
- "created_at": "2012-11-14T15:25:33Z",
- "comments": 0,
- "milestone": null,
- "title": "New logo",
- "body": "We should have one",
- "user": {
- "login": "pengwynn",
- "gravatar_id": "7e19cd5486b5d6dc1ef90e671ba52ae0",
- "avatar_url": "https://secure.gravatar.com/avatar/7e19cd5486b5d6dc1ef90e671ba52ae0?d=https://a248.e.akamai.net/assets.github.com%2Fimages%2Fgravatars%2Fgravatar-user-420.png",
- "id": 865,
- "url": "https://api.github.com/users/pengwynn"
- },
- "closed_at": null,
- "updated_at": "2012-11-14T15:25:33Z",
- "number": 17,
- "closed_by": null,
- "html_url": "https://github.com/pengwynn/api-sandbox/issues/17",
- "labels": [
- {
- "color": "ededed",
- "name": "design",
- "url": "https://api.github.com/repos/pengwynn/api-sandbox/labels/design"
- }
- ],
- "id": 8356941,
- "assignee": null,
- "state": "open",
- "url": "https://api.github.com/repos/pengwynn/api-sandbox/issues/17"
-}
-
+$ -d '{ \
+$ "title": "New logo", \
+$ "body": "We should have one", \
+$ "labels": ["design"] \
+$ }' \
+$ {{ site.data.variables.product.api_url_pre }}/repos/pengwynn/api-sandbox/issues
+
+> HTTP/1.1 201 Created
+> Location: {{ site.data.variables.product.api_url_pre }}/repos/pengwynn/api-sandbox/issues/17
+> X-RateLimit-Limit: 5000
+
+> {
+> "pull_request": {
+> "patch_url": null,
+> "html_url": null,
+> "diff_url": null
+> },
+> "created_at": "2012-11-14T15:25:33Z",
+> "comments": 0,
+> "milestone": null,
+> "title": "New logo",
+> "body": "We should have one",
+> "user": {
+> "login": "pengwynn",
+> "gravatar_id": "7e19cd5486b5d6dc1ef90e671ba52ae0",
+> "avatar_url": "https://secure.gravatar.com/avatar/7e19cd5486b5d6dc1ef90e671ba52ae0?d=https://a248.e.akamai.net/assets.github.com%2Fimages%2Fgravatars%2Fgravatar-user-420.png",
+> "id": 865,
+> "url": "{{ site.data.variables.product.api_url_pre }}/users/pengwynn"
+> },
+> "closed_at": null,
+> "updated_at": "2012-11-14T15:25:33Z",
+> "number": 17,
+> "closed_by": null,
+> "html_url": "https://github.com/pengwynn/api-sandbox/issues/17",
+> "labels": [
+> {
+> "color": "ededed",
+> "name": "design",
+> "url": "{{ site.data.variables.product.api_url_pre }}/repos/pengwynn/api-sandbox/labels/design"
+> }
+> ],
+> "id": 8356941,
+> "assignee": null,
+> "state": "open",
+> "url": "{{ site.data.variables.product.api_url_pre }}/repos/pengwynn/api-sandbox/issues/17"
+> }
+```
The response gives us a couple of pointers to the newly created issue, both in
the `Location` response header and the `url` field of the JSON response.
@@ -481,30 +483,30 @@ caching information that hasn't changed. The API supports [conditional
requests][conditional-requests] and helps you do the right thing. Consider the
first call we made to get defunkt's profile:
-
-$ curl -i https://api.github.com/users/defunkt
+``` command-line
+$ curl -i {{ site.data.variables.product.api_url_pre }}/users/defunkt
-HTTP/1.1 200 OK
-ETag: "bfd85cbf23ac0b0c8a29bee02e7117c6"
-
+> HTTP/1.1 200 OK
+> ETag: "bfd85cbf23ac0b0c8a29bee02e7117c6"
+```
In addition to the JSON body, take note of the HTTP status code of `200` and
the `ETag` header.
The [ETag][etag] is a fingerprint of the response. If we pass that on subsequent calls,
we can tell the API to give us the resource again, only if it has changed:
-
+``` command-line
$ curl -i -H 'If-None-Match: "bfd85cbf23ac0b0c8a29bee02e7117c6"' \
- https://api.github.com/users/defunkt
+$ {{ site.data.variables.product.api_url_pre }}/users/defunkt
-HTTP/1.1 304 Not Modified
-
+> HTTP/1.1 304 Not Modified
+```
The `304` status indicates that the resource hasn't changed since the last time
we asked for it and the response will contain no body. As a bonus, `304`
responses don't count against your [rate limit][rate-limiting].
-Woot! Now you know the basics of the GitHub API!
+Woot! Now you know the basics of the {{ site.data.variables.product.product_name }} API!
* Basic & OAuth authentication
* Fetching and creating repositories and issues
@@ -522,10 +524,10 @@ Keep learning with the next API guide [Basics of Authentication][auth guide]!
[scopes]: /v3/oauth/#scopes
[repos-api]: /v3/repos/
[pages]: http://pages.github.com
-[nanoc]: http://nanoc.stoneship.org/
+[nanoc]: http://nanoc.ws/
[gitignore templates]: https://github.com/github/gitignore
[issues-api]: /v3/issues/
-[link-header]: http://www.w3.org/wiki/LinkHeader
+[link-header]: http://www.w3.org/wiki/LinkHeader/
[conditional-requests]: /v3/#conditional-requests
[rate-limiting]: /v3/#rate-limiting
[users api]: /v3/users/#get-a-single-user
@@ -538,7 +540,7 @@ Keep learning with the next API guide [Basics of Authentication][auth guide]!
[2fa header]: /v3/auth/#working-with-two-factor-authentication
[oauth section]: /guides/getting-started/#oauth
[personal token]: https://help.github.com/articles/creating-an-access-token-for-command-line-use
-[application settings]: https://github.com/settings/applications
+[tokens settings]: https://github.com/settings/tokens
[pagination]: /v3/#pagination
[get repo]: /v3/repos/#get
[create repo]: /v3/repos/#create
diff --git a/content/guides/index.md b/content/guides/index.md
index 6c3b0be0ed..4b2d2e5219 100644
--- a/content/guides/index.md
+++ b/content/guides/index.md
@@ -1,12 +1,12 @@
---
-title: Development Guides | GitHub API
+title: Development Guides
layout: guides
---
# Development Guides
This section of the documentation is intended to get you up-and-running with
-real-world GitHub API applications. We'll cover everything you need to know, from
+real-world {{ site.data.variables.product.product_name }} API applications. We'll cover everything you need to know, from
authentication, to manipulating results, to combining results with other services.
Every tutorial here will have a project, and every project will be
@@ -15,4 +15,4 @@ stored and documented in our public
Feel free to fork, clone, and improve these guides.
-
+
diff --git a/content/guides/managing-deploy-keys.md b/content/guides/managing-deploy-keys.md
new file mode 100644
index 0000000000..5c830b6b62
--- /dev/null
+++ b/content/guides/managing-deploy-keys.md
@@ -0,0 +1,127 @@
+---
+title: Managing deploy keys
+---
+
+# Managing Deploy Keys
+
+{:toc}
+
+There are four ways to manage SSH keys on your servers when automating deployment scripts:
+
+* SSH agent forwarding
+* HTTPS with OAuth tokens
+* Deploy keys
+* Machine users
+
+This guide will help you decide what strategy is best for you.
+
+## SSH agent forwarding
+
+In many cases, especially in the beginning of a project, SSH agent forwarding is the quickest and simplest method to use. Agent forwarding uses the same SSH keys that your local development computer uses.
+
+#### Pros
+
+* You do not have to generate or keep track of any new keys.
+* There is no key management; users have the same permissions on the server that they do locally.
+* No keys are stored on the server, so in case the server is compromised, you don't need to hunt down and remove the compromised keys.
+
+#### Cons
+
+* Users **must** SSH in to deploy; automated deploy processes can't be used.
+* SSH agent forwarding can be troublesome to run for Windows users.
+
+#### Setup
+
+1. Turn on agent forwarding locally. See [our guide on SSH agent forwarding][ssh-agent-forwarding] for more information.
+2. Set your deploy scripts to use agent forwarding. For example, on a bash script, enabling agent forwarding would look something like this: `ssh -A serverA 'bash -s' < deploy.sh`
+
+## HTTPS cloning with OAuth tokens
+
+If you don't want to use SSH keys, you can use [HTTPS with OAuth tokens][git-automation].
+
+#### Pros
+
+* Anyone with access to the server can deploy the repository.
+* Users don't have to change their local SSH settings.
+* Multiple tokens (one for each user) are not needed; one token per server is enough.
+* A token can be revoked at any time, turning it essentially into a one-use password.
+* Generating new tokens can be easily scripted using [the OAuth API](https://developer.github.com/v3/oauth_authorizations/#create-a-new-authorization)
+
+#### Cons
+
+* You must make sure that you configure your token with the correct access scopes.
+* Tokens are essentially passwords, and must be protected the same way.
+
+#### Setup
+
+See [our guide on Git automation with tokens][git-automation].
+
+## Deploy keys
+
+A deploy key is an SSH key that is stored on your server and grants access to a single {{ site.data.variables.product.product_name }} repository. This key is attached directly to the repository instead of to a personal user account.
+
+#### Pros
+
+* Anyone with access to the repository and server has the ability to deploy the project.
+* Users don't have to change their local SSH settings.
+* Deploy keys can read and write by default, but can be made read-only.
+
+#### Cons
+
+* Deploy keys only grant access to a single repository. More complex projects may have many repositories to pull to the same server.
+* Deploy keys are usually not protected by a passphrase, making the key easily accessible if the server is compromised.
+
+#### Setup
+
+1. [Run the `ssh-keygen` procedure][generating-ssh-keys] on your server.
+2. In the top right corner of any {{ site.data.variables.product.product_name }} page, click your profile photo.
+ 
+3. On your profile page, click the **Repositories** tab, then click the name of your repository.
+ 
+4. In your repository's right sidebar, click **Settings**.
+ 
+3. In the sidebar, click **Deploy Keys**.
+ 
+3. Click **Add deploy key**. Paste your public key in and submit.
+ 
+
+## Machine users
+
+If your server needs to access multiple repositories, you can choose to create a new {{ site.data.variables.product.product_name }} account and attach an SSH key that will be used exclusively for automation. Since this {{ site.data.variables.product.product_name }} account won't be used by a human, it's called a machine user. You can then [add the machine user as collaborator][collaborator] or [add the machine user to a team][team] with access to the repositories it needs to manipulate. **NOTE**: Adding a machine user as a collaborator always grants read/write access. Adding a machine user to a team grants the permissions of the team.
+
+{% if page.version == 'dotcom' %}
+
+{{#tip}}
+
+**Tip:** Our [terms of service][tos] state:
+
+> *Accounts registered by "bots" or other automated methods are not permitted.*
+
+This means that you cannot automate the creation of accounts. But if you want to create a single machine user for automating tasks such as deploy scripts in your project or organization, that is totally cool.
+
+{{/tip}}
+
+{% endif %}
+
+#### Pros
+
+* Anyone with access to the repository and server has the ability to deploy the project.
+* No (human) users need to change their local SSH settings.
+* Multiple keys are not needed; one per server is adequate.
+
+#### Cons
+
+* Only organizations have access to create teams; therefore only organizations can use them to restrict machine users to read-only access. Personal repositories always grant collaborators read/write access.
+* Machine user keys, like deploy keys, are usually not protected by a passphrase.
+
+#### Setup
+
+1. [Run the `ssh-keygen` procedure][generating-ssh-keys] on your server and attach the public key to the machine user account.
+2. Give that account access to the repositories it will need to access. You can do this by [adding the account as collaborator][collaborator] or [adding it to a team][team] in an organization.
+
+[ssh-agent-forwarding]: /guides/using-ssh-agent-forwarding/
+[generating-ssh-keys]: https://help.github.com/articles/generating-ssh-keys
+[tos]: https://help.github.com/articles/github-terms-of-service/
+[git-automation]: https://help.github.com/articles/git-automation-with-oauth-tokens
+[collaborator]: https://help.github.com/articles/how-do-i-add-a-collaborator
+[team]: https://help.github.com/articles/adding-organization-members-to-a-team
diff --git a/content/guides/rendering-data-as-graphs.md b/content/guides/rendering-data-as-graphs.md
index 4bcd8b19a6..02d61e1fc9 100644
--- a/content/guides/rendering-data-as-graphs.md
+++ b/content/guides/rendering-data-as-graphs.md
@@ -1,16 +1,15 @@
---
-title: Rendering Data as Graphs | GitHub API
+title: Rendering Data as Graphs
---
# Rendering Data as Graphs
-* TOC
{:toc}
In this guide, we're going to use the API to fetch information about repositories
that we own, and the programming languages that make them up. Then, we'll
visualize that information in a couple of different ways using the [D3.js][D3.js] library. To
-interact with the GitHub API, we'll be using the excellent Ruby library, [Octokit][Octokit].
+interact with the {{ site.data.variables.product.product_name }} API, we'll be using the excellent Ruby library, [Octokit][Octokit].
If you haven't already, you should read the ["Basics of Authentication"][basics-of-authentication]
guide before starting this example. You can find the complete source code for this project in the [platform-samples][platform samples] repository.
@@ -19,60 +18,62 @@ Let's jump right in!
## Setting up an OAuth application
-First, [register a new application][new oauth application] on GitHub. Set the main and callback
+First, [register a new application][new oauth application] on {{ site.data.variables.product.product_name }}. Set the main and callback
URLs to `http://localhost:4567/`. As [before][basics-of-authentication], we're going to handle authentication for the API by
implementing a Rack middleware using [sinatra-auth-github][sinatra auth github]:
- #!ruby
- require 'sinatra/auth/github'
-
- module Example
- class MyGraphApp < Sinatra::Base
- # !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!!
- # Instead, set and test environment variables, like below
- # if ENV['GITHUB_CLIENT_ID'] && ENV['GITHUB_CLIENT_SECRET']
- # CLIENT_ID = ENV['GITHUB_CLIENT_ID']
- # CLIENT_SECRET = ENV['GITHUB_CLIENT_SECRET']
- # end
-
- CLIENT_ID = ENV['GH_GRAPH_CLIENT_ID']
- CLIENT_SECRET = ENV['GH_GRAPH_SECRET_ID']
-
- enable :sessions
-
- set :github_options, {
- :scopes => "repo",
- :secret => CLIENT_SECRET,
- :client_id => CLIENT_ID,
- :callback_url => "/"
- }
-
- register Sinatra::Auth::Github
-
- get '/' do
- if !authenticated?
- authenticate!
- else
- access_token = github_user["token"]
- end
- end
+``` ruby
+require 'sinatra/auth/github'
+
+module Example
+ class MyGraphApp < Sinatra::Base
+ # !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!!
+ # Instead, set and test environment variables, like below
+ # if ENV['GITHUB_CLIENT_ID'] && ENV['GITHUB_CLIENT_SECRET']
+ # CLIENT_ID = ENV['GITHUB_CLIENT_ID']
+ # CLIENT_SECRET = ENV['GITHUB_CLIENT_SECRET']
+ # end
+
+ CLIENT_ID = ENV['GH_GRAPH_CLIENT_ID']
+ CLIENT_SECRET = ENV['GH_GRAPH_SECRET_ID']
+
+ enable :sessions
+
+ set :github_options, {
+ :scopes => "repo",
+ :secret => CLIENT_SECRET,
+ :client_id => CLIENT_ID,
+ :callback_url => "/"
+ }
+
+ register Sinatra::Auth::Github
+
+ get '/' do
+ if !authenticated?
+ authenticate!
+ else
+ access_token = github_user["token"]
end
end
+ end
+end
+```
Set up a similar _config.ru_ file as in the previous example:
- #!ruby
- ENV['RACK_ENV'] ||= 'development'
- require "rubygems"
- require "bundler/setup"
+``` ruby
+ENV['RACK_ENV'] ||= 'development'
+require "rubygems"
+require "bundler/setup"
- require File.expand_path(File.join(File.dirname(__FILE__), 'server'))
+require File.expand_path(File.join(File.dirname(__FILE__), 'server'))
- run Example::MyGraphApp
+run Example::MyGraphApp
+```
## Fetching repository information
-This time, in order to talk to the GitHub API, we're going to use the [Octokit
+This time, in order to talk to the {{ site.data.variables.product.product_name }} API, we're going to use the [Octokit
Ruby library][Octokit]. This is much easier than directly making a bunch of
REST calls. Plus, Octokit was developed by a GitHubber, and is actively maintained,
so you know it'll work.
@@ -80,43 +81,48 @@ so you know it'll work.
Authentication with the API via Octokit is easy. Just pass your login
and token to the `Octokit::Client` constructor:
- #!ruby
- if !authenticated?
- authenticate!
- else
- octokit_client = Octokit::Client.new(:login => github_user.login, :oauth_token => github_user.token)
- end
+``` ruby
+if !authenticated?
+ authenticate!
+else
+ octokit_client = Octokit::Client.new(:login => github_user.login, :oauth_token => github_user.token)
+end
+```
Let's do something interesting with the data about our repositories. We're going
to see the different programming languages they use, and count which ones are used
most often. To do that, we'll first need a list of our repositories from the API.
With Octokit, that looks like this:
- #!ruby
- repos = client.repositories
+``` ruby
+repos = client.repositories
+```
-Next, we'll iterate over each repository, and count the language that GitHub
+Next, we'll iterate over each repository, and count the language that {{ site.data.variables.product.product_name }}
associates with it:
- #!ruby
- language_obj = {}
- repos.each do |repo|
- # sometimes language can be nil
- if repo.language
- if !language_obj[repo.language]
- language_obj[repo.language] = 1
- else
- language_obj[repo.language] += 1
- end
- end
+``` ruby
+language_obj = {}
+repos.each do |repo|
+ # sometimes language can be nil
+ if repo.language
+ if !language_obj[repo.language]
+ language_obj[repo.language] = 1
+ else
+ language_obj[repo.language] += 1
end
+ end
+end
- languages.to_s
+languages.to_s
+```
When you restart your server, your web page should display something
that looks like this:
- {"JavaScript"=>13, "PHP"=>1, "Perl"=>1, "CoffeeScript"=>2, "Python"=>1, "Java"=>3, "Ruby"=>3, "Go"=>1, "C++"=>1}
+``` ruby
+{"JavaScript"=>13, "PHP"=>1, "Perl"=>1, "CoffeeScript"=>2, "Python"=>1, "Java"=>3, "Ruby"=>3, "Go"=>1, "C++"=>1}
+```
So far, so good, but not very human-friendly. A visualization
would be great in helping us understand how these language counts are distributed. Let's feed
@@ -131,13 +137,14 @@ check out ["D3 for Mortals"][D3 mortals].
D3 is a JavaScript library, and likes working with data as arrays. So, let's convert our Ruby hash into
a JSON array for use by JavaScript in the browser.
- #!ruby
- languages = []
- language_obj.each do |lang, count|
- languages.push :language => lang, :count => count
- end
+``` ruby
+languages = []
+language_obj.each do |lang, count|
+ languages.push :language => lang, :count => count
+end
- erb :lang_freq, :locals => { :languages => languages.to_json}
+erb :lang_freq, :locals => { :languages => languages.to_json}
+```
We're simply iterating over each key-value pair in our object and pushing them into
a new array. The reason we didn't do this earlier is because we didn't want to iterate
@@ -147,83 +154,84 @@ Now, _lang_freq.erb_ is going to need some JavaScript to support rendering a bar
For now, you can just use the code provided here, and refer to the resources linked above
if you want to learn more about how D3 works:
- #!html
-
-
-
-
-
-
-
-
- Check this sweet data out:
- - - - - +``` html + + + + + + + + +Check this sweet data out:
+ + + + + +``` Phew! Again, don't worry about what most of this code is doing. The relevant part here is a line way at the top--`var data = <%= languages %>;`--which indicates @@ -246,100 +254,104 @@ should be a great way to visualize the sizes of our coding languages used, rathe than simply the count. We'll need to construct an array of objects that looks something like this: - #!javascript - [ { "name": "language1", "size": 100}, - { "name": "language2", "size": 23} - ... - ] +``` json +[ { "name": "language1", "size": 100}, + { "name": "language2", "size": 23} + ... +] +``` Since we already have a list of repositories above, let's inspect each one, and call [the language listing API method][language API]: - #!ruby - repos.each do |repo| - repo_name = repo.name - repo_langs = octokit_client.languages("#{github_user.login}/#{repo_name}") - end +``` ruby +repos.each do |repo| + repo_name = repo.name + repo_langs = octokit_client.languages("#{github_user.login}/#{repo_name}") +end +``` From there, we'll cumulatively add each language found to a "master list": - #!ruby - repo_langs.each do |lang, count| - if !language_obj[lang] - language_obj[lang] = count - else - language_obj[lang] += count - end - end +``` ruby +repo_langs.each do |lang, count| + if !language_obj[lang] + language_obj[lang] = count + else + language_obj[lang] += count + end +end +``` After that, we'll format the contents into a structure that D3 understands: - #!ruby - language_obj.each do |lang, count| - language_byte_count.push :name => "#{lang} (#{count})", :count => count - end +``` ruby +language_obj.each do |lang, count| + language_byte_count.push :name => "#{lang} (#{count})", :count => count +end - # some mandatory formatting for D3 - language_bytes = [ :name => "language_bytes", :elements => language_byte_count] +# some mandatory formatting for D3 +language_bytes = [ :name => "language_bytes", :elements => language_byte_count] +``` (For more information on D3 tree map magic, check out [this simple tutorial][language API].) To wrap up, we pass this JSON information over to the same ERB template: - #!ruby - erb :lang_freq, :locals => { :languages => languages.to_json, :language_byte_count => language_bytes.to_json} - +``` ruby +erb :lang_freq, :locals => { :languages => languages.to_json, :language_byte_count => language_bytes.to_json} +``` Like before, here's a bunch of JavaScript that you can drop directly into your template: - #!html - - +``` html + + +``` Et voila! Beautiful rectangles containing your repo languages, with relative proportions that are easy to see at a glance. You might need to @@ -350,7 +362,7 @@ arguments to `drawTreemap` above, to get all the information to show up properly [D3.js]: http://d3js.org/ [basics-of-authentication]: ../basics-of-authentication/ [sinatra auth github]: https://github.com/atmos/sinatra_auth_github -[Octokit]: https://github.com/pengwynn/octokit +[Octokit]: https://github.com/octokit/octokit.rb [D3 mortals]: http://www.recursion.org/d3-for-mere-mortals/ [D3 treemap]: http://bl.ocks.org/mbostock/4063582 [language API]: https://developer.github.com/v3/repos/#list-languages diff --git a/content/guides/traversing-with-pagination.md b/content/guides/traversing-with-pagination.md index 62ab0b7d5d..ff4d11cf0b 100644 --- a/content/guides/traversing-with-pagination.md +++ b/content/guides/traversing-with-pagination.md @@ -1,17 +1,16 @@ --- -title: Traversing with Pagination | GitHub API +title: Traversing with Pagination --- # Traversing with Pagination -* TOC {:toc} -The GitHub API provides a vast wealth of information for developers to consume. +The {{ site.data.variables.product.product_name }} API provides a vast wealth of information for developers to consume. Most of the time, you might even find that you're asking for _too much_ information, and in order to keep our servers happy, the API will automatically [paginate the requested items][pagination]. -In this guide, we'll make some calls to the GitHub Search API, and iterate over +In this guide, we'll make some calls to the {{ site.data.variables.product.product_name }} Search API, and iterate over the results using pagination. You can find the complete source code for this project in the [platform-samples][platform samples] repository. @@ -32,7 +31,9 @@ Information about pagination is provided in [the Link header](http://tools.ietf. of an API call. For example, let's make a curl request to the search API, to find out how many times Mozilla projects use the phrase `addClass`: - curl -I "https://api.github.com/search/code?q=addClass+user:mozilla" +``` command-line +$ curl -I "{{ site.data.variables.product.api_url_pre }}/search/code?q=addClass+user:mozilla" +``` The `-I` parameter indicates that we only care about the headers, not the actual content. In examining the result, you'll notice some information in the Link header @@ -59,7 +60,9 @@ through the pages to consume the results. You do this by passing in a `page` parameter. By default, `page` always starts at `1`. Let's jump ahead to page 14 and see what happens: - curl -I "https://api.github.com/search/code?q=addClass+user:mozilla&page=14" +``` command-line +$ curl -I "https://api.github.com/search/code?q=addClass+user:mozilla&page=14" +``` Here's the link header once more: @@ -79,7 +82,9 @@ between the first, previous, next, or last list of results in an API call. By passing the `per_page` parameter, you can specify how many items you want each page to return, up to 100 items. Let's try asking for 50 items about `addClass`: - curl -I "https://api.github.com/search/code?q=addClass+user:mozilla&per_page=50" +``` command-line +$ curl -I "https://api.github.com/search/code?q=addClass+user:mozilla&per_page=50" +``` Notice what it does to the header response: @@ -99,20 +104,22 @@ just described above. As always, first we'll require [GitHub's Octokit.rb][octokit.rb] Ruby library, and pass in our [personal access token][personal token]: - #!ruby - require 'octokit' +``` ruby +require 'octokit' - # !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! - # Instead, set and test environment variables, like below - client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] +# !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! +# Instead, set and test environment variables, like below +client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] +``` Next, we'll execute the search, using Octokit's `search_code` method. Unlike using `curl`, we can also immediately retrieve the number of results, so let's do that: - #!ruby - results = client.search_code('addClass user:mozilla') - total_count = results.total_count +``` ruby +results = client.search_code('addClass user:mozilla') +total_count = results.total_count +``` Now, let's grab the number of the last page, similar to `page=34>; rel="last"` information in the link header. Octokit.rb support pagination information through @@ -126,11 +133,12 @@ on. These relations also contain information about the resulting URL, by calling Knowing this, let's grab the page number of the last result, and present all this information to the user: - #!ruby - last_response = client.last_response - number_of_pages = last_response.rels[:last].href.match(/page=(\d+)$/)[1] +``` ruby +last_response = client.last_response +number_of_pages = last_response.rels[:last].href.match(/page=(\d+).*$/)[1] - puts "There are #{total_count} results, on #{number_of_pages} pages!" +puts "There are #{total_count} results, on #{number_of_pages} pages!" +``` Finally, let's iterate through the results. You could do this with a loop `for i in 1..number_of_pages.to_i`, but instead, let's follow the `rels[:next]` headers to retrieve information from @@ -140,105 +148,108 @@ we'll retrieve the data set for the next page by following the `rels[:next]` inf The loop will finish when there is no `rels[:next]` information to consume (in other words, we are at `rels[:last]`). It might look something like this: - #!ruby - loop do - puts last_response.data.items.first.path - last_response = last_response.rels[:next].get - sleep 4 # back off from the API rate limiting; don't do this in Real Life - break if last_response.rels[:next].nil? - end +``` ruby +puts last_response.data.items.first.path +until last_response.rels[:next].nil? + last_response = last_response.rels[:next].get + puts last_response.data.items.first.path +end +``` Changing the number of items per page is extremely simple with Octokit.rb. Simply pass a `per_page` options hash to the initial client construction. After that, your code should remain intact: - #!ruby - require 'octokit' +``` ruby +require 'octokit' - # !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! - # Instead, set and test environment variables, like below - client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] +# !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! +# Instead, set and test environment variables, like below +client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] - results = client.search_code('addClass user:mozilla', :per_page => 100) - total_count = results.total_count +results = client.search_code('addClass user:mozilla', :per_page => 100) +total_count = results.total_count - last_response = client.last_response - number_of_pages = last_response.rels[:last].href.match(/page=(\d+)$/)[1] +last_response = client.last_response +number_of_pages = last_response.rels[:last].href.match(/page=(\d+).*$/)[1] - puts last_response.rels[:last].href - puts "There are #{total_count} results, on #{number_of_pages} pages!" +puts last_response.rels[:last].href +puts "There are #{total_count} results, on #{number_of_pages} pages!" - puts "And here's the first path for every set" +puts "And here's the first path for every set" - loop do - puts last_response.data.items.first.path - last_response = last_response.rels[:next].get - sleep 4 # back off from the API rate limiting; don't do this in Real Life - break if last_response.rels[:next].nil? - end +puts last_response.data.items.first.path +until last_response.rels[:next].nil? + last_response = last_response.rels[:next].get + puts last_response.data.items.first.path +end +``` ## Constructing Pagination Links Normally, with pagination, your goal isn't to concatenate all of the possible results, but rather, to produce a set of navigation, like this: - + Let's sketch out a micro-version of what that might entail. From the code above, we already know we can get the `number_of_pages` in the paginated results from the first call: - #!ruby - require 'octokit' +``` ruby +require 'octokit' - # !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! - # Instead, set and test environment variables, like below - client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] +# !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! +# Instead, set and test environment variables, like below +client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] - results = client.search_code('addClass user:mozilla') - total_count = results.total_count +results = client.search_code('addClass user:mozilla') +total_count = results.total_count - last_response = client.last_response - number_of_pages = last_response.rels[:last].href.match(/page=(\d+)$/)[1] - - puts last_response.rels[:last].href - puts "There are #{total_count} results, on #{number_of_pages} pages!" +last_response = client.last_response +number_of_pages = last_response.rels[:last].href.match(/page=(\d+).*$/)[1] +puts last_response.rels[:last].href +puts "There are #{total_count} results, on #{number_of_pages} pages!" +``` From there, we can construct a beautiful ASCII representation of the number boxes: - - #!ruby - numbers = "" - for i in 1..number_of_pages.to_i - numbers << "[#{i}] " - end - puts numbers +``` ruby +numbers = "" +for i in 1..number_of_pages.to_i + numbers << "[#{i}] " +end +puts numbers +``` Let's simulate a user clicking on one of these boxes, by constructing a random number: - #!ruby - random_page = Random.new - random_page = random_page.rand(1..number_of_pages.to_i) +``` ruby +random_page = Random.new +random_page = random_page.rand(1..number_of_pages.to_i) - puts "A User appeared, and clicked number #{random_page}!" +puts "A User appeared, and clicked number #{random_page}!" +``` Now that we have a page number, we can use Octokit to explicitly retrieve that individual page, by passing the `:page` option: - #!ruby - clicked_results = client.search_code('addClass user:mozilla', :page => random_page) +``` ruby +clicked_results = client.search_code('addClass user:mozilla', :page => random_page) +``` If we wanted to get fancy, we could also grab the previous and next pages, in -order to generate links for back (`<<`) and foward (`>>`) elements: +order to generate links for back (`<<`) and forward (`>>`) elements: - #!ruby - prev_page_href = client.last_response.rels[:prev] ? client.last_response.rels[:prev].href : "(none)" - next_page_href = client.last_response.rels[:next] ? client.last_response.rels[:next].href : "(none)" +``` ruby +prev_page_href = client.last_response.rels[:prev] ? client.last_response.rels[:prev].href : "(none)" +next_page_href = client.last_response.rels[:next] ? client.last_response.rels[:next].href : "(none)" - puts "The prev page link is #{prev_page_href}" - puts "The next page link is #{next_page_href}" +puts "The prev page link is #{prev_page_href}" +puts "The next page link is #{next_page_href}" +``` [pagination]: /v3/#pagination [platform samples]: https://github.com/github/platform-samples/tree/master/api/ruby/traversing-with-pagination diff --git a/content/guides/using-ssh-agent-forwarding.md b/content/guides/using-ssh-agent-forwarding.md new file mode 100644 index 0000000000..6a19d0c804 --- /dev/null +++ b/content/guides/using-ssh-agent-forwarding.md @@ -0,0 +1,155 @@ +--- +title: Using SSH Agent Forwarding +--- + +# Using SSH agent forwarding + +{:toc} + +SSH agent forwarding can be used to make deploying to a server simple. It allows you to use your local SSH keys instead of leaving keys (without passphrases!) sitting on your server. + +If you've already set up an SSH key to interact with {{ site.data.variables.product.product_name }}, you're probably familiar with `ssh-agent`. It's a program that runs in the background and keeps your key loaded into memory, so that you don't need to enter your passphrase every time you need to use the key. The nifty thing is, you can choose to let servers access your local `ssh-agent` as if they were already running on the server. This is sort of like asking a friend to enter their password so that you can use their computer. + +Check out [Steve Friedl's Tech Tips guide][tech-tips] for a more detailed explanation of SSH agent forwarding. + +## Setting up SSH agent forwarding + +Ensure that your own SSH key is set up and working. You can use [our guide on generating SSH keys][generating-keys] if you've not done this yet. + +You can test that your local key works by entering `ssh -T git@github.com` in the terminal: + +``` command-line +$ ssh -T git@github.com +# Attempt to SSH in to github +> Hi username! You've successfully authenticated, but GitHub does not provide +> shell access. +``` + +We're off to a great start. Let's set up SSH to allow agent forwarding to your server. + +1. Using your favorite text editor, open up the file at `~/.ssh/config`. If this file doesn't exist, you can create it by entering `touch ~/.ssh/config` in the terminal. + +2. Enter the following text into the file, replacing `example.com` with your server's domain name or IP: + + Host example.com + ForwardAgent yes + +{{#warning}} + +**Warning:** You may be tempted to use a wildcard like `Host *` to just apply this setting to all SSH connections. That's not really a good idea, as you'd be sharing your local SSH keys with *every* server you SSH into. They won't have direct access to the keys, but they will be able to use them *as you* while the connection is established. **You should only add servers you trust and that you intend to use with agent forwarding.** + +{{/warning}} + +## Testing SSH agent forwarding + +To test that agent forwarding is working with your server, you can SSH into your server and run `ssh -T git@github.com` once more. If all is well, you'll get back the same prompt as you did locally. + +If you're unsure if your local key is being used, you can also inspect the `SSH_AUTH_SOCK` variable on your server: + +``` command-line +$ echo "$SSH_AUTH_SOCK" +# Print out the SSH_AUTH_SOCK variable +> /tmp/ssh-4hNGMk8AZX/agent.79453 +``` + +If the variable is not set, it means that agent forwarding is not working: + +``` command-line +$ echo "$SSH_AUTH_SOCK" +# Print out the SSH_AUTH_SOCK variable +> [No output] +$ ssh -T git@github.com +# Try to SSH to github +> Permission denied (publickey). +``` + +## Troubleshooting SSH agent forwarding + +Here are some things to look out for when troubleshooting SSH agent forwarding. + +### You must be using an SSH URL to check out code + +SSH forwarding only works with SSH URLs, not HTTP(s) URLs. Check the *.git/config* file on your server and ensure the URL is an SSH-style URL like below: + +``` command-line +[remote "origin"] + url = git@github.com:yourAccount/yourProject.git + fetch = +refs/heads/*:refs/remotes/origin/* +``` + +### Your SSH keys must work locally + +Before you can make your keys work through agent forwarding, they must work locally first. [Our guide on generating SSH keys][generating-keys] can help you set up your SSH keys locally. + +### Your system must allow SSH agent forwarding + +Sometimes, system configurations disallow SSH agent forwarding. You can check if a system configuration file is being used by entering the following command in the terminal: + +``` command-line +$ ssh -v example.com +# Connect to example.com with verbose debug output +> OpenSSH_5.6p1, OpenSSL 0.9.8r 8 Feb 2011 +> debug1: Reading configuration data /Users/you/.ssh/config +> debug1: Applying options for example.com +> debug1: Reading configuration data /etc/ssh_config +> debug1: Applying options for * +$ exit +# Returns to your local command prompt +``` + +In the example above, the file *~/.ssh/config* is loaded first, then */etc/ssh_config* is read. We can inspect that file to see if it's overriding our options by running the following commands: + +``` command-line +$ cat /etc/ssh_config +# Print out the /etc/ssh_config file +> Host * +> SendEnv LANG LC_* +> ForwardAgent no +``` + +In this example, our */etc/ssh_config* file specifically says `ForwardAgent no`, which is a way to block agent forwarding. Deleting this line from the file should get agent forwarding working once more. + +### Your server must allow SSH agent forwarding on inbound connections + +Agent forwarding may also be blocked on your server. You can check that agent forwarding is permitted by SSHing into the server and running `sshd_config`. The output from this command should indicate that `AllowAgentForwarding` is set. + +### Your local `ssh-agent` must be running + +On most computers, the operating system automatically launches `ssh-agent` for you. On Windows, however, you need to do this manually. We have [a guide on how to start `ssh-agent` whenever you open Git Bash][autolaunch-ssh-agent]. + +To verify that `ssh-agent` is running on your computer, type the following command in the terminal: + +``` command-line +$ echo "$SSH_AUTH_SOCK" +# Print out the SSH_AUTH_SOCK variable +> /tmp/launch-kNSlgU/Listeners +``` + +### Your key must be available to `ssh-agent` + +You can check that your key is visible to `ssh-agent` by running the following command: + +``` command-line +ssh-add -L +``` + +If the command says that no identity is available, you'll need to add your key: + +``` command-line +$ ssh-add yourkey +``` + +{{#tip}} + +On Mac OS X, `ssh-agent` will "forget" this key, once it gets restarted during reboots. But you can import your SSH keys into Keychain using this command: + +``` command-line +$ /usr/bin/ssh-add -K yourkey +``` + +{{/tip}} + +[tech-tips]: http://www.unixwiz.net/techtips/ssh-agent-forwarding.html +[generating-keys]: https://help.github.com/articles/generating-ssh-keys +[ssh-passphrases]: https://help.github.com/ssh-key-passphrases/ +[autolaunch-ssh-agent]: https://help.github.com/articles/working-with-ssh-key-passphrases#auto-launching-ssh-agent-on-msysgit diff --git a/content/guides/working-with-comments.md b/content/guides/working-with-comments.md index 3a1f3850bf..13a4266023 100644 --- a/content/guides/working-with-comments.md +++ b/content/guides/working-with-comments.md @@ -1,17 +1,16 @@ --- -title: Working with Comments | GitHub API +title: Working with Comments --- # Working with Comments -* TOC {:toc} -For any Pull Request, GitHub provides three kinds of comment views: +For any Pull Request, {{ site.data.variables.product.product_name }} provides three kinds of comment views: [comments on the Pull Request][PR comment] as a whole, [comments on a specific line][PR line comment] within the Pull Request, and [comments on a specific commit][commit comment] within the Pull Request. -Each of these types of comments goes through a different portion of the GitHub API. +Each of these types of comments goes through a different portion of the {{ site.data.variables.product.product_name }} API. In this guide, we'll explore how you can access and manipulate each one. For every example, we'll be using [this sample Pull Request made][sample PR] on the "octocat" repository. As always, samples can be found in [our platform-samples repository][platform-samples]. @@ -29,20 +28,21 @@ We'll demonstrate fetching Pull Request comments by creating a Ruby script using The following code should help you get started accessing comments from a Pull Request using Octokit.rb: - #!ruby - require 'octokit' +``` ruby +require 'octokit' - # !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! - # Instead, set and test environment variables, like below - client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] +# !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! +# Instead, set and test environment variables, like below +client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] - client.issue_comments("octocat/Spoon-Knife", 1176).each do |comment| - username = comment[:user][:login] - post_date = comment[:created_at] - content = comment[:body] +client.issue_comments("octocat/Spoon-Knife", 1176).each do |comment| + username = comment[:user][:login] + post_date = comment[:created_at] + content = comment[:body] - puts "#{username} made a comment on #{post_date}. It says:\n'#{content}'\n" - end + puts "#{username} made a comment on #{post_date}. It says:\n'#{content}'\n" +end +``` Here, we're specifically calling out to the Issues API to get the comments (`issue_comments`), providing both the repository's name (`octocat/Spoon-Knife`), and the Pull Request ID @@ -57,22 +57,23 @@ within a changed file. The endpoint URL for this discussion comes from [the Pull The following code fetches all the Pull Request comments made on files, given a single Pull Request number: - #!ruby - require 'octokit' +``` ruby +require 'octokit' - # !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! - # Instead, set and test environment variables, like below - client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] +# !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! +# Instead, set and test environment variables, like below +client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] - client.pull_request_comments("octocat/Spoon-Knife", 1176).each do |comment| - username = comment[:user][:login] - post_date = comment[:created_at] - content = comment[:body] - path = comment[:path] - position = comment[:position] +client.pull_request_comments("octocat/Spoon-Knife", 1176).each do |comment| + username = comment[:user][:login] + post_date = comment[:created_at] + content = comment[:body] + path = comment[:path] + position = comment[:position] - puts "#{username} made a comment on #{post_date} for the file called #{path}, on line #{position}. It says:\n'#{content}'\n" - end + puts "#{username} made a comment on #{post_date} for the file called #{path}, on line #{position}. It says:\n'#{content}'\n" +end +``` You'll notice that it's incredibly similar to the example above. The difference between this view and the Pull Request comment is the focus of the conversation. @@ -88,20 +89,21 @@ they make use of [the commit comment API][commit comment API]. To retrieve the comments on a commit, you'll want to use the SHA1 of the commit. In other words, you won't use any identifier related to the Pull Request. Here's an example: - #!ruby - require 'octokit' +``` ruby +require 'octokit' - # !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! - # Instead, set and test environment variables, like below - client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] +# !!! DO NOT EVER USE HARD-CODED VALUES IN A REAL APP !!! +# Instead, set and test environment variables, like below +client = Octokit::Client.new :access_token => ENV['MY_PERSONAL_TOKEN'] - client.commit_comments("octocat/Spoon-Knife", "cbc28e7c8caee26febc8c013b0adfb97a4edd96e").each do |comment| - username = comment[:user][:login] - post_date = comment[:created_at] - content = comment[:body] +client.commit_comments("octocat/Spoon-Knife", "cbc28e7c8caee26febc8c013b0adfb97a4edd96e").each do |comment| + username = comment[:user][:login] + post_date = comment[:created_at] + content = comment[:body] - puts "#{username} made a comment on #{post_date}. It says:\n'#{content}'\n" - end + puts "#{username} made a comment on #{post_date}. It says:\n'#{content}'\n" +end +``` Note that this API call will retrieve single line comments, as well as comments made on the entire commit. diff --git a/content/index.md b/content/index.md index 2024c05223..1cf54f6892 100644 --- a/content/index.md +++ b/content/index.md @@ -1,6 +1,7 @@ --- title: GitHub Developer layout: overview +hide_from_search: true ---Get started with one of our guides, or jump straight into the API documentation.
Browse the documentation - +
+ 
 +
+ 
It takes a community to design, build, and ship great software.
Building an application that integrates with GitHub? Register for our Developer Program! The possibilities are endless, and you enjoy the kudos.
Register now + +
+  -
-  -
- 
Awesome! We'd love to have you be part of the program. Here’s how you can spread the word:
- Let us know about your integration -
- Use the Octocat or GitHub logo to advertise that your product works with GitHub +
- Use the Octocat or GitHub logo to identify that your product works with GitHub
- Post a video or a blog on your website about your integration
Ready to join the GitHub Developer Program?
Membership is open to individual developers and companies who have:
-
diff --git a/content/search/search-index.json b/content/search/search-index.json
new file mode 100644
index 0000000000..708851ff81
--- /dev/null
+++ b/content/search/search-index.json
@@ -0,0 +1,26 @@
+<%
+ #build the JSON tree
+ if @config[:audience]
+ @preface = "/enterprise/#{@config[:audience]}"
+ end
+ @output = []
+ @items.select { |item| !item.attributes[:hide_from_search] }.each do |item|
+ next if item[:filename].nil? || !item[:filename].end_with?('.md')
+ @path = item[:filename].split('/')[1..-1].join('/')[0..-4]
+ @path.chomp!('/index') if @path.end_with?('/index')
+
+ @output.push({
+ :title => "#{clean_for_json(item[:title])}",
+ :url => "#{@preface}/#{@path}/",
+ :body => "#{clean_for_json(item.compiled_content)}"
+ })
+ end
+%>
+<%=
+ #output the generated tree
+ if ENV['RACK_ENV'] == "production"
+ JSON.generate(@output.sort{|a, b| a[:title] <=> b[:title]})
+ else
+ JSON.pretty_generate(@output.sort{|a, b| a[:title] <=> b[:title]})
+ end
+%>
diff --git a/content/v3.md b/content/v3.md
index c6eb7492d3..a387737d67 100644
--- a/content/v3.md
+++ b/content/v3.md
@@ -4,10 +4,9 @@ title: GitHub API v3
# Overview
-This describes the resources that make up the official GitHub API v3. If you have any problems or requests please contact
+This describes the resources that make up the official {{ site.data.variables.product.product_name }} API v3. If you have any problems or requests please contact
[support][].
-* TOC
{:toc}
## Current Version
@@ -19,30 +18,29 @@ We encourage you to [explicitly request this version via the `Accept` header](/v
## Schema
-All API access is over HTTPS, and accessed from the `api.github.com`
-domain (or through `yourdomain.com/api/v3/` for enterprise). All data is
+All API access is over HTTPS, and accessed from the `{{ site.data.variables.product.api_url_code }}`. All data is
sent and received as JSON.
-
-$ curl -i https://api.github.com/users/octocat/orgs - -HTTP/1.1 200 OK -Server: nginx -Date: Fri, 12 Oct 2012 23:33:14 GMT -Content-Type: application/json; charset=utf-8 -Connection: keep-alive -Status: 200 OK -ETag: "a00049ba79152d03380c34652f2cb612" -X-GitHub-Media-Type: github.v3 -X-RateLimit-Limit: 5000 -X-RateLimit-Remaining: 4987 -X-RateLimit-Reset: 1350085394 -Content-Length: 5 -Cache-Control: max-age=0, private, must-revalidate -X-Content-Type-Options: nosniff - -[] -+``` command-line +$ curl -i {{ site.data.variables.product.api_url_pre }}/users/octocat/orgs + +> HTTP/1.1 200 OK +> Server: nginx +> Date: Fri, 12 Oct 2012 23:33:14 GMT +> Content-Type: application/json; charset=utf-8 +> Connection: keep-alive +> Status: 200 OK +> ETag: "a00049ba79152d03380c34652f2cb612" +> X-GitHub-Media-Type: github.v3 +{% if page.version == 'dotcom' %} +> X-RateLimit-Limit: 5000 +> X-RateLimit-Remaining: 4987 +> X-RateLimit-Reset: 1350085394 +{% endif %} +> Content-Length: 5 +> Cache-Control: max-age=0, private, must-revalidate +> X-Content-Type-Options: nosniff +``` Blank fields are included as `null` instead of being omitted. @@ -86,9 +84,9 @@ Many API methods take optional parameters. For GET requests, any parameters not specified as a segment in the path can be passed as an HTTP query string parameter: -
-$ curl -i "https://api.github.com/repos/vmg/redcarpet/issues?state=closed" -+``` command-line +$ curl -i "{{ site.data.variables.product.api_url_pre }}/repos/vmg/redcarpet/issues?state=closed" +``` In this example, the 'vmg' and 'redcarpet' values are provided for the `:owner` and `:repo` parameters in the path while `:state` is passed in the query @@ -97,11 +95,31 @@ string. For POST, PATCH, PUT, and DELETE requests, parameters not included in the URL should be encoded as JSON with a Content-Type of 'application/json': -
-$ curl -i -u username -d '{"scopes":["public_repo"]}' https://api.github.com/authorizations
-
+``` command-line
+$ curl -i -u username -d '{"scopes":["public_repo"]}' {{ site.data.variables.product.api_url_pre }}/authorizations
+```
+## Root Endpoint
+You can issue a `GET` request to the root endpoint to get all the endpoint categories that the API supports:
+
+``` command-line
+$ curl {{ site.data.variables.product.api_url_pre }}
+```
+
+{% if page.version != 'dotcom' %}
+
+{{#tip}}
+
+**Tip:** For GitHub Enterprise, [as with all other endpoints](https://developer.github.com/v3/enterprise/#endpoint-urls), you'll need to pass in your GitHub Enterprise endpoint as the hostname, *as well as your username and password*:
+
+``` command-line
+$ curl https://hostname/api/v3/ -u username:password
+```
+
+{{/tip}}
+
+{% endif %}
## Client Errors
@@ -121,7 +139,7 @@ receive request bodies:
HTTP/1.1 400 Bad Request
Content-Length: 40
- {"message":"Body should be a JSON Hash"}
+ {"message":"Body should be a JSON object"}
3. Sending invalid fields will result in a `422 Unprocessable Entity`
response.
@@ -153,7 +171,7 @@ Error Name | Description
`invalid` | This means the formatting of a field is invalid. The documentation for that resource should be able to give you more specific information.
`already_exists` | This means another resource has the same value as this field. This can happen in resources that must have some unique key (such as Label names).
-If resources have custom validation errors, they will be documented with the resource.
+Resources may also send custom validation errors (where `code` is `custom`). Custom errors will always have a `message` field describing the error, and most errors will also include a `documentation_url` field pointing to some content that might help you resolve the error.
## HTTP Redirects
@@ -179,35 +197,35 @@ Verb | Description
-----|-----------
`HEAD` | Can be issued against any resource to get just the HTTP header info.
`GET` | Used for retrieving resources.
-`POST` | Used for creating resources, or performing custom actions (such as merging a pull request).
+`POST` | Used for creating resources.
`PATCH` | Used for updating resources with partial JSON data. For instance, an Issue resource has `title` and `body` attributes. A PATCH request may accept one or more of the attributes to update the resource. PATCH is a relatively new and uncommon HTTP verb, so resource endpoints also accept `POST` requests.
`PUT` | Used for replacing resources or collections. For `PUT` requests with no `body` attribute, be sure to set the `Content-Length` header to zero.
`DELETE` |Used for deleting resources.
## Authentication
-There are three ways to authenticate through GitHub API v3. Requests that
+There are three ways to authenticate through {{ site.data.variables.product.product_name }} API v3. Requests that
require authentication will return `404 Not Found`, instead of
`403 Forbidden`, in some places. This is to prevent the accidental leakage
of private repositories to unauthorized users.
### Basic Authentication
--$ curl -u "username" https://api.github.com -+``` command-line +$ curl -u "username" {{ site.data.variables.product.api_url_pre }} +``` ### OAuth2 Token (sent in a header) -
-$ curl -H "Authorization: token OAUTH-TOKEN" https://api.github.com -+``` command-line +$ curl -H "Authorization: token OAUTH-TOKEN" {{ site.data.variables.product.api_url_pre }} +``` ### OAuth2 Token (sent as a parameter) -
-$ curl https://api.github.com/?access_token=OAUTH-TOKEN -+``` command-line +$ curl {{ site.data.variables.product.api_url_pre }}/?access_token=OAUTH-TOKEN +``` Read [more about OAuth2](/v3/oauth/). Note that OAuth2 tokens can be [acquired programmatically](/v3/oauth_authorizations/#create-a-new-authorization), for applications that @@ -215,43 +233,46 @@ are not websites. ### OAuth2 Key/Secret -
-$ curl 'https://api.github.com/users/whatever?client_id=xxxx&client_secret=yyyy' -+``` command-line +$ curl '{{ site.data.variables.product.api_url_pre }}/users/whatever?client_id=xxxx&client_secret=yyyy' +``` This should only be used in server to server scenarios. Don't leak your -OAuth application's client secret to your users. Read [more about -unauthenticated rate limiting](#unauthenticated-rate-limited-requests). +OAuth application's client secret to your users. + +{% if page.version == 'dotcom' %} + +Read [more about unauthenticated rate limiting](#increasing-the-unauthenticated-rate-limit-for-oauth-applications). + +{% endif %} ### Failed login limit Authenticating with invalid credentials will return `401 Unauthorized`: -
-$ curl -i https://api.github.com -u foo:bar
+``` command-line
+$ curl -i {{ site.data.variables.product.api_url_pre }} -u foo:bar
+> HTTP/1.1 401 Unauthorized
-HTTP/1.1 401 Unauthorized
-
-{
- "message": "Bad credentials",
- "documentation_url": "https://developer.github.com/v3"
-}
-
+> {
+> "message": "Bad credentials",
+> "documentation_url": "https://developer.github.com/v3"
+> }
+```
After detecting several requests with invalid credentials within a short period,
the API will temporarily reject all authentication attempts for that user
(including ones with valid credentials) with `403 Forbidden`:
-
-$ curl -i https://api.github.com -u valid_username:valid_password
-
-HTTP/1.1 403 Forbidden
+``` command-line
+$ curl -i {{ site.data.variables.product.api_url_pre }} -u valid_username:valid_password
+> HTTP/1.1 403 Forbidden
-{
- "message": "Maximum number of login attempts exceeded. Please try again later.",
- "documentation_url": "https://developer.github.com/v3"
-}
-
+> {
+> "message": "Maximum number of login attempts exceeded. Please try again later.",
+> "documentation_url": "https://developer.github.com/v3"
+> }
+```
## Hypermedia
@@ -285,9 +306,9 @@ resources, you can also set a custom page size up to 100 with the `?per_page` pa
Note that for technical reasons not all endpoints respect the `?per_page` parameter,
see [events](https://developer.github.com/v3/activity/events/) for example.
--$ curl 'https://api.github.com/user/repos?page=2&per_page=100' -+``` command-line +$ curl '{{ site.data.variables.product.api_url_pre }}/user/repos?page=2&per_page=100' +``` Note that page numbering is 1-based and that omitting the `?page` parameter will return the first page. @@ -308,35 +329,39 @@ SHA1 and not on page number. _Linebreak is included for readability._ +This `Link` response header contains one or more [Hypermedia](/v3/#hypermedia) link relations, some of which may require expansion as [URI templates](http://tools.ietf.org/html/rfc6570). + The possible `rel` values are: Name | Description -----------|-----------| -`next` |Shows the URL of the immediate next page of results. -`last` |Shows the URL of the last page of results. -`first` |Shows the URL of the first page of results. -`prev` |Shows the URL of the immediate previous page of results. +`next` |The link relation for the immediate next page of results. +`last` |The link relation for the last page of results. +`first` |The link relation for the first page of results. +`prev` |The link relation for the immediate previous page of results. + +{% if page.version == 'dotcom' %} ## Rate Limiting For requests using Basic Authentication or OAuth, you can make up to 5,000 requests per hour. For unauthenticated requests, the rate limit allows you to -make up to 60 requests per hour. (The Search API has [custom rate limit -rules](/v3/search/#rate-limit).) +make up to 60 requests per hour. Unauthenticated requests are associated with your IP address, +and not the user making requests. Note that [the Search API has custom rate limit +rules](/v3/search/#rate-limit). You can check the returned HTTP headers of any API request to see your current rate limit status: -
-$ curl -i https://api.github.com/users/whatever - -HTTP/1.1 200 OK -Date: Mon, 01 Jul 2013 17:27:06 GMT -Status: 200 OK -X-RateLimit-Limit: 60 -X-RateLimit-Remaining: 56 -X-RateLimit-Reset: 1372700873 -+``` command-line +$ curl -i {{ site.data.variables.product.api_url_pre }}/users/whatever +> HTTP/1.1 200 OK +> Date: Mon, 01 Jul 2013 17:27:06 GMT +> Status: 200 OK +> X-RateLimit-Limit: 60 +> X-RateLimit-Remaining: 56 +> X-RateLimit-Reset: 1372700873 +``` The headers tell you everything you need to know about your current rate limit status: @@ -348,46 +373,44 @@ Header Name | Description If you need the time in a different format, any modern programming language can get the job done. For example, if you open up the console on your web browser, you can easily get the reset time as a JavaScript Date object. -
+``` javascript
new Date(1372700873 * 1000)
// => Mon Jul 01 2013 13:47:53 GMT-0400 (EDT)
-
-HTTP/1.1 403 Forbidden
-Date: Tue, 20 Aug 2013 14:50:41 GMT
-Status: 403 Forbidden
-X-RateLimit-Limit: 60
-X-RateLimit-Remaining: 0
-X-RateLimit-Reset: 1377013266
+``` command-line
+> HTTP/1.1 403 Forbidden
+> Date: Tue, 20 Aug 2013 14:50:41 GMT
+> Status: 403 Forbidden
+> X-RateLimit-Limit: 60
+> X-RateLimit-Remaining: 0
+> X-RateLimit-Reset: 1377013266
-{
- "message": "API rate limit exceeded. See https://developer.github.com/v3/#rate-limiting for details."
-}
-
+> {
+> "message": "API rate limit exceeded for xxx.xxx.xxx.xxx. (But here's the good news: Authenticated requests get a higher rate limit. Check out the documentation for more details.)",
+> "documentation_url": "https://developer.github.com/v3/#rate-limiting"
+> }
+```
You can also [check your rate limit status](/v3/rate_limit) without incurring an
API hit.
-### Unauthenticated rate limited requests - -If you need to make unauthenticated calls but need to use a higher rate limit -associated with your OAuth application, you can send over your client ID and -secret in the query string. +### Increasing the unauthenticated rate limit for OAuth applications -
-$ curl -i 'https://api.github.com/users/whatever?client_id=xxxx&client_secret=yyyy' +If your OAuth application needs to make unauthenticated calls with a higher rate limit, you can pass your app's client ID and secret as part of the query string. -HTTP/1.1 200 OK -Date: Mon, 01 Jul 2013 17:27:06 GMT -Status: 200 OK -X-RateLimit-Limit: 5000 -X-RateLimit-Remaining: 4966 -X-RateLimit-Reset: 1372700873 -+``` command-line +$ curl -i '{{ site.data.variables.product.api_url_pre }}/users/whatever?client_id=xxxx&client_secret=yyyy' +> HTTP/1.1 200 OK +> Date: Mon, 01 Jul 2013 17:27:06 GMT +> Status: 200 OK +> X-RateLimit-Limit: 5000 +> X-RateLimit-Remaining: 4966 +> X-RateLimit-Reset: 1372700873 +``` This method should only be used for server-to-server calls. You should never share your client secret with anyone or include it in client-side browser code. @@ -402,133 +425,179 @@ If you're using conditional requests and still exceeding your rate limit, please [contact us][support] to request a higher rate limit for your OAuth application. +### Abuse Rate Limits + +To protect the quality of service from GitHub, additional rate limits may apply to some actions. +For example, rapidly creating content, polling aggressively instead of using webhooks, +making API calls with a high concurrency, or repeatedly requesting data that is computationally expensive +may result in abuse rate limiting. + +It is not intended for this rate limit to interfere with any legitimate use of +the API. Your normal [rate limits](/v3/#rate-limiting) should be the only +limit you target. Please [contact support][abuse-support] if your use is affected by +this rate limit. To ensure you're acting as a good API citizen, check out our +[Best Practices guidelines](/guides/best-practices-for-integrators/). + +If your application triggers this rate limit, you'll receive an informative +response: + +``` command-line +> HTTP/1.1 403 Forbidden +> Content-Type: application/json; charset=utf-8 +> Connection: close + +> { +> "message": "You have triggered an abuse detection mechanism and have been temporarily blocked from content creation. Please retry your request again later.", +> "documentation_url": "https://developer.github.com/v3#abuse-rate-limits" +> } +``` + +{% endif %} + ## User Agent Required All API requests MUST include a valid `User-Agent` header. Requests with no `User-Agent` -header will be rejected. We request that you use your GitHub username, or the name of your +header will be rejected. We request that you use your {{ site.data.variables.product.product_name }} username, or the name of your application, for the `User-Agent` header value. This allows us to contact you if there are problems. Here's an example: -
+``` command-line User-Agent: Awesome-Octocat-App -+``` If you provide an invalid `User-Agent` header, you will receive a `403 Forbidden` response: -
-$ curl -iH 'User-Agent: ' https://api.github.com/meta
-HTTP/1.0 403 Forbidden
-Connection: close
-Content-Type: text/html
+``` command-line
+$ curl -iH 'User-Agent: ' {{ site.data.variables.product.api_url_pre }}/meta
+> HTTP/1.0 403 Forbidden
+> Connection: close
+> Content-Type: text/html
-Request forbidden by administrative rules.
-Please make sure your request has a User-Agent header.
-Check https://developer.github.com for other possible causes.
-
+> Request forbidden by administrative rules.
+> Please make sure your request has a User-Agent header.
+> Check https://developer.github.com for other possible causes.
+```
## Conditional requests
Most responses return an `ETag` header. Many responses also return a `Last-Modified` header. You can use the values
of these headers to make subsequent requests to those resources using the
`If-None-Match` and `If-Modified-Since` headers, respectively. If the resource
-has not changed, the server will return a `304 Not Modified`. Also note: making
-a conditional request and receiving a 304 response does not count against your
-[Rate Limit](#rate-limiting), so we encourage you to use it whenever possible.
-
--$ curl -i https://api.github.com/user -HTTP/1.1 200 OK -Cache-Control: private, max-age=60 -ETag: "644b5b0155e6404a9cc4bd9d8b1ae730" -Last-Modified: Thu, 05 Jul 2012 15:31:30 GMT -Status: 200 OK -Vary: Accept, Authorization, Cookie -X-RateLimit-Limit: 5000 -X-RateLimit-Remaining: 4996 -X-RateLimit-Reset: 1372700873 - -$ curl -i https://api.github.com/user -H 'If-None-Match: "644b5b0155e6404a9cc4bd9d8b1ae730"' -HTTP/1.1 304 Not Modified -Cache-Control: private, max-age=60 -ETag: "644b5b0155e6404a9cc4bd9d8b1ae730" -Last-Modified: Thu, 05 Jul 2012 15:31:30 GMT -Status: 304 Not Modified -Vary: Accept, Authorization, Cookie -X-RateLimit-Limit: 5000 -X-RateLimit-Remaining: 4996 -X-RateLimit-Reset: 1372700873 - -$ curl -i https://api.github.com/user -H "If-Modified-Since: Thu, 05 Jul 2012 15:31:30 GMT" -HTTP/1.1 304 Not Modified -Cache-Control: private, max-age=60 -Last-Modified: Thu, 05 Jul 2012 15:31:30 GMT -Status: 304 Not Modified -Vary: Accept, Authorization, Cookie -X-RateLimit-Limit: 5000 -X-RateLimit-Remaining: 4996 -X-RateLimit-Reset: 1372700873 -+has not changed, the server will return a `304 Not Modified`. + +{% if page.version == 'dotcom' %} + +{{#tip}} + +**Note**: Making a conditional request and receiving a 304 response does not +count against your [Rate Limit](#rate-limiting), so we encourage you to use it +whenever possible. + +{{/tip}} + +{% endif %} + +``` command-line +$ curl -i {{ site.data.variables.product.api_url_pre }}/user +> HTTP/1.1 200 OK +> Cache-Control: private, max-age=60 +> ETag: "644b5b0155e6404a9cc4bd9d8b1ae730" +> Last-Modified: Thu, 05 Jul 2012 15:31:30 GMT +> Status: 200 OK +> Vary: Accept, Authorization, Cookie +{% if page.version == 'dotcom' %} +> X-RateLimit-Limit: 5000 +> X-RateLimit-Remaining: 4996 +> X-RateLimit-Reset: 1372700873 +{% endif %} + +$ curl -i {{ site.data.variables.product.api_url_pre }}/user -H 'If-None-Match: "644b5b0155e6404a9cc4bd9d8b1ae730"' +> HTTP/1.1 304 Not Modified +> Cache-Control: private, max-age=60 +> ETag: "644b5b0155e6404a9cc4bd9d8b1ae730" +> Last-Modified: Thu, 05 Jul 2012 15:31:30 GMT +> Status: 304 Not Modified +> Vary: Accept, Authorization, Cookie +{% if page.version == 'dotcom' %} +> X-RateLimit-Limit: 5000 +> X-RateLimit-Remaining: 4996 +> X-RateLimit-Reset: 1372700873 +{% endif %} + +$ curl -i {{ site.data.variables.product.api_url_pre }}/user -H "If-Modified-Since: Thu, 05 Jul 2012 15:31:30 GMT" +> HTTP/1.1 304 Not Modified +> Cache-Control: private, max-age=60 +> Last-Modified: Thu, 05 Jul 2012 15:31:30 GMT +> Status: 304 Not Modified +> Vary: Accept, Authorization, Cookie +{% if page.version == 'dotcom' %} +> X-RateLimit-Limit: 5000 +> X-RateLimit-Remaining: 4996 +> X-RateLimit-Reset: 1372700873 +{% endif %} +``` ## Cross Origin Resource Sharing -The API supports Cross Origin Resource Sharing (CORS) for AJAX requests. -you can read the [CORS W3C working draft](http://www.w3.org/TR/cors), or +The API supports Cross Origin Resource Sharing (CORS) for AJAX requests from +any origin. +You can read the [CORS W3C Recommendation](http://www.w3.org/TR/cors/), or [this intro](http://code.google.com/p/html5security/wiki/CrossOriginRequestSecurity) from the HTML 5 Security Guide. Here's a sample request sent from a browser hitting `http://example.com`: - $ curl -i https://api.github.com -H "Origin: http://example.com" - HTTP/1.1 302 Found - -Any domain that is registered as an OAuth Application is accepted. -Here's a sample request for a browser hitting [Travis CI](http://travis-ci.org/): - - $ curl -i https://api.github.com -H "Origin: http://travis-ci.org" - HTTP/1.1 302 Found - Access-Control-Allow-Origin: * - Access-Control-Expose-Headers: ETag, Link, X-RateLimit-Limit, X-RateLimit-Remaining, X-RateLimit-Reset, X-OAuth-Scopes, X-Accepted-OAuth-Scopes - Access-Control-Allow-Credentials: true +``` command-line +$ curl -i {{ site.data.variables.product.api_url_pre }} -H "Origin: http://example.com" +HTTP/1.1 302 Found +Access-Control-Allow-Origin: * +Access-Control-Expose-Headers: ETag, Link, X-GitHub-OTP, {% if page.version == 'dotcom' %}X-RateLimit-Limit, X-RateLimit-Remaining, X-RateLimit-Reset,{% endif %} X-OAuth-Scopes, X-Accepted-OAuth-Scopes, X-Poll-Interval +Access-Control-Allow-Credentials: true +``` This is what the CORS preflight request looks like: - $ curl -i https://api.github.com -H "Origin: http://travis-ci.org" -X OPTIONS - HTTP/1.1 204 No Content - Access-Control-Allow-Origin: * - Access-Control-Allow-Headers: Authorization, Content-Type, If-Match, If-Modified-Since, If-None-Match, If-Unmodified-Since, X-Requested-With - Access-Control-Allow-Methods: GET, POST, PATCH, PUT, DELETE - Access-Control-Expose-Headers: ETag, Link, X-RateLimit-Limit, X-RateLimit-Remaining, X-RateLimit-Reset, X-OAuth-Scopes, X-Accepted-OAuth-Scopes - Access-Control-Max-Age: 86400 - Access-Control-Allow-Credentials: true +``` command-line +$ curl -i {{ site.data.variables.product.api_url_pre }} -H "Origin: http://example.com" -X OPTIONS +HTTP/1.1 204 No Content +Access-Control-Allow-Origin: * +Access-Control-Allow-Headers: Authorization, Content-Type, If-Match, If-Modified-Since, If-None-Match, If-Unmodified-Since, X-GitHub-OTP, X-Requested-With +Access-Control-Allow-Methods: GET, POST, PATCH, PUT, DELETE +Access-Control-Expose-Headers: ETag, Link, X-GitHub-OTP, {% if page.version == 'dotcom' %}X-RateLimit-Limit, X-RateLimit-Remaining, X-RateLimit-Reset,{% endif %} X-OAuth-Scopes, X-Accepted-OAuth-Scopes, X-Poll-Interval +Access-Control-Max-Age: 86400 +Access-Control-Allow-Credentials: true +``` ## JSON-P Callbacks You can send a `?callback` parameter to any GET call to have the results wrapped in a JSON function. This is typically used when browsers want -to embed GitHub content in web pages by getting around cross domain +to embed {{ site.data.variables.product.product_name }} content in web pages by getting around cross domain issues. The response includes the same data output as the regular API, plus the relevant HTTP Header information. -
+``` command-line
$ curl https://api.github.com?callback=foo
-/**/foo({
- "meta": {
- "status": 200,
- "X-RateLimit-Limit": "5000",
- "X-RateLimit-Remaining": "4966",
- "X-RateLimit-Reset": "1372700873",
- "Link": [ // pagination headers and other links
- ["https://api.github.com?page=2", {"rel": "next"}]
- ]
- },
- "data": {
- // the data
- }
-})
-
+> /**/foo({
+> "meta": {
+> "status": 200,
+{% if page.version == 'dotcom' %}
+> "X-RateLimit-Limit": "5000",
+> "X-RateLimit-Remaining": "4966",
+> "X-RateLimit-Reset": "1372700873",
+{% endif %}
+> "Link": [ // pagination headers and other links
+> ["https://api.github.com?page=2", {"rel": "next"}]
+> ]
+> },
+> "data": {
+> // the data
+> }
+> })
+```
You can write a JavaScript handler to process the callback. Here's a minimal example you can try out:
@@ -588,7 +657,9 @@ how these timestamps can be specified.
It is possible to supply a `Time-Zone` header which defines a timezone according
to the [list of names from the Olson database](https://en.wikipedia.org/wiki/List_of_tz_database_time_zones).
- $ curl -H "Time-Zone: Europe/Amsterdam" -X POST https://api.github.com/repos/github/linguist/contents/new_file.md
+``` command-line
+$ curl -H "Time-Zone: Europe/Amsterdam" -X POST {{ site.data.variables.product.api_url_pre }}/repos/github/linguist/contents/new_file.md
+```
This means that we generate a timestamp for the moment your API call is made in
the timezone this header defines. For example, the [Contents API](/v3/repos/contents/)
@@ -599,8 +670,8 @@ that current timestamp.
#### Using the last known timezone for the user
If no `Time-Zone` header is specified and you make an authenticated call to the
-API, we use the last known timezone for the authenticated user. The last know
-timezone is updated whenever you browse the GitHub.com website.
+API, we use the last known timezone for the authenticated user. The last known
+timezone is updated whenever you browse the {{ site.data.variables.product.product_name }} website.
#### UTC
@@ -608,4 +679,5 @@ If the steps above don't result in any information, we use UTC as the timezone
to create the git commit.
[support]: https://github.com/contact?form[subject]=APIv3
+[abuse-support]: https://github.com/contact?form[subject]=API+Abuse+Rate+Limits
[pagination-guide]: /guides/traversing-with-pagination
diff --git a/content/v3/activity.md b/content/v3/activity.md
index 79a516815b..cdac1ca8a7 100644
--- a/content/v3/activity.md
+++ b/content/v3/activity.md
@@ -1,11 +1,20 @@
---
-title: Activity | GitHub API
+title: Activity
---
# Activity
-Serving up the 'social' in Social Coding™, the Activity APIs provide access to
+Serving up the 'social' in Social Coding, the Activity APIs provide access to
notifications, subscriptions, and timelines.
+## [Events][]
+
+The [Events API][Events] is a read-only interface to all the [event
+types][types] that power the various activity streams on {{ site.data.variables.product.product_name }}.
+
+## [Feeds][]
+
+List of [Atom feeds][Feeds] available for the authenticated user.
+
## [Notifications][]
Notifications of new comments are delivered to users. [The Notifications
@@ -22,18 +31,9 @@ have no effect on notifications or the activity feed.
[Watching a Repository][Watching] registers the user to receive notifications on new
discussions, as well as events in the user's activity feed.
-## [Events][]
-
-The [Events API][Events] is a read-only interface to all the [event
-types][types] that power the various activity streams on GitHub.
-
-## [Feeds][]
-
-List of [Atom feeds][Feeds] available for the authenticating user.
-
-[Notifications]: /v3/activity/notifications/
-[Starring]: /v3/activity/starring/
-[Watching]: /v3/activity/watching/
[Events]: /v3/activity/events/
[types]: /v3/activity/events/types/
[Feeds]: /v3/activity/feeds/
+[Notifications]: /v3/activity/notifications/
+[Starring]: /v3/activity/starring/
+[Watching]: /v3/activity/watching/
diff --git a/content/v3/activity/events.md b/content/v3/activity/events.md
index 3ce235c663..5541291631 100644
--- a/content/v3/activity/events.md
+++ b/content/v3/activity/events.md
@@ -1,13 +1,12 @@
---
-title: Events | GitHub API
+title: Events
---
# Events
-This is a read-only API to the GitHub events. These events power the
+This is a read-only API to the {{ site.data.variables.product.product_name }} events. These events power the
various activity streams on the site.
-* TOC
{:toc}
Events are optimized for polling with the "ETag" header. If no new events have
@@ -16,24 +15,30 @@ rate limit will be untouched. There is also an "X-Poll-Interval" header that
specifies how often (in seconds) you are allowed to poll. In times of high
server load, the time may increase. Please obey the header.
- $ curl -I https://api.github.com/users/tater/events
- HTTP/1.1 200 OK
- X-Poll-Interval: 60
- ETag: "a18c3bded88eb5dbb5c849a489412bf3"
+``` command-line
+$ curl -I {{ site.data.variables.product.api_url_pre }}/users/tater/events
+> HTTP/1.1 200 OK
+> X-Poll-Interval: 60
+> ETag: "a18c3bded88eb5dbb5c849a489412bf3"
- # The quotes around the ETag value are important
- $ curl -I https://api.github.com/users/tater/events \
- -H 'If-None-Match: "a18c3bded88eb5dbb5c849a489412bf3"'
- HTTP/1.1 304 Not Modified
- X-Poll-Interval: 60
+# The quotes around the ETag value are important
+$ curl -I {{ site.data.variables.product.api_url_pre }}/users/tater/events \
+$ -H 'If-None-Match: "a18c3bded88eb5dbb5c849a489412bf3"'
+> HTTP/1.1 304 Not Modified
+> X-Poll-Interval: 60
+```
Events support [pagination](/v3/#pagination),
however the `per_page` option is unsupported. The fixed page size is 30 items.
Fetching up to ten pages is supported, for a total of 300 events.
+Only events created within the past 90 days will be included in timelines. Events
+older than 90 days will not be included (even if the total number of events
+in the timeline is less than 300).
+
All Events have the same response format:
-<%= headers 200, :pagination => { :next => 'https://api.github.com/resource?page=2' } %>
+<%= headers 200, :pagination => default_pagination_rels %>
<%= json(:event) { |h| [h] } %>
## List public events
@@ -65,26 +70,26 @@ These are events that you've received by watching repos and following
users. If you are authenticated as the given user, you will see private
events. Otherwise, you'll only see public events.
- GET /users/:user/received_events
+ GET /users/:username/received_events
## List public events that a user has received
- GET /users/:user/received_events/public
+ GET /users/:username/received_events/public
## List events performed by a user
If you are authenticated as the given user, you will see your private
events. Otherwise, you'll only see public events.
- GET /users/:user/events
+ GET /users/:username/events
## List public events performed by a user
- GET /users/:user/events/public
+ GET /users/:username/events/public
## List events for an organization
This is the user's organization dashboard. You must be authenticated as
the user to view this.
- GET /users/:user/events/orgs/:org
+ GET /users/:username/events/orgs/:org
diff --git a/content/v3/activity/events/types.md b/content/v3/activity/events/types.md
index f9d5e81107..9504e2de89 100644
--- a/content/v3/activity/events/types.md
+++ b/content/v3/activity/events/types.md
@@ -1,48 +1,47 @@
---
-title: Event Types | GitHub API
+title: Event Types & Payloads
---
-# Event Types
+# Event Types & Payloads
Each event has a similar JSON schema, but a unique `payload` object that is
-determined by its event type. [Repository hook](/v3/repos/hooks/) names relate to event types, and will have the exact same payload. The only exception to this is the `push` hook, which has a larger, more detailed payload.
+determined by its event type.
-This describes just the payload of an event. A full event will also
-show the user that performed the event (actor), the repository, and the
-organization (if applicable).
+Event names are used by [repository webhooks](/v3/repos/hooks/) to specify
+which events the webhook should receive. The included payloads below are from webhook deliveries but
+match events returned by the [Events API](/v3/activity/events/) (except where noted). The Events API uses the CamelCased name (e.g. `CommitCommentEvent`) in the `type` field of an event object and does not include the `repository` or `sender` fields in the event payload object.
-Note that some of these events may not be rendered in timelines.
-They're only created for various internal and repository hooks.
-* TOC
+**Note:** Some of these events may not be rendered in timelines, they're only
+created for various internal and webhook purposes.
+
{:toc}
## CommitCommentEvent
Triggered when a [commit comment](/v3/repos/comments/#list-commit-comments-for-a-repository) is created.
-### Hook name
-
-`commit_comment`
-
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
`comment`|`object` | The [comment](/v3/repos/comments/#list-commit-comments-for-a-repository) itself.
+### Webhook event name
-## CreateEvent
+`commit_comment`
-Represents a created repository, branch, or tag.
+### Webhook payload example
-Note: webhooks will not receive this event for created repositories.
+<%= webhook_payload "commit_comment" %>
-### Hook name
+## CreateEvent
-`create`
+Represents a created repository, branch, or tag.
-### Payload
+Note: webhooks will not receive this event for created repositories. Additionally, webhooks will not receive this event for tags if more than three tags are pushed at once.
+
+### Events API payload
Key | Type | Description
----|------|-------------
@@ -51,63 +50,84 @@ Key | Type | Description
`master_branch`|`string` | The name of the repository's default branch (usually `master`).
`description`|`string` | The repository's current description.
+### Webhook event name
+
+`create`
+
+### Webhook payload example
+
+<%= webhook_payload "create" %>
## DeleteEvent
Represents a [deleted branch or tag](/v3/git/refs/#delete-a-reference).
-### Hook name
+Note: webhooks will not receive this event for tags if more than three tags are deleted at once.
-`delete`
-
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
`ref_type`|`string` | The object that was deleted. Can be "branch" or "tag".
`ref`|`string` | The full git ref.
-## DeploymentEvent
+### Webhook event name
-Represents a [deployment](/v3/repos/deployments/#list-deployments).
+`delete`
-Events of this type are not visible in timelines, they are only used to trigger hooks.
+### Webhook payload example
-### Hook name
+<%= webhook_payload "delete" %>
-`deployment`
+## DeploymentEvent
+
+Represents a [deployment](/v3/repos/deployments/#list-deployments).
+
+Events of this type are not visible in timelines. These events are only used to trigger hooks.
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
-`sha` |`string` | The commit SHA for which this deployment was created.
-`name` |`string` | Name of repository for this deployment, formatted as `:owner/:repo`.
-`payload` |`string` | The optional extra information for this deployment.
-`description`|`string` | The optional human-readable description added to the deployment.
+`deployment` |`object` | The [deployment](/v3/repos/deployments/#list-deployments).
+`deployment`[`"sha"`] |`string` | The commit SHA for which this deployment was created.
+`deployment`[`"payload"`] |`string` | The optional extra information for this deployment.
+`deployment`[`"environment"`] |`string` | The optional environment to deploy to. Default: `"production"`
+`deployment`[`"description"`] |`string` | The optional human-readable description added to the deployment.
+`repository` |`object` | The [repository](/v3/repos/) for this deployment.
+### Webhook event name
-## DeploymentStatusEvent
+`deployment`
-Represents a [deployment status](/v3/repos/deployments/#list-deployment-statuses).
+### Webhook payload example
-Events of this type are not visible in timelines, they are only used to trigger hooks.
+<%= webhook_payload "deployment" %>
-### Hook name
+## DeploymentStatusEvent
-`deployment_status`
+Represents a [deployment status](/v3/repos/deployments/#list-deployment-statuses).
+
+Events of this type are not visible in timelines. These events are only used to trigger hooks.
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
-`sha` |`string` | The commit SHA for the associated deployment.
-`name` |`string` | Name of repository for the associated deployment, formatted as `:owner/:repo`.
-`state` |`string` | The new state. Can be `pending`, `success`, `failure`, or `error`.
-`payload` |`string` | The optional extra information for the associated deployment.
-`target_url` |`string` | The optional link added to the status.
-`description`|`string` | The optional human-readable description added to the status.
+`deployment_status` |`object` | The [deployment status](/v3/repos/deployments/#list-deployment-statuses).
+`deployment_status["state"]` |`string` | The new state. Can be `pending`, `success`, `failure`, or `error`.
+`deployment_status["target_url"]` |`string` | The optional link added to the status.
+`deployment_status["description"]`|`string` | The optional human-readable description added to the status.
+`deployment` |`object` | The [deployment](/v3/repos/deployments/#list-deployments) that this status is associated with.
+`repository` |`object` | The [repository](/v3/repos/) for this deployment.
+
+### Webhook event name
+
+`deployment_status`
+
+### Webhook payload example
+<%= webhook_payload "deployment_status" %>
## DownloadEvent
@@ -115,48 +135,49 @@ Triggered when a new [download](/v3/repos/downloads/) is created.
Events of this type are **no longer created**, but it's possible that they exist in timelines of some users.
-### Hook name
-
-`download`
-
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
`download`|`object` | The [download](/v3/repos/downloads/) that was just created.
+### Webhook event name
+
+`download`
## FollowEvent
Triggered when a user [follows another user](/v3/users/followers/#follow-a-user).
-Events of this type are not visible in timelines, they are only used to trigger hooks.
-
-### Hook name
-
-`follow`
+Events of this type are **no longer created**, but it's possible that they exist in timelines of some users.
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
`target`|`object` | The [user](/v3/users) that was just followed.
+### Webhook event name
+
+`follow`
## ForkEvent
Triggered when a user [forks a repository](/v3/repos/forks/#create-a-fork).
-### Hook name
-
-`fork`
-
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
`forkee`|`object` | The created [repository](/v3/repos/).
+### Webhook event name
+
+`fork`
+
+### Webhook payload example
+
+<%= webhook_payload "fork" %>
## ForkApplyEvent
@@ -164,11 +185,7 @@ Triggered when a patch is applied in the Fork Queue.
Events of this type are **no longer created**, but it's possible that they exist in timelines of some users.
-### Hook name
-
-`fork_apply`
-
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
@@ -176,6 +193,9 @@ Key | Type | Description
`before`|`string` | SHA of the repository state before the patch.
`after`|`string` | SHA of the repository state after the patch.
+### Webhook event name
+
+`fork_apply`
## GistEvent
@@ -183,27 +203,22 @@ Triggered when a [Gist](/v3/gists/) is created or updated.
Events of this type are **no longer created**, but it's possible that they exist in timelines of some users.
-### Hook name
-
-`gist`
-
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
`action`|`string` | The action that was performed. Can be "create" or "update"
`gist`|`object` | The [gist](/v3/gists/) itself.
+### Webhook event name
+
+`gist`
## GollumEvent
Triggered when a Wiki page is created or updated.
-### Hook name
-
-`gollum`
-
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
@@ -214,55 +229,105 @@ Key | Type | Description
`pages[][sha]`|`string` | The latest commit SHA of the page.
`pages[][html_url]`|`string` | Points to the HTML wiki page.
+### Webhook event name
-## IssueCommentEvent
+`gollum`
-Triggered when an [issue comment](/v3/issues/comments/) is created.
+### Webhook payload example
-### Hook name
+<%= webhook_payload "gollum" %>
-`issue_comment`
+## IssueCommentEvent
+
+{% if page.version == 'dotcom' or page.version > 2.6 %}
+Triggered when an [issue comment](/v3/issues/comments/) is created, edited, or deleted.
+{% else %}
+Triggered when an [issue is commented on](/v3/issues/comments/).
+{% endif %}
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
-`action`|`string` | The action that was performed on the comment. Currently, can only be "created".
+`action`|`string` | The action that was performed on the comment. {% if page.version == 'dotcom' or page.version > 2.6 %}Can be one of "created", "edited", or "deleted".
+`changes`|`object` | The changes to the comment if the action was "edited".
+`changes[body][from]` |`string` | The previous version of the body if the action was "edited".{% else %}Currently, can only be "created".{% endif %}
`issue`|`object` | The [issue](/v3/issues/) the comment belongs to.
`comment`|`object` | The [comment](/v3/issues/comments/) itself.
+### Webhook event name
-## IssuesEvent
+`issue_comment`
-Triggered when an [issue](/v3/issues) is created, closed or reopened.
+### Webhook payload example
-### Hook name
+<%= webhook_payload "issue_comment" %>
-`issues`
+## IssuesEvent
+
+Triggered when an [issue](/v3/issues) is assigned, unassigned, labeled, unlabeled, opened, {% if page.version == 'dotcom' or page.version > 2.6 %}edited, {% endif %}closed, or reopened.
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
-`action`|`string` | The action that was performed. Can be one of "opened", "closed", or "reopened".
-`issue`|`object` | The [issue](/v3/issues) itself.
+`action`|`string` | The action that was performed. Can be one of "assigned", "unassigned", "labeled", "unlabeled", "opened", {% if page.version == 'dotcom' or page.version > 2.6 %}"edited", {% endif %}"closed", or "reopened".
+`issue`|`object` | The [issue](/v3/issues) itself.{% if page.version == 'dotcom' or page.version > 2.6 %}
+`changes`|`object`| The changes to the issue if the action was "edited".
+`changes[title][from]`|`string` | The previous version of the title if the action was "edited".
+`changes[body][from]`|`string` | The previous version of the body if the action was "edited".{% endif %}
+`assignee`|`object` | The optional user who was assigned or unassigned from the issue.
+`label`|`object` | The optional label that was added or removed from the issue.
+### Webhook event name
-## MemberEvent
+`issues`
-Triggered when a user is [added as a collaborator](/v3/repos/collaborators/#add-collaborator) to a repository.
+### Webhook payload example
-### Hook name
+<%= webhook_payload "issues" %>
-`member`
+## MemberEvent
+
+Triggered when a user is [added as a collaborator](/v3/repos/collaborators/#add-user-as-a-collaborator) to a repository.
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
`member`|`object` | The [user](/v3/users/) that was added.
`action`|`string` | The action that was performed. Currently, can only be "added".
+### Webhook event name
+
+`member`
+
+### Webhook payload example
+
+<%= webhook_payload "member" %>
+
+## MembershipEvent
+
+Triggered when a user is added or removed from a team.
+
+Events of this type are not visible in timelines. These events are only used to trigger hooks.
+
+### Events API payload
+
+Key | Type | Description
+----|------|-------------
+`action` |`string` | The action that was performed. Can be "added" or "removed".
+`scope` |`string` | The scope of the membership. Currently, can only be "team".
+`member` |`object` | The [user](/v3/users/) that was added or removed.
+`team` |`object` | The [team](/v3/orgs/teams/) for the membership.
+
+### Webhook event name
+
+`membership`
+
+### Webhook payload example
+
+<%= webhook_payload "membership" %>
## PageBuildEvent
@@ -270,77 +335,105 @@ Represents an attempted build of a GitHub Pages site, whether successful or not.
Triggered on push to a GitHub Pages enabled branch (`gh-pages` for project pages, `master` for user and organization pages).
-### Hook Name
-
-`page_build`
+Events of this type are not visible in timelines. These events are only used to trigger hooks.
-### Payload
+### Events API payload
Key | Type | Description
----|------|------------
`build` | `object` | The [page build](https://developer.github.com/v3/repos/pages/#list-pages-builds) itself.
+### Webhook event name
+
+`page_build`
+
+### Webhook payload example
+
+<%= webhook_payload "page_build" %>
## PublicEvent
-Triggered when a private repository is [open sourced](/v3/repos/#edit). Without a doubt: the best GitHub event.
+Triggered when a private repository is [open sourced](/v3/repos/#edit). Without a doubt: the best {{ site.data.variables.product.product_name }} event.
+
+### Events API payload
-### Hook name
+### Webhook event name
`public`
-### Payload
+### Webhook payload example
-(empty payload)
+<%= webhook_payload "public" %>
## PullRequestEvent
-Triggered when a [pull request](/v3/pulls) is created, closed, reopened or synchronized.
+Triggered when a [pull request](/v3/pulls) is assigned, unassigned, labeled, unlabeled, opened, {% if page.version == 'dotcom' or page.version > 2.6 %}edited, {% endif %}closed, reopened, or synchronized.
-### Hook name
-
-`pull_request`
-
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
-`action`|`string` | The action that was performed. Can be one of "opened", "closed", "synchronize", or "reopened".
-`number`|`integer` | The pull request number.
+`action`|`string` | The action that was performed. Can be one of "assigned", "unassigned", "labeled", "unlabeled", "opened", {% if page.version == 'dotcom' or page.version > 2.6 %}"edited", {% endif %}"closed", or "reopened", or "synchronize". If the action is "closed" and the `merged` key is `false`, the pull request was closed with unmerged commits. If the action is "closed" and the `merged` key is `true`, the pull request was merged.
+`number`|`integer` | The pull request number.{% if page.version == 'dotcom' or page.version > 2.6 %}
+`changes`|`object`| The changes to the comment if the action was "edited".
+`changes[title][from]`|`string` | The previous version of the title if the action was "edited".
+`changes[body][from]`|`string` | The previous version of the body if the action was "edited".{% endif %}
`pull_request`|`object` | The [pull request](/v3/pulls) itself.
+### Webhook event name
-## PullRequestReviewCommentEvent
+`pull_request`
-Triggered when a [comment is created on a portion of the unified diff](/v3/pulls/comments) of a pull request.
+### Webhook payload example
-### Hook name
+<%= webhook_payload "pull_request" %>
-`pull_request_review_comment`
+## PullRequestReviewCommentEvent
+
+{% if page.version == 'dotcom' or page.version > 2.6 %}
+Triggered when a [comment on a Pull Request's unified diff](/v3/pulls/comments) is created, edited, or deleted (in the Files Changed tab).
+{% else %}
+Triggered when a [Pull Request's unified diff is commented on](/v3/pulls/comments) (in the Files Changed tab).
+{% endif %}
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
+`action`|`string` | The action that was performed on the comment. {% if page.version == 'dotcom' or page.version > 2.6 %}Can be one of "created", "edited", or "deleted".
+`changes`|`object`| The changes to the comment if the action was "edited".
+`changes[body][from]`|`string` | The previous version of the body if the action was "edited".{% else %}Currently, can only be "created".{% endif %}
+`pull_request`|`object` | The [pull request](/v3/pulls/) the comment belongs to.
`comment`|`object` | The [comment](/v3/pulls/comments) itself.
+### Webhook event name
+
+`pull_request_review_comment`
+
+### Webhook payload example
+
+<%= webhook_payload "pull_request_review_comment" %>
## PushEvent
-Triggered when a repository branch is pushed to.
+Triggered when a repository branch is pushed to. In addition to branch pushes, webhook [`push` events](/webhooks/#events) are also triggered when repository tags are pushed.
-### Hook name
+{{#tip}}
-`push`
+The Events API `PushEvent` payload is described in the table below. The example payload below that is from a webhook delivery and will differ from the Events API `PushEvent` payload.
-### Payload
+{{/tip}}
+
+### Events API payload
Key | Type | Description
----|------|-------------
-`head`|`string` | The SHA of the HEAD commit on the repository.
-`ref`|`string` | The full Git ref that was pushed. Example: "refs/heads/master"
+`ref`|`string` | The full Git ref that was pushed. Example: `"refs/heads/master"`.
+`head`|`string` | The SHA of the most recent commit on `ref` after the push.
+`before`|`string` | The SHA of the most recent commit on `ref` before the push.
`size`|`integer` | The number of commits in the push.
-`commits`|`array` | An array of commit objects describing the pushed commits. (The array includes a maximum of 20 commits. If necessary, you can use the [Commits API](/v3/repos/commits/) to fetch additional commits.)
+`distinct_size`|`integer` | The number of distinct commits in the push.
+`commits`|`array` | An array of commit objects describing the pushed commits. (The array includes a maximum of 20 commits. If necessary, you can use the [Commits API](/v3/repos/commits/) to fetch additional commits. This limit is applied to timeline events only and isn't applied to webhook deliveries.)
`commits[][sha]`|`string` | The SHA of the commit.
`commits[][message]`|`string` | The commit message.
`commits[][author]`|`object` | The git author of the commit.
@@ -349,33 +442,61 @@ Key | Type | Description
`commits[][url]`|`url` | Points to the commit API resource.
`commits[][distinct]`|`boolean` | Whether this commit is distinct from any that have been pushed before.
+### Webhook event name
+
+`push`
+
+### Webhook payload example
+
+<%= webhook_payload "push" %>
+
## ReleaseEvent
Triggered when a [release](/v3/repos/releases/#get-a-single-release) is published.
-### Hook name
+### Events API payload
+
+Key | Type | Description
+----|------|-------------
+`action`|`string` | The action that was performed. Currently, can only be "published".
+`release`|`object` | The [release](/v3/repos/releases/#get-a-single-release) itself.
+
+### Webhook event name
`release`
-### Payload
+### Webhook payload example
+
+<%= webhook_payload "release" %>
+
+## RepositoryEvent
+
+Triggered when a repository is created{% if page.version == 'dotcom' or page.version > 2.6 %}, deleted, made public, or made private{% endif %}.
+
+Events of this type are not visible in timelines. These events are only used to trigger {% if page.version != 'dotcom' and page.version <= 2.6 %}organization {% endif %}hooks.
+
+### Events API payload
Key | Type | Description
----|------|-------------
-`action`|`string` | The action that was performed. Currently, can only be "published".
-`release`|`object` | The [release](/v3/repos/releases/#get-a-single-release) itself.
+`action` |`string` | The action that was performed. {% if page.version == 'dotcom' or page.version > 2.6 %}This can be one of "created", "deleted", "publicized", or "privatized".{% else %}Currently, can only be "created".{% endif %}
+`repository`|`object` | The [repository](/v3/repos/) itself.
+### Webhook event name
-## StatusEvent
+`repository`
-Triggered when the status of a Git commit changes.
+### Webhook payload example
+
+<%= webhook_payload "repository" %>
-Events of this type are not visible in timelines, they are only used to trigger hooks.
+## StatusEvent
-### Hook name
+Triggered when the status of a Git commit changes.
-`status`
+Events of this type are not visible in timelines. These events are only used to trigger hooks.
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
@@ -385,40 +506,53 @@ Key | Type | Description
`target_url`|`string` | The optional link added to the status.
`branches`|`array` | An array of branch objects containing the status' SHA. Each branch contains the given SHA, but the SHA may or may not be the head of the branch. The array includes a maximum of 10 branches.
+### Webhook event name
-## TeamAddEvent
+`status`
-Triggered when a [user is added to a team](/v3/orgs/teams/#add-team-member) or when a [repository is added to a team](/v3/orgs/teams/#add-team-repo).
+### Webhook payload example
-Note: this event is created in [users' organization timelines](/v3/activity/events/#list-events-for-an-organization).
+<%= webhook_payload "status" %>
-### Hook name
+## TeamAddEvent
-`team_add`
+Triggered when a [repository is added to a team](/v3/orgs/teams/#add-or-update-team-repository).
+
+Events of this type are not visible in timelines. These events are only used to trigger hooks.
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
`team`|`object` | The [team](/v3/orgs/teams/) that was modified. Note: older events may not include this in the payload.
-`user`|`object` | The [user](/v3/users/) that was added to this team.
`repository`|`object` | The [repository](/v3/repos/) that was added to this team.
+### Webhook event name
+
+`team_add`
+
+### Webhook payload example
+
+<%= webhook_payload "team_add" %>
## WatchEvent
The WatchEvent is related to [starring a repository](/v3/activity/starring/#star-a-repository), not [watching](/v3/activity/watching/).
-See [this API blog post](/changes/2012-9-5-watcher-api/) for an explanation.
+See [this API blog post](/changes/2012-09-05-watcher-api/) for an explanation.
The event’s actor is the [user](/v3/users/) who starred a repository, and the
event’s repository is the [repository](/v3/repos/) that was starred.
-### Hook name
-
-`watch`
-
-### Payload
+### Events API payload
Key | Type | Description
----|------|-------------
`action`|`string` | The action that was performed. Currently, can only be `started`.
+
+### Webhook event name
+
+`watch`
+
+### Webhook payload example
+
+<%= webhook_payload "watch" %>
diff --git a/content/v3/activity/feeds.md b/content/v3/activity/feeds.md
index c3b3d5ff2e..11c583fa9b 100644
--- a/content/v3/activity/feeds.md
+++ b/content/v3/activity/feeds.md
@@ -1,26 +1,25 @@
---
-title: Feeds | GitHub API
+title: Feeds
---
# Feeds
-* TOC
{:toc}
## List Feeds
-GitHub provides several timeline resources in [Atom][] format. The Feeds API
-lists all the feeds available to the authenticating user:
+{{ site.data.variables.product.product_name }} provides several timeline resources in [Atom][] format. The Feeds API
+lists all the feeds available to the authenticated user:
-* **Timeline**: The GitHub global public timeline
+* **Timeline**: The {{ site.data.variables.product.product_name }} global public timeline
* **User**: The public timeline for any user, using [URI template][]
* **Current user public**: The public timeline for the authenticated user
* **Current user**: The private timeline for the authenticated user
* **Current user actor**: The private timeline for activity created by the authenticated user
-* **Current user organization**: The private timeline for the authenticated user for a given organization, using [URI template][]
+* **Current user organizations**: The private timeline for the organizations the authenticated user is a member of.
**Note**: Private feeds are only returned when [authenticating via Basic
-Auth][authenticating] since current feed URIs use the older, non revokable auth
+Auth][authenticating] since current feed URIs use the older, non revocable auth
tokens.
GET /feeds
diff --git a/content/v3/activity/notifications.md b/content/v3/activity/notifications.md
index 7ba5af3e87..b09ec649a7 100644
--- a/content/v3/activity/notifications.md
+++ b/content/v3/activity/notifications.md
@@ -1,21 +1,19 @@
---
-title: Notifications | GitHub API
+title: Notifications
---
# Notifications
-* TOC
{:toc}
-GitHub Notifications are powered by [watched repositories](/v3/activity/watching/).
-Users receive notifications for discussions in repositories they watch
+Users receive notifications for conversations in repositories they watch
including:
* Issues and their comments
* Pull Requests and their comments
* Comments on any commits
-Notifications are also sent for discussions in unwatched repositories when the
+Notifications are also sent for conversations in unwatched repositories when the
user is involved including:
* **@mentions**
@@ -37,17 +35,19 @@ leaving your current rate limit untouched. There is an "X-Poll-Interval"
header that specifies how often (in seconds) you are allowed to poll. In times
of high server load, the time may increase. Please obey the header.
- # Add authentication to your requests
- $ curl -I https://api.github.com/notifications
- HTTP/1.1 200 OK
- Last-Modified: Thu, 25 Oct 2012 15:16:27 GMT
- X-Poll-Interval: 60
+``` command-line
+# Add authentication to your requests
+$ curl -I {{ site.data.variables.product.api_url_pre }}/notifications
+HTTP/1.1 200 OK
+Last-Modified: Thu, 25 Oct 2012 15:16:27 GMT
+X-Poll-Interval: 60
- # Pass the Last-Modified header exactly
- $ curl -I https://api.github.com/notifications
- -H "If-Modified-Since: Thu, 25 Oct 2012 15:16:27 GMT"
- HTTP/1.1 304 Not Modified
- X-Poll-Interval: 60
+# Pass the Last-Modified header exactly
+$ curl -I {{ site.data.variables.product.api_url_pre }}/notifications
+$ -H "If-Modified-Since: Thu, 25 Oct 2012 15:16:27 GMT"
+> HTTP/1.1 304 Not Modified
+> X-Poll-Interval: 60
+```
## Notification Reasons
@@ -59,20 +59,20 @@ Here's a list of potential `reason`s for receiving a notification:
Reason Name | Description
------------|------------
`subscribed` | The notification arrived because you're watching the repository
-`manual` | The notification arrived because you've specifically decided to watch the item (via an Issue or Pull Request)
-`author` | The notification arrived because you've created the item
-`comment` | The notification arrived because you've commented on the item
-`mention` | The notification arrived because you were specifically **@mentioned** in the content
-`team_mention` | The notification arrived because you were on a team that was mentioned (like @org/team)
-`state_change` | The notification arrived because you changed the item state (like closing an Issue or merging a Pull Request)
-`assign` | The notification arrived because you were assigned to the Issue
+`manual` | The notification arrived because you've specifically decided to subscribe to the thread (via an Issue or Pull Request)
+`author` | The notification arrived because you've created the thread
+`comment` | The notification arrived because you've commented on the thread
+`mention` | The notification arrived because you were specifically **@mentioned** in the content
+`team_mention` | The notification arrived because you were on a team that was mentioned (like @org/team)
+`state_change` | The notification arrived because you changed the thread state (like closing an Issue or merging a Pull Request)
+`assign` | The notification arrived because you were assigned to the Issue
Note that the `reason` is modified on a per-thread basis, and can change, if the
-`reason` on a later notification is different.
+`reason` on a later notification is different.
-For example, if you are the author of an issue, subsequent notifications on that
-issue will have a `reason` of `author`. If you're then **@mentioned** on the same
-issue, the notifications you fetch thereafter will have a `reason` of `mention`.
+For example, if you are the author of an issue, subsequent notifications on that
+issue will have a `reason` of `author`. If you're then **@mentioned** on the same
+issue, the notifications you fetch thereafter will have a `reason` of `mention`.
The `reason` remains as `mention`, regardless of whether you're ever mentioned again.
## List your notifications
@@ -87,12 +87,16 @@ Name | Type | Description
-----|------|--------------
`all`|`boolean` | If `true`, show notifications marked as read. Default: `false`
`participating`|`boolean` | If `true`, only shows notifications in which the user is directly participating or mentioned. Default: `false`
-`since`|`string` | Filters out any notifications updated before the given time. This is a timestamp in ISO 8601 format: `YYYY-MM-DDTHH:MM:SSZ`. Default: `Time.now`
-
+`since`|`string` | Only show notifications updated after the given time. This is a timestamp in ISO 8601 format: `YYYY-MM-DDTHH:MM:SSZ`. Default: `Time.now`
+`before`|`string` | Only show notifications updated before the given time. This is a timestamp in ISO 8601 format: `YYYY-MM-DDTHH:MM:SSZ`.
### Response
+{% if page.version == 'dotcom' or page.version > 2.5 %}
+<%= headers 200, :pagination => default_pagination_rels %>
+{% else %}
<%= headers 200 %>
+{% endif %}
<%= json(:thread) { |h| [h] } %>
## List your notifications in a repository
@@ -107,18 +111,22 @@ Name | Type | Description
-----|------|--------------
`all`|`boolean` | If `true`, show notifications marked as read. Default: `false`
`participating`|`boolean` | If `true`, only shows notifications in which the user is directly participating or mentioned. Default: `false`
-`since`|`string` | Filters out any notifications updated before the given time. This is a timestamp in ISO 8601 format: `YYYY-MM-DDTHH:MM:SSZ`. Default: `Time.now`
-
+`since`|`string` | Only show notifications updated after the given time. This is a timestamp in ISO 8601 format: `YYYY-MM-DDTHH:MM:SSZ`. Default: `Time.now`
+`before`|`string` | Only show notifications updated before the given time. This is a timestamp in ISO 8601 format: `YYYY-MM-DDTHH:MM:SSZ`.
### Response
+{% if page.version == 'dotcom' or page.version > 2.5 %}
+<%= headers 200, :pagination => default_pagination_rels %>
+{% else %}
<%= headers 200 %>
+{% endif %}
<%= json(:thread) { |h| [h] } %>
## Mark as read
Marking a notification as "read" removes it from the [default view
-on GitHub.com](https://github.com/notifications).
+on {{ site.data.variables.product.product_name }}](https://github.com/notifications).
PUT /notifications
@@ -136,13 +144,13 @@ Name | Type | Description
## Mark notifications as read in a repository
Marking all notifications in a repository as "read" removes them
-from the [default view on GitHub.com](https://github.com/notifications).
+from the [default view on {{ site.data.variables.product.product_name }}](https://github.com/notifications).
PUT /repos/:owner/:repo/notifications
### Parameters
-Name | Type | Description
+Name | Type | Description
-----|------|--------------
`last_read_at`|`string` | Describes the last point that notifications were checked. Anything updated since this time will not be updated. This is a timestamp in ISO 8601 format: `YYYY-MM-DDTHH:MM:SSZ`. Default: `Time.now`
@@ -173,6 +181,12 @@ Name | Type | Description
This checks to see if the current user is subscribed to a thread. You can also
[get a Repository subscription](/v3/activity/watching/#get-a-repository-subscription).
+{{#tip}}
+
+Note that subscriptions are only generated if a user is participating in a conversation--for example, they've replied to the thread, were **@mention**ed, or manually subscribe to a thread.
+
+{{/tip}}
+
GET /notifications/threads/:id/subscription
### Response
@@ -182,10 +196,7 @@ This checks to see if the current user is subscribed to a thread. You can also
## Set a Thread Subscription
-This lets you subscribe to a thread, or ignore it. Subscribing to a thread
-is unnecessary if the user is already subscribed to the repository. Ignoring
-a thread will mute all future notifications (until you comment or get
-@mentioned).
+This lets you subscribe or unsubscribe from a conversation. Unsubscribing from a conversation mutes all future notifications (until you comment or get **@mention**ed once more).
PUT /notifications/threads/:id/subscription
@@ -209,4 +220,3 @@ Name | Type | Description
### Response
<%= headers 204 %>
-
diff --git a/content/v3/activity/starring.md b/content/v3/activity/starring.md
index bb78af0460..b32b1a7c0b 100644
--- a/content/v3/activity/starring.md
+++ b/content/v3/activity/starring.md
@@ -1,10 +1,9 @@
---
-title: Starring | GitHub API
+title: Starring
---
# Starring
-* TOC
{:toc}
Repository Starring is a feature that lets users bookmark repositories. Stars
@@ -15,10 +14,10 @@ Watching](/v3/activity/watching).
### Starring vs. Watching
In August 2012, we [changed the way watching
-works](https://github.com/blog/1204-notifications-stars) on GitHub. Many API
+works](https://github.com/blog/1204-notifications-stars) on {{ site.data.variables.product.product_name }}. Many API
client applications may be using the original "watcher" endpoints for accessing
this data. You can now start using the "star" endpoints instead (described
-below). Check out the [Watcher API Change post](/changes/2012-9-5-watcher-api/)
+below). Check out the [Watcher API Change post](/changes/2012-09-05-watcher-api/)
for more details.
## List Stargazers
@@ -30,11 +29,20 @@ for more details.
<%= headers 200, :pagination => default_pagination_rels %>
<%= json(:user) { |h| [h] } %>
+### Alternative response with star creation timestamps
+
+You can also find out _when_ stars were created by passing the following custom [media type](/v3/media/) via the `Accept` header:
+
+ Accept: application/vnd.github.v3.star+json
+
+<%= headers 200, :pagination => default_pagination_rels %>
+<%= json(:stargazer_with_timestamps) { |hash| [hash] } %>
+
## List repositories being starred
List repositories being starred by a user.
- GET /users/:user/starred
+ GET /users/:username/starred
List repositories being starred by the authenticated user.
@@ -42,17 +50,25 @@ List repositories being starred by the authenticated user.
### Parameters
-Name | Type | Description
+Name | Type | Description
-----|------|--------------
`sort`|`string` | One of `created` (when the repository was starred) or `updated` (when it was last pushed to). Default: `created`
`direction`|`string` | One of `asc` (ascending) or `desc` (descending). Default: `desc`
-
### Response
<%= headers 200, :pagination => default_pagination_rels %>
<%= json(:repo) { |h| [h] } %>
+### Alternative response with star creation timestamps
+
+You can also find out _when_ stars were created by passing the following custom [media type](/v3/media/) via the `Accept` header:
+
+ Accept: application/vnd.github.v3.star+json
+
+<%= headers 200, :pagination => default_pagination_rels %>
+<%= json(:starred_repo) { |hash| [hash] } %>
+
## Check if you are starring a repository
Requires for the user to be authenticated.
@@ -73,6 +89,8 @@ Requires for the user to be authenticated.
PUT /user/starred/:owner/:repo
+<%= fetch_content(:put_content_length) %>
+
### Response
<%= headers 204 %>
diff --git a/content/v3/activity/watching.md b/content/v3/activity/watching.md
index 1f387aba15..40b39b87bd 100644
--- a/content/v3/activity/watching.md
+++ b/content/v3/activity/watching.md
@@ -1,10 +1,9 @@
---
-title: Watching | GitHub API
+title: Watching
---
# Watching
-* TOC
{:toc}
Watching a Repository registers the user to receive notifications on new
@@ -21,7 +20,7 @@ legacy "watcher" endpoints continue to provide starring data.
To provide access to watching data, the v3 Watcher API uses the "subscription"
endpoints described below. Check out the [Watcher API Change
-post](/changes/2012-9-5-watcher-api/) for more details.
+post](/changes/2012-09-05-watcher-api/) for more details.
## List watchers
@@ -36,7 +35,7 @@ post](/changes/2012-9-5-watcher-api/) for more details.
List repositories being watched by a user.
- GET /users/:user/subscriptions
+ GET /users/:username/subscriptions
List repositories being watched by the authenticated user.
@@ -66,11 +65,16 @@ List repositories being watched by the authenticated user.
### Parameters
-Name | Type | Description
+Name | Type | Description
-----|------|--------------
`subscribed`|`boolean`| Determines if notifications should be received from this repository.
`ignored`|`boolean`| Determines if all notifications should be blocked from this repository.
+{{#tip}}
+
+If you would like to watch a repository, set `subscribed` to `true`. If you would like to ignore notifications made within a repository, set `ignored` to `true`. If you would like to stop watching a repository, [delete the repository's subscription](#delete-a-repository-subscription) completely.
+
+{{/tip}}
### Response
@@ -79,6 +83,12 @@ Name | Type | Description
## Delete a Repository Subscription
+{{#tip}}
+
+This endpoint should only be used to stop watching a repository. To control whether or not you wish to receive notifications from a repository, [set the repository's subscription manually](#set-a-repository-subscription).
+
+{{/tip}}
+
DELETE /repos/:owner/:repo/subscription
### Response
@@ -101,10 +111,12 @@ Requires for the user to be authenticated.
## Watch a repository (LEGACY)
-Requires for the user to be authenticated.
+Requires the user to be authenticated.
PUT /user/subscriptions/:owner/:repo
+<%= fetch_content(:put_content_length) %>
+
### Response
<%= headers 204 %>
diff --git a/content/v3/auth.md b/content/v3/auth.md
index 2060438b4e..ca387bfaa0 100644
--- a/content/v3/auth.md
+++ b/content/v3/auth.md
@@ -1,17 +1,16 @@
---
-title: Other Authentication Methods | GitHub API
+title: Other Authentication Methods
---
# Other Authentication Methods
-* TOC
{:toc}
While the API provides multiple methods for authentication, we strongly
recommend using [OAuth](/v3/oauth/) for production applications. The other
methods provided are intended to be used for scripts or testing (i.e., cases
where full OAuth would be overkill). Third party applications that rely on
-GitHub for authentication should not ask for or collect GitHub credentials.
+{{ site.data.variables.product.product_name }} for authentication should not ask for or collect {{ site.data.variables.product.product_name }} credentials.
Instead, they should use the [OAuth web flow](/v3/oauth).
## Basic Authentication
@@ -20,34 +19,31 @@ The API supports Basic Authentication as defined in
[RFC2617](http://www.ietf.org/rfc/rfc2617.txt) with a few slight differences.
The main difference is that the RFC requires unauthenticated requests to be
answered with `401 Unauthorized` responses. In many places, this would disclose
-the existence of user data. Instead, the GitHub API responds with `404 Not Found`.
+the existence of user data. Instead, the {{ site.data.variables.product.product_name }} API responds with `404 Not Found`.
This may cause problems for HTTP libraries that assume a `401 Unauthorized`
response. The solution is to manually craft the `Authorization` header.
### Via Username and Password
-To use Basic Authentication with the GitHub API, simply send the username and
+To use Basic Authentication with the {{ site.data.variables.product.product_name }} API, simply send the username and
password associated with the account.
For example, if you're accessing the API via [cURL][curl], the following command
-would authenticate you if you replace `-$ curl -u <username> https://api.github.com/user -+``` command-line +$ curl -u username {{ site.data.variables.product.api_url_pre }}/user +``` ### Via OAuth Tokens -Alternatively, you can authenticate using [personal access -tokens][personal-access-tokens] or OAuth tokens. To do so, provide the token as -the username and provide a blank password or a password of `x-oauth-basic`. If -you're accessing the API via cURL, replace `
-$ curl -u <token>:x-oauth-basic https://api.github.com/user -+``` command-line +$ curl -u username:token {{ site.data.variables.product.api_url_pre }}/user +``` This approach is useful if your tools only support Basic Authentication but you want to take advantage of OAuth access token security features. @@ -68,8 +64,7 @@ Because these authentication codes expire quickly, we recommend using the Authorizations API to [create an access token][create-access] and using that token to [authenticate via OAuth][oauth-auth] for most API access. -Alternately, you can create access tokens from the Personal Access Token -section of your [application settings page](https://github.com/settings/applications). +Alternately, you can create access tokens from the Personal Access Token [settings page](https://github.com/settings/tokens). [create-access]: /v3/oauth_authorizations/#create-a-new-authorization [curl]: http://curl.haxx.se/ diff --git a/content/v3/changelog.md b/content/v3/changelog.md index 5852a338a1..9a102517b7 100644 --- a/content/v3/changelog.md +++ b/content/v3/changelog.md @@ -2,4 +2,4 @@ title: GitHub API Changelog --- -The API changelog can now be found on the [homepage](/). Please update your links. +The API changelog can now be found [here](/changes). Please update your links. diff --git a/content/v3/emojis.md b/content/v3/emojis.md index 4f5dc5b3ce..b80e96eb51 100644 --- a/content/v3/emojis.md +++ b/content/v3/emojis.md @@ -1,10 +1,10 @@ --- -title: Emojis | GitHub API +title: Emojis --- # Emojis -Lists all the emojis available to use on GitHub. +Lists all the emojis available to use on {{ site.data.variables.product.product_name }}. GET /emojis diff --git a/content/v3/enterprise.md b/content/v3/enterprise.md new file mode 100644 index 0000000000..2bcd997e44 --- /dev/null +++ b/content/v3/enterprise.md @@ -0,0 +1,46 @@ +--- +title: Enterprise +--- + +# Enterprise <%= config[:latest_enterprise_version] %> + +{:toc} + +[GitHub Enterprise](https://enterprise.github.com/) supports the same powerful API available on GitHub.com as well as its own set of API endpoints. You can find a list of these endpoints on the sidebar, with the exception of the [User Administration][] API, which is within its own section. + +## Endpoint URLs + +All API endpoints—except [Management Console][] API endpoints—are prefixed with the following URL: + +``` command-line +http(s)://hostname/api/v3/ +``` + +[Management Console][] API endpoints are only prefixed with a hostname: + +``` command-line +http(s)://hostname/ +``` + +## Authentication + +Your Enterprise installation's API endpoints accept [the same authentication methods](http://developer.github.com/v3/#authentication) as the GitHub.com API. Specifically, you can authenticate yourself with **[OAuth tokens][]** (which can be created using the [Authorizations API][]) or **[basic authentication][]**. + +Every Enterprise API endpoint is only accessible to GitHub Enterprise site administrators, with the exception of the [Management Console][] API, which is only accessible via the [Management Console password][]. + +[Authorizations API]: /v3/oauth_authorizations/#create-a-new-authorization +[OAuth tokens]: /v3/oauth/ +[basic authentication]: /v3/#basic-authentication +[Management Console]: /v3/enterprise/management_console/ +[User Administration]: /v3/users/administration/ +[Management Console password]: https://help.github.com/enterprise/admin/articles/accessing-the-management-console/ + +## Releases + +The latest release for GitHub Enterprise is <%= config[:versions][0] %>. The GitHub APIs available to this release are located at
null object.
+
+{{/tip}}
### Response
@@ -125,13 +176,15 @@ including the filename with a `null` hash.
### Response
-<%= headers 200 %>
+<%= headers 200, :pagination => { :next => 'https://api.github.com/resource?page=2' } %>
<%= json(:gist_history) %>
## Star a gist
PUT /gists/:id/star
+<%= fetch_content(:put_content_length) %>
+
### Response
<%= headers 204 %>
@@ -160,11 +213,15 @@ including the filename with a `null` hash.
POST /gists/:id/forks
-**Note**: This was previously `/gists/:id/fork`
+{{#tip}}
+
+**Note**: This was previously `/gists/:id/fork`.
+
+{{/tip}}
### Response
-<%= headers 201, :Location => "https://api.github.com/gists/2" %>
+<%= headers 201, :Location => get_resource(:gist)['url'] %>
<%= json(:gist) %>
## List gist forks
@@ -173,7 +230,7 @@ including the filename with a `null` hash.
### Response
-<%= headers 200 %>
+<%= headers 200, :pagination => default_pagination_rels %>
<%= json(:gist_forks) %>
## Delete a gist
@@ -185,3 +242,11 @@ including the filename with a `null` hash.
<%= headers 204 %>
[1]: /v3/oauth/#scopes
+
+## Custom media types
+
+The following media types are supported when fetching gist contents. You can read more about the
+use of media types in the API [here](/v3/media/).
+
+ application/vnd.github.VERSION.raw
+ application/vnd.github.VERSION.base64
diff --git a/content/v3/gists/comments.md b/content/v3/gists/comments.md
index 0a53cfa580..91249c09f6 100644
--- a/content/v3/gists/comments.md
+++ b/content/v3/gists/comments.md
@@ -1,10 +1,9 @@
---
-title: Gist Comments | GitHub API
+title: Gist Comments
---
# Comments
-* TOC
{:toc}
Gist Comments use [these custom media types](#custom-media-types).
@@ -17,7 +16,7 @@ You can read more about the use of media types in the API
### Response
-<%= headers 200 %>
+<%= headers 200, :pagination => default_pagination_rels %>
<%= json(:gist_comment) { |h| [h] } %>
## Get a single comment
@@ -35,7 +34,7 @@ You can read more about the use of media types in the API
### Parameters
-Name | Type | Description
+Name | Type | Description
-----|------|--------------
`body`|`string` | **Required**. The comment text.
@@ -44,8 +43,7 @@ Name | Type | Description
### Response
-<%= headers 201,
- :Location => "https://api.github.com/gists/comments/1" %>
+<%= headers 201, :Location => get_resource(:gist_comment)['url'] %>
<%= json :gist_comment %>
## Edit a comment
@@ -54,7 +52,7 @@ Name | Type | Description
### Input
-Name | Type | Description
+Name | Type | Description
-----|------|--------------
`body`|`string` | **Required**. The comment text.
diff --git a/content/v3/git.md b/content/v3/git.md
index 8259eeda3d..a7ec1bd618 100644
--- a/content/v3/git.md
+++ b/content/v3/git.md
@@ -1,11 +1,11 @@
---
-title: Git Data | GitHub API
+title: Git Data
---
# Git Data
The Git Database API gives you access to read and write raw Git objects
-to your Git database on GitHub and to list and update your references
+to your Git database on {{ site.data.variables.product.product_name }} and to list and update your references
(branch heads and tags).
This basically allows you to reimplement a lot of Git functionality over
@@ -20,7 +20,7 @@ Support](https://github.com/contact?form[subject]=Commits API) if this response
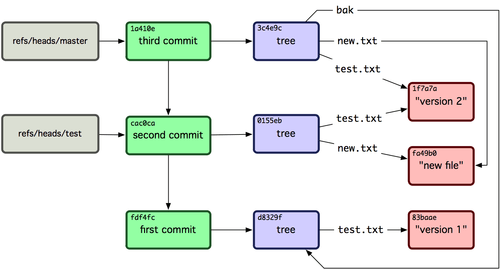
For more information on the Git object database, please read the
-[Git Internals](http://git-scm.com/book/en/Git-Internals) chapter of
+[Git Internals](http://git-scm.com/book/en/v1/Git-Internals) chapter of
the Pro Git book.
As an example, if you wanted to commit a change to a file in your
diff --git a/content/v3/git/blobs.md b/content/v3/git/blobs.md
index 7238820939..df84b5c41f 100644
--- a/content/v3/git/blobs.md
+++ b/content/v3/git/blobs.md
@@ -1,17 +1,11 @@
---
-title: Git Blobs | GitHub API
+title: Git Blobs
---
# Blobs
-* TOC
{:toc}
-Since blobs can be any arbitrary binary data, the input and responses
-for the blob API takes an encoding parameter that can be either `utf-8`
-or `base64`. If your data cannot be losslessly sent as a UTF-8 string,
-you can base64 encode it.
-
Blobs leverage [these custom media types](#custom-media-types). You can
read more about the use of media types in the API [here](/v3/media/).
@@ -19,6 +13,8 @@ read more about the use of media types in the API [here](/v3/media/).
GET /repos/:owner/:repo/git/blobs/:sha
+The `content` in the response will always be Base64 encoded.
+
*Note*: This API supports blobs up to 100 megabytes in size.
### Response
@@ -30,14 +26,20 @@ read more about the use of media types in the API [here](/v3/media/).
POST /repos/:owner/:repo/git/blobs
-### Input
+### Parameters
+
+Name | Type | Description
+-----|------|-------------
+`content`|`string` | **Required**. The new blob's content.
+`encoding`|`string` | The encoding used for `content`. Currently, `"utf-8"` and `"base64"` are supported. Default: `"utf-8"`.
+
+### Example Input
<%= json :content => "Content of the blob", :encoding => "utf-8" %>
### Response
-<%= headers 201,
- :Location => "https://api.github.com/repos/octocat/example/git/blobs/3a0f86fb8db8eea7ccbb9a95f325ddbedfb25e15" %>
+<%= headers 201, :Location => get_resource(:blob_after_create)['url'] %>
<%= json :blob_after_create %>
## Custom media types
diff --git a/content/v3/git/commits.md b/content/v3/git/commits.md
index 6bfb8cdf2c..69a0da52fe 100644
--- a/content/v3/git/commits.md
+++ b/content/v3/git/commits.md
@@ -1,10 +1,9 @@
---
-title: Git Commits | GitHub API
+title: Git Commits
---
# Commits
-* TOC
{:toc}
## Get a Commit
@@ -31,20 +30,20 @@ Name | Type | Description
### Optional Parameters
-You can provide an additional `commiter` parameter, which is a hash containing
+You can provide an additional `committer` parameter, which is an object containing
information about the committer. Or, you can provide an `author` parameter, which
-is a hash containing information about the author.
+is an object containing information about the author.
The `committer` section is optional and will be filled with the `author`
data if omitted. If the `author` section is omitted, it will be filled
in with the authenticated user's information and the current date.
-Both the `author` and `commiter` parameters have the same keys:
+Both the `author` and `committer` parameters have the same keys:
Name | Type | Description
-----|------|-------------
-`name`|`string` | The name of the author (or commiter) of the commit
-`email`|`string` | The email of the author (or commiter) of the commit
+`name`|`string` | The name of the author (or committer) of the commit
+`email`|`string` | The email of the author (or committer) of the commit
`date`|`string` | Indicates when this commit was authored (or committed). This is a timestamp in ISO 8601 format: `YYYY-MM-DDTHH:MM:SSZ`.
### Example Input
@@ -58,6 +57,61 @@ Name | Type | Description
### Response
-<%= headers 201,
- :Location => "https://api.github.com/repos/octocat/Hello-World/git/commits/7638417db6d59f3c431d3e1f261cc637155684cd" %>
+<%= headers 201, :Location => get_resource(:new_commit)['url'] %>
<%= json :new_commit %>
+
+{% if page.version == 'dotcom' %}
+
+## Commit signature verification
+
+{{#tip}}
+
+Commit response objects including signature verification data are currently available for developers to preview.
+During the preview period, the object formats may change without advance notice.
+Please see the [blog post](/changes/2016-04-04-git-signing-api-preview) for full details.
+
+To receive signature verification data in commit objects you must provide a custom [media type](/v3/media) in the `Accept` header:
+
+ application/vnd.github.cryptographer-preview
+
+{{/tip}}
+
+ GET /repos/:owner/:repo/git/commits/:sha
+
+### Response
+
+<%= headers 200 %>
+<%= json(:signed_git_commit) %>
+
+### The `verification` object
+
+The response will include a `verification` field whose value is an object describing the result of verifying the commit's signature. The following fields are included in the `verification` object:
+
+Name | Type | Description
+-----|------|--------------
+`verified`|`boolean` | Does GitHub consider the signature in this commit to be verified?
+`reason`|`string` | The reason for `verified` value. Possible values and their meanings are enumerated in the table below.
+`signature`|`string` | The signature that was extracted from the commit.
+`payload`|`string` | The value that was signed.
+
+#### The `reason` field
+
+The following are possible `reason`s that may be included in the `verification` object:
+
+Value | Description
+------|------------
+`expired_key` | The key that made the signature is expired.
+`not_signing_key` | The "signing" flag is not among the usage flags in the GPG key that made the signature.
+`gpgverify_error` | There was an error communicating with the signature-verification service.
+`gpgverify_unavailable` | The signature-verification service is currently unavailable.
+`unsigned` | The object does not include a signature.
+`unknown_signature_type` | A non-PGP signature was found in the commit.
+`no_user` | No user was associated with the `committer` email address in the commit.
+`unverified_email` | The `committer` email address in the commit was associated with a user, but the email address is not verified on her/his account.
+`bad_email` | The `committer` email address in the commit is not included in the identities of the PGP key that made the signature.
+`unknown_key` | The key that made the signature has not been registered with any user's account.
+`malformed_signature` | There was an error parsing the signature.
+`invalid` | The signature could not be cryptographically verified using the key whose key-id was found in the signature.
+`valid` | None of the above errors applied, so the signature is considered to be verified.
+
+{% endif %}
diff --git a/content/v3/git/refs.md b/content/v3/git/refs.md
index d7707ec33d..ef4a444d92 100644
--- a/content/v3/git/refs.md
+++ b/content/v3/git/refs.md
@@ -1,10 +1,9 @@
---
-title: Git Refs | GitHub API
+title: Git Refs
---
# References
-* TOC
{:toc}
## Get a Reference
@@ -15,11 +14,26 @@ The `ref` in the URL must be formatted as `heads/branch`, not just `branch`. For
GET /repos/:owner/:repo/git/refs/heads/skunkworkz/featureA
-### Response
-
<%= headers 200 %>
<%= json :ref %>
+If the `ref` doesn't exist in the repository, but existing refs start with `ref`
+they will be returned as an array. For example, a call to get the data for a
+branch named `feature`, which doesn't exist, would return head refs
+including `featureA` and `featureB` which do.
+
+ GET /repos/:owner/:repo/git/refs/heads/feature
+
+<%= headers 200 %>
+<%= json :refs_matching %>
+
+If the `ref` doesn't match an existing ref or any prefixes a 404 will be returned.
+
+ GET /repos/:owner/:repo/git/refs/heads/feature-branch-that-no-longer-exists
+
+<%= headers 404 %>
+<%= json :refs_not_found %>
+
## Get all References
GET /repos/:owner/:repo/git/refs
@@ -36,7 +50,7 @@ references, you can call:
For a full refs listing, you'll get something that looks like:
-<%= headers 200 %>
+<%= headers 200, :pagination => default_pagination_rels %>
<%= json :refs %>
@@ -48,8 +62,8 @@ For a full refs listing, you'll get something that looks like:
Name | Type | Description
-----|------|--------------
-`ref`|`type`| The name of the fully qualified reference (ie: `refs/heads/master`). If it doesn't start with 'refs' and have at least two slashes, it will be rejected.
-`sha`|`type`| The SHA1 value to set this reference to
+`ref`|`type`| **Required**. The name of the fully qualified reference (ie: `refs/heads/master`). If it doesn't start with 'refs' and have at least two slashes, it will be rejected.
+`sha`|`type`| **Required**. The SHA1 value to set this reference to
### Input
@@ -59,8 +73,7 @@ Name | Type | Description
### Response
-<%= headers 201, \
- :Location => "https://api.github.com/repos/octocat/Hello-World/git/refs/heads/featureA" %>
+<%= headers 201, :Location => get_resource(:ref)['url'] %>
<%= json :ref %>
## Update a Reference
@@ -71,7 +84,7 @@ Name | Type | Description
Name | Type | Description
-----|------|--------------
-`sha`|`type`| The SHA1 value to set this reference to
+`sha`|`type`| **Required**. The SHA1 value to set this reference to
`force`|`boolean`| Indicates whether to force the update or to make sure the update is a fast-forward update. Leaving this out or setting it to `false` will make sure you're not overwriting work. Default: `false`
diff --git a/content/v3/git/tags.md b/content/v3/git/tags.md
index 1b51ae7107..b0605da270 100644
--- a/content/v3/git/tags.md
+++ b/content/v3/git/tags.md
@@ -1,10 +1,9 @@
---
-title: Git Tags | GitHub API
+title: Git Tags
---
# Tags
-* TOC
{:toc}
This tags API only deals with tag objects - so only annotated tags, not
@@ -39,9 +38,9 @@ Name | Type | Description
`message`|`string`| The tag message
`object`|`string`| The SHA of the git object this is tagging
`type`|`string`| The type of the object we're tagging. Normally this is a `commit` but it can also be a `tree` or a `blob`.
-`tagger`|`hash`| A hash with information about the individual creating the tag.
+`tagger`|`object`| An object with information about the individual creating the tag.
-The `tagger` hash contains the following keys:
+The `tagger` object contains the following keys:
Name | Type | Description
-----|------|--------------
@@ -62,6 +61,61 @@ Name | Type | Description
### Response
-<%= headers 201,
- :Location => "https://api.github.com/repos/octocat/Hello-World/git/tags/940bd336248efae0f9ee5bc7b2d5c985887b16ac" %>
+<%= headers 201, :Location => get_resource(:gittag)['url'] %>
<%= json :gittag %>
+
+{% if page.version == 'dotcom' %}
+
+## Tag signature verification
+
+{{#tip}}
+
+Tag response objects including signature verification data are currently available for developers to preview.
+During the preview period, the object formats may change without advance notice.
+Please see the [blog post](/changes/2016-04-04-git-signing-api-preview) for full details.
+
+To receive signature verification data in tag objects you must provide a custom [media type](/v3/media) in the `Accept` header:
+
+ application/vnd.github.cryptographer-preview
+
+{{/tip}}
+
+ GET /repos/:owner/:repo/git/tags/:sha
+
+### Response
+
+<%= headers 200 %>
+<%= json(:signed_gittag) %>
+
+### The `verification` object
+
+The response will include a `verification` field whose value is an object describing the result of verifying the tag's signature. The following fields are included in the `verification` object:
+
+Name | Type | Description
+-----|------|--------------
+`verified`|`boolean` | Does GitHub consider the signature in this tag to be verified?
+`reason`|`string` | The reason for `verified` value. Possible values and their meanings are enumerated in the table below.
+`signature`|`string` | The signature that was extracted from the tag.
+`payload`|`string` | The value that was signed.
+
+#### The `reason` field
+
+The following are possible `reason`s that may be included in the `verification` object:
+
+Value | Description
+------|------------
+`expired_key` | The key that made the signature is expired.
+`not_signing_key` | The "signing" flag is not among the usage flags in the GPG key that made the signature.
+`gpgverify_error` | There was an error communicating with the signature-verification service.
+`gpgverify_unavailable` | The signature-verification service is currently unavailable.
+`unsigned` | The object does not include a signature.
+`unkown_signature_type` | A non-PGP signature was found in the tag.
+`no_user` | No user was associated with the `tagger` email address in the tag.
+`unverified_email` | The `tagger` email address in the tag was associated with a user, but the email address is not verified on her/his account.
+`bad_email` | The `tagger` email address in the tag is not included in the identities of the PGP key that made the signature.
+`unknown_key` | The key that made the signature has not been registered with any user's account.
+`malformed_signature` | There was an error parsing the signature.
+`invalid` | The signature could not be cryptographically verified using the key whose key-id was found in the signature.
+`valid` | None of the above errors applied, so the signature is considered to be verified.
+
+{% endif %}
diff --git a/content/v3/git/trees.md b/content/v3/git/trees.md
index dac6e4366c..485e622ada 100644
--- a/content/v3/git/trees.md
+++ b/content/v3/git/trees.md
@@ -1,10 +1,9 @@
---
-title: Git Trees | GitHub API
+title: Git Trees
---
# Trees
-* TOC
{:toc}
## Get a Tree
@@ -13,6 +12,12 @@ title: Git Trees | GitHub API
### Response
+{{#tip}}
+
+If `truncated` is `true`, the number of items in the `tree` array exceeded our maximum limit. If you need to fetch more items, you can clone the repository and iterate over the Git data locally.
+
+{{/tip}}
+
<%= headers 200 %>
<%= json :tree %>
@@ -22,6 +27,12 @@ title: Git Trees | GitHub API
### Response
+{{#tip}}
+
+If `truncated` is `true`, the number of items in the `tree` array exceeded our maximum limit. If you need to fetch more items, use the non-recursive method of fetching trees, and fetch one sub-tree at a time.
+
+{{/tip}}
+
<%= headers 200 %>
<%= json :tree_extra %>
@@ -38,7 +49,7 @@ a new tree out.
Name | Type | Description
-----|------|--------------
-`tree`|`array` of `hash`es | **Required**. Objects (of `path`, `mode`, `type`, and `sha`) specifying a tree structure
+`tree`|`array` of `object`s | **Required**. Objects (of `path`, `mode`, `type`, and `sha`) specifying a tree structure
`base_tree`| `string` | The SHA1 of the tree you want to update with new data. If you don't set this, the commit will be created on top of everything; however, it will only contain your change, the rest of your files will show up as deleted.
The `tree` parameter takes the following keys:
@@ -49,7 +60,7 @@ Name | Type | Description
`mode`|`string`| The file mode; one of `100644` for file (blob), `100755` for executable (blob), `040000` for subdirectory (tree), `160000` for submodule (commit), or `120000` for a blob that specifies the path of a symlink
`type`| `string`| Either `blob`, `tree`, or `commit`
`sha`|`string`| The SHA1 checksum ID of the object in the tree
-`content`|`string` | The content you want this file to have. GitHub will write this blob out and use that SHA for this entry. Use either this, or `tree.sha`.
+`content`|`string` | The content you want this file to have. {{ site.data.variables.product.product_name }} will write this blob out and use that SHA for this entry. Use either this, or `tree.sha`.
### Input
@@ -64,6 +75,5 @@ Name | Type | Description
### Response
-<%= headers 201,
- :Location => "https://api.github.com/repos/octocat/Hello-World/trees/cd8274d15fa3ae2ab983129fb037999f264ba9a7" %>
+<%= headers 201, :Location => get_resource(:tree_new)['url'] %>
<%= json :tree_new %>
diff --git a/content/v3/gitignore.md b/content/v3/gitignore.md
index bdd18a6e78..66fc12632d 100644
--- a/content/v3/gitignore.md
+++ b/content/v3/gitignore.md
@@ -1,15 +1,14 @@
---
-title: Gitignore | GitHub API
+title: Gitignore
---
# Gitignore
-* TOC
{:toc}
-When you create a new GitHub repository via the API, you can specify a
+When you create a new {{ site.data.variables.product.product_name }} repository via the API, you can specify a
[.gitignore template][what-is] to apply to the repository upon creation. The
-.gitignore Templates API lists and fetches templates from the [GitHub .gitignore repository][templates-repo].
+.gitignore Templates API lists and fetches templates from the [{{ site.data.variables.product.product_name }} .gitignore repository][templates-repo].
## Listing available templates
diff --git a/content/v3/issues.md b/content/v3/issues.md
index 4344a90789..59e7f99a29 100644
--- a/content/v3/issues.md
+++ b/content/v3/issues.md
@@ -1,10 +1,9 @@
---
-title: Issues | GitHub API
+title: Issues
---
# Issues
-* TOC
{:toc}
Issues use [these custom media types](#custom-media-types). You can
@@ -12,17 +11,25 @@ read more about the use of media types in the API [here](/v3/media/).
## List issues
-List all issues across all the authenticated user's visible repositories
+<%= fetch_content(:prs_as_issues) %>
+
+List all issues **assigned** to the authenticated user across all visible repositories
including owned repositories, member repositories, and organization
repositories:
GET /issues
-List all issues across owned and member repositories for the authenticated user:
+{{#tip}}
+
+You can use the `filter` query parameter to fetch issues that are not necessarily assigned to you. See the table below for more information.
+
+{{/tip}}
+
+List all issues across owned and member repositories assigned to the authenticated user:
GET /user/issues
-List all issues for a given organization for the authenticated user:
+List all issues for a given organization assigned to the authenticated user:
GET /orgs/:org/issues
@@ -42,17 +49,39 @@ Name | Type | Description
<%= headers 200, :pagination => default_pagination_rels %>
<%= json(:issue) { |h| [h] } %>
+{% if page.version == 'dotcom' %}
+#### Reactions summary
+
+{{#tip}}
+
+
+
+ An additional `reactions` object in the issue payload is currently available for developers to preview. During the preview period, the APIs may change without advance notice.
+ Please see the [blog post](/changes/2016-05-12-reactions-api-preview) for full details.
+
+ To access the API you must provide a custom [media type](/v3/media) in the `Accept` header:
+
+ application/vnd.github.squirrel-girl-preview
+
+ The `reactions` key will have the following payload where `url` can be used to construct the API location for [listing and creating](/v3/reactions) reactions.
+
+{{/tip}}
+<%= json :issue_reaction_summary %>
+{% endif %}
+
## List issues for a repository
+<%= fetch_content(:prs_as_issues) %>
+
GET /repos/:owner/:repo/issues
### Parameters
Name | Type | Description
-----|------|--------------
-`milestone`|`integer` or `string`| If an `integer` is passed, it should refer to a milestone number. If the string `*` is passed, issues with any milestone are accepted. If the string `none` is passed, issues without milestones are returned. Default: `*`
+`milestone`|`integer` or `string`| If an `integer` is passed, it should refer to a milestone by its `number` field. If the string `*` is passed, issues with any milestone are accepted. If the string `none` is passed, issues without milestones are returned.
`state`|`string`| Indicates the state of the issues to return. Can be either `open`, `closed`, or `all`. Default: `open`
-`assignee`|`string`| Can be the name of a user. Pass in `none` for issues with no assigned user, and `*` for issues assigned to any user. Default: `*`
+`assignee`|`string`| Can be the name of a user. Pass in `none` for issues with no assigned user, and `*` for issues assigned to any user.
`creator`|`string`| The user that created the issue.
`mentioned`|`string`| A user that's mentioned in the issue.
`labels`|`string`| A list of comma separated label names. Example: `bug,ui,@high`
@@ -65,8 +94,31 @@ Name | Type | Description
<%= headers 200, :pagination => default_pagination_rels %>
<%= json(:issue) { |h| [h] } %>
+{% if page.version == 'dotcom' %}
+#### Reactions summary
+
+{{#tip}}
+
+
+
+ An additional `reactions` object in the issue payload is currently available for developers to preview.
+ During the preview period, the APIs may change without advance notice.
+ Please see the [blog post](/changes/2016-05-12-reactions-api-preview) for full details.
+
+ To access the API you must provide a custom [media type](/v3/media) in the `Accept` header:
+
+ application/vnd.github.squirrel-girl-preview
+
+ The `reactions` key will have the following payload where `url` can be used to construct the API location for [listing and creating](/v3/reactions) reactions.
+
+{{/tip}}
+<%= json :issue_reaction_summary %>
+{% endif %}
+
## Get a single issue
+<%= fetch_content(:prs_as_issues) %>
+
GET /repos/:owner/:repo/issues/:number
### Response
@@ -74,11 +126,26 @@ Name | Type | Description
<%= headers 200 %>
<%= json :full_issue %>
-
- Note: Every pull request is an issue, but not every issue is a pull request. If the issue is not a pull request, the response omits the pull_request attribute.
-
-
+
- id +
- The Integer ID of the event. -commit_id -: The String SHA of a commit that referenced this Issue +
- url +
- The API URL for fetching the event. -event -: Identifies the actual type of Event that occurred. +
- actor +
- The User object that generated the event. + +
- commit_id +
- The String SHA of a commit that referenced this Issue + +
- commit_url +
- The GitHub API link to a commit that referenced this Issue + +
- event +
- Identifies the actual type of Event that occurred. + +
- created_at +
- The timestamp indicating when the event occurred. + +
- label +
- The Label object including `name` and `color` attributes. Only provided for `labeled` + and `unlabeled` events. + +
- assignee +
- The User object which was assigned to (or unassigned from) this Issue. Only provided for 'assigned' and 'unassigned' events. + + {% if page.version == 'dotcom' or page.version > 2.5 %} +
- assigner +
- The User object that performed the assignment (or unassignment) for this Issue. Only provided for 'assigned' and 'unassigned' events. + {% endif %} + +
- milestone +
- The Milestone object including a `title` attribute. Only provided for `milestoned` and + `demilestoned` events. + +
- rename +
- An object containing rename details including `from` and `to` attributes. Only + provided for `renamed` events. +
-
+
- closed +
- The issue was closed by the actor. When the commit_id is present, it identifies the commit that closed the issue using "closes / fixes #NN" - syntax. + syntax. + -reopened -: The issue was reopened by the actor. +
- reopened +
- The issue was reopened by the actor. -subscribed -: The actor subscribed to receive notifications for an issue. +
- subscribed +
- The actor subscribed to receive notifications for an issue. -merged -: The issue was merged by the actor. The `commit_id` attribute is the SHA1 of - the HEAD commit that was merged. +
- merged +
- The issue was merged by the actor. The `commit_id` attribute is the SHA1 of + the HEAD commit that was merged. -referenced -: The issue was referenced from a commit message. The `commit_id` attribute is - the commit SHA1 of where that happened. +
- referenced +
- The issue was referenced from a commit message. The `commit_id` attribute is + the commit SHA1 of where that happened. -mentioned -: The actor was @mentioned in an issue body. +
- mentioned +
- The actor was @mentioned in an issue body. -assigned -: The issue was assigned to the actor. +
- assigned +
- The issue was assigned to the actor. -head_ref_deleted -: The pull request's branch was deleted. +
- unassigned +
- The actor was unassigned from the issue. -head_ref_restored -: The pull request's branch was restored. +
- labeled +
- A label was added to the issue. + +
- unlabeled +
- A label was removed from the issue. + +
- milestoned +
- The issue was added to a milestone. + +
- demilestoned +
- The issue was removed from a milestone. + +
- renamed +
- The issue title was changed. + +
- locked +
- The issue was locked by the actor. + +
- unlocked +
- The issue was unlocked by the actor. + +
- head_ref_deleted +
- The pull request's branch was deleted. + +
- head_ref_restored +
- The pull request's branch was restored. +
-
+
- id +
- The Integer ID of the event. + +
- url +
- The API URL for fetching the event. + +
- actor +
- The User object that generated the event. + +
- commit_id +
- The String SHA of a commit that referenced this Issue. + +
- event +
- Identifies the actual type of Event that occurred. + +
- created_at +
- The timestamp indicating when the event occurred. + +
- label +
- The Label object including `name` and `color` attributes. Only provided for `labeled` + and `unlabeled` events. + +
- assignee +
- The User object which was assigned to (or unassigned from) this Issue. Only provided for `assigned` and `unassigned` events. + +
- milestone +
- The Milestone object including a `title` attribute. Only provided for `milestoned` and + `demilestoned` events. + +
- source +
- The `id`, `actor`, and `url` for the source of a reference from +another issue. Only provided for `cross-referenced` events. + +
- rename +
- An object containing rename details including `from` and `to` attributes. Only + provided for `renamed` events. +
-
+
- assigned +
- The issue was assigned to the assignee. + +
- closed +
- The issue was closed by the actor. When the commit_id is present, it + identifies the commit that closed the issue using "closes / fixes #NN" + syntax. + +
- commented +
- A comment was added to the issue. + +
- committed +
- A commit was added to the pull request's `HEAD` branch. Only +provided for pull requests. + +
- cross-referenced +
- The issue was referenced from another issue. The `source` +attribute contains the `id`, `actor`, and `url` of the reference's +source. + +
- demilestoned +
- The issue was removed from a milestone. + +
- head_ref_deleted +
- The pull request's branch was deleted. + +
- head_ref_restored +
- The pull request's branch was restored. + +
- labeled +
- A label was added to the issue. + +
- locked +
- The issue was locked by the actor. + +
- mentioned +
- The actor was @mentioned in an issue body. + +
- merged +
- The issue was merged by the actor. The `commit_id` attribute is the SHA1 of + the HEAD commit that was merged. + +
- milestoned +
- The issue was added to a milestone. + +
- referenced +
- The issue was referenced from a commit message. The `commit_id` attribute is + the commit SHA1 of where that happened. + +
- renamed +
- The issue title was changed. + +
- reopened +
- The issue was reopened by the actor. + +
- subscribed +
- The actor subscribed to receive notifications for an issue. + +
- unassigned +
- The assignee was unassigned from the issue. + +
- unlabeled +
- A label was removed from the issue. + +
- unlocked +
- The issue was unlocked by the actor. + +
- unsubscribed +
- The actor unsubscribed to stop receiving notifications for an issue. +
* `markdown` to render a document as plain Markdown, just like README files are rendered.
* `gfm` to render a document as user-content, _e.g._ like user comments or issues are rendered. In GFM mode, hard line breaks are always taken into account, and issue and user mentions are linked accordingly.
Default: `markdown` diff --git a/content/v3/media.md b/content/v3/media.md index 33515e58b7..539acc407c 100644 --- a/content/v3/media.md +++ b/content/v3/media.md @@ -1,9 +1,8 @@ --- -title: Media Types | GitHub API +title: Media Types --- # Media Types -* TOC {:toc} Custom media types are used in the API to let consumers choose the format @@ -12,7 +11,7 @@ the following types to the `Accept` header when you make a request. Media types are specific to resources, allowing them to change independently and support formats that other resources don't. -All GitHub media types look like this: +All {{ site.data.variables.product.product_name }} media types look like this: application/vnd.github[.version].param[+json] @@ -45,19 +44,21 @@ put the version before the property: You can check the current version through every response's headers. Look for the `X-GitHub-Media-Type` header: - $ curl https://api.github.com/users/technoweenie -I - HTTP/1.1 200 OK - X-GitHub-Media-Type: github.v3 +``` command-line +$ curl {{ site.data.variables.product.api_url_pre }}/users/technoweenie -I +> HTTP/1.1 200 OK +> X-GitHub-Media-Type: github.v3 - $ curl https://api.github.com/users/technoweenie -I \ - -H "Accept: application/vnd.github.full+json" - HTTP/1.1 200 OK - X-GitHub-Media-Type: github.v3; param=full; format=json +$ curl {{ site.data.variables.product.api_url_pre }}/users/technoweenie -I \ +$ -H "Accept: application/vnd.github.full+json" +> HTTP/1.1 200 OK +> X-GitHub-Media-Type: github.v3; param=full; format=json - $ curl https://api.github.com/users/technoweenie -I \ - -H "Accept: application/vnd.github.v3.full+json" - HTTP/1.1 200 OK - X-GitHub-Media-Type: github.v3; param=full; format=json +$ curl {{ site.data.variables.product.api_url_pre }}/users/technoweenie -I \ +$ -H "Accept: application/vnd.github.v3.full+json" +> HTTP/1.1 200 OK +> X-GitHub-Media-Type: github.v3; param=full; format=json +``` ## Comment Body Properties @@ -124,6 +125,37 @@ The Commit, Commit Comparison, and Pull Request resources support application/vnd.github.VERSION.patch +### sha + + application/vnd.github.VERSION.sha + +## Repository contents + +### Raw + + application/vnd.github.VERSION.raw + +Return the raw contents of a file. This is the default if you do not pass any specific media type. + +### HTML + + application/vnd.github.VERSION.html + +For markup files such as Markdown or AsciiDoc, you can retrieve the rendered HTML using the `.html` media type. Markup languages are rendered to HTML using our open-source [Markup library](https://github.com/github/markup). + +## Gists + +### Raw + + application/vnd.github.VERSION.raw + +Return the raw contents of a gist. This is the default if you do not pass any specific media type. + +### base64 + + application/vnd.github.VERSION.base64 + +The gist contents are base64-encoded before being sent out. This can be useful if your gist contains any invalid UTF-8 sequences. [gfm]:http://github.github.com/github-flavored-markdown/ [git-diff]: http://git-scm.com/docs/git-diff diff --git a/content/v3/meta.md b/content/v3/meta.md index 908e6c64a6..6ba388351d 100644 --- a/content/v3/meta.md +++ b/content/v3/meta.md @@ -1,11 +1,18 @@ --- -title: Meta | GitHub API +title: Meta --- # Meta +{% if page.version == 'dotcom' %} + This endpoint provides information about GitHub.com, the service. -Or, if you access this endpoint on your organization's [GitHub Enterprise](https://enterprise.github.com/) installation, this endpoint provides information about that installation. + +{% else %} + +If you access this endpoint on your organization's [GitHub Enterprise](https://enterprise.github.com/) installation, this endpoint provides information about that installation. + +{% endif %} GET /meta @@ -18,6 +25,9 @@ Or, if you access this endpoint on your organization's [GitHub Enterprise](https Name | Type | Description -----|------|-------------- +`verifiable_password_authentication`|`boolean` | Whether authentication with username and password is supported. {% if page.version != 'dotcom' %}GitHub Enterprise instances using CAS or OAuth for authentication will return `false`. Features like [Basic Authentication with a username and password](/v3/auth/#via-username-and-password), [sudo mode](https://help.github.com/articles/sudo-mode), and [two-factor authentication](https://help.github.com/articles/about-two-factor-authentication) are not supported on these servers.{% endif %} +`github_services_sha` | `string` | The currently-deployed SHA of [`github-services`](https://github.com/github/github-services). `hooks`|`array` of `strings` | An Array of IP addresses in CIDR format specifying the addresses that incoming service hooks will originate from on GitHub.com. Subscribe to the [API Changes blog](https://developer.github.com/changes/) or follow [@GitHubAPI](https://twitter.com/GitHubAPI) on Twitter to get updated when this list changes. `git`|`array` of `strings` | An Array of IP addresses in CIDR format specifying the Git servers for GitHub.com. -`verifiable_password_authentication`|`boolean` | Whether authentication with username and password is supported. (GitHub Enterprise instances using CAS or OAuth for authentication will return `false`. Features like [Basic Authentication with a username and password](/v3/auth/#via-username-and-password), [sudo mode](https://help.github.com/articles/sudo-mode), and [two-factor authentication](https://help.github.com/articles/about-two-factor-authentication) are not supported on these servers.) +`pages`|`array` of `strings` | An Array of IP addresses in CIDR format specifying the A records for [GitHub Pages](https://pages.github.com/). +`importer`|`array` of `strings` | An Array of IP addresses specifying the addresses that source imports will originate from on GitHub.com. diff --git a/content/v3/migration.md b/content/v3/migration.md new file mode 100644 index 0000000000..5291cd5928 --- /dev/null +++ b/content/v3/migration.md @@ -0,0 +1,29 @@ +--- +title: Migration +--- + +# Migration + +These APIs help you move projects to or from {{ site.data.variables.product.product_name }}. + +{% if page.version == 'dotcom' %} + +## [Enterprise Migrations][migrations] + +The [Enterprise Migrations API][migrations] lets you move a repository from GitHub to GitHub Enterprise. + +## [Source Imports][source_imports] + +The [Source Imports API][source_imports] lets you import a source repository to +{{ site.data.variables.product.product_name }}. + +{% else %} + +The migration APIs are only available on github.com. To learn more about migration, +read the [API documentation on github.com](https://developer.github.com/v3/migration/) +or check out the [Enterprise Migration Guide](https://help.github.com/enterprise/admin/guides/migrations/). + +{% endif %} + +[migrations]: /v3/migration/migrations/ +[source_imports]: /v3/migration/source_imports/ diff --git a/content/v3/migration/migrations.md b/content/v3/migration/migrations.md new file mode 100644 index 0000000000..be76e44e2e --- /dev/null +++ b/content/v3/migration/migrations.md @@ -0,0 +1,115 @@ +--- +title: Migrations +--- + +# Migrations + +{:toc} + +The Migrations API *is only available to [authenticated](https://developer.github.com/v3/#authentication) organization [owners](https://help.github.com/articles/permission-levels-for-an-organization/)*. + +{% if page.version != 'dotcom' %} + +{{#warning}} + +This API is not currently available on GitHub Enterprise. + +{{/warning}} + +{% endif %} + +{{#tip}} + + To access the Migrations API, you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.wyandotte-preview+json + +{{/tip}} + +## Start a migration + +Initiates the generation of a migration archive. + + POST /orgs/:org/migrations + +### Parameters + +Name | Type | Description +--------|---------|-------------- +`repositories` | `array` of `strings` | **Required**. A list of arrays indicating which repositories should be migrated. +`lock_repositories`|`boolean` | Indicates whether repositories should be locked (to prevent manipulation) while migrating data. Default: `false`. +`exclude_attachments`|`boolean` | Indicates whether attachments should be excluded from the migration (to reduce migration archive file size). Default: `false`. + +### Example + +<%= json \ + :repositories => ["octocat/Hello-World"], + :lock_repositories => true +%> + +### Response + +<%= headers 201 %> +<%= json(:migrations) %> + +## Get a list of migrations + +Lists the most recent migrations. + + GET /orgs/:org/migrations + +### Response + +<%= headers 200, :pagination => default_pagination_rels %> +<%= json(:migrations) { |h| [h] } %> + +## Get the status of a migration + +Fetches the status of a migration. + + GET /orgs/:org/migrations/:id + +### Response + +The `state` of a migration can be one of the following values: + +* `pending`, which means the migration hasn't started yet. +* `exporting`, which means the migration is in progress. +* `exported`, which means the migration finished successfully. +* `failed`, which means the migration failed. + +<%= headers 200 %> +<%= json(:migrations) { |h| h['state'] = 'exported'; h } %> + +## Download a migration archive + +Fetches the URL to a migration archive. + + GET /orgs/:org/migrations/:id/archive + +### Response + +<%= headers 302 %> +
+https://s3.amazonaws.com/github-cloud/migration/79/67?response-content-disposition=filename%3D0b989ba4-242f-11e5-81e1.tar.gz&response-content-type=application/x-gzip
++
Deprecation Notice
+ +
+ The token attribute is deprecated in all
+ of the following OAuth Authorizations API responses:
+
-
+
- List your authorizations +
- Get a single authorization +
- Get-or-create an authorization for a specific app -
tokenis still returned for "create"
+ {% if page.version == 'dotcom' or page.version > 2.2 %}
+ - Get-or-create an authorization for a specific app and fingerprint -
tokenis still returned for "create"
+ {% endif %}
+ - Update an existing authorization +
+ To reduce the impact of removing the token value,
+ the OAuth Authorizations API now includes a new request attribute
+ (fingerprint), three new response attributes
+ (token_last_eight, hashed_token, and
+ fingerprint), and
+ one new endpoint.
+
+ To reduce the impact of removing the token value,
+ the OAuth Authorizations API now includes a new request attribute
+ (fingerprint) and three new response attributes
+ (token_last_eight, hashed_token, and
+ fingerprint).
+
+ This functionality became the default for all requests on April 20, 2015. Please see the blog post for full details. +
+* `2fa_disabled`: Members without [two-factor authentication][2fa-blog] enabled. Available for owners of organizations with private repositories.
* `all`: All members the authenticated user can see.
Default: `all` +`filter`|`string` | Filter members returned in the list. Can be one of:
* `2fa_disabled`: Members without [two-factor authentication][2fa-blog] enabled. Available for organization owners.
* `all`: All members the authenticated user can see.
Default: `all` +`role` |`string` | Filter members returned by their role. Can be one of:
* `all`: All members of the organization, regardless of role.
* `admin`: Organization owners.
* `member`: Non-owner organization members. {% if page.version != 'dotcom' and page.version == 2.4 %}This option requires a custom media type to be specified. Please see more in the alert below.**{% endif %}
Default: `all` [2fa-blog]: https://github.com/blog/1614-two-factor-authentication +{% if page.version != 'dotcom' and page.version > 2.3 and page.version < 2.6 %} + +{{#tip}} + +We're currently offering a preview period allowing applications to opt in to the Organization Permissions API. Please see [the blog post](/changes/2015-06-24-api-enhancements-for-working-with-organization-permissions/) for full details. + +To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + +``` +application/vnd.github.ironman-preview+json +``` + +{{/tip}} + +{% endif %} + ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:user) { |h| [h] } %> ### Response if requester is not an organization member @@ -38,7 +54,7 @@ Name | Type | Description Check if a user is, publicly or privately, a member of the organization. - GET /orgs/:org/members/:user + GET /orgs/:org/members/:username ### Response if requester is an organization member and user is a member @@ -58,15 +74,24 @@ Check if a user is, publicly or privately, a member of the organization. ## Add a member -To add someone as a member to an org, you must add them to a -[team](/v3/orgs/teams/#add-team-member). +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +To add someone as a member to an organization, you must +[invite them to the organization](/v3/orgs/members/#add-or-update-organization-membership) +or [invite them to a team](/v3/orgs/teams/#add-team-membership). + +{% else %} + +To add someone as a member to an organization, you must add them to a [team](/v3/orgs/teams/#add-team-member). + +{% endif %} ## Remove a member Removing a user from this list will remove them from all teams and they will no longer have any access to the organization's repositories. - DELETE /orgs/:org/members/:user + DELETE /orgs/:org/members/:username ### Response @@ -81,12 +106,12 @@ publicized or not. ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:user) { |h| [h] } %> ## Check public membership - GET /orgs/:org/public_members/:user + GET /orgs/:org/public_members/:username ### Response if user is a public member @@ -101,7 +126,9 @@ publicized or not. The user can publicize their own membership. (A user cannot publicize the membership for another user.) - PUT /orgs/:org/public_members/:user + PUT /orgs/:org/public_members/:username + +<%= fetch_content(:put_content_length) %> ### Response @@ -109,8 +136,146 @@ The user can publicize their own membership. ## Conceal a user's membership - DELETE /orgs/:org/public_members/:user + DELETE /orgs/:org/public_members/:username ### Response <%= headers 204 %> + +## Get organization membership + +{% if page.version == 'dotcom' or page.version >= 2.6 %} + +In order to get a user's membership with an organization, the authenticated user must be an organization member. + +{% elsif page.version >= 2.4 %} + +In order to get a user's membership with an organization, the authenticated user must be an organization owner. + +{% else %} + +In order to get a user's membership with an organization, the authenticated user must be an organization admin. + +{% endif %} + + GET /orgs/:org/memberships/:username + +### Response if user has an active admin membership with organization + +<%= headers 200 %> +<%= json(:active_admin_org_membership) %> + +### Response if user has an active membership with organization + +<%= headers 200 %> +<%= json(:active_limited_org_membership) %> + +### Response if user has a pending membership with organization + +<%= headers 200 %> +<%= json(:pending_limited_org_membership) %> + +## Add or update organization membership + +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +In order to create or update a user's membership with an organization, the authenticated user must be an organization owner. + +{% else %} + +In order to create or update a user's membership with an organization, the authenticated user must be an organization admin. + +{% endif %} + + PUT /orgs/:org/memberships/:username + +### Parameters + +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +Name | Type | Description +------|--------|-------------- +`role`|`string`| **Required**. The role to give the user in the organization. Can be one of:
* `admin` - The user will become an owner of the organization.
* `member` - The user will become a non-owner member of the organization. + +{% else %} + +Name | Type | Description +------|--------|-------------- +`role`|`string`| **Required**. The role to give the user in the organization. Can be one of:
* `admin` - The user will become an administrator of the organization.
* `member` - The user will become a non-admin member of the organization. Use this only to demote an existing admin to a non-admin. + +{% endif %} + +### Response if user was previously unaffiliated with organization + +<%= headers 200 %> +<%= json(:pending_admin_org_membership) %> + +### Response if user already had membership with organization + +<%= headers 200 %> +<%= json(:active_admin_org_membership) %> + +## Remove organization membership + +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +In order to remove a user's membership with an organization, the authenticated user must be an organization owner. + +{% else %} + +In order to remove a user's membership with an organization, the authenticated user must be an organization admin. + +{% endif %} + + DELETE /orgs/:org/memberships/:username + +If the specified user is an active member of the organization, this will remove them from the organization. If the specified user has been invited to the organization, this will cancel their invitation. + +### Response + +<%= headers 204 %> + +## List your organization memberships + + GET /user/memberships/orgs + +### Input + +Name | Type | Description +-----|------|-------------- +`state`|`string`| Indicates the state of the memberships to return. Can be either `active` or `pending`. If not specified, both active and pending memberships are returned. + +### Response + +<%= headers 200, :pagination => default_pagination_rels %> +<%= json(:org_memberships) %> + +## Get your organization membership + + GET /user/memberships/orgs/:org + +### Response + +<%= headers 200 %> +<%= json(:pending_admin_org_membership) %> + +## Edit your organization membership + + PATCH /user/memberships/orgs/:org + +### Input + +Name | Type | Description +-----|------|-------------- +`state`|`string`| **Required**. The state that the membership should be in. Only `"active"` will be accepted. + +### Example + +<%= json \ + :state => "active" + %> + +### Response + +<%= headers 200 %> +<%= json(:active_admin_org_membership) %> diff --git a/content/v3/orgs/pre_receive_hooks.md b/content/v3/orgs/pre_receive_hooks.md new file mode 100644 index 0000000000..7d3afc0bd4 --- /dev/null +++ b/content/v3/orgs/pre_receive_hooks.md @@ -0,0 +1,83 @@ +--- +title: Organization Pre-receive Hooks +--- + +# Organization Pre-receive Hooks (Enterprise) + +{{#tip}} + + + + APIs for managing pre-receive hooks are currently available for developers to preview. + During the preview period, the APIs may change without advance notice. + + To access the API you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.eye-scream-preview + +{{/tip}} + +{:toc} + +The Organization Pre-receive Hooks API allows you to view and modify +enforcement of the pre-receive hooks that are available to an organization. + +Prefix all the endpoints for this API with the following URL: + +``` command-line +http(s)://hostname/api/v3 +``` + +## Object attributes + +| Name | Type | Description | +|----------------------------------|-----------|-----------------------------------------------------------| +| `name` | `string` | The name of the hook. | +| `enforcement` | `string` | The state of enforcement for the hook on this repository. | +| `allow_downstream_configuration` | `boolean` | Whether repositories can override enforcement. | +| `configuration_url` | `string` | URL for the endpoint where enforcement is set. | + +Possible values for *enforcement* are `enabled`, `disabled` and`testing`. `disabled` indicates the pre-receive hook will not run. `enabled` indicates it will run and reject +any pushes that result in a non-zero status. `testing` means the script will run but will not cause any pushes to be rejected. + +`configuration_url` may be a link to this endpoint or this hook's global +configuration. Only site admins are able to access the global configuration. + +## List pre-receive hooks + +List all pre-receive hooks that are enabled or testing for this +organization as well as any disabled hooks that can be configured at the +organization level. Globally disabled pre-receive hooks that do not allow +downstream configuration are not listed. + + GET /orgs/:org/pre-receive-hooks + +<%= headers 200, :pagination => default_pagination_rels %> +<%= json :pre_receive_hooks_org %> + +## Get a single pre-receive hook + + GET /orgs/:org:pre-receive-hooks/:id + +<%= headers 200 %> <%= json :pre_receive_hook_org %> + +## Update pre-receive hook enforcement + +For pre-receive hooks which are allowed to be configured at the org level, you can set +`enforcement` and `allow_downstream_configuration` + + PATCH /orgs/:org/pre-receive-hooks/:id + +<%= json :enforcement => "enabled", :allow_downstream_configuration => false %> + +### Response + +<%= headers 200 %><%= json :pre_receive_hook_org_update %> + +## Remove enforcment overrides for a pre-receive hook + +Removes any overrides for this hook at the org level for this org. + + DELETE /orgs/:org/pre-receive-hooks/:id + +<%= headers 200 %> <%= json :pre_receive_hook_org %> diff --git a/content/v3/orgs/teams.md b/content/v3/orgs/teams.md index 769205208c..07a233bea9 100644 --- a/content/v3/orgs/teams.md +++ b/content/v3/orgs/teams.md @@ -1,10 +1,9 @@ --- -title: Organization Teams | GitHub API +title: Organization Teams --- # Teams -* TOC {:toc} All actions against teams require at a minimum an authenticated user who @@ -17,7 +16,7 @@ OAuth users require the "read:org" [scope](/v3/oauth/#scopes). ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:team) { |h| [h] } %> ## Get team @@ -31,26 +30,74 @@ OAuth users require the "read:org" [scope](/v3/oauth/#scopes). ## Create team -In order to create a team, the authenticated user must be an owner of -`:org`. +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +In order to create a team, the authenticated user must be a member of `:org`. + +{% else %} + +In order to create a team, the authenticated user must be an owner of `:org`. + +{% endif %} POST /orgs/:org/teams ### Parameters -Name | Type | Description +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +Name | Type | Description +-----|------|-------------- +`name`|`string` | **Required**. The name of the team. +`description`|`string` | The description of the team. +`repo_names`|`array` of `strings` | The full name (e.g., "organization-name/repository-name") of repositories to add the team to. +`privacy`|`string`| The level of privacy this team should have. Can be one of:
* `secret` - only visible to organization owners and members of this team.
* `closed` - visible to all members of this organization.
Default: `secret`
{% if page.version != 'dotcom' and page.version == 2.4 %}**This parameter requires a custom media type to be specified. Please see more in the alert below.**{% endif %} +`permission`|`string` | **Deprecated**. The permission that new repositories will be added to the team with when none is specified. Can be one of:
* `pull` - team members can pull, but not push to or administer newly-added repositories.
* `push` - team members can pull and push, but not administer newly-added repositories.
* `admin` - team members can pull, push and administer newly-added repositories.
Default: `pull` + +{% if page.version != 'dotcom' and page.version > 2.3 and page.version < 2.6 %} + +{{#tip}} + +We're currently offering a preview period allowing applications to opt in to the Organization Permissions API. Please see the [blog post](/changes/2015-06-24-api-enhancements-for-working-with-organization-permissions/) for full details. + +To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + +``` +application/vnd.github.ironman-preview+json +``` + +**Warning:** If you specify the `privacy` attribute on an organization that hasn't had [improved organization permissions](https://github.com/blog/2020-improved-organization-permissions) enabled yet, you will get a `422` error response. + +{{/tip}} + +{% endif %} + +#### Example + +<%= json \ + :name => 'new team', + :description => 'team description', + :privacy => 'closed' %> + +{% else %} + +Name | Type | Description -----|------|-------------- `name`|`string` | **Required**. The name of the team. -`repo_names`|`array` of `strings` | The repositories to add the team to. +`description`|`string` | The description of the team. +`repo_names`|`array` of `strings` | The full name (e.g., "organization-name/repository-name") of repositories to add the team to. `permission`|`string` | The permission to grant the team. Can be one of:
* `pull` - team members can pull, but not push to or administer these repositories.
* `push` - team members can pull and push, but not administer these repositories.
* `admin` - team members can pull, push and administer these repositories.
Default: `pull` #### Example <%= json \ :name => 'new team', + :description => 'team description', :permission => 'push', :repo_names => ['github/dotfiles'] %> +{% endif %} + ### Response <%= headers 201 %> @@ -58,24 +105,74 @@ Name | Type | Description ## Edit team -In order to edit a team, the authenticated user must be an owner of -the org that the team is associated with. +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +In order to edit a team, the authenticated user must either be an owner of +the org that the team is associated with, or a maintainer of the team. + +{% else %} + +In order to edit a team, the authenticated user must be an owner of the org that the team is associated with. + +{% endif %} PATCH /teams/:id +{% if page.version == 'dotcom' or page.version >= 2.4 %} + ### Parameters -Name | Type | Description +Name | Type | Description -----|------|-------------- `name`|`string` | **Required**. The name of the team. +`description`|`string` | The description of the team. +`privacy`|`string`| The level of privacy this team should have. Can be one of:
* `secret` - only visible to organization owners and members of this team.
* `closed` - visible to all members of this organization.
Default: `secret`
{% if page.version != 'dotcom' and page.version == 2.4 %}**This parameter requires a custom media type to be specified. Please see more in the alert below.**{% endif %} +`permission`|`string` | **Deprecated**. The permission that new repositories will be added to the team with when none is specified. Can be one of:
* `pull` - team members can pull, but not push to or administer newly-added repositories.
* `push` - team members can pull and push, but not administer newly-added repositories.
* `admin` - team members can pull, push and administer newly-added repositories.
Default: `pull` + +{% if page.version != 'dotcom' and page.version > 2.3 and page.version < 2.6 %} + +{{#tip}} + +We're currently offering a preview period allowing applications to opt in to the Organization Permissions API. Please see the [blog post](/changes/2015-06-24-api-enhancements-for-working-with-organization-permissions/) for full details. + +To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + +``` +application/vnd.github.ironman-preview+json +``` + +**Warning:** If you specify the `privacy` attribute on an organization that hasn't had [improved organization permissions](https://github.com/blog/2020-improved-organization-permissions) enabled yet, you will get a `422` error response. + +{{/tip}} + +{% endif %} + +#### Example + +<%= json \ + :name => 'new team name', + :description => 'new team description', + :privacy => 'closed' %> + +{% else %} + +### Parameters + +Name | Type | Description +-----|------|-------------- +`name`|`string` | **Required**. The name of the team. +`description`|`string` | The description of the team. `permission`|`string` | The permission to grant the team. Can be one of:
* `pull` - team members can pull, but not push to or administer these repositories.
* `push` - team members can pull and push, but not administer these repositories.
* `admin` - team members can pull, push and administer these repositories. Default: `pull` #### Example <%= json \ :name => 'new team name', + :description => 'new team description', :permission => 'push' %> +{% endif %} + ### Response <%= headers 200 %> @@ -84,7 +181,7 @@ Name | Type | Description ## Delete team In order to delete a team, the authenticated user must be an owner of -the org that the team is associated with. +the org that the team is associated with{% if page.version == 'dotcom' or page.version >= 2.4 %}, or a maintainer of the team{% endif %}. DELETE /teams/:id @@ -94,22 +191,66 @@ the org that the team is associated with. ## List team members -In order to list members in a team, the authenticated user must be a -member of the team. +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +In order to list members in a team, the team must be visible to the +authenticated user. + +{% else %} + +In order to list members in a team, the authenticated user must be a member of the team. + +{% endif %} + +{% if page.version != 'dotcom' and page.version >= 2.3 %} + +<%= fetch_content(:if_site_admin) %> +you will be able to list all members for the team. + +{% endif %} GET /teams/:id/members +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +Name | Type | Description +-----|------|-------------- +`role`|`string`| Filters members returned by their role in the team. Can be one of:
* `member` - normal members of the team.
* `maintainer` - team maintainers.
* `all` - all members of the team.
Default: `all` + +{% endif %} + ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:user) { |h| [h] } %> ## Get team member -In order to get if a user is a member of a team, the authenticated user -must be a member of the team. +### Deprecation notice + +{{#tip}} + +The "Get team member" API (described below) is +[deprecated](/v3/versions/#v3-deprecations) and is scheduled for +removal in the next major version of the API. + +We recommend using the +[Get team membership API](/v3/orgs/teams/#get-team-membership) +instead. It allows you to get both active and pending memberships. + +{{/tip}} + +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +In order to list members in a team, the team must be visible to the authenticated user. + +{% else %} + +In order to get if a user is a member of a team, the authenticated user must be a member of the team. - GET /teams/:id/members/:user +{% endif %} + + GET /teams/:id/members/:username ### Response if user is a member @@ -121,11 +262,28 @@ must be a member of the team. ## Add team member +### Deprecation notice + +{{#tip}} + +The "Add team member" API (described below) is +[deprecated](/v3/versions/#v3-deprecations) and is scheduled for +removal in the next major version of the API. + +We recommend using the +[Add team membership API](/v3/orgs/teams/#add-team-membership) +instead. It allows you to invite new organization members to your teams. + +{{/tip}} + In order to add a user to a team, the authenticated user must have -'admin' permissions to the team or be an owner of the org that the team -is associated with. +'admin' permissions to the team or be an owner of the organization that the team +is associated with, and the user being added must already be a member of at +least one other team on the same organization. + + PUT /teams/:id/members/:username - PUT /teams/:id/members/:user +<%= fetch_content(:put_content_length) %> ### Response @@ -135,7 +293,7 @@ If you attempt to add an organization to a team, you will get this: <%= headers 422 %> <%= - json :message => "Validation Failed", + json :message => "Cannot add an organization as a member.", :errors => [{ :code => "org", :field => :user, @@ -143,14 +301,149 @@ If you attempt to add an organization to a team, you will get this: }] %> +If you attempt to add a user to a team and that user is not a member of at least +one other team on the same organization, you will get this: + +<%= headers 422 %> +<%= + json :message => "User isn't a member of this organization. Please invite them first.", + :errors => [{ + :code => "unaffiliated", + :field => :user, + :resource => :TeamMember + }] +%> + ## Remove team member +### Deprecation notice + +{{#tip}} + +The "Remove team member" API (described below) is +[deprecated](/v3/versions/#v3-deprecations) and is scheduled for +removal in the next major version of the API. + +We recommend using the +[Remove team membership API](/v3/orgs/teams/#remove-team-membership) +instead. It allows you to remove both active and pending memberships. + +{{/tip}} + In order to remove a user from a team, the authenticated user must have 'admin' permissions to the team or be an owner of the org that the team is associated with. -NOTE: This does not delete the user, it just remove them from the team. +NOTE: This does not delete the user, it just removes them from the team. - DELETE /teams/:id/members/:user + DELETE /teams/:id/members/:username + +### Response + +<%= headers 204 %> + +## Get team membership + +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +In order to get a user's membership with a team, the team must be visible to the +authenticated user. + +{% else %} + +In order to get a user's membership with a team, the authenticated user must be a member of the team or an owner of the team's organization. + +{% endif %} + + GET /teams/:id/memberships/:username + +### Response if user has an active membership with team + +<%= headers 200 %> +<%= json(:active_team_membership) %> + +### Response if user has a pending membership with team + +<%= headers 200 %> +<%= json(:pending_team_membership) %> + +### Response if user has no membership with team + +<%= headers 404 %> + +## Add team membership + +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +If the user is already a member of the team's organization, this endpoint will +add the user to the team. In order to add a membership between an organization +member and a team, the authenticated user must be an organization owner or a +maintainer of the team. + +If the user is unaffiliated with the team's organization, this endpoint will +send an invitation to the user via email. This newly-created membership will be +in the "pending" state until the user accepts the invitation, at which point the +membership will transition to the "active" state and the user will be added as a +member of the team. In order to add a membership between an unaffiliated user +and a team, the authenticated user must be an organization owner. + +{% else %} + +In order to add a membership between a user and a team, the authenticated user +must have 'admin' permissions to the team or be an owner of the organization +that the team is associated with. + +If the user is already a part of the team's organization (meaning they're on at +least one other team in the organization), this endpoint will add the user to +the team. + +If the user is completely unaffiliated with the team's organization (meaning +they're on none of the organization's teams), this endpoint will send an +invitation to the user via email. This newly-created membership will be in the +"pending" state until the user accepts the invitation, at which point the +membership will transition to the "active" state and the user will be added as a +member of the team. + +{% endif %} + + PUT /teams/:id/memberships/:username + +### Parameters + +Name | Type | Description +-----|------|-------------- +`role`|`string`| The role that this user should have in the team. Can be one of:
* `member` - a normal member of the team.
* `maintainer` - a team maintainer. Able to add/remove other team members, promote other team members to team maintainer, and edit the team's name and description.
Default: `member` + +### Response if user's membership with team is now active + +<%= headers 200 %> +<%= json(:active_team_membership) %> + +### Response if user's membership with team is now pending + +<%= headers 200 %> +<%= json(:pending_team_membership) %> + +If you attempt to add an organization to a team, you will get this: + +<%= headers 422 %> +<%= + json :message => "Cannot add an organization as a member.", + :errors => [{ + :code => "org", + :field => :user, + :resource => :TeamMember + }] +%> + +## Remove team membership + +In order to remove a membership between a user and a team, the authenticated +user must have 'admin' permissions to the team or be an owner of the +organization that the team is associated with. +NOTE: This does not delete the user, it just removes their membership from the +team. + + DELETE /teams/:id/memberships/:username ### Response @@ -160,12 +453,19 @@ NOTE: This does not delete the user, it just remove them from the team. GET /teams/:id/repos +{% if page.version != 'dotcom' and page.version >= 2.3 %} + +<%= fetch_content(:if_site_admin) %> +you will be able to list all repositories for the team. + +{% endif %} + ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:repo) { |h| [h] } %> -## Check if a team manages a repository {#get-team-repo} +## Check if a team manages a repository GET /teams/:id/repos/:owner/:repo @@ -177,15 +477,69 @@ NOTE: This does not delete the user, it just remove them from the team. <%= headers 404 %> -## Add team repository {#add-team-repo} +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +### Alternative response with extra repository information + +You can also get information about the specified repository, including what +permissions the team grants on it, by passing the following custom +[media type](/v3/media/) via the `Accept` header: + + Accept: application/vnd.github.v3.repository+json + +{% endif %} + +<%= headers 200 %> +<%= json :repo %> + +## Add or update team repository + +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +In order to add a repository to a team or update the team's permission on a repository, the authenticated user must have admin access to the repository, and must be able to see the team. Also, the repository must be owned by the organization, or a direct fork of a repository owned by the organization. + +{% else %} -In order to add a repository to a team, the authenticated user must be an -owner of the org that the team is associated with. Also, the repository must -be owned by the organization, or a direct fork of a repository owned by the +In order to add a repository to a team, the authenticated user must have admin +access to the repository, and must be able to see the team. Also, the repository +must be owned by the organization, or a direct fork of a repository owned by the organization. +{% endif %} + PUT /teams/:id/repos/:org/:repo +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +### Parameters + +Name | Type | Description +-----|------|-------------- +`permission`|`string` | The permission to grant the team on this repository. Can be one of:
* `pull` - team members can pull, but not push to or administer this repository.
* `push` - team members can pull and push, but not administer this repository.
* `admin` - team members can pull, push and administer this repository.
If no permission is specified, the team's `permission` attribute will be used to determine what permission to grant the team on this repository. + +<%= fetch_content(:optional_put_content_length) %> + +{% endif %} + + +{% if page.version != 'dotcom' and page.version > 2.3 and page.version < 2.6 %} + +{{#tip}} + +We're currently offering a preview period allowing applications to opt in to the Organization Permissions API. Please see the [blog post](/changes/2015-06-24-api-enhancements-for-working-with-organization-permissions/) for full details. + +To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + +``` +application/vnd.github.ironman-preview+json +``` + +**Warning:** If you specify the `permission` attribute on an organization that hasn't had [improved organization permissions](https://github.com/blog/2020-improved-organization-permissions) enabled yet, you will get a `422` error response. + +{{/tip}} + +{% endif %} + ### Response <%= headers 204 %> @@ -202,14 +556,22 @@ organization, you get: :resource => :TeamMember}] %> -## Remove team repository {#remove-team-repo} + + +## Remove team repository -In order to remove a repository from a team, the authenticated user must be an -owner of the org that the team is associated with. Also, since the Owners team -always has access to all repositories in the organization, repositories cannot -be removed from the Owners team. +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +In order to remove a repository from a team, the authenticated user must have +admin access to the repository or be a maintainer of the team. NOTE: This does not delete the repository, it just removes it from the team. +{% else %} + +In order to remove a repository from a team, the authenticated user must be an owner of the org that the team is associated with. Also, since the Owners team always has access to all repositories in the organization, repositories cannot be removed from the Owners team. + +{% endif %} + DELETE /teams/:id/repos/:owner/:repo ### Response @@ -219,14 +581,14 @@ NOTE: This does not delete the repository, it just removes it from the team. ## List user teams List all of the teams across all of the organizations to which the -authenticated user belongs. This method requires `user` or `repo` -[scope][] when authenticating via [OAuth][]. +authenticated user belongs. This method requires `user`, `repo`, or +`read:org` [scope][] when authenticating via [OAuth][]. GET /user/teams ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:full_team) { |h| [h] } %> [OAuth]: /v3/oauth/ diff --git a/content/v3/pulls.md b/content/v3/pulls.md index 44f7566398..332c98ff3d 100644 --- a/content/v3/pulls.md +++ b/content/v3/pulls.md @@ -1,10 +1,9 @@ --- -title: Pull Requests | GitHub API +title: Pull Requests --- # Pull Requests -* TOC {:toc} The Pull Request API allows you to list, view, edit, create, and even merge @@ -42,12 +41,11 @@ Name | Type | Description `head`|`string` | Filter pulls by head user and branch name in the format of `user:ref-name`. Example: `github:new-script-format`. `base`|`string` | Filter pulls by base branch name. Example: `gh-pages`. `sort`|`string`| What to sort results by. Can be either `created`, `updated`, `popularity` (comment count) or `long-running` (age, filtering by pulls updated in the last month). Default: `created` -`direction`|`string`| The direction of the sort. Can be either `asc` or `desc`. Default: `desc` - +`direction`|`string`| The direction of the sort. Can be either `asc` or `desc`. Default: `desc` when sort is `created` or sort is not specified, otherwise `asc`. ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:pull) { |h| [h] } %> ## Get a single pull request @@ -56,12 +54,9 @@ Name | Type | Description ### Response -<%= headers 200 %> -<%= json :full_pull %> - -### Mergability +{{#tip}} -Each time the pull request receives new commits, GitHub creates a merge commit +Each time the pull request receives new commits, {{ site.data.variables.product.product_name }} creates a merge commit to _test_ whether the pull request can be automatically merged into the base branch. (This _test_ commit is not added to the base branch or the head branch.) The `merge_commit_sha` attribute holds the SHA of the _test_ merge commit; @@ -69,10 +64,19 @@ however, this attribute is [deprecated](/v3/versions/#v3-deprecations) and is sc removal in the next version of the API. The Boolean `mergeable` attribute will remain to indicate whether the pull request can be automatically merged. -### Alternative Response Formats +The value of the `mergeable` attribute can be `true`, `false`, or `null`. If +the value is `null`, this means that the mergeability hasn't been computed yet, +and a background job was started to compute it. Give the job a few moments to +complete, and then submit the request again. When the job is complete, the +response will include a non-`null` value for the `mergeable` attribute. + +{{/tip}} Pass the appropriate [media type](/v3/media/#commits-commit-comparison-and-pull-requests) to fetch diff and patch formats. +<%= headers 200 %> +<%= json :full_pull %> + ## Create a pull request POST /repos/:owner/:repo/pulls @@ -83,7 +87,7 @@ Name | Type | Description -----|------|------------- `title`|`string` | **Required**. The title of the pull request. `head`|`string` | **Required**. The name of the branch where your changes are implemented. For cross-repository pull requests in the same network, namespace `head` with a user like this: `username:branch`. -`base`|`string` | **Required**. The name of the branch you want your changes pulled into. This should be an existing branch on the current repository. You cannot submit a pull request to one repository that requests a merge to a base of another repository. +`base`|`string` | **Required**. The name of the branch you want the changes pulled into. This should be an existing branch on the current repository. You cannot submit a pull request to one repository that requests a merge to a base of another repository. `body`|`string` | The contents of the pull request. @@ -103,19 +107,19 @@ Issue number instead of `title` and `body`. Name | Type | Description -----|------|-------------- -`issue`|`number` | **Required**. The issue number in this repository to turn into a Pull Request. +`issue`|`integer` | **Required**. The issue number in this repository to turn into a Pull Request. #### Example <%= json \ - :issue => "5", + :issue => 5, :head => "octocat:new-feature", :base => "master" %> ### Response -<%= headers 201, :Location => "https://api.github.com/user/repo/pulls/1" %> +<%= headers 201, :Location => get_resource(:pull)['url'] %> <%= json :pull %> ## Update a pull request @@ -128,14 +132,18 @@ Name | Type | Description -----|------|-------------- `title`|`string` | The title of the pull request. `body`|`string` | The contents of the pull request. -`state`|`string` | State of this Pull Request. Either `open` or `closed`. +`state`|`string` | State of this Pull Request. Either `open` or `closed`.{% if page.version == 'dotcom' or page.version >= 2.8 %} +`base`|`string` | The name of the branch you want your changes pulled into. This should be an existing branch on the current repository. You cannot update the base branch on a pull request to point to another repository. +{% endif %} #### Example <%= json \ :title => "new title", :body => "updated body", - :state => "open" + :state => "open"{% if page.version == 'dotcom' or page.version >= 2.8 %}, + :base => "master" +{% endif %} %> ### Response @@ -149,7 +157,7 @@ Name | Type | Description ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:commit) { |h| [h] } %> Note: The response includes a maximum of 250 commits. If you are working with a pull request larger than that, you can use the [Commit List API](/v3/repos/commits/#list-commits-on-a-repository) to enumerate all commits in the pull request. @@ -160,7 +168,7 @@ Note: The response includes a maximum of 250 commits. If you are working with a ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:file) { |h| [h] } %> ## Get if a pull request has been merged @@ -183,8 +191,26 @@ Note: The response includes a maximum of 250 commits. If you are working with a Name | Type | Description -----|------|------------- -`commit_message`|`string`| The message that will be used for the merge commit +{% if page.version == 'dotcom' or page.version >= 2.6 %}`commit_title`|`string`| Title for the automatic commit message.{% endif %} +`commit_message`|`string`| Extra detail to append to automatic commit message. +`sha`|`string`| SHA that pull request head must match to allow merge +{% if page.version == 'dotcom' or page.version >= 2.6 %}`squash`|`boolean`| Commit a single commit to the head branch.{% endif %} +{% if page.version == 'dotcom' or page.version >= 2.6 %} + +{{#tip}} + +The `commit_title` and `squash` parameters are currently available for developers to preview. During the preview period, the API may change without advance notice. Please see the [blog post](/changes/2016-04-01-squash-api-preview) for full details. + +To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + +``` +application/vnd.github.polaris-preview+json +``` + +{{/tip}} + +{% endif %} ### Response if merge was successful @@ -199,11 +225,22 @@ Name | Type | Description <%= headers 405 %> <%= json \ - :sha => nil, - :merged => false, - :message => 'Failure reason' + :message => "Pull Request is not mergeable", + :documentation_url => "https://developer.github.com/v3/pulls/#merge-a-pull-request-merge-button" +%> + +### Response if sha was provided and pull request head did not match + +<%= headers 409 %> +<%= json \ + :message => "Head branch was modified. Review and try the merge again.", + :documentation_url => "https://developer.github.com/v3/pulls/#merge-a-pull-request-merge-button" %> +## Labels, assignees, and milestones + +Every pull request is an issue, but not every issue is a pull request. For this reason, "shared" actions for both features, like manipulating assignees, labels and milestones, are provided within [the Issues API](/v3/issues). + ## Custom media types These are the supported media types for pull requests. You can read more about the @@ -213,3 +250,9 @@ use of media types in the API [here](/v3/media/). application/vnd.github.VERSION.text+json application/vnd.github.VERSION.html+json application/vnd.github.VERSION.full+json + application/vnd.github.VERSION.diff + application/vnd.github.VERSION.patch + + + +If a diff is corrupt, contact {{ site.data.variables.contact.contact_support }} to receive help. Be sure to include the repository name and pull request ID. diff --git a/content/v3/pulls/comments.md b/content/v3/pulls/comments.md index 8554349576..fa543427ab 100644 --- a/content/v3/pulls/comments.md +++ b/content/v3/pulls/comments.md @@ -1,10 +1,9 @@ --- -title: Review Comments | GitHub API +title: Review Comments --- # Review Comments -* TOC {:toc} Pull Request Review Comments are comments on a portion of the unified @@ -22,9 +21,30 @@ types](#custom-media-types). You can read more about the use of media types in t ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:pull_comment) { |h| [h] } %> +{% if page.version == 'dotcom' %} +#### Reactions summary + +{{#tip}} + + + + An additional `reactions` object in the review comment payload is currently available for developers to preview. + During the preview period, the APIs may change without advance notice. + Please see the [blog post](/changes/2016-05-12-reactions-api-preview) for full details. + + To access the API you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.squirrel-girl-preview + + The `reactions` key will have the following payload where `url` can be used to construct the API location for [listing and creating](/v3/reactions) reactions. + +{{/tip}} +<%= json :pull_comment_reaction_summary %> +{% endif %} + ## List comments in a repository GET /repos/:owner/:repo/pulls/comments @@ -42,18 +62,60 @@ Name | Type | Description ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:pull_comment) { |h| [h] } %> +{% if page.version == 'dotcom' %} +#### Reactions summary + +{{#tip}} + + + + An additional `reactions` object in the review comment payload is currently available for developers to preview. + During the preview period, the APIs may change without advance notice. + Please see the [blog post](/changes/2016-05-12-reactions-api-preview) for full details. + + To access the API you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.squirrel-girl-preview + + The `reactions` key will have the following payload where `url` can be used to construct the API location for [listing and creating](/v3/reactions) reactions. + +{{/tip}} +<%= json :pull_comment_reaction_summary %> +{% endif %} + ## Get a single comment - GET /repos/:owner/:repo/pulls/comments/:number + GET /repos/:owner/:repo/pulls/comments/:id ### Response <%= headers 200 %> <%= json :pull_comment %> +{% if page.version == 'dotcom' %} +#### Reactions summary + +{{#tip}} + + + + An additional `reactions` object in the review comment payload is currently available for developers to preview. + During the preview period, the APIs may change without advance notice. + Please see the [blog post](/changes/2016-05-12-reactions-api-preview) for full details. + + To access the API you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.squirrel-girl-preview + + The `reactions` key will have the following payload where `url` can be used to construct the API location for [listing and creating](/v3/reactions) reactions. + +{{/tip}} +<%= json :pull_comment_reaction_summary %> +{% endif %} + ## Create a comment POST /repos/:owner/:repo/pulls/:number/comments @@ -65,8 +127,15 @@ Name | Type | Description `body`|`string` | **Required**. The text of the comment `commit_id`|`string` | **Required**. The SHA of the commit to comment on. `path`|`string` | **Required**. The relative path of the file to comment on. -`position`|`number` | **Required**. The line index in the diff to comment on. +`position`|`integer` | **Required**. The line index in the diff to comment on. + +{{#tip}} + +When passing the `commit_id`, use the SHA of the latest commit in the pull request or your comment may appear as "outdated" if the specified `position` has been modified in a subsequent commit. + +To comment on a specific line in a file, you will need to first determine the position in the diff. GitHub offers a `application/vnd.github.v3.diff` media type which you can use in a preceding request to view the pull request's diff. The diff needs to be [interpreted](https://en.wikipedia.org/wiki/Diff_utility#Unified_format) to translate from the *line in the file* to a *position in the diff*. The `position` value is the number of lines down from the first "@@" hunk header in the file you would like to comment on. The line just below the "@@" line is position 1, the next line is position 2, and so on. The position in the file's diff continues to increase through lines of whitespace and additional hunks until a new file is reached. +{{/tip}} #### Example @@ -85,7 +154,7 @@ an existing Pull Request Comment like this: Name | Type | Description -----|------|-------------- `body`|`string` | **Required**. The text of the comment -`in_reply_to`|`number` | **Required**. The comment id to reply to. +`in_reply_to`|`integer` | **Required**. The comment id to reply to. #### Example @@ -97,14 +166,12 @@ Name | Type | Description ### Response -<%= headers 201, - :Location => -"https://api.github.com/repos/octocat/Hello-World/pulls/comments/1" %> +<%= headers 201, :Location => get_resource(:pull_comment)['url'] %> <%= json :pull_comment %> ## Edit a comment - PATCH /repos/:owner/:repo/pulls/comments/:number + PATCH /repos/:owner/:repo/pulls/comments/:id ### Input @@ -126,7 +193,7 @@ Name | Type | Description ## Delete a comment - DELETE /repos/:owner/:repo/pulls/comments/:number + DELETE /repos/:owner/:repo/pulls/comments/:id ### Response diff --git a/content/v3/rate_limit.md b/content/v3/rate_limit.md index 83288c934a..cb27f21b3b 100644 --- a/content/v3/rate_limit.md +++ b/content/v3/rate_limit.md @@ -1,7 +1,9 @@ --- -title: Rate Limit | GitHub API +title: Rate Limit --- +{% if page.version == 'dotcom' %} + # Rate Limit The overview documentation describes the [rate limit rules](/v3/#rate-limiting). @@ -25,7 +27,7 @@ Note: Accessing this endpoint does not count against your rate limit. <%= json :resources => { :core => {:limit => 5000, :remaining => 4999, :reset => 1372700873}, - :search => {:limit => 20, :remaining => 18, :reset => 1372697452}, + :search => {:limit => 30, :remaining => 18, :reset => 1372697452}, }, :rate => {:limit => 5000, :remaining => 4999, :reset => 1372700873} %> @@ -36,16 +38,18 @@ Note: Accessing this endpoint does not count against your rate limit. The Search API has a [custom rate limit](/v3/search/#rate-limit), separate from the rate limit governing the rest of the API. For that reason, the response (shown above) categorizes your rate limit by resource. Within the `"resources"` -hash, the `"search"` hash provides your rate limit status for the -[Search API](/v3/search). The `"core"` hash provides your rate limit status for +object, the `"search"` object provides your rate limit status for the +[Search API](/v3/search). The `"core"` object provides your rate limit status for all the _rest_ of the API. #### Deprecation Notice -The `"rate"` hash (shown at the bottom of the response above) is +The `"rate"` object (shown at the bottom of the response above) is [deprecated](/v3/versions/#v3-deprecations) and is scheduled for removal in the next version of the API. If you're writing new API client code (or updating your existing code), you -should use the `"core"` hash instead of the `"rate"` hash. The `"core"` hash -contains the same information that is present in the `"rate"` hash. +should use the `"core"` object instead of the `"rate"` object. The `"core"` object +contains the same information that is present in the `"rate"` object. + +{% endif %} diff --git a/content/v3/reactions.md b/content/v3/reactions.md new file mode 100644 index 0000000000..d8effc8a38 --- /dev/null +++ b/content/v3/reactions.md @@ -0,0 +1,208 @@ +--- +title: Reactions +--- + +{% if page.version == 'dotcom' or page.version >= 2.7 %} + +# Reactions + +{{#tip}} + + + + APIs for managing reactions are currently available for developers to preview. + During the preview period, the APIs may change without advance notice. + Please see the [blog post](/changes/2016-05-12-reactions-api-preview) for full details. + + To access the API you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.squirrel-girl-preview + +{{/tip}} + +{:toc} + + +## Reaction types + + When creating a reaction, the allowed values for the `content` parameter are as follows (with the corresponding emoji for reference): + +content | emoji +-----|------ +`+1` | :+1: +`-1` | :-1: +`laugh` | :smile: +`confused` | :confused: +`heart` | :heart: +`hooray` | :tada: + + +## List reactions for a commit comment + + GET /repos/:owner/:repo/comments/:id/reactions + +### Parameters + +Name | Type | Description +-----|------|-------------- +`content`|`string` | Indicates which type of reaction to return. + +### Response + +<%= headers 200, :pagination => default_pagination_rels %> +<%= json(:reaction) { |h| [h] } %> + + +## Create reaction for a commit comment + + POST /repos/:owner/:repo/comments/:id/reactions + +### Parameters + +Name | Type | Description +-----|------|-------------- +`content`|`string` | **Required**. The reaction type + +<%= json :content => 'heart' %> + +### Response + +{{#tip}} + + If you have already created a reaction of type `content`, the previously created reaction will be returned with `Status: 200 OK`. + +{{/tip}} + +<%= headers 201 %> +<%= json :reaction %> + + +## List reactions for an issue + + GET /repos/:owner/:repo/issues/:number/reactions + +### Parameters + +Name | Type | Description +-----|------|-------------- +`content`|`string` | Indicates which type of reaction to return. + +### Response + +<%= headers 200, :pagination => default_pagination_rels %> +<%= json(:reaction) { |h| [h] } %> + + +## Create reaction for an issue + + POST /repos/:owner/:repo/issues/:number/reactions + +### Parameters + +Name | Type | Description +-----|------|-------------- +`content`|`string` | **Required**. The reaction type + +<%= json :content => 'heart' %> + +### Response + +{{#tip}} + + If you have already created a reaction of type `content`, the previously created reaction will be returned with `Status: 200 OK`. + +{{/tip}} + +<%= headers 201 %> +<%= json :reaction %> + + +## List reactions for an issue comment + + GET /repos/:owner/:repo/issues/comments/:id/reactions + +### Parameters + +Name | Type | Description +-----|------|-------------- +`content`|`string` | Indicates which type of reaction to return. + +### Response + +<%= headers 200, :pagination => default_pagination_rels %> +<%= json(:reaction) { |h| [h] } %> + + +## Create reaction for an issue comment + + POST /repos/:owner/:repo/issues/comments/:id/reactions + +### Parameters + +Name | Type | Description +-----|------|-------------- +`content`|`string` | **Required**. The reaction type + +<%= json :content => 'heart' %> + +### Response + +{{#tip}} + + If you have already created a reaction of type `content`, the previously created reaction will be returned with `Status: 200 OK`. + +{{/tip}} + +<%= headers 201 %> +<%= json :reaction %> + + +## List reactions for a pull request review comment + + GET /repos/:owner/:repo/pulls/comments/:id/reactions + +### Parameters + +Name | Type | Description +-----|------|-------------- +`content`|`string` | Indicates which type of reaction to return. + +### Response + +<%= headers 200, :pagination => default_pagination_rels %> +<%= json(:reaction) { |h| [h] } %> + + +## Create reaction for a pull request review comment + + POST /repos/:owner/:repo/pulls/comments/:id/reactions + +### Parameters + +Name | Type | Description +-----|------|-------------- +`content`|`string` | **Required**. The reaction type + +<%= json :content => 'heart' %> + +### Response + +{{#tip}} + + If you have already created a reaction of type `content`, the previously created reaction will be returned with `Status: 200 OK`. + +{{/tip}} + +<%= headers 201 %> +<%= json :reaction %> + + +## Delete a reaction + + DELETE /reactions/:id + +### Response + +<%= headers 204 %> + +{% endif %} diff --git a/content/v3/repos.md b/content/v3/repos.md index ed93eb203b..2e8b726228 100644 --- a/content/v3/repos.md +++ b/content/v3/repos.md @@ -1,19 +1,18 @@ --- -title: Repositories | GitHub API +title: Repositories --- # Repositories -* TOC {:toc} ## List your repositories -List repositories for the authenticated user. Note that this does not include -repositories owned by organizations which the user can access. You can -[list user organizations](/v3/orgs/#list-user-organizations) and -[list organization repositories](/v3/repos/#list-organization-repositories) -separately. +List repositories that are accessible to the authenticated user. + +This includes repositories owned by the authenticated user, repositories where +the authenticated user is a collaborator, and repositories that the +authenticated user has access to through an organization membership. GET /user/repos @@ -21,16 +20,17 @@ separately. Name | Type | Description -----|------|-------------- -`type`|`string` | Can be one of `all`, `owner`, `public`, `private`, `member`. Default: `all` +`visibility` | `string` | Can be one of `all`, `public`, or `private`. Default: `all` +`affiliation` | `string` | Comma-separated list of values. Can include:
* `owner`: Repositories that are owned by the authenticated user.
* `collaborator`: Repositories that the user has been added to as a collaborator.
* `organization_member`: Repositories that the user has access to through being a member of an organization. This includes every repository on every team that the user is on.
Default: `owner,collaborator,organization_member` +`type`|`string` | Can be one of `all`, `owner`, `public`, `private`, `member`. Default: `all`
Will cause a `422` error if used in the same request as **visibility** or **affiliation**. `sort`|`string` | Can be one of `created`, `updated`, `pushed`, `full_name`. Default: `full_name` `direction`|`string` | Can be one of `asc` or `desc`. Default: when using `full_name`: `asc`; otherwise `desc` - ## List user repositories List public repositories for the specified user. - GET /users/:user/repos + GET /users/:username/repos ### Parameters @@ -67,6 +67,19 @@ Note: Pagination is powered exclusively by the `since` parameter. Use the [Link header](/v3/#link-header) to get the URL for the next page of repositories. +{% if page.version != 'dotcom' and page.version >= 2.3 %} + +If you are an [authenticated](/v3/#authentication) site administrator for your Enterprise instance, +you will be able to list all repositories including private repositories. + +### Parameters + +Name | Type | Description +-----|------|-------------- +`visibility`|`string`| To include private repositories as well set to `all`. Default: `public` + +{% endif %} + GET /repositories ### Parameters @@ -83,8 +96,7 @@ Name | Type | Description ## Create -Create a new repository for the authenticated user. OAuth users must supply -`repo` scope. +Create a new repository for the authenticated user. POST /user/repos @@ -93,6 +105,13 @@ be a member of the specified organization. POST /orgs/:org/repos +### OAuth scope requirements + +When using [OAuth](/v3/oauth/#scopes), authorizations must include: + +- `public_repo` scope or `repo` scope to create a public repository +- `repo` scope to create a private repository + ### Input Name | Type | Description @@ -104,10 +123,10 @@ Name | Type | Description `has_issues`|`boolean` | Either `true` to enable issues for this repository, `false` to disable them. Default: `true` `has_wiki`|`boolean` | Either `true` to enable the wiki for this repository, `false` to disable it. Default: `true` `has_downloads`|`boolean` | Either `true` to enable downloads for this repository, `false` to disable them. Default: `true` -`team_id`|`number` | The id of the team that will be granted access to this repository. This is only valid when creating a repository in an organization. +`team_id`|`integer` | The id of the team that will be granted access to this repository. This is only valid when creating a repository in an organization. `auto_init`|`boolean` | Pass `true` to create an initial commit with empty README. Default: `false` -`gitignore_template`|`string` | Desired language or platform [.gitignore template](https://github.com/github/gitignore) to apply. Use the name of the template without the extension. For example, "Haskell". _Ignored if the `auto_init` parameter is not provided._ -`license_template`|`string` | Desired [LICENSE template](https://github.com/github/choosealicense.com) to apply. Use the [name of the template](https://github.com/github/choosealicense.com/tree/gh-pages/licenses) without the extension. For example, "mit" or "mozilla". _Ignored if the `auto_init` parameter is not provided._ +`gitignore_template`|`string` | Desired language or platform [.gitignore template](https://github.com/github/gitignore) to apply. Use the name of the template without the extension. For example, "Haskell". +`license_template`|`string` | Desired [LICENSE template](https://github.com/github/choosealicense.com) to apply. Use the [name of the template](https://github.com/github/choosealicense.com/tree/gh-pages/_licenses) without the extension. For example, "mit" or "mozilla". #### Example @@ -123,9 +142,7 @@ Name | Type | Description ### Response -<%= headers 201, - :Location => -'https://api.github.com/repos/octocat/Hello-World' %> +<%= headers 201, :Location => get_resource(:repo)['url'] %> <%= json :repo %> ## Get @@ -179,6 +196,14 @@ Name | Type | Description List contributors to the specified repository, sorted by the number of commits per contributor in descending order. +{{#tip}} + +Contributors data is cached for performance reasons. This endpoint may return information that is a few hours old. + +Git contributors are identified by author email address. This API attempts to group contribution counts by GitHub user, across all of their associated email addresses. For performance reasons, only the first 500 author email addresses in the repository will be linked to GitHub users. The rest will appear as anonymous contributors without associated GitHub user information. + +{{/tip}} + GET /repos/:owner/:repo/contributors ### Parameters @@ -190,7 +215,7 @@ Name | Type | Description ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:contributor) { |h| [h] } %> ## List languages @@ -213,7 +238,7 @@ List languages for the specified repository. The value on the right of a languag ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:team) { |h| [h] } %> ## List Tags @@ -222,27 +247,9 @@ List languages for the specified repository. The value on the right of a languag ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:tag) { |h| [h] } %> -## List Branches - - GET /repos/:owner/:repo/branches - -### Response - -<%= headers 200 %> -<%= json(:branches) %> - -## Get Branch - - GET /repos/:owner/:repo/branches/:branch - -### Response - -<%= headers 200 %> -<%= json(:branch) %> - ## Delete a Repository Deleting a repository requires admin access. If OAuth is used, the diff --git a/content/v3/repos/branches.md b/content/v3/repos/branches.md new file mode 100644 index 0000000000..e620efd95c --- /dev/null +++ b/content/v3/repos/branches.md @@ -0,0 +1,522 @@ +--- +title: Branches +--- + +# Branches + +{:toc} + +{% if page.version != 'dotcom' and page.version >= 2.5 and page.version < 2.7 %} + +## List Branches + + GET /repos/:owner/:repo/branches + +### Parameters + +Name | Type | Description +-----|------|------------- +`protected`| `boolean` | Set to `true` to only return protected branches + +{{#tip}} + + + + The Protected Branch API is currently available for developers to preview. + During the preview period, the API may change without advance notice. + Please see the [blog post](/changes/2015-11-11-protected-branches-api) for full details. + + To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.loki-preview+json + + The `protection` key will only be present in branch payloads if this header is passed. + +{{/tip}} + +### Response + +<%= headers 200, :pagination => default_pagination_rels %> +<%= json(:branches) { |a| a.each { |b| b.merge!("protection" => { + "enabled" => false, + "required_status_checks" => { + "enforcement_level" => "off", + "contexts" => [] + } +}) } } %> + +## Get Branch + + GET /repos/:owner/:repo/branches/:branch + +### Response + +{{#tip}} + + + + The Protected Branch API is currently available for developers to preview. + During the preview period, the API may change without advance notice. + Please see the [blog post](/changes/2015-11-11-protected-branches-api) for full details. + + To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.loki-preview+json + + The `protection` key will only be present in branch payloads if this header is passed. + +{{/tip}} + +<%= headers 200 %> +<%= json(:branch) { |h| h.merge!("protection" => { + "enabled" => false, + "required_status_checks" => { + "enforcement_level" => "off", + "contexts" => [] + } +}) } %> + +## Enabling and disabling branch protection + +{{#tip}} + + + + The Protected Branch API is currently available for developers to preview. + During the preview period, the API may change without advance notice. + Please see the [blog post](/changes/2015-11-11-protected-branches-api) for full details. + + To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.loki-preview+json + +{{/tip}} + +Protecting a branch requires admin access. + + PATCH /repos/:owner/:repo/branches/:branch + +### Parameters + +You need to pass a `protection` object. + +Name | Type | Description +-----|------|------------- +`enabled`|`boolean` | **Required**. Should this branch be protected or not +`required_status_checks`|`object`| Configure required status checks here + +The `required_status_checks` object must have the following keys: + +Name | Type | Description +-----|------|------------- +`enforcement_level`|`string` | **Required**. Who required status checks apply to. Options are `off`, `non_admins` or `everyone`. +`contexts`|`array` | **Required**. The list of status checks to require in order to merge into this branch + +The `enforcement_level` key can have the following values: + +Name | Description +------|------------ +`off` | Turn off required status checks for this branch. +`non_admins` | Required status checks will be enforced for non-admins. +`everyone` | Required status checks will be enforced for everyone (including admins). + +#### Example + +<%= json \ + "protection" => { + "enabled" => true, + "required_status_checks" => { + "enforcement_level" => "everyone", + "contexts" => ["continuous-integration/travis-ci"] + } + } +%> + +{% endif %} + +{% if page.version == 'dotcom' or page.version >= 2.7 %} + +{{#tip}} + + + + The Protected Branch API is currently available for developers to preview. + During the preview period, the API may change without advance notice. + Please see the [blog post](/changes/2016-06-27-protected-branches-api-update) for full details. + + To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.loki-preview+json + +{{/tip}} + +## List Branches + + GET /repos/:owner/:repo/branches + +### Parameters + +Name | Type | Description +-----|------|------------- +`protected` | `boolean` | Set to `true` to only return protected branches + +{{#tip}} + + + + The Protected Branch API is currently available for developers to preview. + During the preview period, the API may change without advance notice. + Please see the [blog post](/changes/2016-06-27-protected-branches-api-update) for full details. + + To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.loki-preview+json + + The `protected` key will only be present in branch payloads if this header is passed. + +{{/tip}} + +### Response + +<%= headers 200, :pagination => default_pagination_rels %> +<%= json(:branches) { |a| a.each { |b| b.merge!( + "protected": true, + "protection_url": "https://api.github.com/repos/octocat/Hello-World/branches/#{b["name"]}/protection", +) } } %> + +## Get Branch + + GET /repos/:owner/:repo/branches/:branch + +### Response + +{{#tip}} + + + + The Protected Branch API is currently available for developers to preview. + During the preview period, the API may change without advance notice. + Please see the [blog post](/changes/2016-06-27-protected-branches-api-update) for full details. + + To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.loki-preview+json + + The `protected` key will only be present in branch payloads if this header is passed. + +{{/tip}} + +<%= headers 200 %> +<%= json(:branch) { |h| h.merge!( + "protected": true, + "protection_url": "https://api.github.com/repos/octocat/Hello-World/branches/#{h["name"]}/protection", +) } %> + + +## Get branch protection + + GET /repos/:owner/:repo/branches/:branch/protection + +<%= headers 200 %> +<%= json(:repo_branch_protection) %> + +## Update branch protection + +Protecting a branch requires admin access. + + PUT /repos/:owner/:repo/branches/:branch/protection + +### Parameters + +You must pass two objects: `required_status_checks` and `restrictions`. Both can have the value `null` for disabled. + +The `required_status_checks` object must have the following keys: + +Name | Type | Description +-----|------|------------- +`include_admins` | `boolean` | **Required**. Enforce required status checks for repository administrators. +`strict` | `boolean` | **Required**. Require branches to be up to date before merging. +`contexts` | `array` | **Required**. The list of status checks to require in order to merge into this branch + +The `restrictions` object must have the following keys: + +Name | Type | Description +-----|------|------------- +`users` | `array` | The list of user `login`s with push access +`teams` | `array` | The list of team `slug`s with push access + +{{#tip}} + +* Teams and users `restrictions` are only available for organization-owned repositories. +* The list of users and teams in total is limited to 100 items. + +{{/tip}} + +### Example + +<%= json \ + "required_status_checks" => { + "include_admins" => true, + "strict" => true, + "contexts" => ["continuous-integration/travis-ci"] + }, + "restrictions" => { + "users" => ["octocat"], + "teams" => ["justice-league"] + } +%> + +### Response + +<%= headers 200 %> +<%= json(:repo_branch_protection) %> + +## Remove branch protection + + DELETE /repos/:owner/:repo/branches/:branch/protection + +<%= headers 204 %> + +## Get required status checks of protected branch + + GET /repos/:owner/:repo/branches/:branch/protection/required_status_checks + +<%= headers 200 %> +<%= json(:repo_branch_protection_required_status_checks) %> + +## Update required status checks of protected branch + +Updating required status checks requires admin access and branch protection to be enabled. + + PATCH /repos/:owner/:repo/branches/:branch/protection/required_status_checks + +### Parameters + +The object passed can have the following keys: + +Name | Type | Description +-----|------|------------- +`include_admins`|`boolean` | Enforce required status checks for repository administrators. +`strict`|`boolean` | Require branches to be up to date before merging. +`contexts`|`array` | The list of status checks to require in order to merge into this branch + +### Example + +<%= json \ + "include_admins" => true, + "strict" => true, + "contexts" => ["continuous-integration/travis-ci"] +%> + +### Response + +<%= headers 200 %> +<%= json(:repo_branch_protection_required_status_checks) %> + +## Remove required status checks of protected branch + + DELETE /repos/:owner/:repo/branches/:branch/protection/required_status_checks + +<%= headers 204 %> + +## List required status checks contexts of protected branch + + GET /repos/:owner/:repo/branches/:branch/protection/required_status_checks/contexts + +<%= headers 200 %> +<%= json ["continuous-integration/travis-ci"] %> + +## Replace required status checks contexts of protected branch + + PUT /repos/:owner/:repo/branches/:branch/protection/required_status_checks/contexts + +### Example + +<%= json ["continuous-integration/travis-ci"] %> + +### Response + +<%= headers 200 %> +<%= json ["continuous-integration/travis-ci"] %> + +## Add required status checks contexts of protected branch + + POST /repos/:owner/:repo/branches/:branch/protection/required_status_checks/contexts + +### Example + +<%= json ["continuous-integration/jenkins"] %> + +### Response + +<%= headers 200 %> +<%= json ["continuous-integration/travis-ci", "continuous-integration/jenkins"] %> + +## Remove required status checks contexts of protected branch + + DELETE /repos/:owner/:repo/branches/:branch/protection/required_status_checks/contexts + +### Example + +<%= json ["continuous-integration/jenkins"] %> + +### Response + +<%= headers 200 %> +<%= json ["continuous-integration/travis-ci"] %> + + +## Get restrictions of protected branch + +{{#tip}} + +Teams and users `restrictions` are only available for organization-owned repositories. + +{{/tip}} + + GET /repos/:owner/:repo/branches/:branch/protection/restrictions + +<%= headers 200 %> +<%= json(:repo_branch_protection_restrictions) %> + +## Remove restrictions of protected branch + + DELETE /repos/:owner/:repo/branches/:branch/protection/restrictions + +<%= headers 204 %> + +## List team restrictions of protected branch + + GET /repos/:owner/:repo/branches/:branch/protection/restrictions/teams + +<%= headers 200 %> +<%= json(:team) { |h| [h] } %> + +## Replace team restrictions of protected branch + + PUT /repos/:owner/:repo/branches/:branch/protection/restrictions/teams + +### Body parameters + +Pass the list of team `slug`s with push access. + +{{#tip}} + + The list of users and teams in total is limited to 100 items. + +{{/tip}} + +### Example + +<%= json ["justice-league"] %> + +### Response + +<%= headers 200 %> +<%= json(:team) { |h| [h] } %> + +## Add team restrictions of protected branch + + POST /repos/:owner/:repo/branches/:branch/protection/restrictions/teams + +### Body parameters + +Pass the list of team `slug`s with push access. + +{{#tip}} + +The list of users and teams in total is limited to 100 items. + +{{/tip}} + +### Example + +<%= json ["justice-league"] %> + +### Response + +<%= headers 200 %> +<%= json(:team) { |h| [h] } %> + +## Remove team restrictions of protected branch + + DELETE /repos/:owner/:repo/branches/:branch/protection/restrictions/teams + +### Example + +<%= json ["octocats"] %> + +### Response + +<%= headers 200 %> +<%= json(:team) { |h| [h] } %> + + +## List user restrictions of protected branch + + GET /repos/:owner/:repo/branches/:branch/protection/restrictions/users + +<%= headers 200 %> +<%= json(:user) { |h| [h] } %> + +## Replace user restrictions of protected branch + + PUT /repos/:owner/:repo/branches/:branch/protection/restrictions/users + +### Body parameters + +Pass the list of user `login`s with push access. + +{{#tip}} + +The list of users and teams in total is limited to 100 items. + +{{/tip}} + +### Example + +<%= json ["octocat"] %> + +### Response + +<%= headers 200 %> +<%= json(:user) { |h| [h] } %> + +## Add user restrictions of protected branch + + POST /repos/:owner/:repo/branches/:branch/protection/restrictions/users + +### Body parameters + +Pass the list of user `login`s with push access. + +{{#tip}} + +The list of users and teams in total is limited to 100 items. + +{{/tip}} + +### Example + +<%= json ["octocat"] %> + +### Response + +<%= headers 200 %> +<%= json(:user) { |h| [h] } %> + +## Remove user restrictions of protected branch + + DELETE /repos/:owner/:repo/branches/:branch/protection/restrictions/users + +### Example + +<%= json ["defunkt"] %> + +### Response + +<%= headers 200 %> +<%= json(:user) { |h| [h] } %> + + +{% endif %} diff --git a/content/v3/repos/collaborators.md b/content/v3/repos/collaborators.md index 2c54d8114b..5e22e210d7 100644 --- a/content/v3/repos/collaborators.md +++ b/content/v3/repos/collaborators.md @@ -1,13 +1,14 @@ --- -title: Collaborators | GitHub API +title: Collaborators --- # Collaborators -* TOC {:toc} -## List collaborators {#list} + + +## List collaborators GET /repos/:owner/:repo/collaborators @@ -18,12 +19,33 @@ collaborators list. ### Response -<%= headers 200 %> +{% if page.version != 'dotcom' and page.version > 2.3 and page.version < 2.6 %} + +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:user) { |h| [h] } %> -## Check if a user is a collaborator {#get} +### Alternative response with extra repository information + +{{#tip}} + +We're currently offering a preview period allowing applications to opt in to the Organization Permissions API. Please see the [blog post](/changes/2015-06-24-api-enhancements-for-working-with-organization-permissions/) for full details. + +To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + +``` +application/vnd.github.ironman-preview+json +``` + +{{/tip}} + +{% endif %} - GET /repos/:owner/:repo/collaborators/:user +<%= headers 200, :pagination => default_pagination_rels %> +<%= json(:collaborator) { |h| [h] } %> + +## Check if a user is a collaborator + + GET /repos/:owner/:repo/collaborators/:username ### Response if user is a collaborator @@ -33,17 +55,68 @@ collaborators list. <%= headers 404 %> -## Add user as a collaborator {#add-collaborator} +## Add user as a collaborator + + PUT /repos/:owner/:repo/collaborators/:username + +### Parameters + +{% if page.version == 'dotcom' or page.version >= 2.4 %} + +Name | Type | Description +-----|------|-------------- +`permission`|`string` | The permission to grant the collaborator. **Only valid on organization-owned repositories.** Can be one of:
* `pull` - can pull, but not push to or administer this repository.
* `push` - can pull and push, but not administer this repository.
* `admin` - can pull, push and administer this repository.
Default: `push` + +<%= fetch_content(:optional_put_content_length) %> + +{{#tip}} - PUT /repos/:owner/:repo/collaborators/:user +We're currently offering a preview period allowing applications to opt in to the Repository Invitations API. + +To send an invitation to a collaborator rather than directly adding them, you must provide a custom [media type](/v3/media) in the `Accept` header: + +``` +application/vnd.github.swamp-thing-preview+json +``` + +{{/tip}} + +{% if page.version != 'dotcom' and page.version > 2.3 and page.version < 2.6 %} + +{{#tip}} + +We're currently offering a preview period allowing applications to opt in to the Organization Permissions API. Please see the [blog post](/changes/2015-06-24-api-enhancements-for-working-with-organization-permissions/) for full details. + +To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header: + +``` +application/vnd.github.ironman-preview+json +``` + +**Warning:** If you use this API to add a collaborator to a repository that's owned by an organization that hasn't had [improved organization permissions](https://github.com/blog/2020-improved-organization-permissions) enabled yet, you will get a `422` error response. + +{{/tip}} + +{% endif %} + +{% else %} + +<%= fetch_content(:put_content_length) %> + +{% endif %} ### Response <%= headers 204 %> -## Remove user as a collaborator {#remove-collaborator} +### Response with preview media type + +<%= headers 201 %> +<%= json(:repository_invitation) %> + +## Remove user as a collaborator - DELETE /repos/:owner/:repo/collaborators/:user + DELETE /repos/:owner/:repo/collaborators/:username ### Response diff --git a/content/v3/repos/comments.md b/content/v3/repos/comments.md index e06697169e..e6f9bb5050 100644 --- a/content/v3/repos/comments.md +++ b/content/v3/repos/comments.md @@ -1,10 +1,9 @@ --- -title: Comments | GitHub API +title: Comments --- # Comments -* TOC {:toc} ## List commit comments for a repository @@ -18,37 +17,78 @@ Comments are ordered by ascending ID. ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:commit_comment) { |h| [h] } %> +{% if page.version == 'dotcom' %} +#### Reactions summary + +{{#tip}} + + + + An additional `reactions` object in the commit comment payload is currently available for developers to preview. + During the preview period, the APIs may change without advance notice. + Please see the [blog post](/changes/2016-05-12-reactions-api-preview) for full details. + + To access the API you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.squirrel-girl-preview + + The `reactions` key will have the following payload where `url` can be used to construct the API location for [listing and creating](/v3/reactions) reactions. + +{{/tip}} +<%= json :commit_comment_reaction_summary %> +{% endif %} + ## List comments for a single commit GET /repos/:owner/:repo/commits/:ref/comments ### Response -<%= headers 200 %> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:commit_comment) { |h| [h] } %> +{% if page.version == 'dotcom' %} +#### Reactions summary + +{{#tip}} + + + + An additional `reactions` object in the commit comment payload is currently available for developers to preview. + During the preview period, the APIs may change without advance notice. + Please see the [blog post](/changes/2016-05-12-reactions-api-preview) for full details. + + To access the API you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.squirrel-girl-preview + + The `reactions` key will have the following payload where `url` can be used to construct the API location for [listing and creating](/v3/reactions) reactions. + +{{/tip}} +<%= json :commit_comment_reaction_summary %> +{% endif %} + ## Create a commit comment POST /repos/:owner/:repo/commits/:sha/comments ### Input -Name | Type | Description +Name | Type | Description -----|------|-------------- -`sha`|`string` | **Required**. The SHA of the commit to comment on. `body`|`string` | **Required**. The contents of the comment. `path`|`string` | Relative path of the file to comment on. -`position`|`number` | Line index in the diff to comment on. -`line`|`number` | **Deprecated**. Use **position** parameter instead. Line number in the file to comment on. +`position`|`integer` | Line index in the diff to comment on. +`line`|`integer` | **Deprecated**. Use **position** parameter instead. Line number in the file to comment on. #### Example <%= json \ - :body => 'Nice change', + :body => 'Great stuff', :path => 'file1.txt', :position => 4, :line => nil @@ -56,7 +96,7 @@ Name | Type | Description ### Response -<%= headers 201, :Location => "https://api.github.com/user/repo/comments/1" %> +<%= headers 201, :Location => get_resource(:commit_comment)['url'] %> <%= json :commit_comment %> ## Get a single commit comment @@ -68,13 +108,34 @@ Name | Type | Description <%= headers 200 %> <%= json :commit_comment %> +{% if page.version == 'dotcom' %} +#### Reactions summary + +{{#tip}} + + + + An additional `reactions` object in the commit comment payload is currently available for developers to preview. + During the preview period, the APIs may change without advance notice. + Please see the [blog post](/changes/2016-05-12-reactions-api-preview) for full details. + + To access the API you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.squirrel-girl-preview + + The `reactions` key will have the following payload where `url` can be used to construct the API location for [listing and creating](/v3/reactions) reactions. + +{{/tip}} +<%= json :commit_comment_reaction_summary %> +{% endif %} + ## Update a commit comment PATCH /repos/:owner/:repo/comments/:id ### Input -Name | Type | Description +Name | Type | Description -----|------|-------------- `body`|`string` | **Required**. The contents of the comment @@ -88,7 +149,7 @@ Name | Type | Description ### Response <%= headers 200 %> -<%= json :commit_comment %> +<%= json(:commit_comment) { |h| h.merge('body' => 'Nice change') } %> ## Delete a commit comment diff --git a/content/v3/repos/commits.md b/content/v3/repos/commits.md index 8edf5e5a66..20c2ee69c3 100644 --- a/content/v3/repos/commits.md +++ b/content/v3/repos/commits.md @@ -1,10 +1,9 @@ --- -title: Commits | GitHub API +title: Commits --- # Commits -* TOC {:toc} The Repo Commits API supports listing, viewing, and comparing commits in a repository. @@ -13,16 +12,11 @@ The Repo Commits API supports listing, viewing, and comparing commits in a repos GET /repos/:owner/:repo/commits -_A special note on pagination:_ Due to the way Git works, commits are paginated -based on SHA instead of page number. Please follow the link headers as outlined -in the [pagination overview](https://developer.github.com/v3/#pagination) -instead of constructing page links yourself. - ### Parameters Name | Type | Description -----|------|-------------- -`sha`|`string` | SHA or branch to start listing commits from. +`sha`|`string` | SHA or branch to start listing commits from. Default: the repository’s default branch (usually `master`). `path`|`string` | Only commits containing this file path will be returned. `author`|`string` | GitHub login or email address by which to filter by commit author. `since`|`string` | Only commits after this date will be returned. This is a timestamp in ISO 8601 format: `YYYY-MM-DDTHH:MM:SSZ`. @@ -31,11 +25,7 @@ Name | Type | Description ### Response -<%= - headers 200, :pagination => { - :next => 'https://api.github.com/repositories/417862/commits?top=master&last_sha=4f9890864feb48296917c2fcf3682d8dc3adf16a' - } -%> +<%= headers 200, :pagination => default_pagination_rels %> <%= json(:commit) { |h| [h] } %> ## Get a single commit @@ -44,29 +34,108 @@ Name | Type | Description ### Response +Diffs with binary data will have no 'patch' property. Pass the +appropriate [media type](/v3/media/#commits-commit-comparison-and-pull-requests) to fetch diff and +patch formats. + <%= headers 200 %> <%= json(:full_commit) %> -Note: Diffs with binary data will have no 'patch' property. Pass the -appropriate [media type](/v3/media/#commits-commit-comparison-and-pull-requests) to fetch diff and -patch formats. +## Get the SHA-1 of a commit reference + +Users with read access can get the SHA-1 of a commit reference: + + GET /repos/:owner/:repo/commits/:ref + +To access the API you must provide a custom [media type](/v3/media) in the `Accept` header: + + application/vnd.github.VERSION.sha + +To check if a remote reference's SHA-1 is the same as your local reference's SHA-1, make a `GET` request and provide the current SHA-1 for the local reference as the ETag. + +### Response + +The SHA-1 of the commit reference. + +<%= headers 200 %> +
+814412cfbd631109df337e16c807207e78c0d24e +## Compare two commits GET /repos/:owner/:repo/compare/:base...:head -Note: Both `:base` and `:head` can be either branch names in `:repo` or branch names in other repositories in the same network as `:repo`. For the latter case, use the format `user:branch`: +Both `:base` and `:head` must be branch names in `:repo`. To compare branches across other repositories in the same network as `:repo`, use the format `
-curl -L https://api.github.com/repos/pengwynn/octokit/tarball > octokit.tar.gz +``` command-line +$curl -L https://api.github.com/repos/octokit/octokit.rb/tarball > octokit.tar.gz - % Total % Received % Xferd Average Speed Time Time Time Current - Dload Upload Total Spent Left Speed -100 206k 100 206k 0 0 146k 0 0:00:01 0:00:01 --:--:-- 790k -+> % Total % Received % Xferd Average Speed Time Time Time Current +> Dload Upload Total Spent Left Speed +> 100 206k 100 206k 0 0 146k 0 0:00:01 0:00:01 --:--:-- 790k +``` ## Custom media types -[READMEs](#get-the-readme), [files](#get-contents), and [symlinks](#get-contents) support the following custom media type. +[READMEs](#get-the-readme), [files](#get-contents), and [symlinks](#get-contents) support the following custom media types: application/vnd.github.VERSION.raw + application/vnd.github.VERSION.html + +Use the `.raw` media type to retrieve the contents of the file. + +For markup files such as Markdown or AsciiDoc, you can retrieve the rendered HTML using the `.html` media type. Markup languages are rendered to HTML using our open-source [Markup library](https://github.com/github/markup). + +[All objects](#get-contents) support the following custom media type: + + application/vnd.github.VERSION.object + +Use the `object` media type parameter to retrieve the contents in a consistent object format regardless of the content type. For example, instead of an array of objects +for a directory, the response will be an object with an `entries` attribute containing the array of objects. You can read more about the use of media types in the API [here](/v3/media/). diff --git a/content/v3/repos/deployments.md b/content/v3/repos/deployments.md index 6de7ccb46f..34e2574621 100644 --- a/content/v3/repos/deployments.md +++ b/content/v3/repos/deployments.md @@ -1,26 +1,12 @@ --- -title: Deployments | GitHub API +title: Deployments --- # Deployments -* TOC {:toc} -
- The Deployments API is currently available for developers to preview. - During the preview period, the API may change without advance notice. - Please see the blog post for full details. -
- -
- To access the API during the preview period, you must provide a custom media type in the Accept header:
-
application/vnd.github.cannonball-preview+json- -
+```
+---------+ +--------+ +-----------+ +-------------+
| Tooling | | GitHub | | 3rd Party | | Your Server |
+---------+ +--------+ +-----------+ +-------------+
@@ -69,15 +55,15 @@ Below is a simple sequence diagram for how these interactions would work.
| | Deployment Status | |
| |<----------------------| |
| | | |
-
+```
Keep in mind that GitHub is never actually accessing your servers. It's up to
-your 3rd party integration to interact with deployment events.
-This allows for [github-services](https://github.com/github/github-services)
-integrations as well as running your own systems depending on your use case.
-Multiple systems can listen for deployment events, and it's up to each of
-those systems to decide whether or not they're responsible for pushing the code
-out to your servers, building native code, etc.
+your 3rd party integration to interact with deployment events. This allows for
+[GitHub integrations](https://github.com/integrations) as
+well as running your own systems depending on your use case. Multiple systems
+can listen for deployment events, and it's up to each of those systems to
+decide whether or not they're responsible for pushing the code out to your
+servers, building native code, etc.
Note that the `repo_deployment` [OAuth scope](/v3/oauth/#scopes) grants
targeted access to Deployments and Deployment Statuses **without**
@@ -86,10 +72,17 @@ as well.
## List Deployments
-Users with pull access can view deployments for a repository:
+Simple filtering of deployments is available via query parameters:
GET /repos/:owner/:repo/deployments
+Name | Type | Description
+-----|------|--------------
+`sha`|`string` | The SHA that was recorded at creation time. Default: `none`
+`ref`|`string` | The name of the ref. This can be a branch, tag, or SHA. Default: `none`
+`task`|`string` | The name of the task for the deployment. e.g. `deploy` or `deploy:migrations`. Default: `none`
+`environment`|`string` | The name of the environment that was deployed to. e.g. `staging` or `production`. Default: `none`
+
### Response
<%= headers 200, :pagination => default_pagination_rels %>
@@ -97,15 +90,16 @@ Users with pull access can view deployments for a repository:
## Create a Deployment
-If your repository is taking advantage of [commit statuses](/v3/repos/statuses),
-the API will reject requests that do not have a successful [combined
-status.](/v3/repos/statuses/#get-the-combined-status-for-a-specific-ref) (Your
-repository is not required to use commit statuses. If no commit statuses are
-present, the deployment will always be created.)
+Deployments offer a few configurable parameters with sane defaults.
-The `force` parameter can be used when you really just need a deployment to go
-out. In these cases, all checks are bypassed, and the deployment is created for
-the ref.
+The `ref` parameter can be any named branch, tag, or SHA. At GitHub we often
+deploy branches and verify them before we merge a pull request.
+
+The `environment` parameter allows deployments to be issued to different
+runtime environments. Teams often have multiple environments for verifying
+their applications, like 'production', 'staging', and 'qa'. This allows for
+easy tracking of which environments had deployments requested. The default
+environment is 'production'.
The `auto_merge` parameter is used to ensure that the requested ref is not
behind the repository's default branch. If the ref *is* behind the default
@@ -113,11 +107,23 @@ branch for the repository, we will attempt to merge it for you. If the merge
succeeds, the API will return a successful merge commit. If merge conflicts
prevent the merge from succeeding, the API will return a failure response.
+By default, [commit statuses](/v3/repos/statuses) for every submitted context
+must be in a 'success' state. The `required_contexts` parameter allows you to
+specify a subset of contexts that must be "success", or to specify contexts
+that have not yet been submitted. You are not required to use commit statuses
+to deploy. If you do not require any contexts or create any commit statuses,
+the deployment will always succeed.
+
The `payload` parameter is available for any extra information that a
deployment system might need. It is a JSON text field that will be passed on
when a deployment event is dispatched.
-Users with push access can create a deployment for a given ref:
+The `task` parameter is used by the deployment system to allow different
+execution paths. In the web world this might be 'deploy:migrations' to run
+schema changes on the system. In the compiled world this could be a flag to
+compile an application with debugging enabled.
+
+Users with `repo` or `repo_deployment` scopes can create a deployment for a given ref:
POST /repos/:owner/:repo/deployments
@@ -125,25 +131,78 @@ Users with push access can create a deployment for a given ref:
Name | Type | Description
-----|------|--------------
-`ref`|`string`| **Required**. The ref to deploy. This can be a branch, tag, or sha.
-`force`|`boolean`| Optional parameter to bypass any ahead/behind checks or commit status checks. Default: `false`
+`ref`|`string`| **Required**. The ref to deploy. This can be a branch, tag, or SHA.
+`task`|`string`| Optional parameter to specify a task to execute, e.g. `deploy` or `deploy:migrations`. Default: `deploy`
+`auto_merge`|`boolean`| Optional parameter to merge the default branch into the requested ref if it is behind the default branch. Default: `true`
+`required_contexts`|`Array`| Optional array of status contexts verified against commit status checks. If this parameter is omitted from the parameters then all unique contexts will be verified before a deployment is created. To bypass checking entirely pass an empty array. Defaults to all unique contexts.
`payload`|`string` | Optional JSON payload with extra information about the deployment. Default: `""`
-`auto_merge`|`boolean`| Optional parameter to merge the default branch into the requested deployment branch if necessary. Default: `false`
+`environment`|`string` | Optional name for the target deployment environment (e.g., production, staging, qa). Default: `"production"`
`description`|`string` | Optional short description. Default: `""`
+{% if page.version == 'dotcom' || page.version > 2.6 %} `transient_environment` | `boolean` | Optionally specifies if the given environment is specific to the deployment and will no longer exist at some point in the future. Default: `false` **This parameter requires a custom media type to be specified. Please see more in the alert below.**{% endif %}
+{% if page.version == 'dotcom' || page.version > 2.6 %} `production_environment` | `boolean` | Optionally specifies if the given environment is one that end-users directly interact with. Default: `true` when `environment` is `"production"` and `false` otherwise. **This parameter requires a custom media type to be specified. Please see more in the alert below.**{% endif %}
-#### Example
+{% if page.version == 'dotcom' || page.version > 2.6 %}
+{{#tip}}
+
+The new `transient_environment` and `production_environment` parameters are currently available for developers to preview. During the preview period, the API may change without advance notice. Please see the [blog post][blog-post] for full details.
+
+To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header:
+
+```
+application/vnd.github.ant-man-preview+json
+```
+
+{{/tip}}
+
+{% endif %}
+
+#### Simple Example
+
+A simple example putting the user and room into the payload to notify back to
+chat networks.
<%= json \
:ref => "topic-branch",
- :payload => "{\"environment\":\"production\",\"deploy_user\":\"atmos\",\"room_id\":123456}",
+ :payload => "{\"user\":\"atmos\",\"room_id\":123456}",
:description => "Deploying my sweet branch"
%>
-<%= headers 201,
- :Location =>
-'https://api.github.com/repos/octocat/example/deployments/1' %>
+### Successful response
+
+<%= headers 201, :Location => get_resource(:deployment)['url'] %>
<%= json :deployment %>
+#### Advanced Example
+
+A more advanced example specifying required commit statuses and bypassing auto-merging.
+
+<%= json \
+ :ref => "topic-branch",
+ :auto_merge => false,
+ :payload => "{\"user\":\"atmos\",\"room_id\":123456}",
+ :description => "Deploying my sweet branch",
+ :required_contexts => ["ci/janky", "security/brakeman"]
+%>
+
+### Successful response
+
+<%= headers 201, :Location => get_resource(:deployment)['url'] %>
+<%= json :deployment %>
+
+### Merge conflict response
+
+This error happens when the `auto_merge` option is enabled and when the default branch (in this case `master`), can't be merged into the branch that's being deployed (in this case `topic-branch`), due to merge conflicts.
+
+<%= headers 409 %>
+<%= json({ :message => "Conflict merging master into topic-branch" }) %>
+
+### Failed commit status checks
+
+This error happens when the `required_contexts` parameter indicates that one or more contexts need to have a `success` status for the commit to be deployed, but one or more of the required contexts do not have a state of `success`.
+
+<%= headers 409 %>
+<%= json({ :message => "Conflict: Commit status checks failed for topic-branch." }) %>
+
## Update a Deployment
Once a deployment is created, it cannot be updated. Information relating to the
@@ -167,7 +226,7 @@ Name | Type | Description
### Response
<%= headers 200, :pagination => default_pagination_rels %>
-<%= json(:deployment_status) { |h| [h] } %>
+<%= json(:deployment_status) { |h| h.delete("deployment"); [h] } %>
## Create a Deployment Status
@@ -179,9 +238,28 @@ Users with push access can create deployment statuses for a given deployment:
Name | Type | Description
-----|------|--------------
-`state`|`string` | **Required**. The state of the status. Can be one of `pending`, `success`, `error`, or `failure`.
+`state`|`string` | **Required**. The state of the status. Can be one of `pending`, `success`, `error`, {% if page.version == 'dotcom' || page.version > 2.6 %} `inactive`, {% endif %}or `failure` **The `inactive` state requires a custom media type to be specified. Please see more in the alert below.**.
`target_url`|`string` | The target URL to associate with this status. This URL should contain output to keep the user updated while the task is running or serve as historical information for what happened in the deployment. Default: `""`
-`description`|`string` | A short description of the status. Default: `""`
+{% if page.version == 'dotcom' || page.version > 2.6 %}`log_url`|`string` | This is functionally equivalent to `target_url`. We will continue accept `target_url` to support legacy uses, but we recommend modifying this to the new name to avoid confusion. Default: `""` **This parameter requires a custom media type to be specified. Please see more in the alert below.**{% endif %}
+`description`|`string` | A short description of the status. Maximum length of 140 characters. Default: `""`
+{% if page.version == 'dotcom' || page.version > 2.6 %}`environment_url`|`string`| Optionally set the URL for accessing your environment. Default: `""` **This parameter requires a custom media type to be specified. Please see more in the alert below.**{% endif %}
+{% if page.version == 'dotcom' || page.version > 2.6 %}`auto_inactive`|`boolean`| Optional parameter to add a new `inactive` status to all non-transient, non-production environment deployments with the same repository and environment name as the created status's deployment. Default: `true` **This parameter requires a custom media type to be specified. Please see more in the alert below.**{% endif %}
+
+{% if page.version == 'dotcom' || page.version > 2.6 %}
+
+{{#tip}}
+
+The new `inactive` state, rename of the `target_url` parameter to `log_url` and new `environment_url` and `auto_inactive` parameters are currently available for developers to preview. During the preview period, the API may change without advance notice. Please see the [blog post][blog-post] for full details.
+
+To access the API during the preview period, you must provide a custom [media type](/v3/media) in the `Accept` header:
+
+```
+application/vnd.github.ant-man-preview+json
+```
+
+{{/tip}}
+
+{% endif %}
#### Example
@@ -193,7 +271,7 @@ Name | Type | Description
### Response
-<%= headers 201,
- :Location =>
-'https://api.github.com/repos/octocat/example/deployments/42/statuses/1' %>
+<%= headers 201, :Location => get_resource(:deployment_status)['url'] %>
<%= json :deployment_status %>
+
+[blog-post]: /changes/2016-04-06-deployment-and-deployment-status-enhancements
diff --git a/content/v3/repos/downloads.md b/content/v3/repos/downloads.md
index 36e0b30109..c5f027a106 100644
--- a/content/v3/repos/downloads.md
+++ b/content/v3/repos/downloads.md
@@ -1,23 +1,20 @@
---
-title: Downloads | GitHub API
+title: Downloads
---
# Downloads
-* TOC
{:toc}
### Downloads API is Deprecated
-- The Downloads API (described below) was - deprecated on December 11, 2012. - It will be removed at a future date. +{{#warning}} - We recommend using Releases instead. -
-For example, if your Continuous Integration system is posting build status, you would want to provide the deep link for the build output for this specific SHA:
`http://ci.example.com/user/repo/build/sha`. +`target_url`|`string` | The target URL to associate with this status. This URL will be linked from the {{ site.data.variables.product.product_name }} UI to allow users to easily see the 'source' of the Status.
For example, if your Continuous Integration system is posting build status, you would want to provide the deep link for the build output for this specific SHA:
`http://ci.example.com/user/repo/build/sha`. `description`|`string` | A short description of the status. -`context`|`string` | A string label to differentiate this status from the status of other systems. +`context`|`string` | A string label to differentiate this status from the status of other systems. Default: `"default"` #### Example @@ -51,26 +59,21 @@ Name | Type | Description ### Response -<%= headers 201, - :Location => -'https://api.github.com/repos/octocat/example/statuses/1' %> +<%= headers 201, :Location => get_resource(:status)['url'] %> <%= json :status %> -<% combined_media_type = "application/vnd.github.she-hulk-preview+json" %> - ## List Statuses for a specific Ref Users with pull access can view commit statuses for a given ref: - GET /repos/:owner/:repo/statuses/:ref + GET /repos/:owner/:repo/commits/:ref/statuses + +{{#tip}} + +This resource is also available via a legacy route: +`GET /repos/:owner/:repo/statuses/:ref`. -
- If you send an Accept header with the Combined Status API preview
- media type, <%= combined_media_type %>,
- this endpoint is also available at /repos/:owner/:repo/commits/:ref/statuses.
-
- The Combined status endpoint is currently available for developers to preview. - During the preview period, the API may change without advance notice. - Please see the blog post for full details. -
-
- To access this endpoint during the preview period, you must provide a custom
- media type in the Accept header:
-
<%= combined_media_type %>- -
Example
@@ -93,7 +97,7 @@ repositories where the primary language is Assembly. We're sorting by stars in descending order, so that the most popular repositories appear first in the search results. -<%= headers 200, {'X-RateLimit-Limit' => 20, 'X-RateLimit-Remaining' => 19} %> +<%= headers 200, {:pagination => default_pagination_rels{% if page.version == 'dotcom' %}, 'X-RateLimit-Limit' => 20, 'X-RateLimit-Remaining' => 19{% endif %}} %> <%= json(:repo_search_v3_results) %> ### Highlighting Repository Search Results @@ -104,8 +108,10 @@ use case. To get this metadata in your search results, specify the `text-match` media type in your Accept header. For example, via curl, the above query would look like this: - curl -H 'Accept: application/vnd.github.v3.text-match+json' \ - https://api.github.com/search/repositories?q=tetris+language:assembly&sort=stars&order=desc +``` command-line +curl -H 'Accept: application/vnd.github.v3.text-match+json' \ + 'https://api.github.com/search/repositories?q=tetris+language:assembly&sort=stars&order=desc' +``` This produces the same JSON payload as above, with an extra key called `text_matches`, an array of objects. These objects provide information such as @@ -126,32 +132,46 @@ Find file contents via various criteria. (This method returns up to 100 results GET /search/code +### Considerations for code search + +Due to the complexity of searching code, there are a few restrictions on how searches are performed: + +-
+
- Only the default branch is considered. In most cases, this will be the
masterbranch.
+ - Only files smaller than {% if page.version != 'dotcom' and page.version >= 2.2 %} 10 MB {% else %} 384 KB {% endif %} are searchable. +{% if page.version == 'dotcom' %} +
- You must always include at least one search term when searching source code. For example, searching for
language:gois not valid, whileamazing language:gois.
+{% endif %}
+
Example
@@ -166,7 +186,7 @@ Here, we're searching for the keyword `addClass` within a file's contents. We're making sure that we're only looking in files where the language is JavaScript. And we're scoping the search to the `repo:jquery/jquery` repository. -<%= headers 200, {'X-RateLimit-Limit' => 20, 'X-RateLimit-Remaining' => 19} %> +<%= headers 200, {:pagination => default_pagination_rels,{% if page.version == 'dotcom' %} 'X-RateLimit-Limit' => 20, 'X-RateLimit-Remaining' => 19{% endif %}} %> <%= json(:code_search_v3_results) %> ### Highlighting Code Search Results @@ -177,8 +197,10 @@ use case. To get this metadata in your search results, specify the `text-match` media type in your Accept header. For example, via curl, the above query would look like this: - curl -H 'Accept: application/vnd.github.v3.text-match+json' \ - https://api.github.com/search/code?q=addClass+in:file+language:js+repo:jquery/jquery +``` command-line +curl -H 'Accept: application/vnd.github.v3.text-match+json' \ + https://api.github.com/search/code?q=addClass+in:file+language:js+repo:jquery/jquery +``` This produces the same JSON payload as above, with an extra key called `text_matches`, an array of objects. These objects provide information such as @@ -207,38 +229,54 @@ Name | Type | Description `sort`|`string`| The sort field. Can be `comments`, `created`, or `updated`. Default: results are sorted by best match. `order`|`string`| The sort order if `sort` parameter is provided. One of `asc` or `desc`. Default: `desc` -The `q` search term can also contain any combination of the supported issue search qualifiers: +The `q` search term can also contain any combination of the supported issue search qualifiers as described by the in-browser [issue search documentation](https://help.github.com/articles/searching-issues/) and [search syntax documentation](https://help.github.com/articles/search-syntax/): - * [`type`](https://help.github.com/articles/searching-issues#type) - With this qualifier you can restrict the search to issues or pull request only. - * [`in`](https://help.github.com/articles/searching-issues#search-in) + * [`type`](https://help.github.com/articles/searching-issues#search-issues-or-pull-requests) + With this qualifier you can restrict the search to issues (`issue`) or pull request (`pr`) only. + * [`in`](https://help.github.com/articles/searching-issues#scope-the-search-fields) Qualifies which fields are searched. With this qualifier you can restrict the - search to just the title, body, comments, or any combination of these. - * [`author`](https://help.github.com/articles/searching-issues#author) - Finds issues created by a certain user. - * [`assignee`](https://help.github.com/articles/searching-issues#assignee) - Finds issues that are assigned to a certain user. - * [`mentions`](https://help.github.com/articles/searching-issues#mentions) - Finds issues that mention a certain user. - * [`commenter`](https://help.github.com/articles/searching-issues#commenter) - Finds issues that a certain user commented on. - * [`involves`](https://help.github.com/articles/searching-issues#involves) - Finds issues that were either created by a certain user, assigned to that + search to just the title (`title`), body (`body`), comments (`comments`), or any combination of these. + * [`author`](https://help.github.com/articles/searching-issues#search-by-the-author-of-an-issue-or-pull-request) + Finds issues or pull requests created by a certain user. + * [`assignee`](https://help.github.com/articles/searching-issues#search-by-the-assignee-of-an-issue-or-pull-request) + Finds issues or pull requests that are assigned to a certain user. + * [`mentions`](https://help.github.com/articles/searching-issues#search-by-a-mentioned-user-within-an-issue-or-pull-request) + Finds issues or pull requests that mention a certain user. + * [`commenter`](https://help.github.com/articles/searching-issues#search-by-a-commenter-within-an-issue-or-pull-request) + Finds issues or pull requests that a certain user commented on. + * [`involves`](https://help.github.com/articles/searching-issues#search-by-a-user-thats-involved-within-an-issue-or-pull-request) + Finds issues or pull requests that were either created by a certain user, assigned to that user, mention that user, or were commented on by that user. - * [`state`](https://help.github.com/articles/searching-issues#state) - Filter issues based on whether they're open or closed. - * [`labels`](https://help.github.com/articles/searching-issues#labels) - Filters issues based on their labels. - * [`language`](https://help.github.com/articles/searching-issues#language) - Searches for issues within repositories that match a certain language. - * [`created` or `updated`](https://help.github.com/articles/searching-issues#created-and-last-updated) - Filters issues based on times of creation, or when they were last updated. - * [`comments`](https://help.github.com/articles/searching-issues#comments) - Filters issues based on the quantity of comments. - * [`user` or `repo`](https://help.github.com/articles/searching-issues#users-organizations-and-repositories) + * [`team`](https://help.github.com/articles/searching-issues/#search-by-a-team-thats-mentioned-within-an-issue-or-pull-request) + For organizations you're a member of, finds issues or pull requests that @mention a team within the organization. + * [`state`](https://help.github.com/articles/searching-issues#search-based-on-whether-an-issue-or-pull-request-is-open) + Filter issues or pull requests based on whether they're open or closed. + * [`labels`](https://help.github.com/articles/searching-issues#search-by-the-labels-on-an-issue) + Filters issues or pull requests based on their labels. + * [`no`](https://help.github.com/articles/searching-issues#search-by-missing-metadata-on-an-issue-or-pull-request) + Filters items missing certain metadata, such as `label`, `milestone`, or `assignee` + * [`language`](https://help.github.com/articles/searching-issues#search-by-the-main-language-of-a-repository) + Searches for issues or pull requests within repositories that match a certain language. + * [`is`](https://help.github.com/articles/searching-issues#search-based-on-the-state-of-an-issue-or-pull-request) + Searches for items within repositories that match a certain state, such as `open`, `closed`, or `merged` + * [`created` or `updated`](https://help.github.com/articles/searching-issues#search-based-on-when-an-issue-or-pull-request-was-created-or-last-updated) + Filters issues or pull requests based on date of creation, or when they were last updated. + * [`merged`](https://help.github.com/articles/searching-issues#search-based-on-when-a-pull-request-was-merged) + Filters pull requests based on the date when they were merged. + * [`status`](https://help.github.com/articles/searching-issues#search-based-on-commit-status) + Filters pull requests based on the commit status. + * [`head` or `base`](https://help.github.com/articles/searching-issues#search-based-on-branch-names) + Filters pull requests based on the branch that they came from or that they are modifying. + * [`closed`](https://help.github.com/articles/searching-issues#search-based-on-when-an-issue-or-pull-request-was-closed) + Filters issues or pull requests based on the date when they were closed. + * [`comments`](https://help.github.com/articles/searching-issues#search-by-the-number-of-comments-an-issue-or-pull-request-has) + Filters issues or pull requests based on the quantity of comments. + * [`user` or `repo`](https://help.github.com/articles/searching-issues#search-within-a-users-or-organizations-repositories) Limits searches to a specific user or repository. +If you know the specific SHA hash of a commit, you can use also [use it to search for pull requests](https://help.github.com/articles/searching-issues#search-by-the-commit-shas-within-a-pull-request) that contain that SHA. Note that the SHA syntax must be at least seven characters. +Example
Let's say you want to find the oldest unresolved Python bugs on Windows. Your @@ -251,7 +289,7 @@ that's labeled as `bug`. The search runs across repositories whose primary language is Python. We’re sorting by creation date in ascending order, so that the oldest issues appear first in the search results. -<%= headers 200, {'X-RateLimit-Limit' => 20, 'X-RateLimit-Remaining' => 19} %> +<%= headers 200, {:pagination => default_pagination_rels,{% if page.version == 'dotcom' %} 'X-RateLimit-Limit' => 20, 'X-RateLimit-Remaining' => 19{% endif %}} %> <%= json(:issue_search_v3_results) %> ### Highlighting Issue Search Results @@ -262,8 +300,10 @@ use case. To get this metadata in your search results, specify the `text-match` media type in your Accept header. For example, via curl, the above query would look like this: - curl -H 'Accept: application/vnd.github.v3.text-match+json' \ - https://api.github.com/search/issues?q=windows+label:bug+language:python+state:open&sort=created&order=asc +``` command-line +curl -H 'Accept: application/vnd.github.v3.text-match+json' \ + 'https://api.github.com/search/issues?q=windows+label:bug+language:python+state:open&sort=created&order=asc' +``` This produces the same JSON payload as above, with an extra key called `text_matches`, an array of objects. These objects provide information such as @@ -292,24 +332,24 @@ Name | Type | Description `sort`|`string`| The sort field. Can be `followers`, `repositories`, or `joined`. Default: results are sorted by best match. `order`|`string`| The sort order if `sort` parameter is provided. One of `asc` or `desc`. Default: `desc` -The `q` search term can also contain any combination of the supported user search qualifiers: +The `q` search term can also contain any combination of the supported user search qualifiers as described by the in-browser [user search documentation](https://help.github.com/articles/searching-users/) and [search syntax documentation](https://help.github.com/articles/search-syntax/): - * [`type`](https://help.github.com/articles/searching-users#type) - With this qualifier you can restrict the search to just personal accounts or - just organization accounts. - * [`in`](https://help.github.com/articles/searching-users#search-in) + * [`type`](https://help.github.com/articles/searching-users#search-for-users-or-organizations) + With this qualifier you can restrict the search to just personal accounts (`user`) or + just organization accounts (`org`). + * [`in`](https://help.github.com/articles/searching-users#scope-the-search-fields) Qualifies which fields are searched. With this qualifier you can restrict - the search to just the username, public email, full name, or any + the search to just the username (`login`), public email (`email`), full name (`fullname`), or any combination of these. - * [`repos`](https://help.github.com/articles/searching-users#repository-count) + * [`repos`](https://help.github.com/articles/searching-users#search-based-on-the-number-of-repositories-a-user-has) Filters users based on the number of repositories they have. - * [`location`](https://help.github.com/articles/searching-users#location) + * [`location`](https://help.github.com/articles/searching-users#search-based-on-the-location-where-a-user-resides) Filter users by the location indicated in their profile. - * [`language`](https://help.github.com/articles/searching-users#language) + * [`language`](https://help.github.com/articles/searching-users#search-based-on-the-languages-of-a-users-repositories) Search for users that have repositories that match a certain language. - * [`created`](https://help.github.com/articles/searching-users#created) + * [`created`](https://help.github.com/articles/searching-users#search-based-on-when-a-user-joined-github) Filter users based on when they joined. - * [`followers`](https://help.github.com/articles/searching-users#followers) + * [`followers`](https://help.github.com/articles/searching-users#search-based-on-the-number-of-followers-a-user-has) Filter users based on the number of followers they have.Example
@@ -321,7 +361,7 @@ Imagine you're looking for a list of popular users. You might try out this query Here, we're looking at users with the name Tom. We're only interested in those with more than 42 repositories, and only if they have over 1,000 followers. -<%= headers 200, {'X-RateLimit-Limit' => 20, 'X-RateLimit-Remaining' => 19} %> +<%= headers 200, {:pagination => default_pagination_rels,{% if page.version == 'dotcom' %} 'X-RateLimit-Limit' => 20, 'X-RateLimit-Remaining' => 19{% endif %}} %> <%= json(:user_search_v3_results) %> ### Highlighting User Search Results @@ -332,8 +372,10 @@ use case. To get this metadata in your search results, specify the `text-match` media type in your Accept header. For example, via curl, the above query would look like this: - curl -H 'Accept: application/vnd.github.v3.text-match+json' \ - https://api.github.com/search/users?q=tom+repos:%3E42+followers:%3E1000 +``` command-line +curl -H 'Accept: application/vnd.github.v3.text-match+json' \ + https://api.github.com/search/users?q=tom+repos:%3E42+followers:%3E1000 +``` This produces the same JSON payload as above, with an extra key called `text_matches`, an array of objects. These objects provide information such as @@ -363,7 +405,7 @@ in your Accept header. application/vnd.github.v3.text-match+json The results will provide the same JSON payloads as shown above, with an extra -key called `text_matches`. Inside the `text_matches` array, each hash includes +key called `text_matches`. Inside the `text_matches` array, each object includes the following attributes: @@ -380,8 +422,10 @@ Name | Description Using curl, and the [example issue search](#issue-search-example) above, our API request would look like this: - curl -H 'Accept: application/vnd.github.v3.text-match+json' \ - https://api.github.com/search/issues?q=windows+label:bug+language:python+state:open&sort=created&order=asc +``` command-line +curl -H 'Accept: application/vnd.github.v3.text-match+json' \ + 'https://api.github.com/search/issues?q=windows+label:bug+language:python+state:open&sort=created&order=asc' +``` The response will include a `text_matches` array for each search result. In the JSON below, we have two objects in the `text_matches` array. diff --git a/content/v3/search/legacy.md b/content/v3/search/legacy.md index eb2031b5fc..bcae61c3ff 100644 --- a/content/v3/search/legacy.md +++ b/content/v3/search/legacy.md @@ -1,10 +1,9 @@ --- -title: Legacy Search | GitHub API +title: Legacy Search --- # Legacy Search -* TOC {:toc} This is a listing of the Legacy Search API features from API v2 that have been ported to API @@ -12,15 +11,13 @@ v3. There should be no changes, other than the new URL and JSON output format. ### Legacy Search API is Deprecated -- The Legacy Search API (described below) is deprecated - and is scheduled for removal in the next major version of the API. +{{#warning}} - We recommend using the v3 Search API instead. - It contains new endpoints and much more functionality. -
-- Note: We recommend using the v3 API - instead of the deprecated beta version of the API. -
-- The beta media type differs from the v3 media type in - just a few places. In most - cases, migrating an application from the beta media type to the v3 media - type is smooth and painless. -
-- We will eventually retire the beta version, but we have no official - retirement date to annouce at the moment. When the time comes, rest assured - that we'll announce the retirement with plenty of notice. -
-