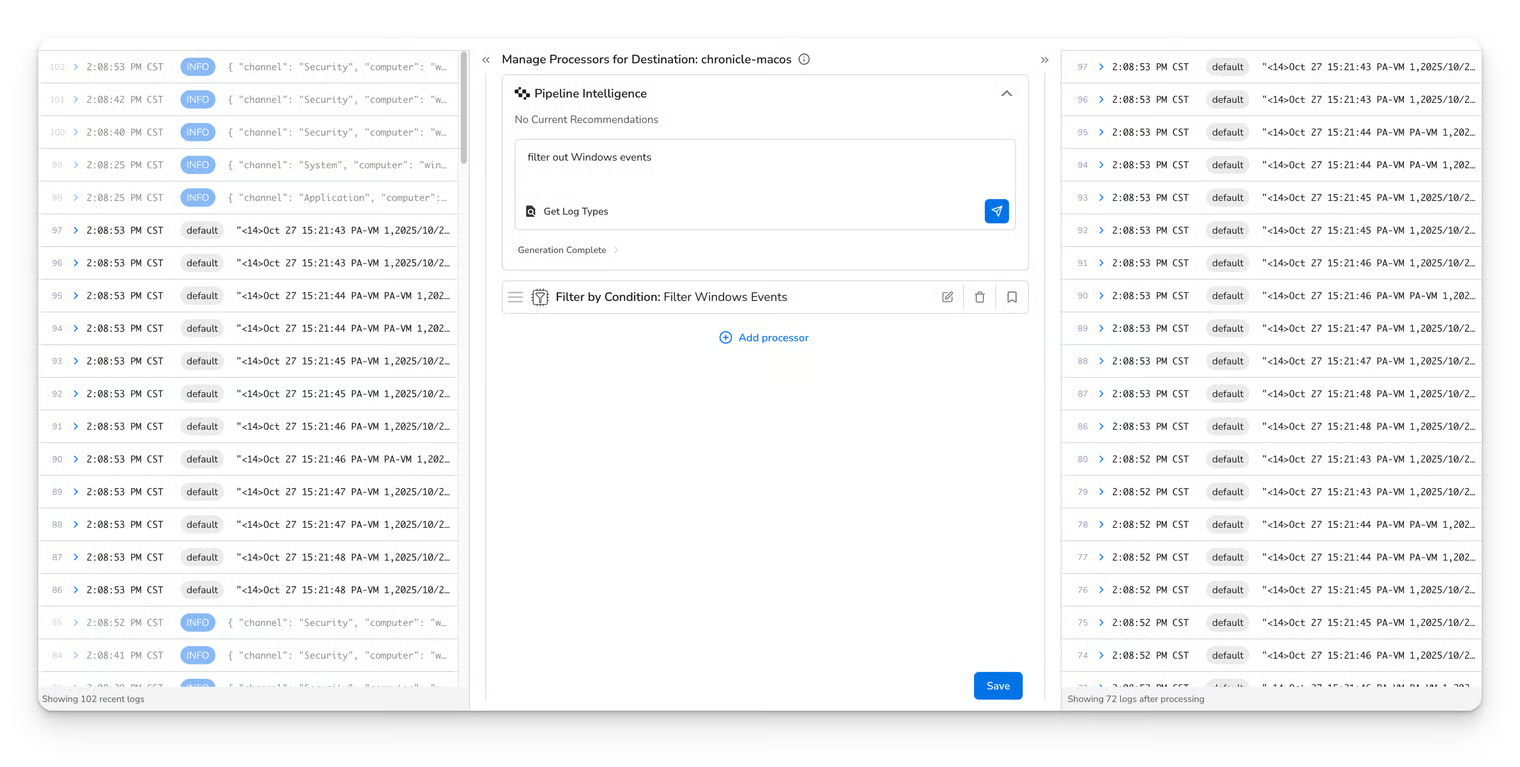
| Generate Processors | Processor generation | Google Gemini | gemini-2.5-flash | No | Yes |
| Get Log Types | Log classification | Google Gemini | gemini-2.5-flash-lite | No | Yes |
| Get Log Type and Body Format | Log classification | Google Gemini | gemini-2.5-flash-lite | No | Yes |
| Migrate Configurations (Chronicle Forwarder) | Config conversion | — | — | — | No |
| Migrate Configurations (OTel) | Config conversion | Google Gemini | gemini-2.5-flash | No | Yes |
| Migrate Configurations (Splunk Universal Forwarder) | Config conversion | — | — | — | No |
| Parse Field | Field parsing | Google Gemini | gemini-2.5-flash | No | Yes |
| Parse with Regex | Regex generation | Google Gemini | gemini-2.5-flash | No | Yes |
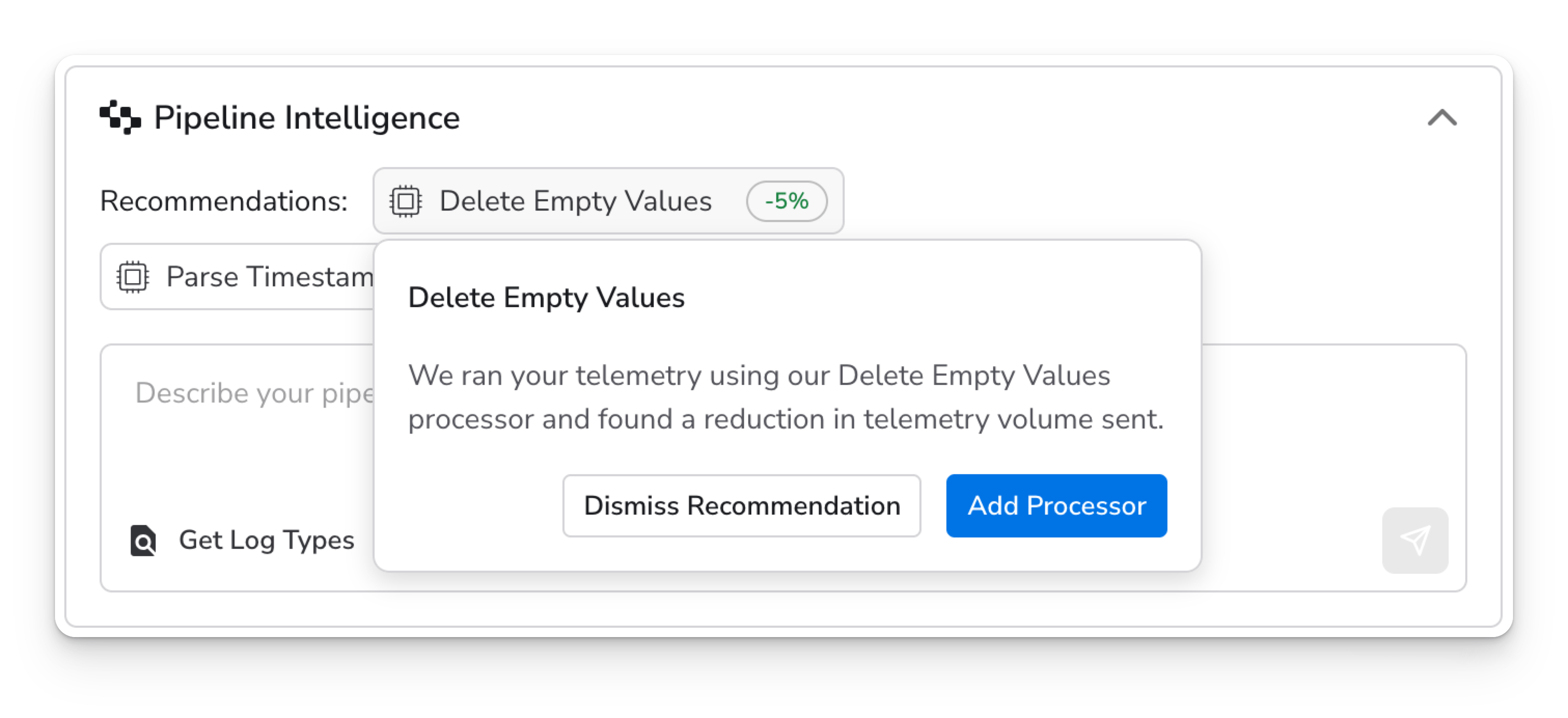
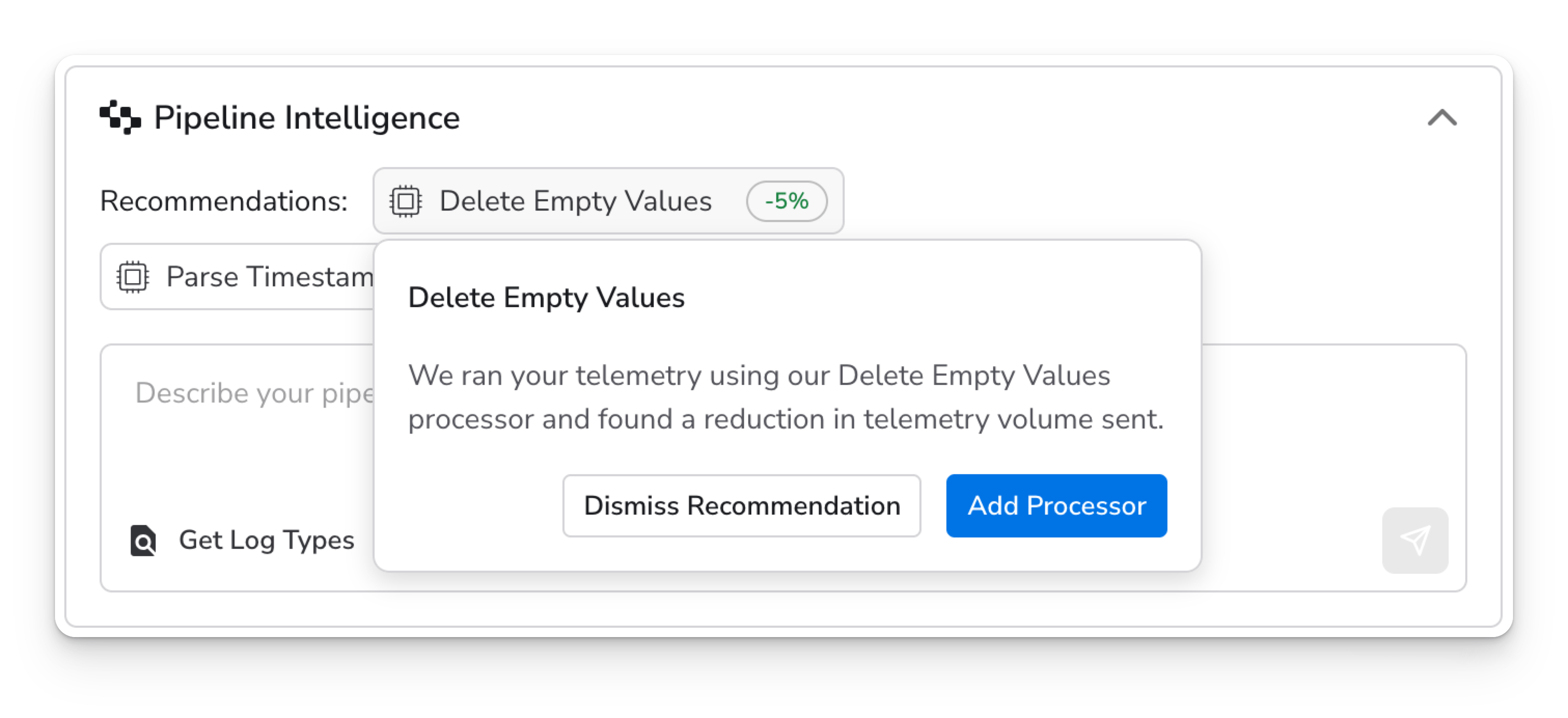
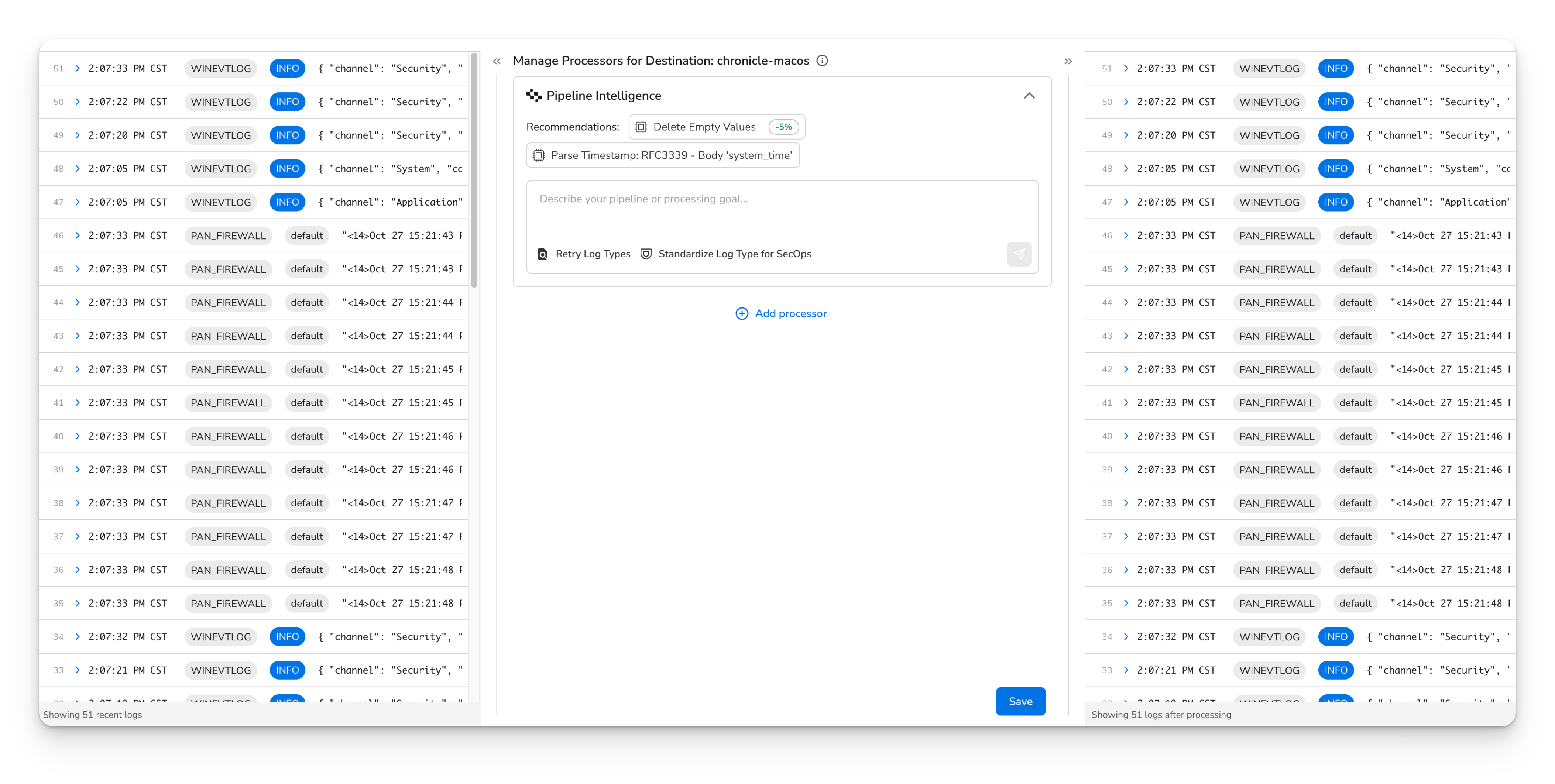
| Pipeline Intelligence Recommendations | Processor recommendations | Google Gemini | gemini-2.5-flash | No | Yes |
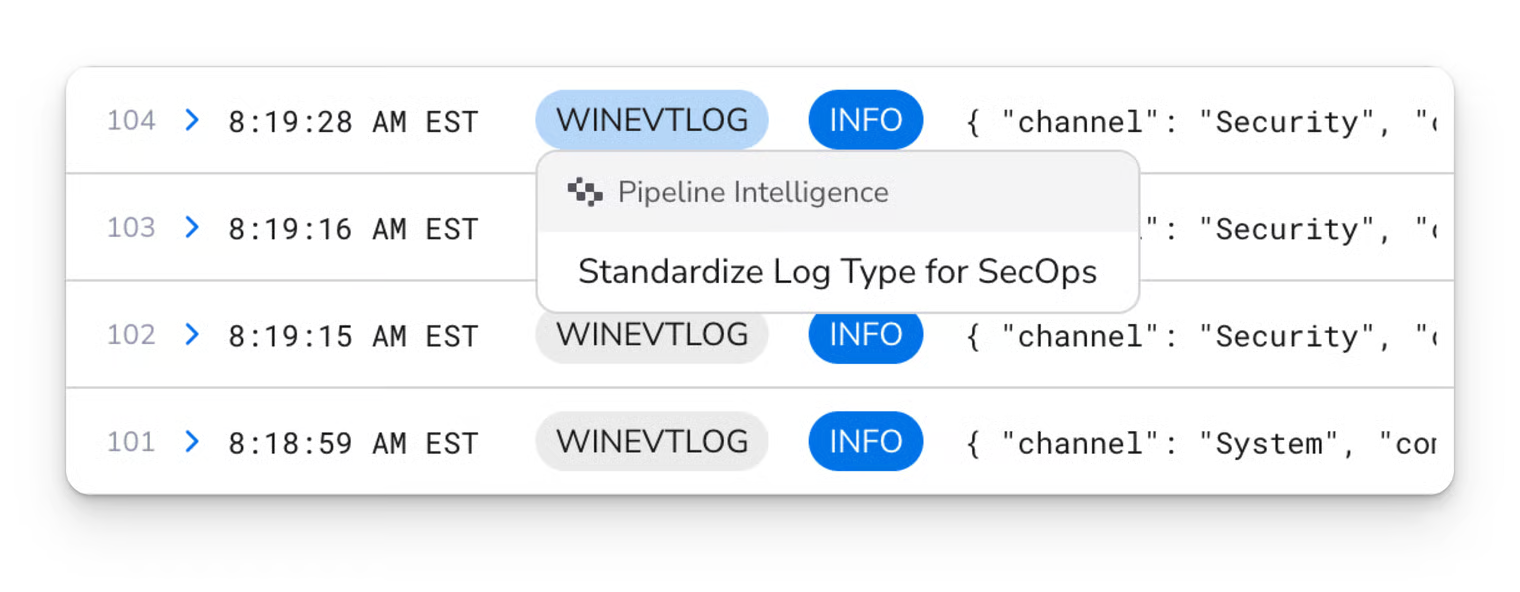
| Standardize Log Type for SecOps | Processor generation | Google Gemini | gemini-2.5-flash | No | Yes |
| Validate SecOps Parser | Parser validation | — | — | — | No |